“The old world is dying, and the new world struggles to be born; now is the time of monsters” - so spoke Italian political theorist Antonio Gramsci nearly one hundred years ago. Or, to be more accurate, around 1930 Gramsci wrote:
La crisi consiste appunto nel fatto che il vecchio muore e il nuovo non può nascere: in questo interregno si verificano i fenomeni morbosi piú svariati.
which has been translated directly as:
The crisis consists precisely in the fact that the old is dying and the new cannot be born; in this interregnum a great variety of morbid symptoms appear.
The vigilance of defenders and investigators often focuses on monsters, typically ones easy to classify and thus easy to articulate wins to management.
What would our industry look like if instead, we triaged the morbid symptoms of our environments, of our systems? Fighting dragons feels more satisfying than covering fundamentals. How do we frame the problem, get exec on-side, but more importantly, how do we continue to motivate ourselves in a world so seemingly full of morbid symptoms, most outside our control?
Answers usually don’t survive first contact with reality. For my part, I fall back on a mindfulness of effort. As I plan and execute, my work of 2026 includes asking myself over and over, “Am I chasing monsters, or is there an underlying morbid symptom here that means monsters spawn less, or elsewhere?”
By the way, this is a discussion on impact.
Articles
- DefenseOne - AI may revive old-school tradecraft even as it transforms intelligence work - ‘“My view,” he said, “is that [HUMINT] will have to have a human element — a real, essential human element — for the foreseeable future.”’
- HivePro - ClipXDaemon Clipboard Attack: Linux Malware Targeting Crypto Payments - May not be the first linux clipboard stealer out there, but it’s the first I can remember seeing.
- AWS Security - Amazon threat intelligence teams identify Interlock ransomware campaign targeting enterprise firewalls - Really glad to see AWS Security taking advantage of their scale and scope to deploy honeypots and sharing the results; in this case, a Cisco FMC 0day. Good intermix of technical and human behaviors here to create an operational profile.
- GTIG - The Proliferation of DarkSword: iOS Exploit Chain Adopted by Multiple Threat Actors - Great collaboration between GTIG, iVerify, and Lookout. The convergence of Coruna and DarkSword, especially around UNC6353, is something to watch.
- Kentik - Internet and Airstrikes: Tracking Iran's Extended Communication Blackout - This is a deeply interesting post to me. Unsurprisingly, we’ve got a good vantage point for internet visibility, and are still working with data from 2/28 onward to better understand what’s taking place. There’s substantial value in being able to visualize negative space, though this is often forgotten amidst the rush to categorize the seen instead.
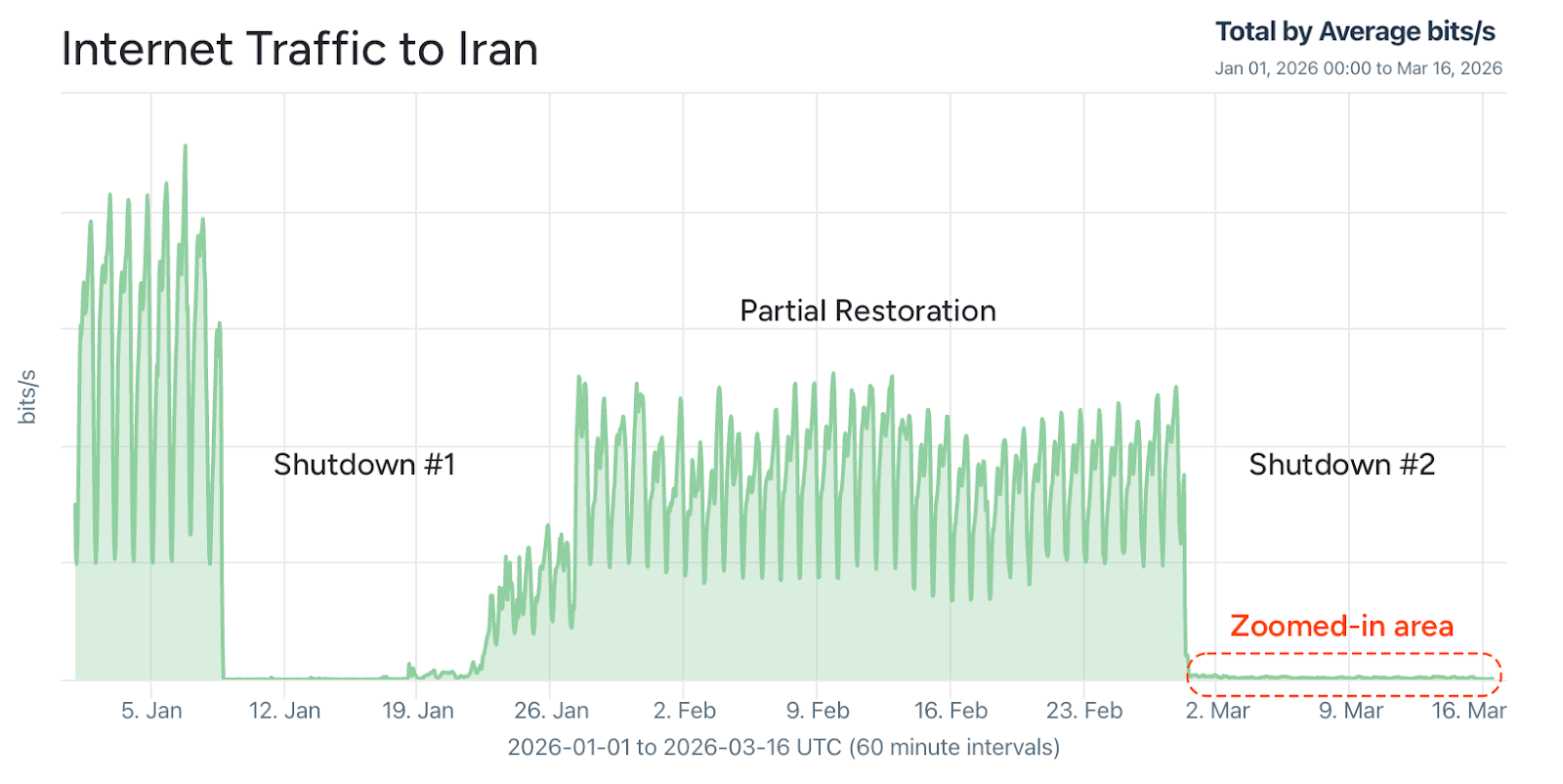
Image above from Kentik post identifying distinct shutdown phases.
We’ve been busy little gremlins, recently, and our ability at DomainTools Investigations to remain timely and relevant despite being a scrappy little team continues to make me deeply proud. From us over the past month or so:
- DTI - Doppelgänger / RRN Disinformation Infrastructure Ecosystem 2026 - One of the pieces I’m most proud of across the past year and a half.
- DTI - DPRK Malware Modularity: Diversity and Functional Specialization - Our industry does well at analyzing individual malware strains. What if we looked at a more holistic picture, though? What if we looked at all the current tracks together, what would it tell us?
- DTI - CloudFlare Anti-Security For Phishing - Shorter piece on some veeeery interesting anti-analysis technicals amidst a larger phishing campaign.
- DTI - OpenAI Anti-Ads Malware - That browser plugin offering to block ads server by OpenAI’s free tier might not be as convenient as you think it is…
- DTI - Exposure of TLS Private Key for Myclaw 360 in Qihoo 360 “Security Claw” AI Platform - We managed to work this up and put it out there within about three days of exposure, and it’s a great set of lessons, from source and scope validation to what the risk of AI looks like for most folks here, as well. And then it flared here, in a different way, last week: OpenClaw’s 8.6 sev CVE allowing any paired entity to escalate privileges without authentication. That’s likely to lead to quite a lot of downstream pain.
Research Papers and Reports
- Mandiant - M-Trends 2026 Report - Breach methodology. Given Mandiant’s front seat at many campaigns these days, very worth diving into.
- ODNI - 2026 Annual Threat Assessment of the U.S. Intelligence Community - Always worth reading, but to be read in-context like any other public product. Perception and messaging as much as content.
Tools and Resources
- Elastic Security Labs - Supply Chain Monitor - accompanying blog post about its visibility on the Axios attack - We’re starting to see some more creative uses of AI by defenders, for which I am grateful. Nowhere near the advantage it appears to give attackers, but I’ll take what progress I can get.