In the past few years, some public figures including President Donald Trump and Elon Musk began promoting investments in various crypto currencies named in their likeness or that they were prominent holders of on their social media platforms they own, Truth Social and X (formerly Twitter) respectively. $TRUMP coin for example was created on January 17, 2025 and endorsed by the official Trump Truth Social account. Likewise the $WLFI coin, in which Trump and his children are listed as co-founders and executives. $MELANIA similarly was endorsed by official Melania Trump posts on X platform. The list goes on, earning Trump the title of “Crypto President”. Elon Musk has had a longer history of high profile endorsements of crypto currency. In fact, repeated posts about pushing his viewers on X to invest in Dogecoin for example led to him calling himself the “Dogefather” on Saturday Night Live. As these figures have made posts promoting or endorsing these currencies, threat actors have begun spoofing these endorsements and promotions to trick users into crypto scams. They spoof the real social media pages and posts and promote crypto currency much like the real personas do but for their own gain.
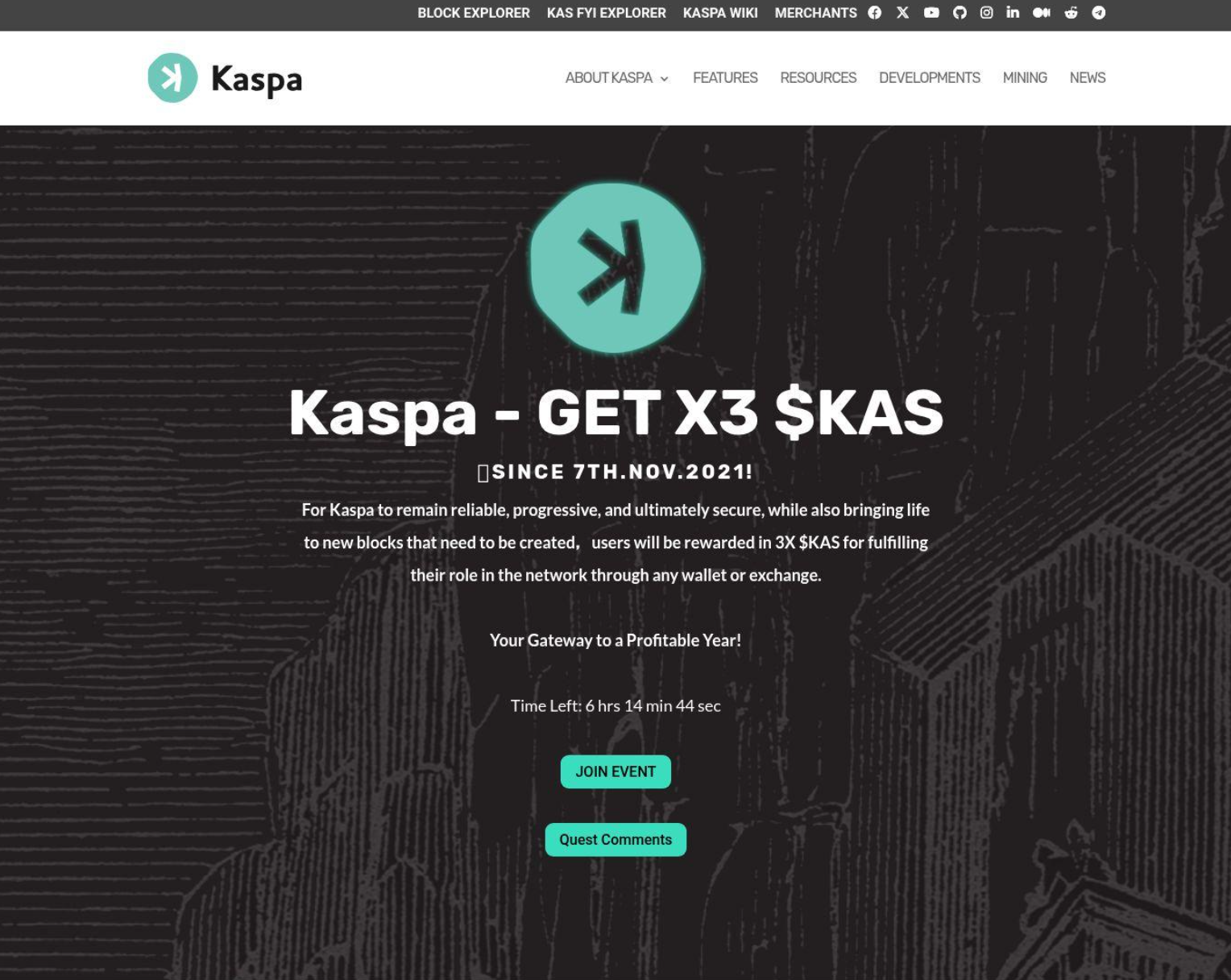
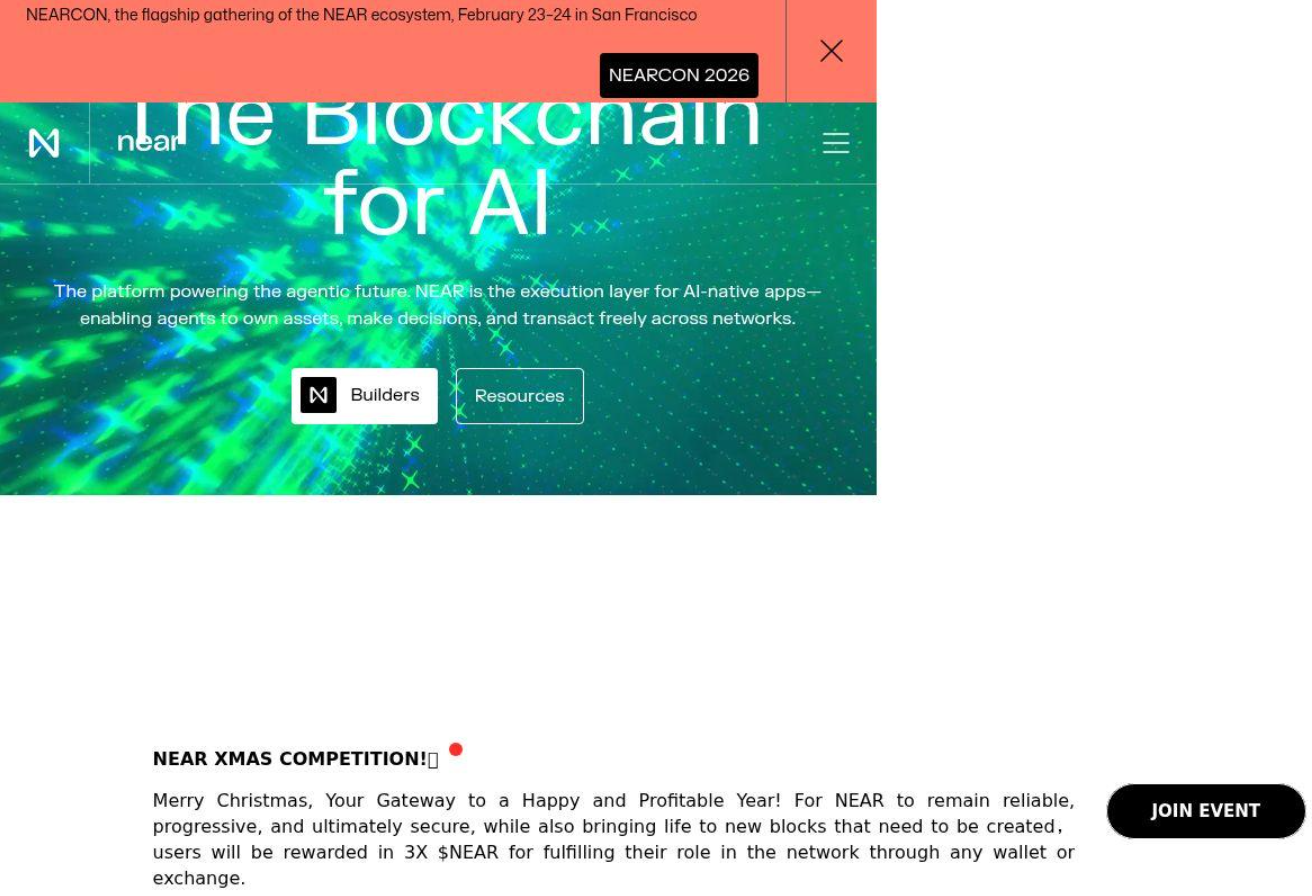
This report documents the analysis of a cryptocurrency scam operation. The operation has been active since at least January 2025 and spans roughly 250 identified domains across multiple scam themes. Nearly all target retail crypto users, but use different approaches to get their money.
Details
The investigation started with an identified set of 60 suspected scam domains sharing the same Google analytics tag ID. Upon scanning them and extracting wallet addresses from the ones that were live, we then verified those wallets against blockchain APIs, and attempted to trace the funds. That work uncovered the first campaign, a network of fake celebrity crypto giveaway sites. A shared actor wallet address and domain registration pattern then led us to a second larger set of more technical scam configurations involving fake token presale sites impersonating a wide variety of real blockchain projects.
Idol Scam Templates:
Idol scam template set is a collection of sites impersonating Elon Musk, Donald Trump, and Truth Social, all pushing the same basic pitch: send crypto and get double back. About 11 of the 60 domains were active with extractable wallets. Several share a common nameserver infrastructure at streetplug[.]me.
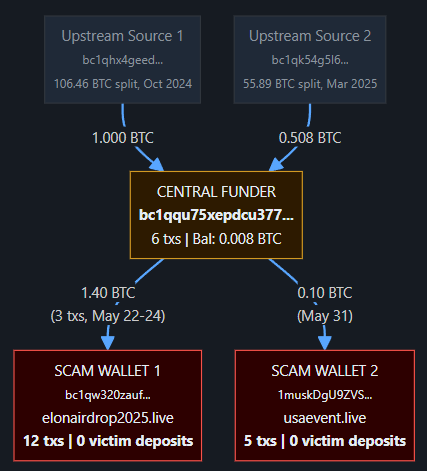
On-chain, the picture was straightforward. The two most active BTC wallets received a combined ~1.5 BTC, but tracing showed all of it came from a single central funder address — not from victims. The actor was likely sending money to themselves to inflate the on-chain transaction history and make the wallets look active. A bridge address connected both wallets with a dust transaction, confirming single-actor control. Downstream, the funds moved through a 5-layer laundering pipeline ending at high-volume mixing or OTC services, some with hundreds of thousands of transactions and multiple fraud flags. One of the upstream wallets was previously reported as being owned by ChangeNow.io, a cryptocurrency swap service that allows transactions to happen wallet-to-wallet instead of involving an exchange like CoinBase or Binance. The pipeline predates this campaign. The intermediary addresses have activity going back to May 2024 with hundreds of transactions, which we suspect is an indication this infrastructure has been used for other operations previously.
We found no confirmed victim deposits in the wallets we could trace, but that doesn't mean there are no victims. The actor may use different receiving addresses than the ones displayed on the sites, or victims may exist in transaction history we couldn't access. However, what we can confirm is that the on-chain activity we traced is the actor moving their own money around.
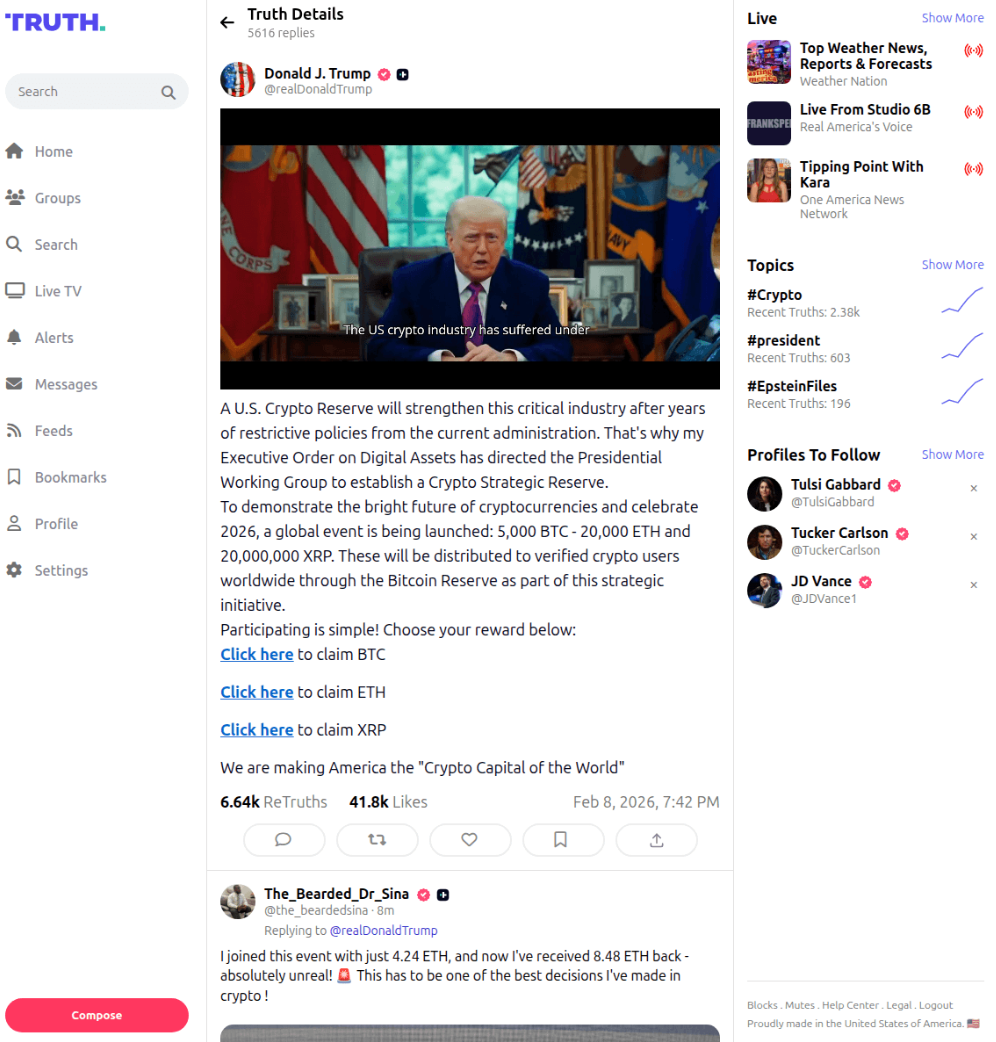
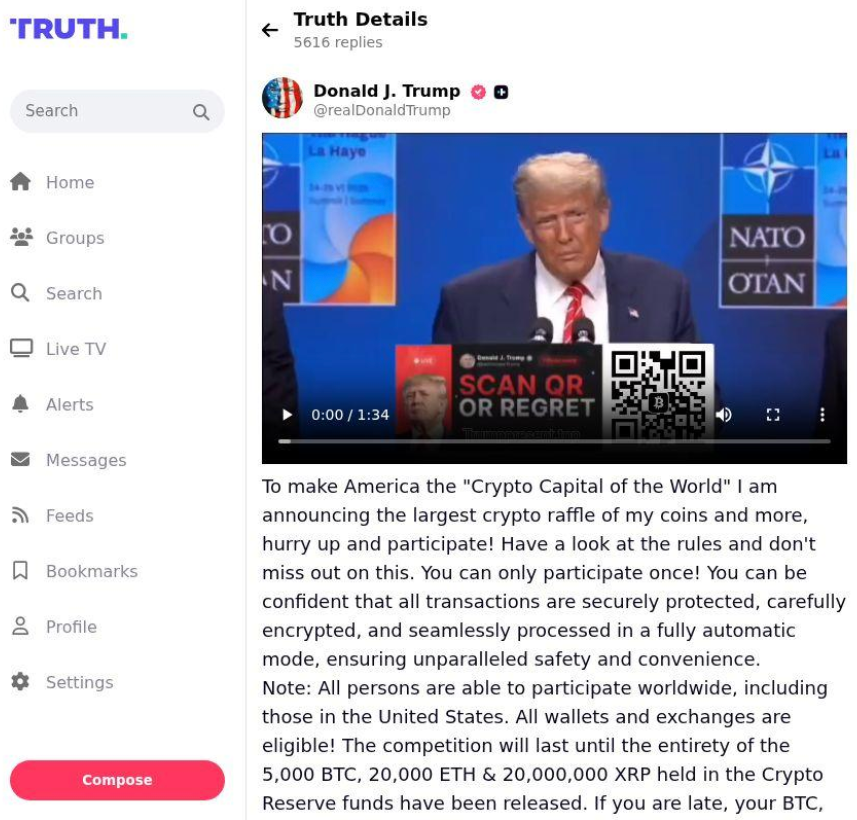
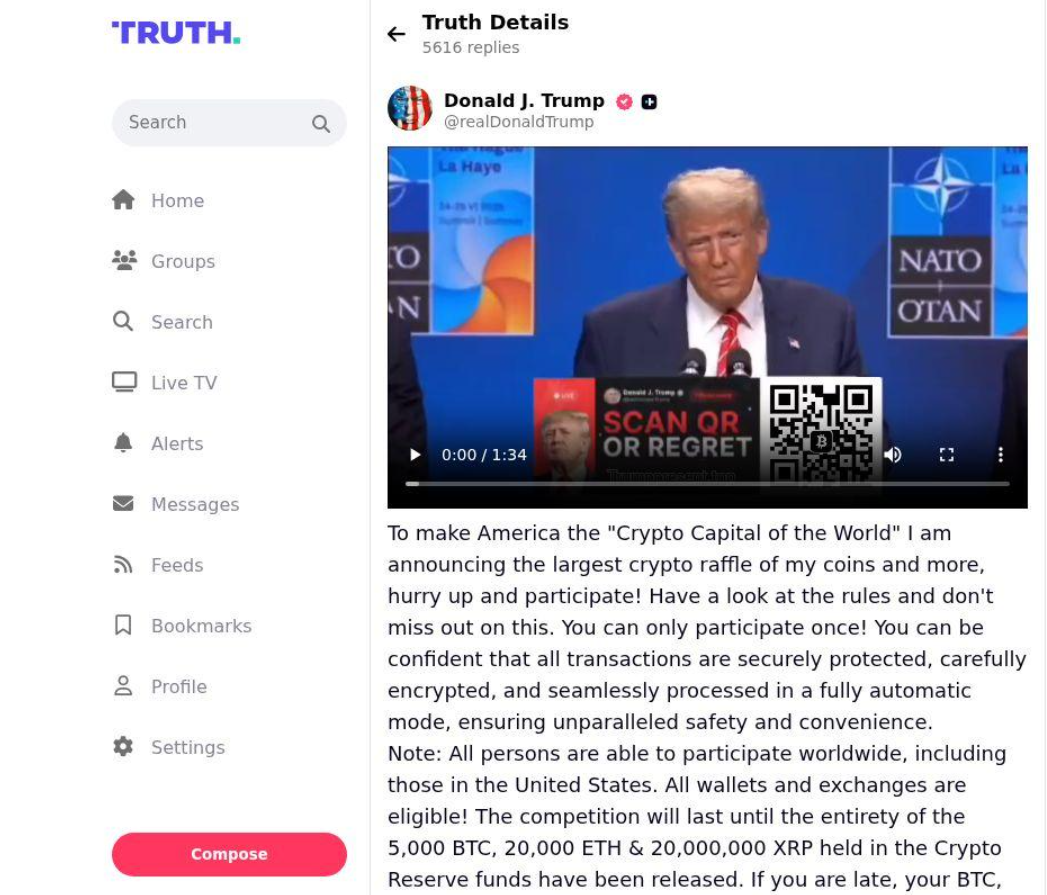
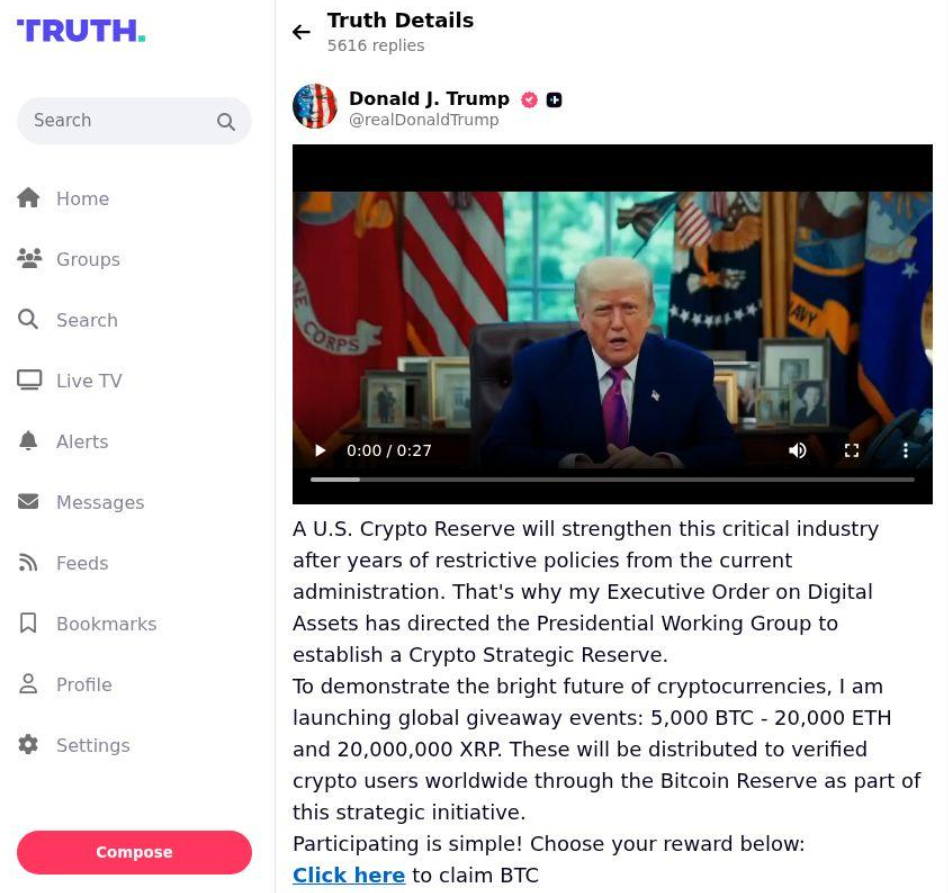
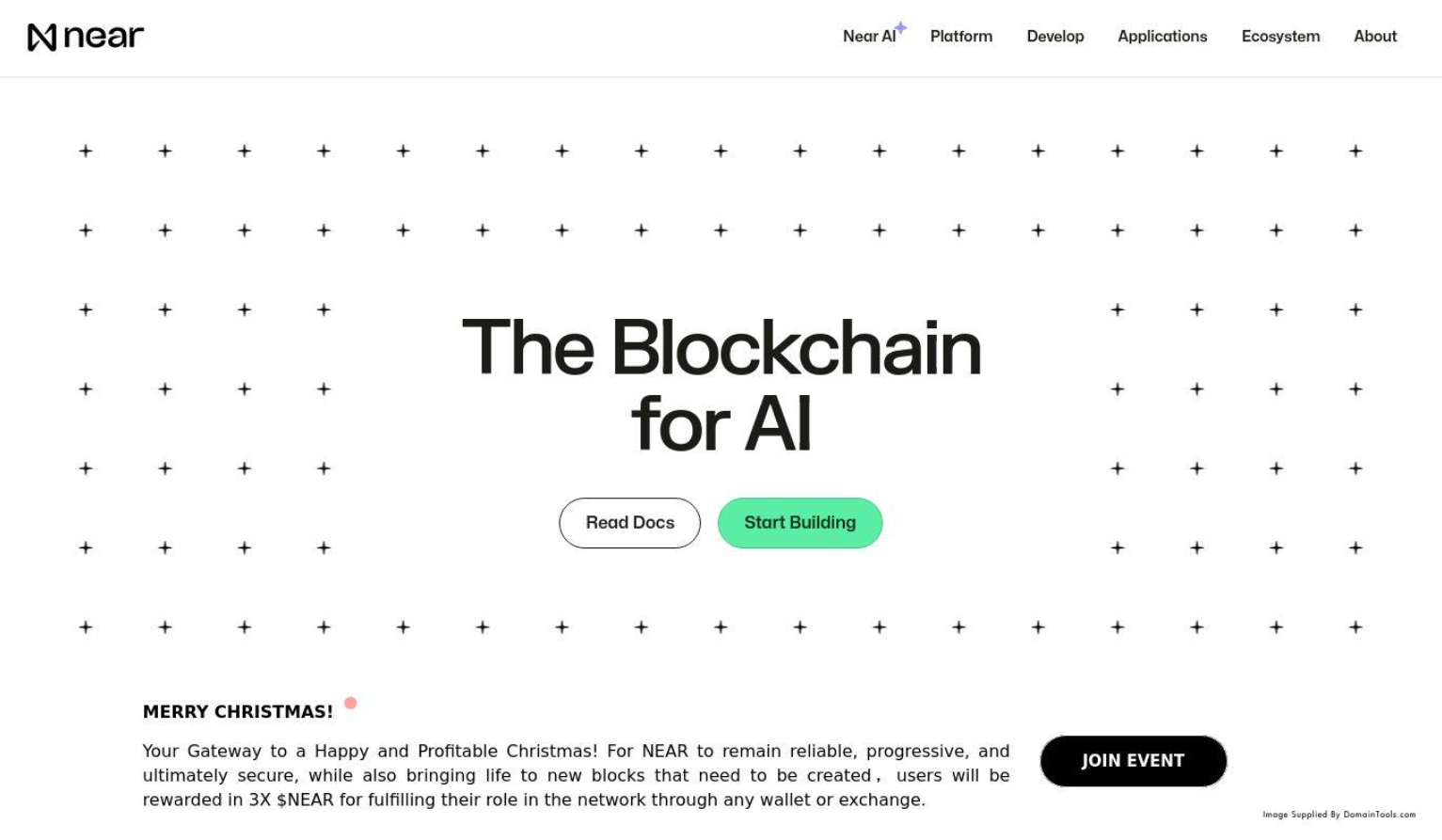
Example scam sites “trump4u[.]org” and “trumppresent[.]top” masquerade as Truth Social posts by President Trump that purports to have signed an executive order to hand out cryptocurrency rewards to those that click the links. While it is true that President Trump has officially established a Strategic Bitcoin Reserve and a U.S. Digital Asset Stockpile, the specific posts are designed to look like related Truth Social posts to trick users into participating in a fraudulent giveaway.
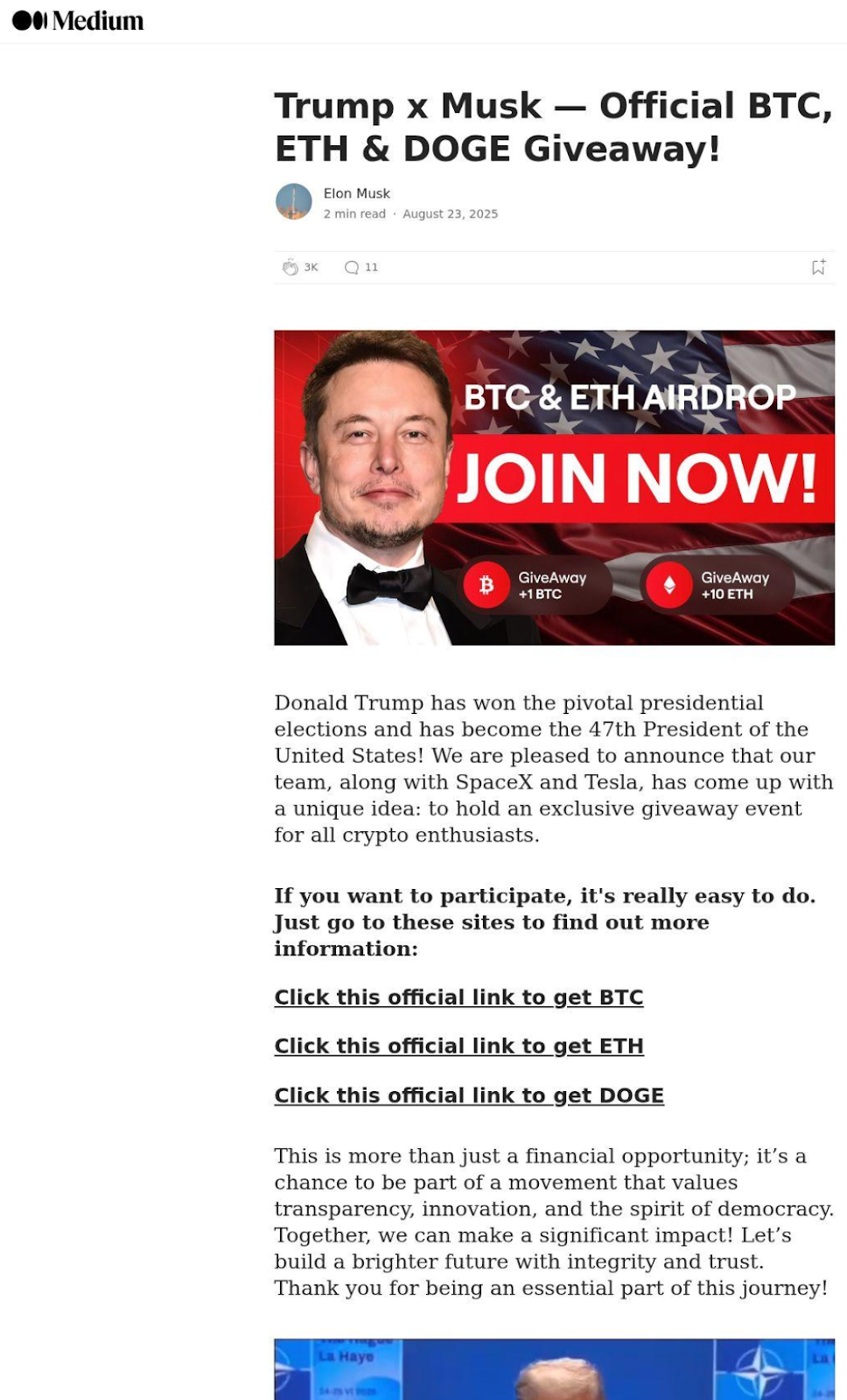
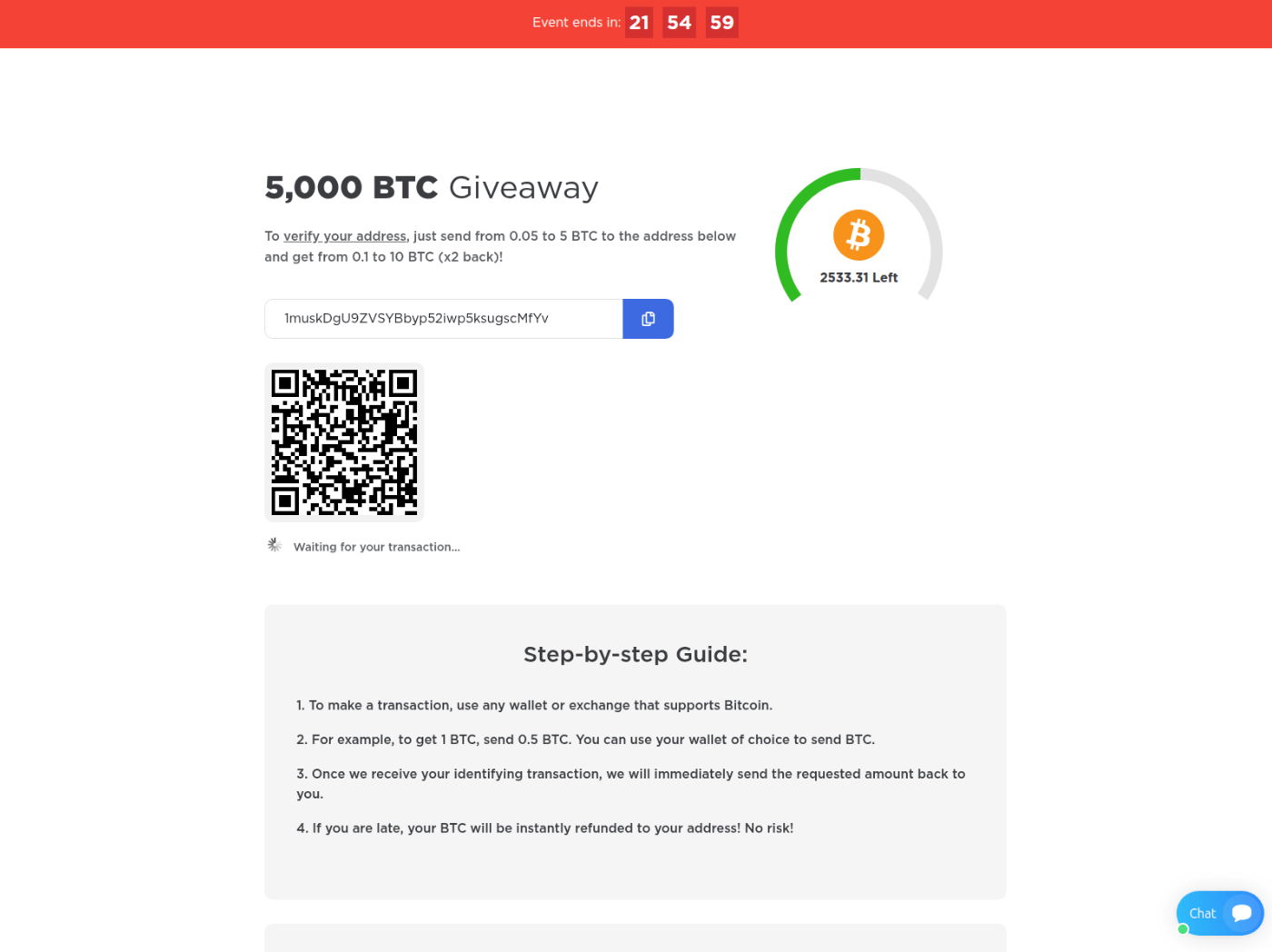
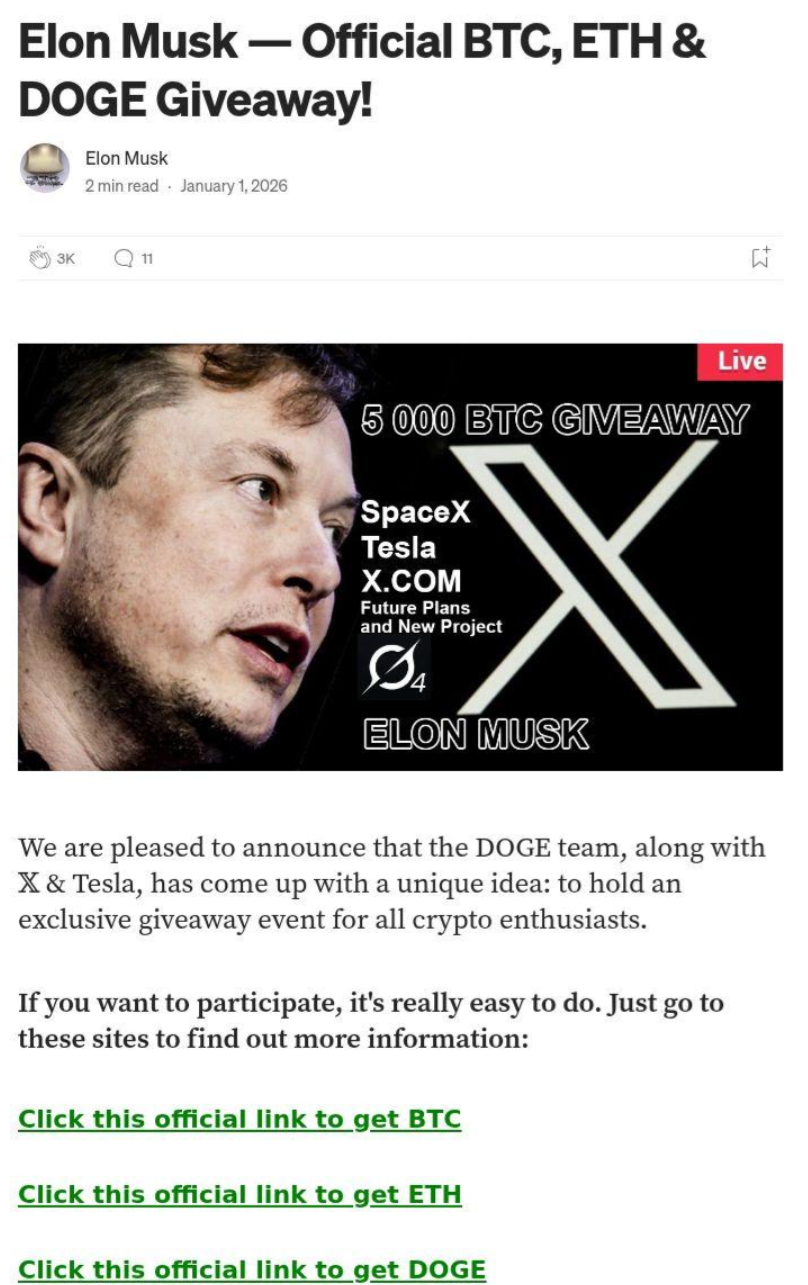
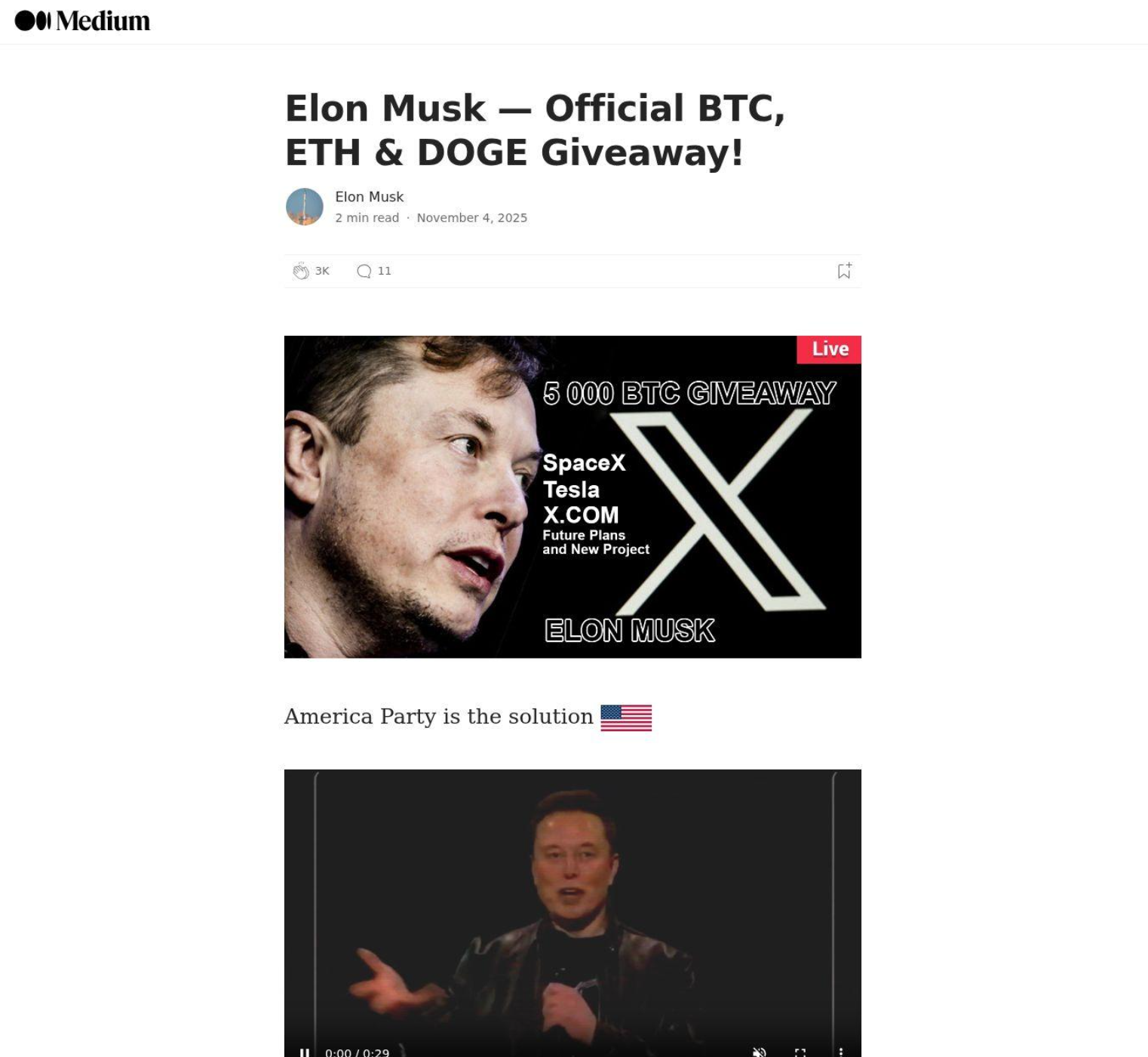
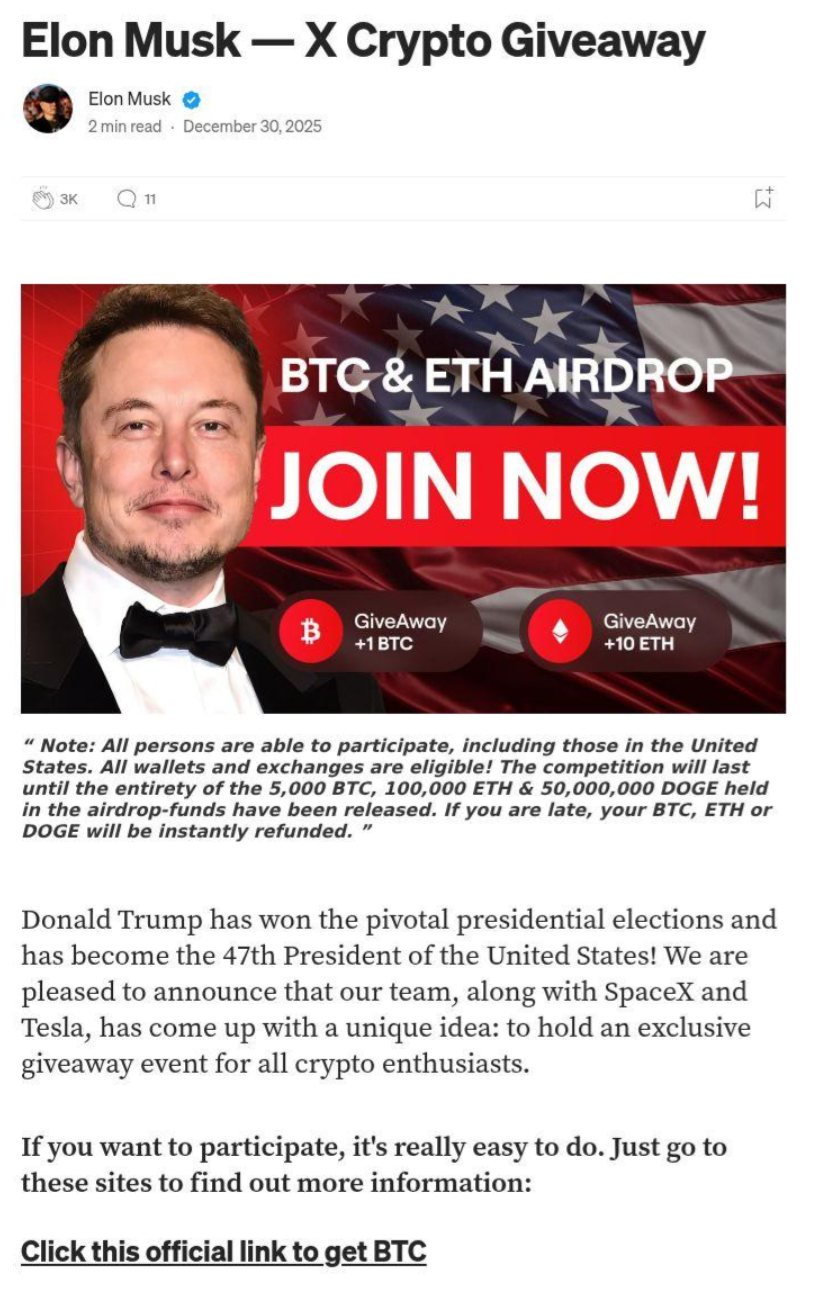
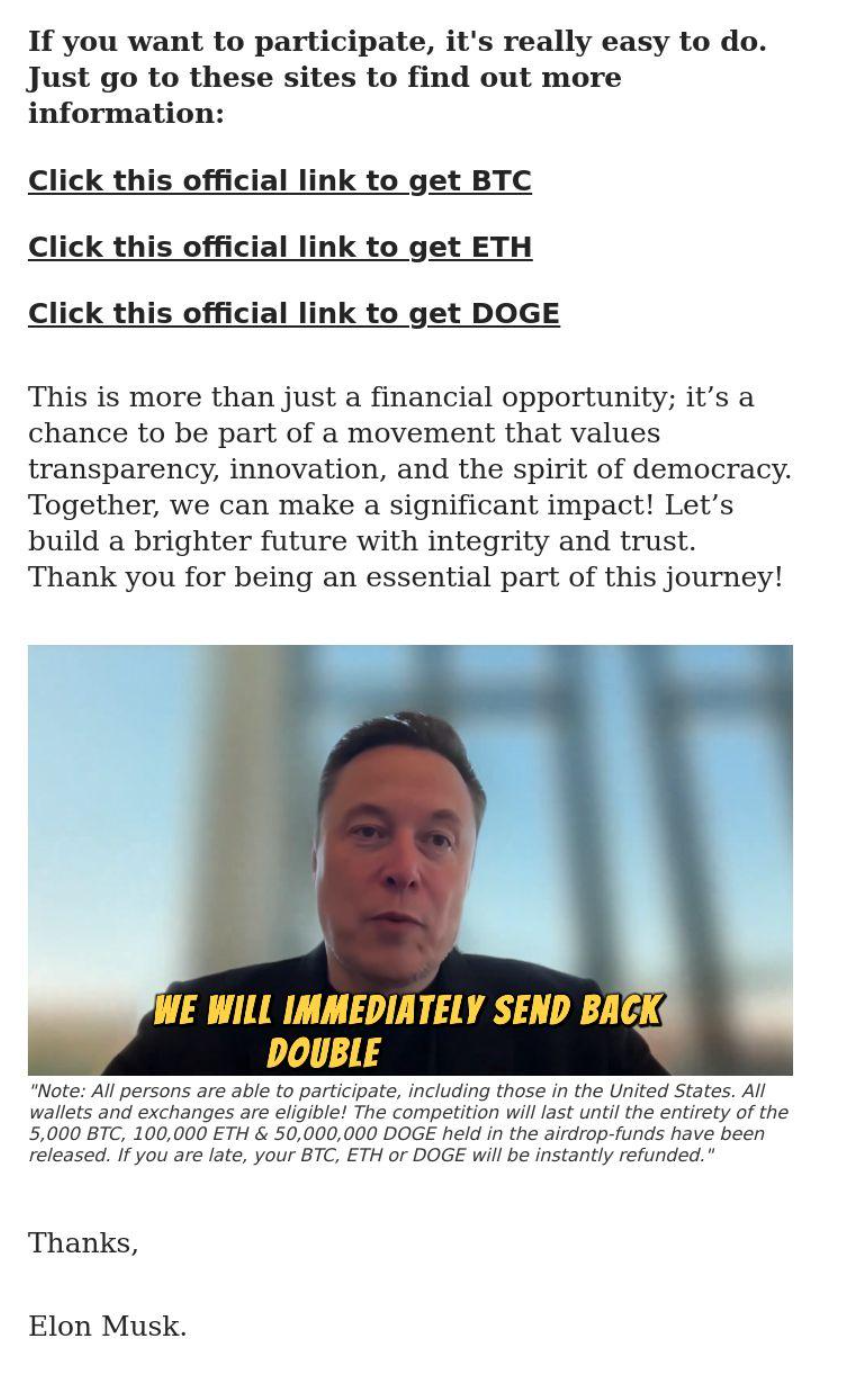
Similar scam sites spoofs as a Medium platform page and masquerade as a user named “Elon Musk” such as the following screenshot of “usaevent[.]live”.
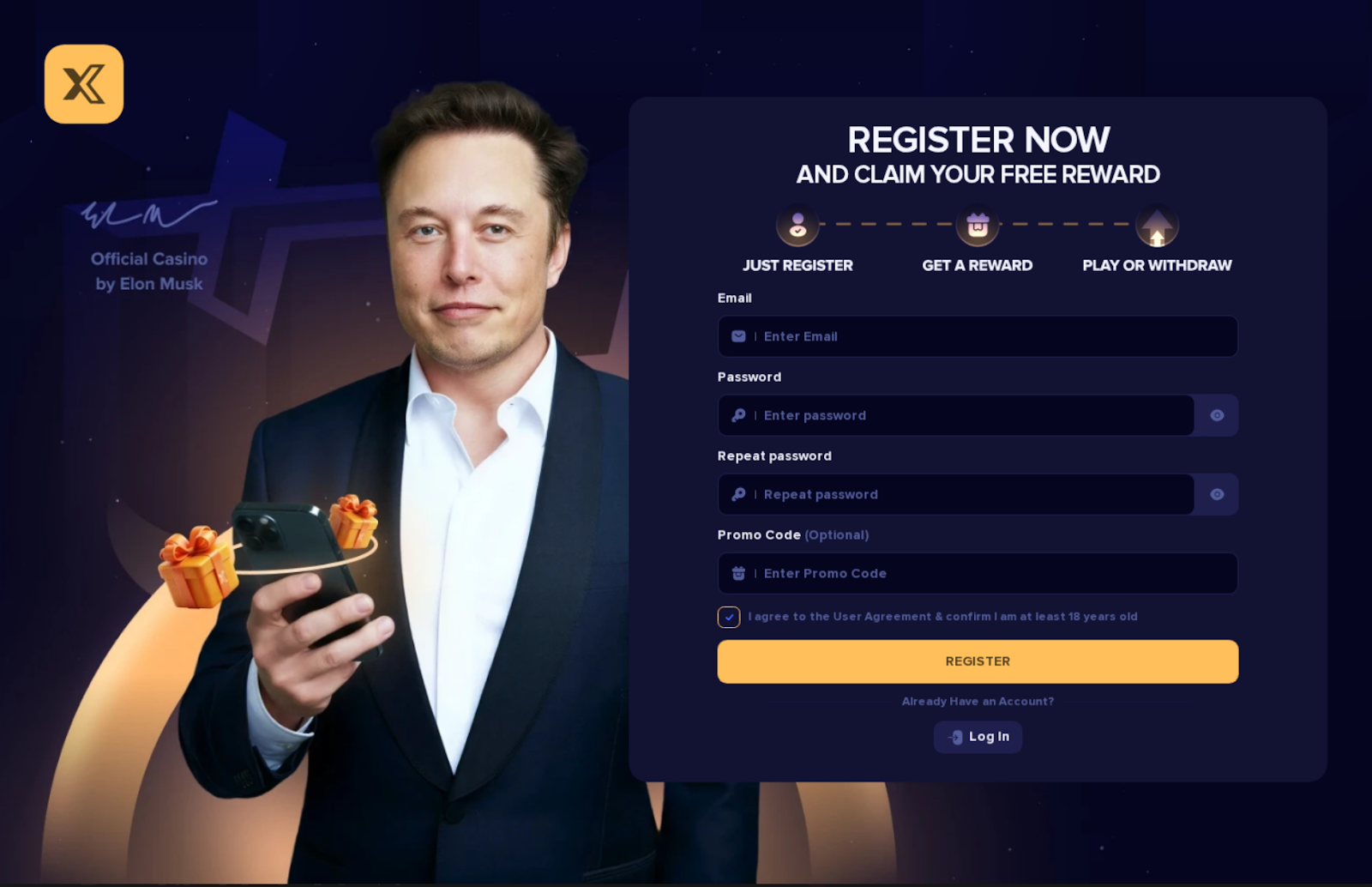
Other scam variations show Elon Musk alongside an “X” logo purportedly endorsing a Casino related site with a reward for signing up.
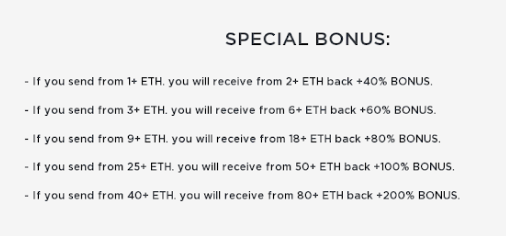
One of the scam’s instructions:
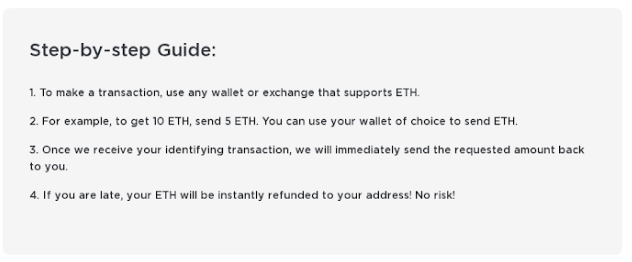
In each of these examples, multiple layers of incentives and ploys are used to appear legitimate and pressure site visitors into being conned by the scam..
Incentives:
Fake Comments:
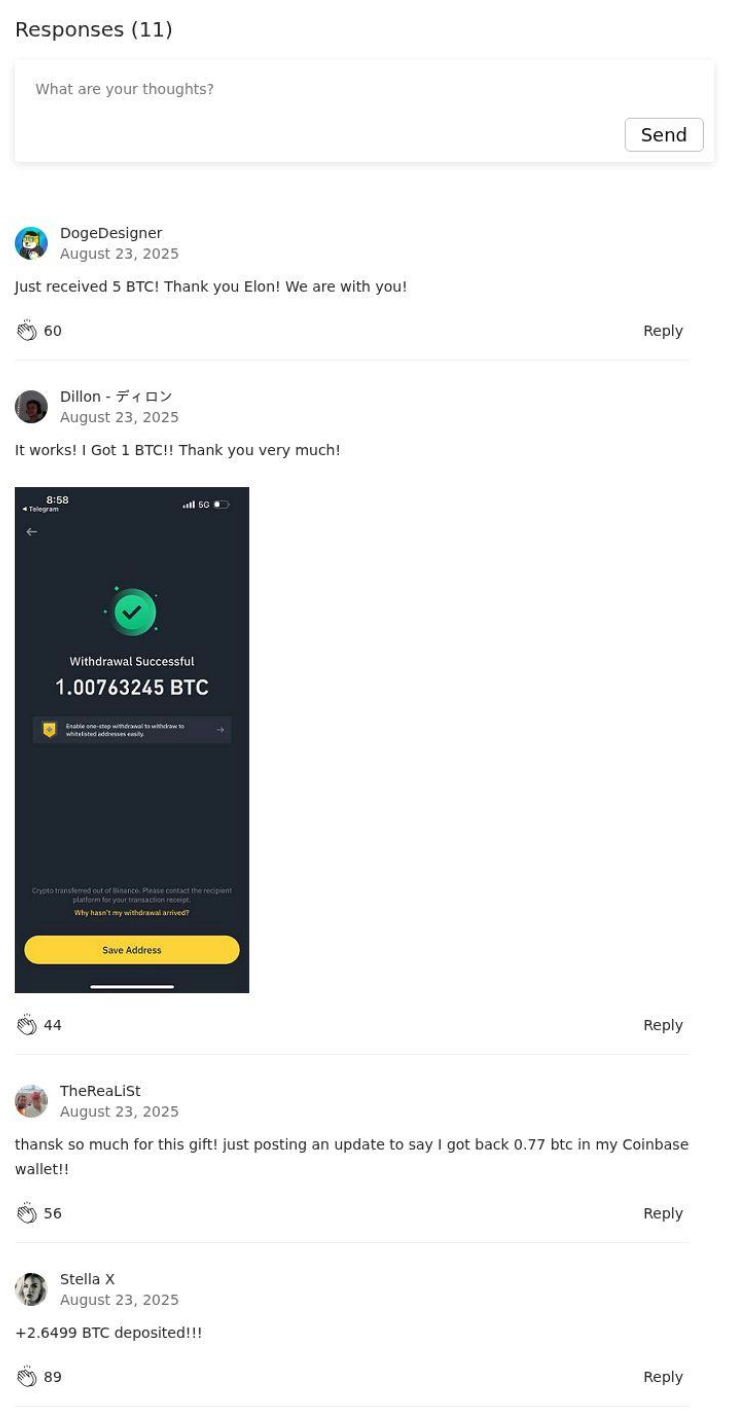
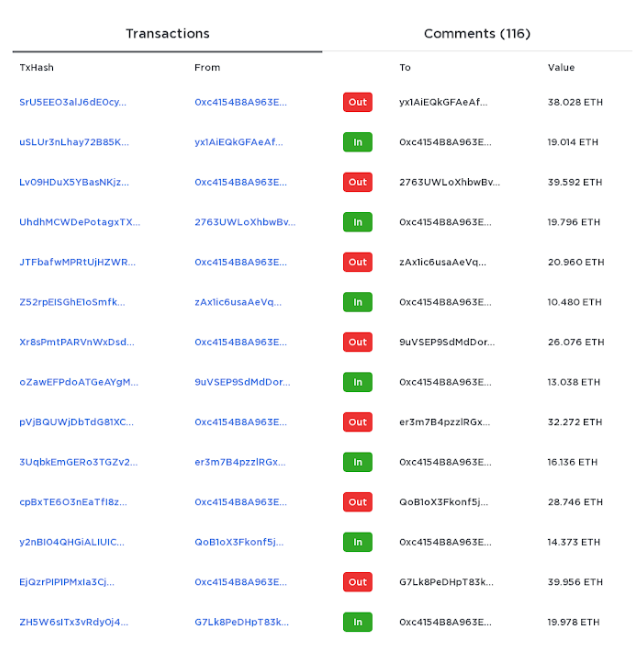
Fake Transactions generated by code on a hardcoded interval
The endgame of the scam is to convince site visitors to click on any of the three links and send money from their wallet. Links to other pages with crypto wallet addresses.
Example: trumpbtc[.]top/btc/index.html from Trump variation
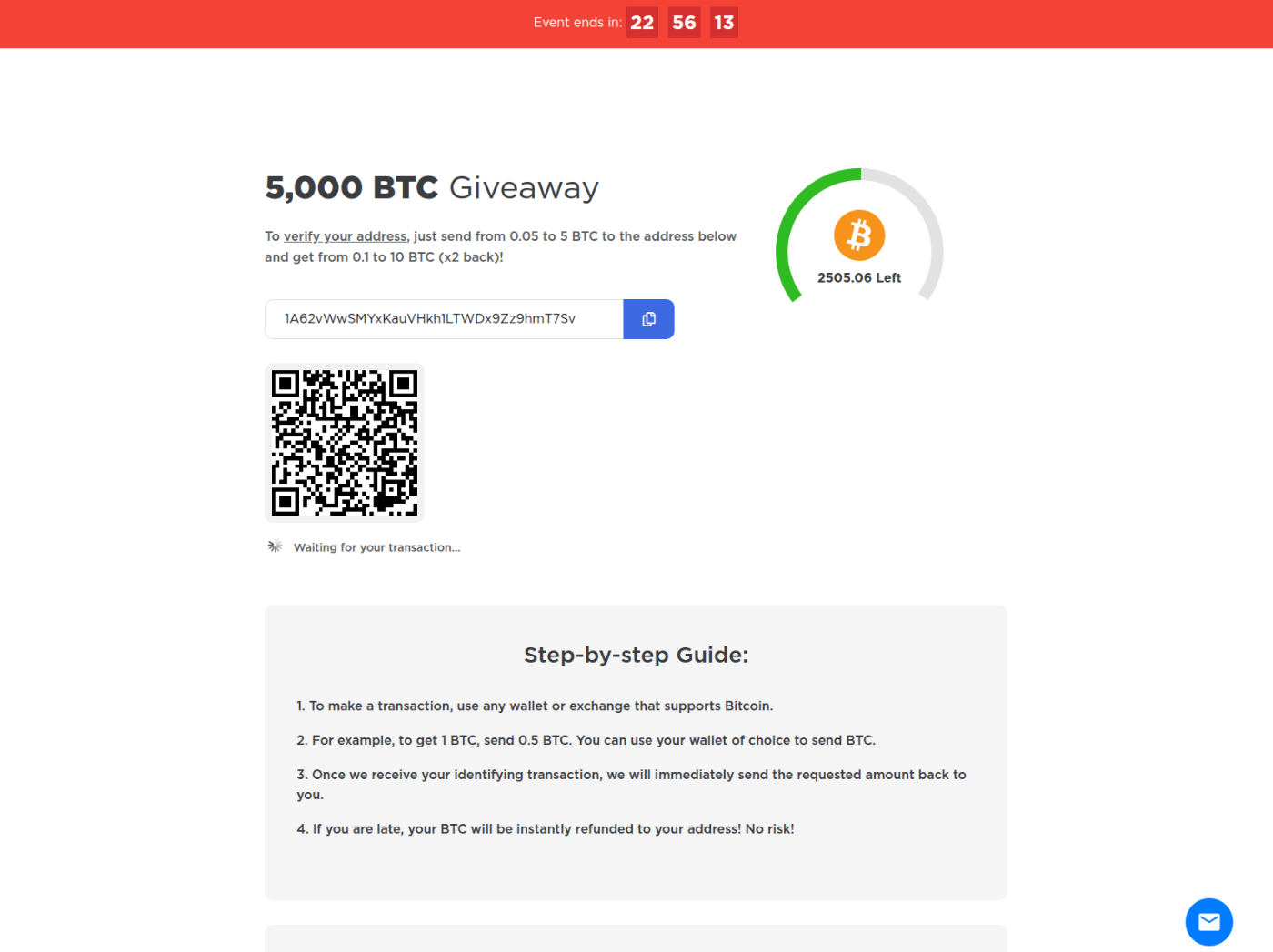
Example: usaevent[.]live with 1musk novelty address variation
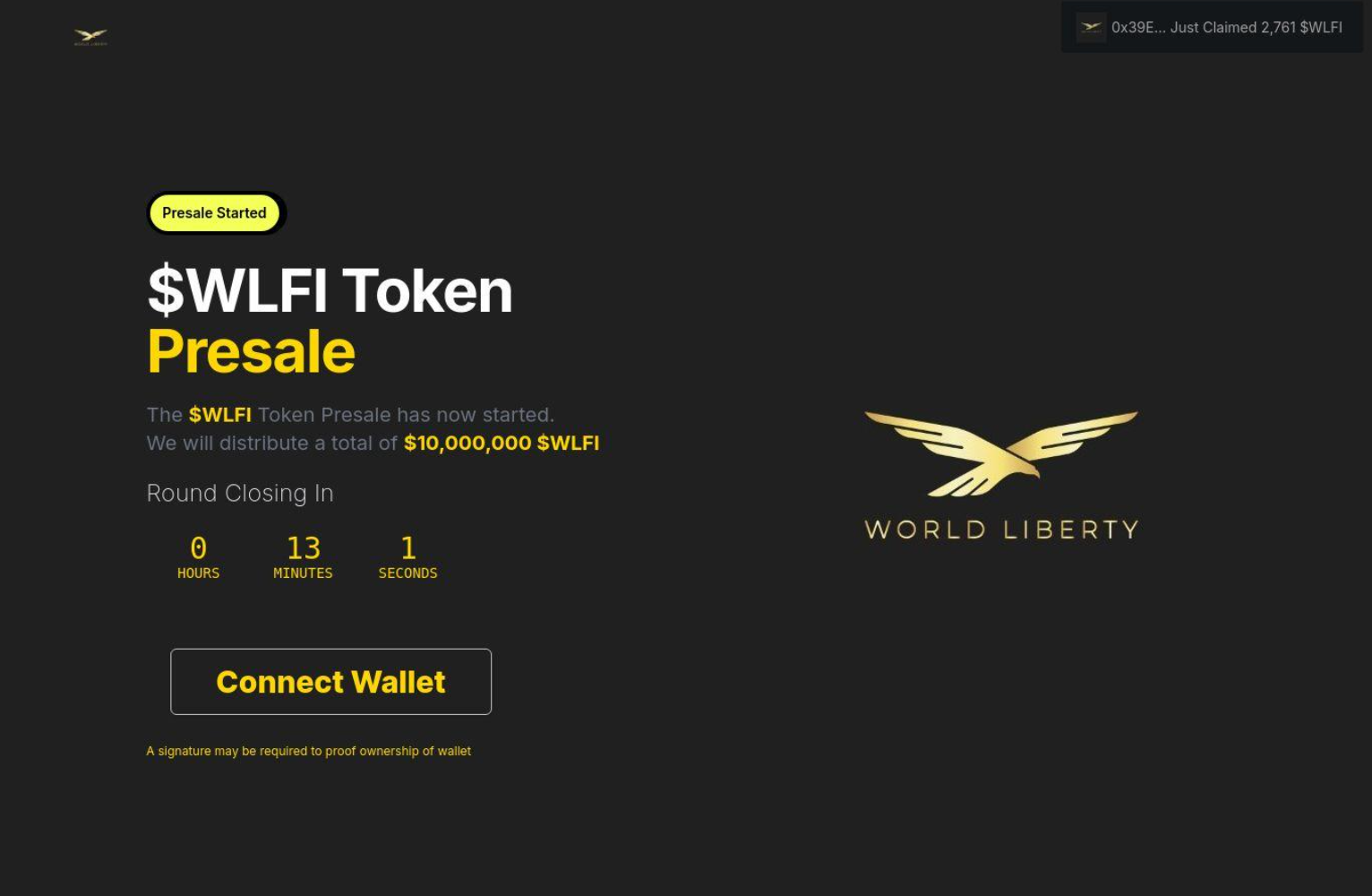
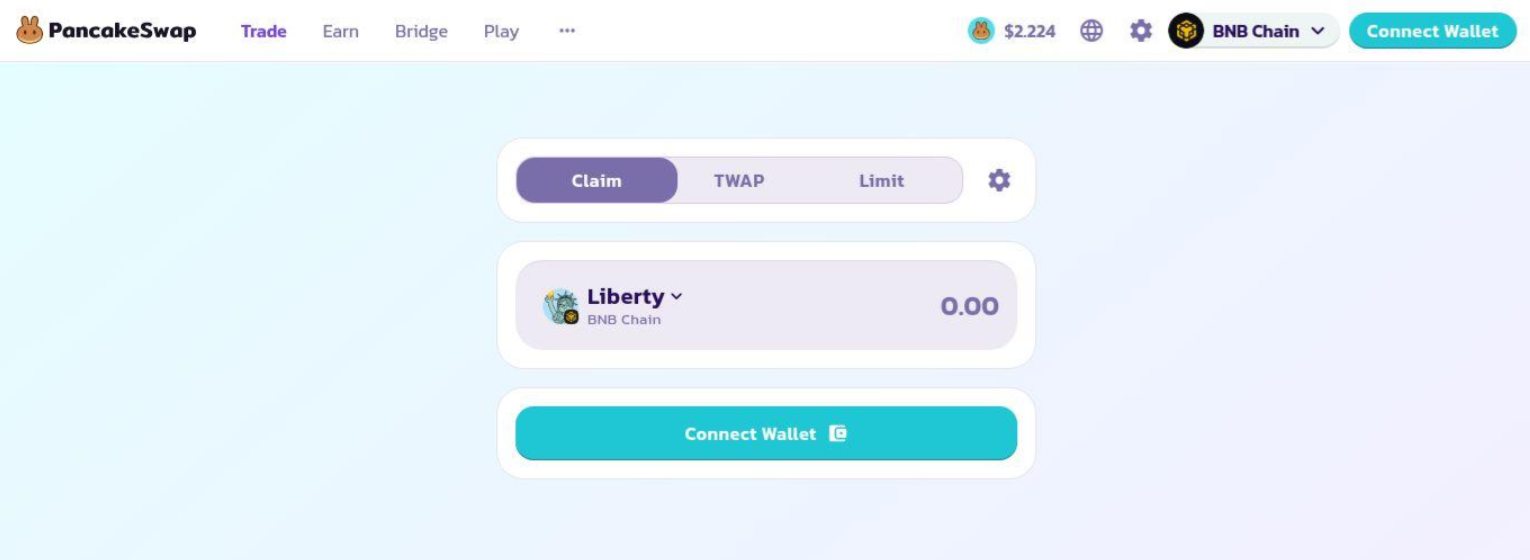
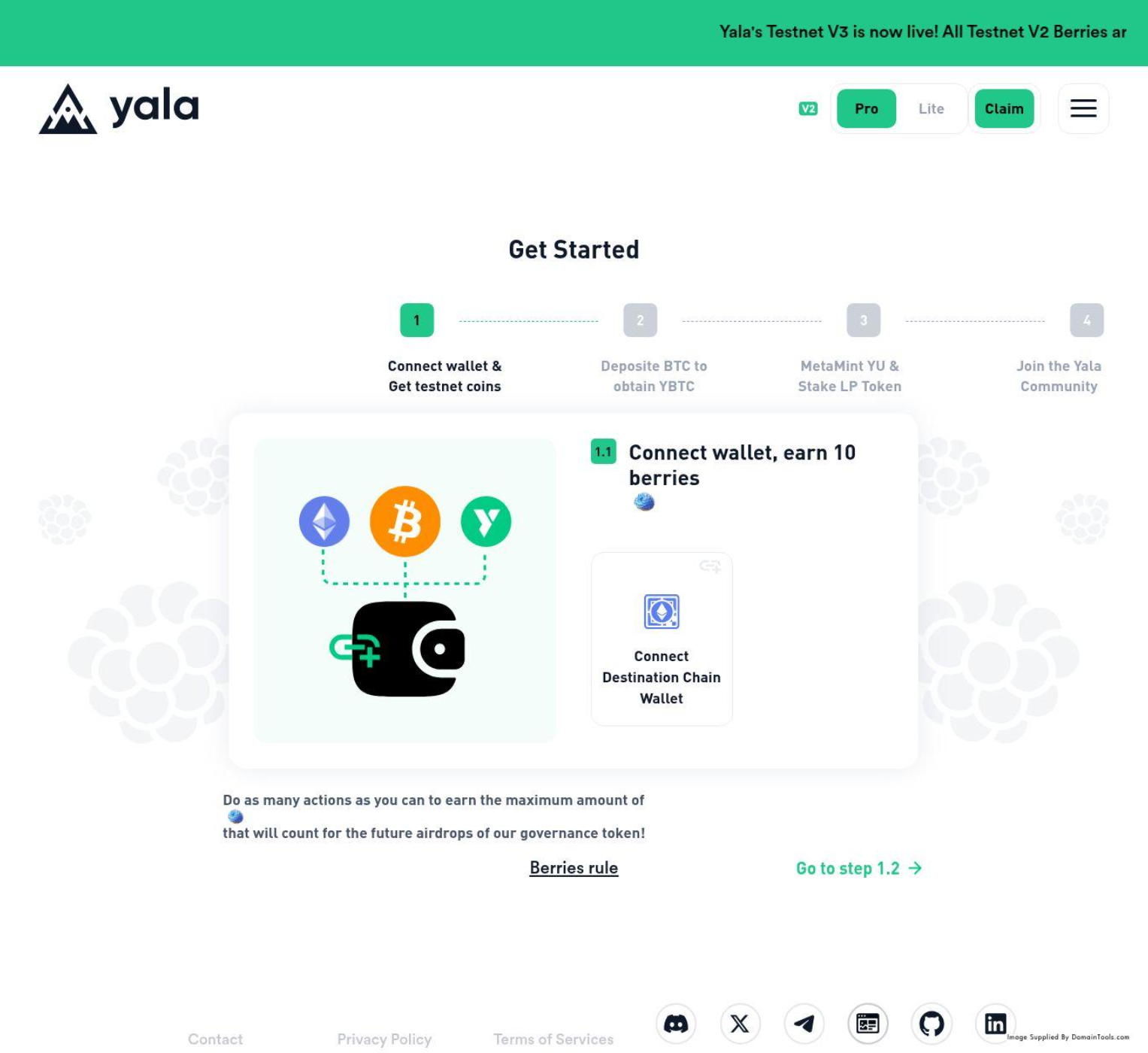
Exchange Spoof / Token Presale Drain Templates:
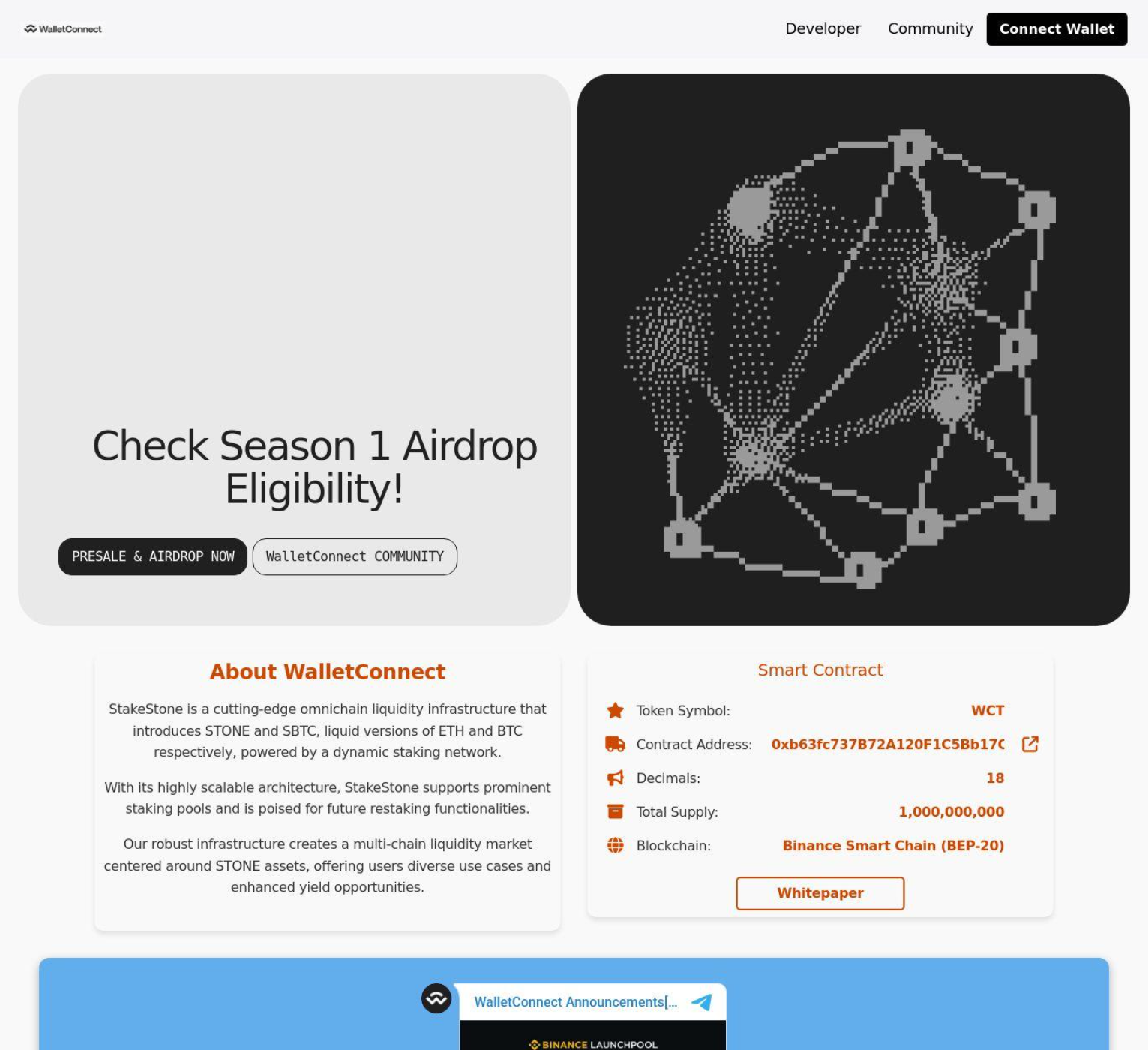
The second style of templates use a less direct transfer style scam approach and instead masquerade as legitimate exchanges. An example is the scam site magaeth[.]bid, which impersonates MegaETH, a real Layer 2 blockchain project, using a cloned website template from bio[.]xyz. Instead of asking victims to manually send crypto, this site connects to their MetaMask wallet and initiates transactions through what looks like a smart contract interaction. Similar to the other templates, these scams also work by using various incentives to trick users into connecting their wallets. They typically appeared to use more dynamically loaded wallet exchanges instead of hardcoding like the other template examples.
The "contract" address in this example (0x134685b581EE7d987c3Caf998CA93CF31BA4Ce10) is just a regular Ethereum wallet, an EOA (Externally Owned Account) with no deployed code on any chain. The following wasn’t fully verified but we suspect the site's JavaScript constructs Web3 contract calls with a full ABI, but when those calls hit the EVM (Etherium Virtual Machine) targeting an EOA, the chain just transfers the ETH (Ether, the native cryptocurrency in Ethereum ecosystem) value and ignores the rest. The victim sees a successful transaction and thinks they bought tokens. In reality, their ETH went straight to the scammer's personal address.
We suspect the site also has two theft mechanisms. One being a presale form that takes whatever amount the victim enters, multiplies by 0.985, and sends it to the scammer. The second being an airdrop withdrawal function that reads the victim's entire wallet balance and sends nearly all of it. If the victim doesn't have enough to be worth draining, the site tells them to deposit more first.
From this scam site, magaeth[.]bid, we suspect there were two victim transactions on Ethereum mainnet totaling 0.1521825 ETH (~$300). Both carried the buyTokens() function selector in their input data, and the first transaction's value (0.0985 ETH) matches exactly what the code would produce from a 0.1 ETH input (0.1 × 0.985). Both senders appear to be real retail users. As of finishing this investigation, the funds haven't been moved.

Expanding
Cluster 1: "X Crypto Giveaway" Template (7 domains)
These sites mimic a crypto exchange giveaway, displaying Elon Musk and/or Donald Trump branding. Victims are told to send crypto to receive double back.
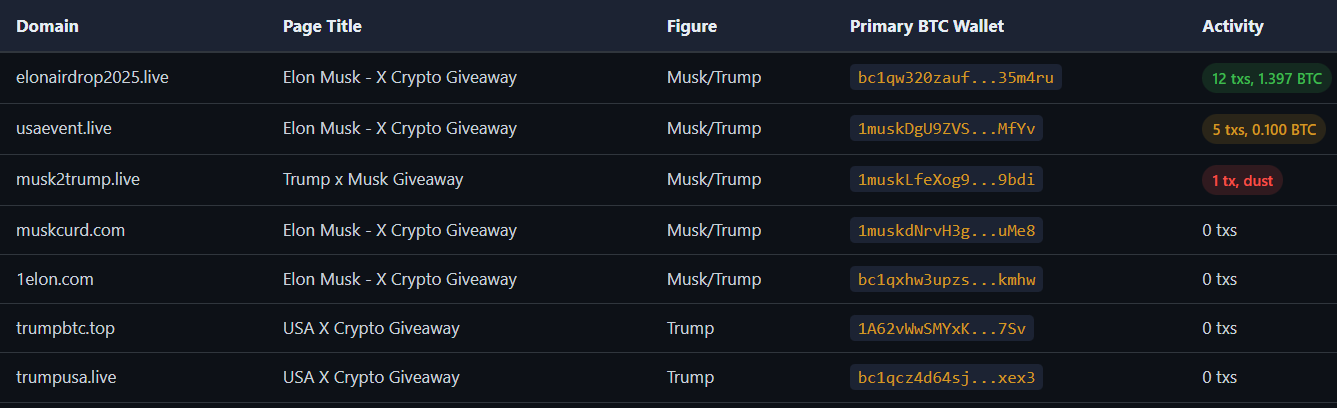
Three wallets use a "1musk" vanity prefix — the actor generated BTC addresses starting with "musk" to reinforce the Elon Musk impersonation. Sites share common decoy addresses in HTML (invalid/truncated strings used as visual filler).
Cluster 2: "Truth Social" Template (4 domains)
Replicate the Truth Social interface with fake posts attributed to Trump about crypto policy or giveaways.
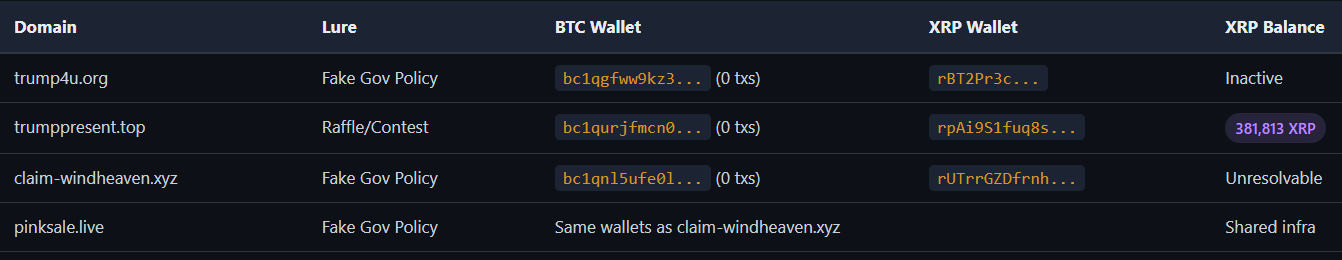
Self-Dealing
Looking up these wallets using open services like blockchain[.]com, we can see transactions to and from the wallet addresses on the scam sites. In some cases it gives the appearance that more than 40k USD worth of transactions had been sent to or from the scammer’s wallets.
Example scammer wallet transaction history:
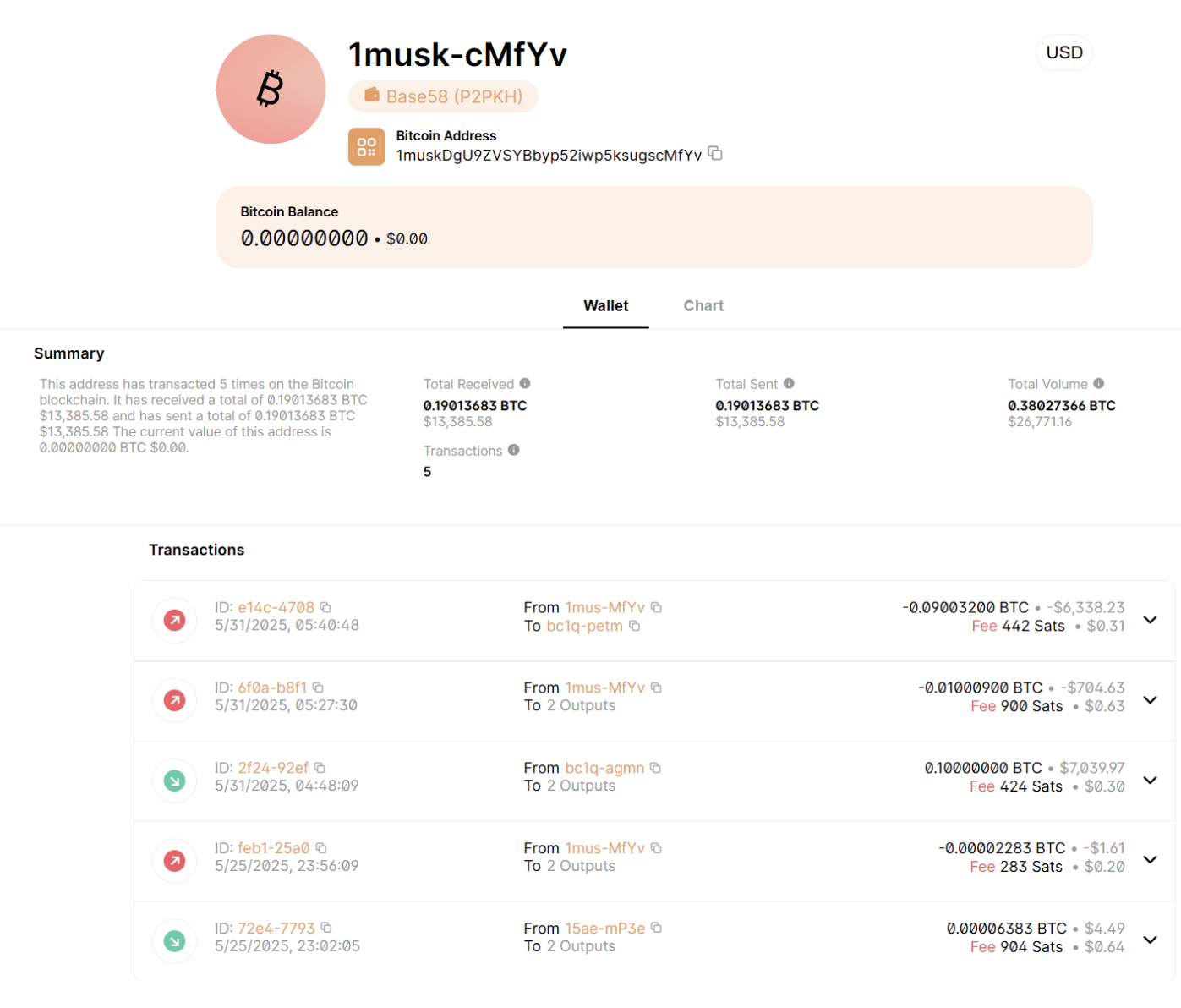
However, on closer inspection in chain analysis, we see these transactions are from wallets likely controlled by the scammer and are intended to trick users into thinking they are legitimate wallets.
Transaction tracing revealed the on-chain BTC activity is the actor sending money to themselves, not real victim payments.
In this example, all recent inbound transactions were from a single sender, rUg8ac5ikpTaWk5RPei8xuYkNEyUs53G1i. Both sender and scam wallet share a parent Binance hot wallet, a wallet that is connected to the internet allowing for fast trading (rDAE53VfMvftPB4ogpWGWvzkQxfht6JPxr, verified binance.com, 115M XRP). The pattern is consistent with self-transfers between Binance sub-accounts used by the scammer.
Chain Analysis
Starting from the scam wallets, funds were traced upstream (funding source) and downstream (drain destinations) through 5 layers of addresses.
Actor Wallet Pipeline:
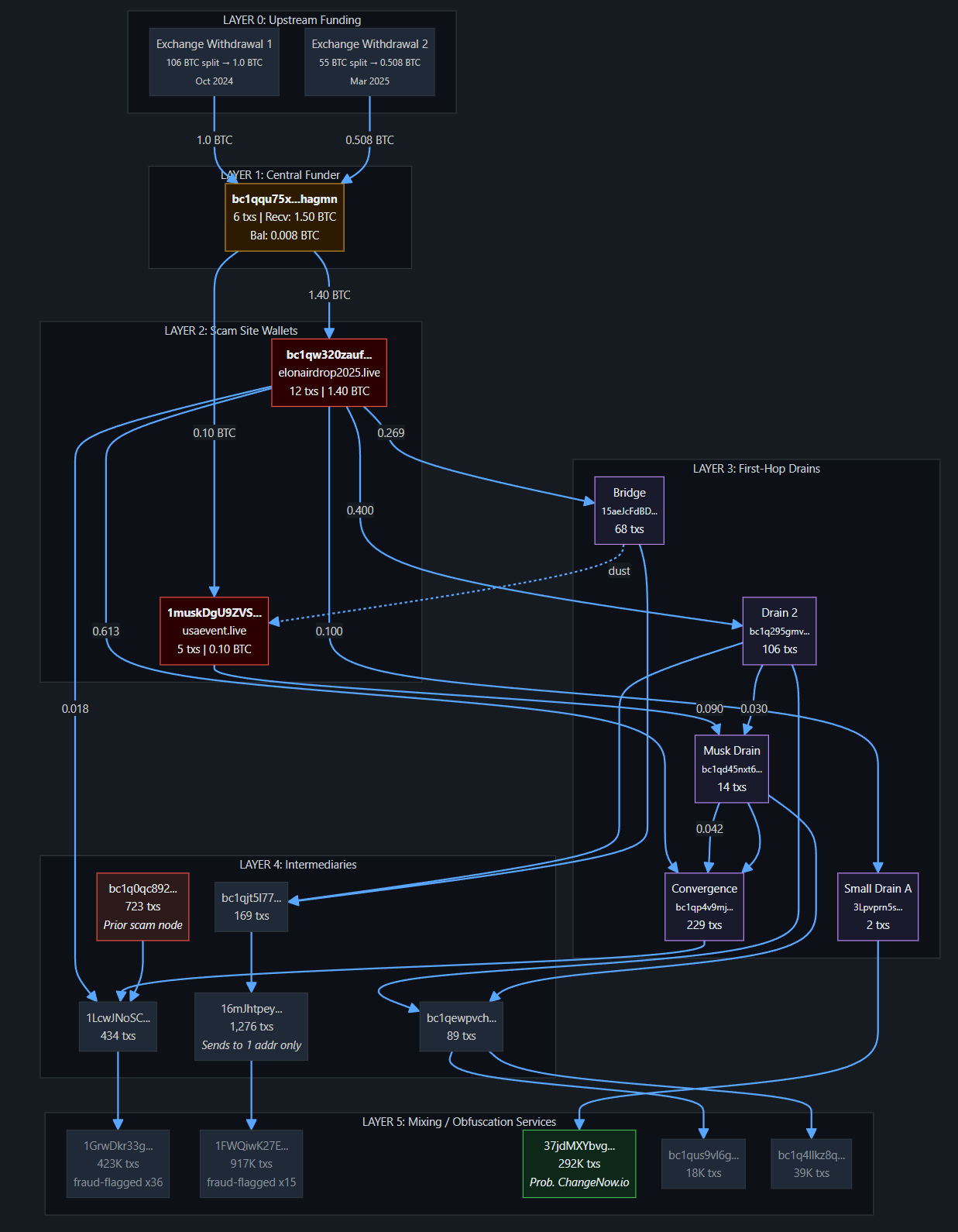
Circular flows: Drain 2 sends to Musk Drain, which sends back to Convergence Drain. Bridge sends back to Drain 2. This tangles the trail.
Bridge cross-link: The dust transaction from Bridge to Scam Wallet 2 is the definitive on-chain proof connecting both scam campaigns.
Prior activity involving what are suspected to be the scammer’s wallets suggests that this pipeline was not built for this one campaign and has considerations for larger scale.
- Convergence drain has 229 txs dating to May 2024.
- Prior scam node bc1q0qc892... has 723 txs (transactions).
- The intermediary, 16mJhtpey…, has 1,276 txs.
Single-destination aggregator: 16mJhtpeyctW... has 1,276 txs but sends to exactly one address. This is either automated or purpose-built for batching before passing to a mixer.
Terminal Destinations (Suspected Mixing/Obfuscation Services)
Network Characteristics
Registration patterns and website configurations had multiple commonalities. A common google analytics tag was used across approximately 50 of the scammer’s sites as well as a registration email address.
Registration Patterns:
Trackers:
- Google:
- G-NK9V3KPEY4
- G-YSMK4G52CC
- G-5Z0ZNNED69
- GTM-PL3G78C
- G-R1QQ1Z50QZ
- G-WRPVL3G32L
- 269367857
- Matomo:
- hxxps://x2025.matomo[.]cloud/
- https://25elon.matomo[.]cloud/
- Hotjar: 4997593
- Statscounter Security: f1980b9f
Emails:
- seunexseun[@]gmail[.]com
- juliambaldwin777[@]gmail[.]com
- ddogenews3[@]gmail[.]com
- diana.lopez88866[@]gmail[.]com
- brainyworld10[@]gmail[.]com
- fsdoplfsdopfsd[@]proton[.]me
- feliciaevanslong777[@]gmail[.]com
- ervins_cudara86[@]outlook[.]com
- konrads_celms30[@]me[.]com
- zanis_latkovska[@]aol[.]com
Website Titles:
- Elon Musk — Official BTC, ETH & DOGE Giveaway!
- Truth Social
- LitEnergy — Official Crypto Event
- NEAR Protocol | Pool Event
- MegaETH | The First Real-Time Blockchain
- Monad | The Most Performant EVM-Compatible Layer 1 Blockchain
- USA X Crypto Giveaway
- Elon Musk — X Crypto Giveaway
- Exchange | PancakeSwap
- Lottery | PancakeSwap
- Hasbulla
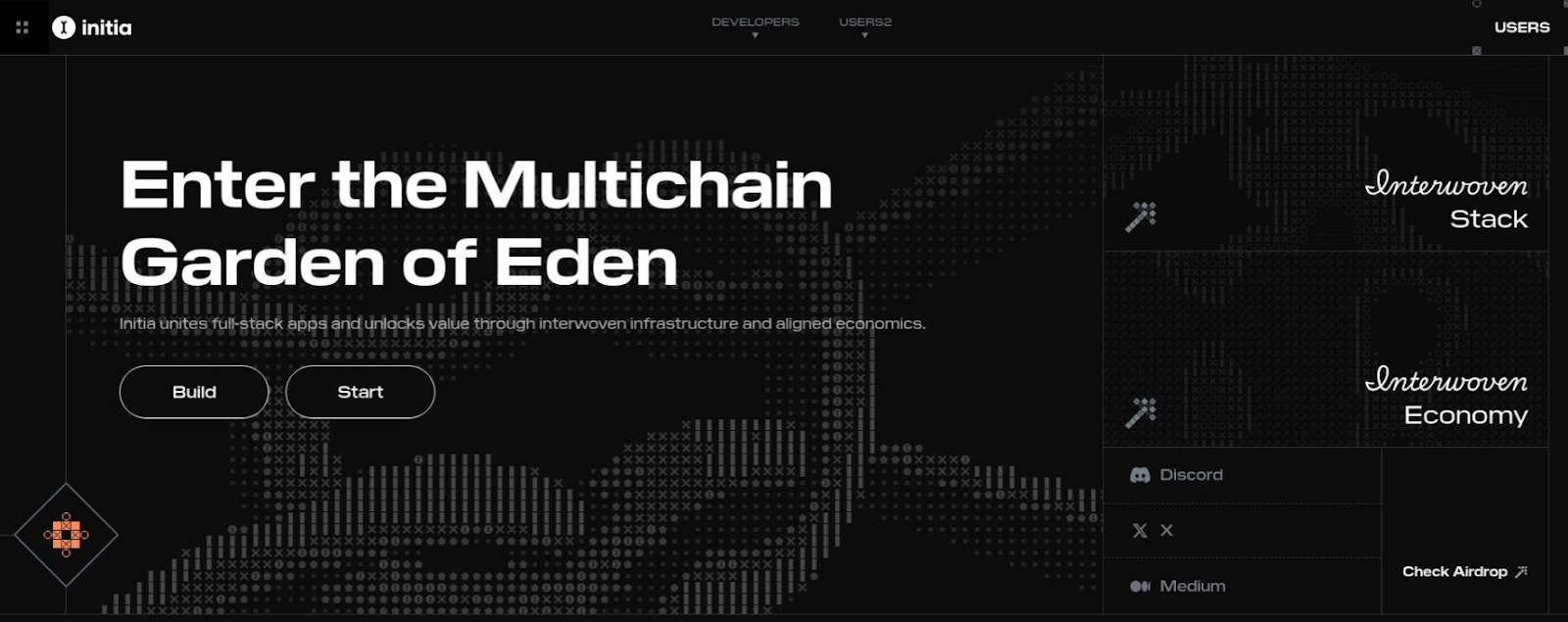
- Initia
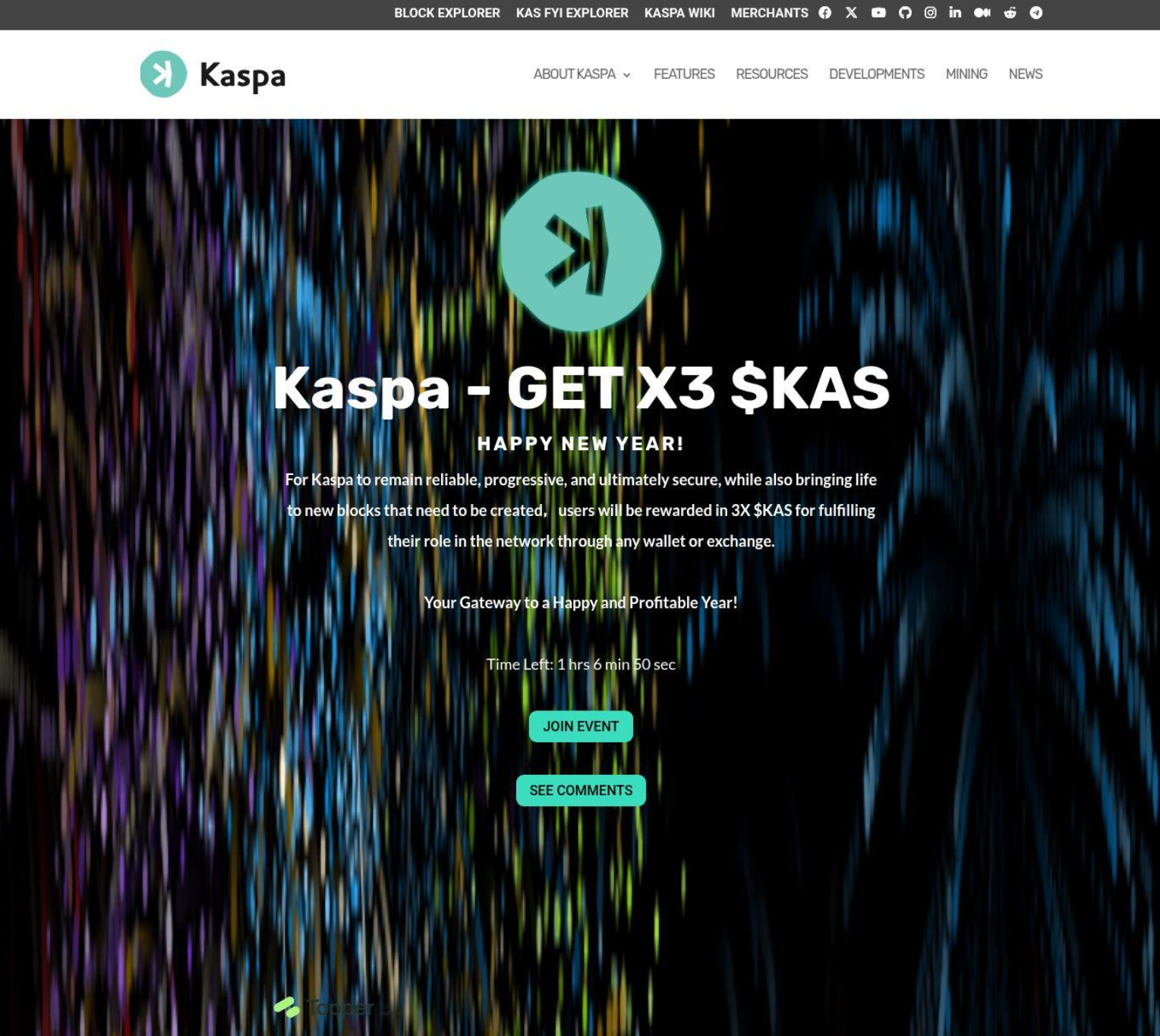
- Home - Kaspa
- Earn and Borrow Crypto | World Liberty Financial
- NEAR Protocol | Pool Event
- BIO Protocol - Listing on Binance Launchpool
- BIO • Home
- Solv Protocol - Stake your Bitcoin today!
- ELSKTRADING | Welcome to ELSK Trading
MX IP: 5.189.161[.]88
The following are screenshot samples of the various scam sites associated with this activity. Notably all are overtly crypto related with one exception, an alleged virtual machine resource for AI Agents that could be “claimed” by applying from the site “avm-code[.]com”. That exception has been taken down by Cloudflare for phishing activity:
Conclusion
This investigation mapped a cryptocurrency scam operation spanning roughly 250 domains, two distinct theme types, and at least 24 actor-controlled wallet addresses across BTC, ETH, and XRP. The operation is suspected of being run by a Russian-speaking actor and has been active since at least January 2025.
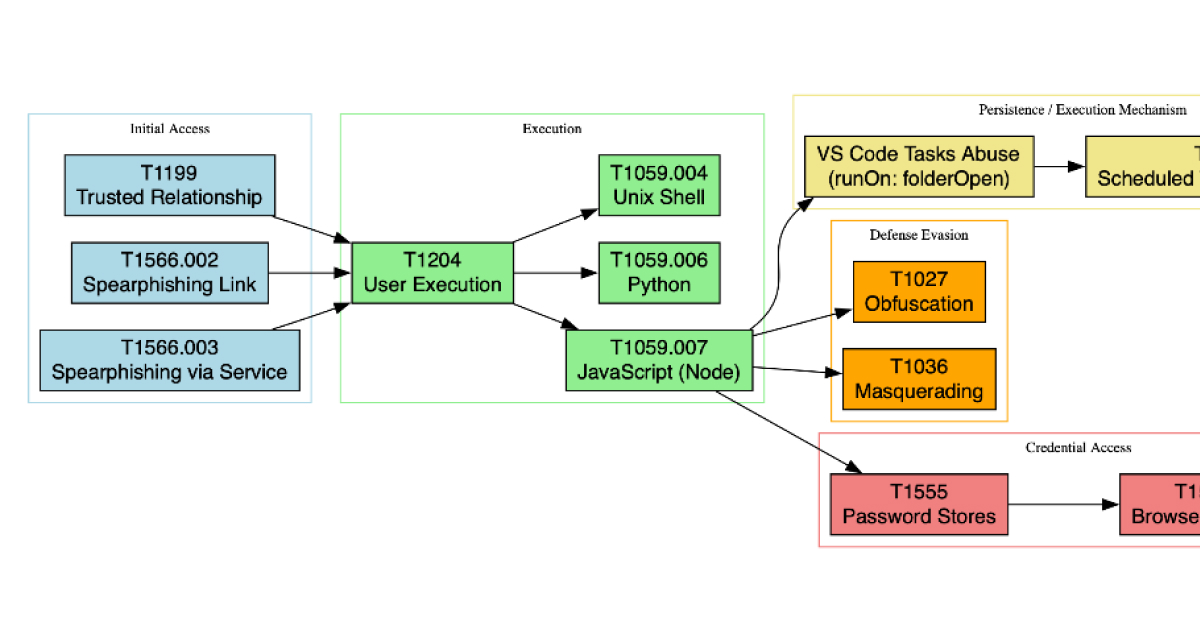
We identified two thematic campaigns linked by a shared Ethereum wallet address and registration pattern overlaps. The first is a broad network of fake giveaway and doubler sites impersonating idolized personalities. Namely Elon Musk, Donald Trump, Truth Social, as well as various crypto projects. It is distributed across three hosting clusters including bulletproof infrastructure. The second consists of more technically advanced fake token presale sites such as megaeth[.]bid, which connects to victims' MetaMask wallets and initiates transactions that look like smart contract interactions but are actually direct transfers to the scammer's personal address.
The on-chain findings were mixed. For the giveaway sites, blockchain tracing showed the actor funding their own wallets from a central source and cycling approximately 1.5 BTC through a multi-layer laundering pipeline ending at high-volume mixing services. We found no confirmed victim deposits in those wallets. For the second themed campaign we ran down a few of the many sites such as megaeth[.]bid site, in which we confirmed two real victim transactions totaling 0.1521825 ETH (~$300). We verified both through function selector matching and value calculation alignment with the scam code. Those funds remain unmoved in the scammer's wallet.
The confirmed financial impact so far from our limited scope of chain analysis is small, roughly $300 from two victims. However, the infrastructure tells a different story. There are hundreds of similar domains over the past year and the identified laundering pipeline has intermediary addresses with hundreds to thousands of transactions dating back to mid-2024, well before the current campaign. The terminal wallets at the end of the chain have transaction counts in the hundreds of thousands and carry multiple fraud flags from independent reporting databases. The actor registered hundreds of domains, set up hosting across multiple jurisdictions, generated vanity Bitcoin addresses, and built scam toolkits that work across Ethereum and Binance Smart Chain. This is not the infrastructure you build for $300. The operation is designed for sustained, repeatable use, and we are most likely seeing a narrow slice of its total activity.
The strongest investigative leads going forward sit outside of blockchain analysis. The Binance sub-account identified behind the 381,813 XRP wallet is a direct path to KYC records. The domain registration and hosting infrastructure, particularly the shared nameservers at streetplug[.]me and the EuroByte hosting cluster, could yield registrant details. Commercial chain analysis tools (Chainalysis, Elliptic) would likely have attributions for the terminal mixing wallets that our open-source methods couldn't resolve. The blockchain trail itself, by design, ends at services built to break traceability.
What we can say with confidence: a single actor controls both campaigns, uses Russian-language code artifacts, operates from infrastructure that spans France, Russia, and UK-based bulletproof hosting, and has built a wallet pipeline capable of handling significantly more volume than what we observed. The two confirmed victims on megaeth[.]bid are likely real people, one funded from Coinbase, the other a multichain DeFi user, who lost money to a scam disguised as a legitimate blockchain project. There are almost certainly more.