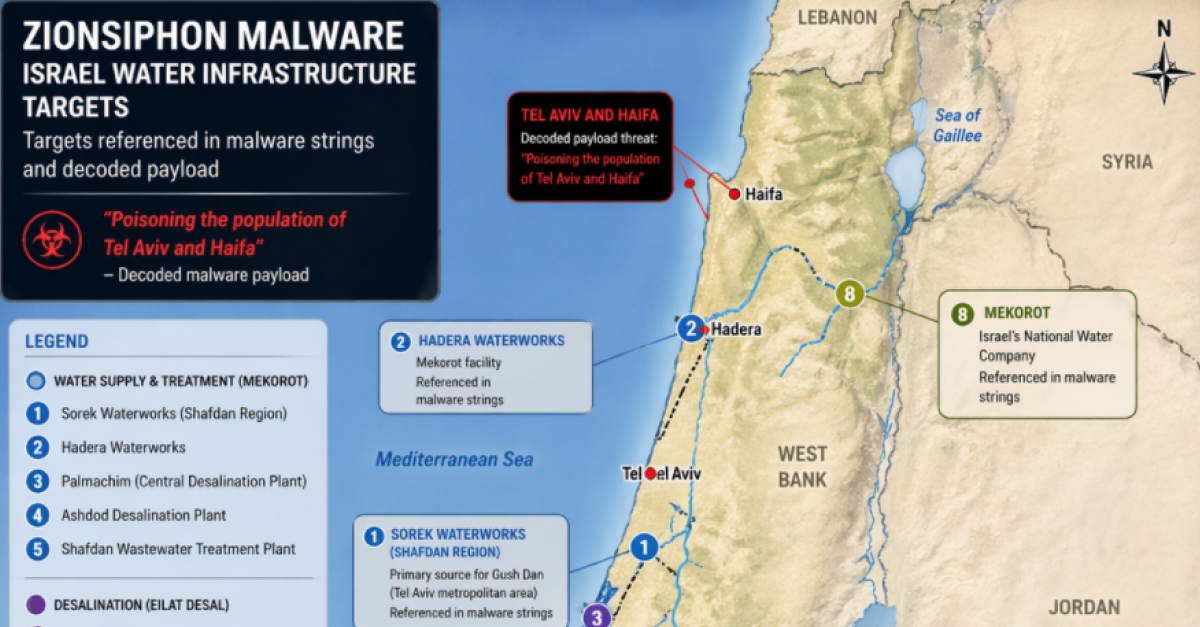
Analysis of ZionSiphon (SCADA_SecurityPatch_v8.4.exe), a .NET OT malware targeting Israeli water utilities. Discover its IOCs, targets, and flawed activation code.
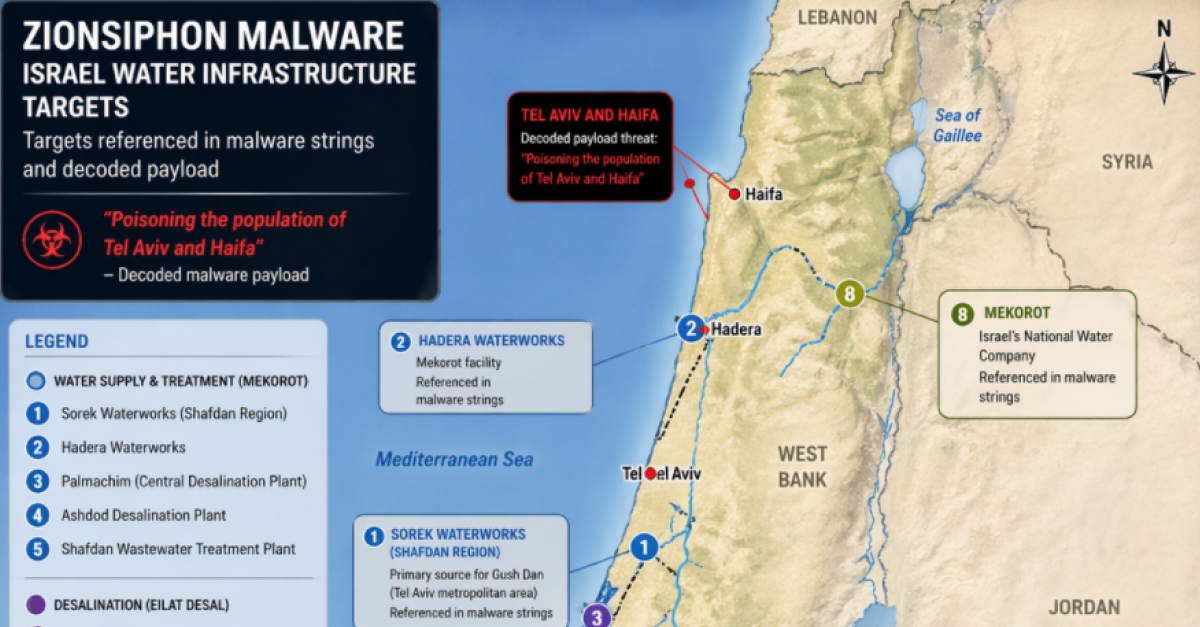
Analysis of ZionSiphon (SCADA_SecurityPatch_v8.4.exe), a .NET OT malware targeting Israeli water utilities. Discover its IOCs, targets, and flawed activation code.
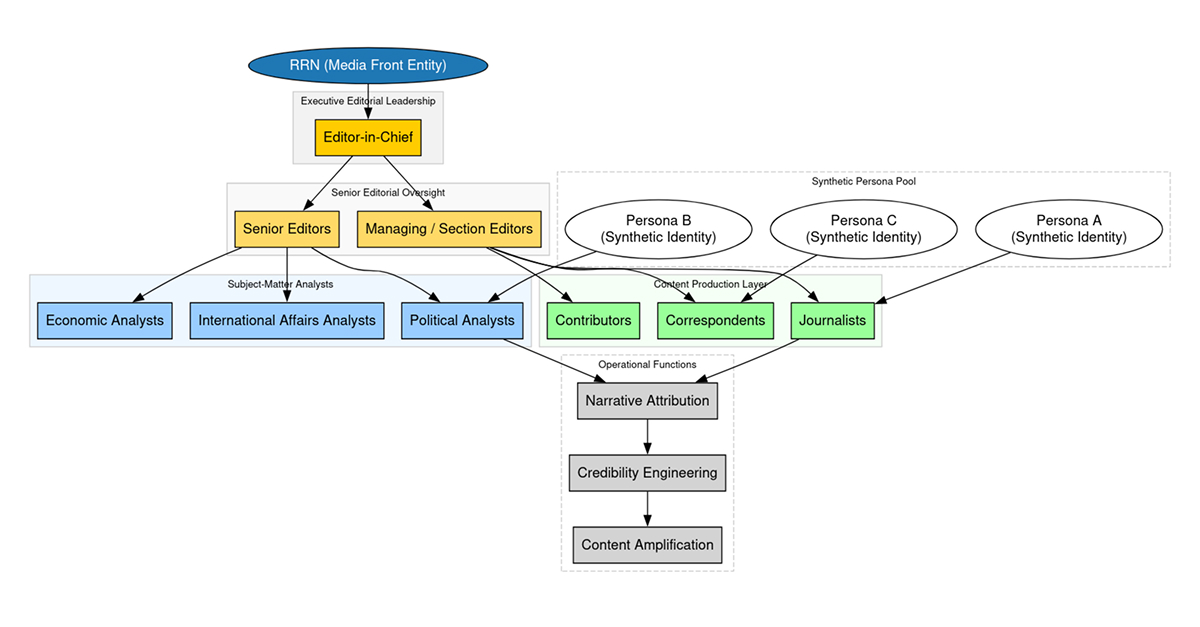
How does the Doppelgänger influence campaign reach 5M+ users? Read DTI’s latest report on the SDA/Structura ecosystem, featuring a deep dive into narrative propagation, domain rotation tactics, and a 72-hour crisis influence timeline.
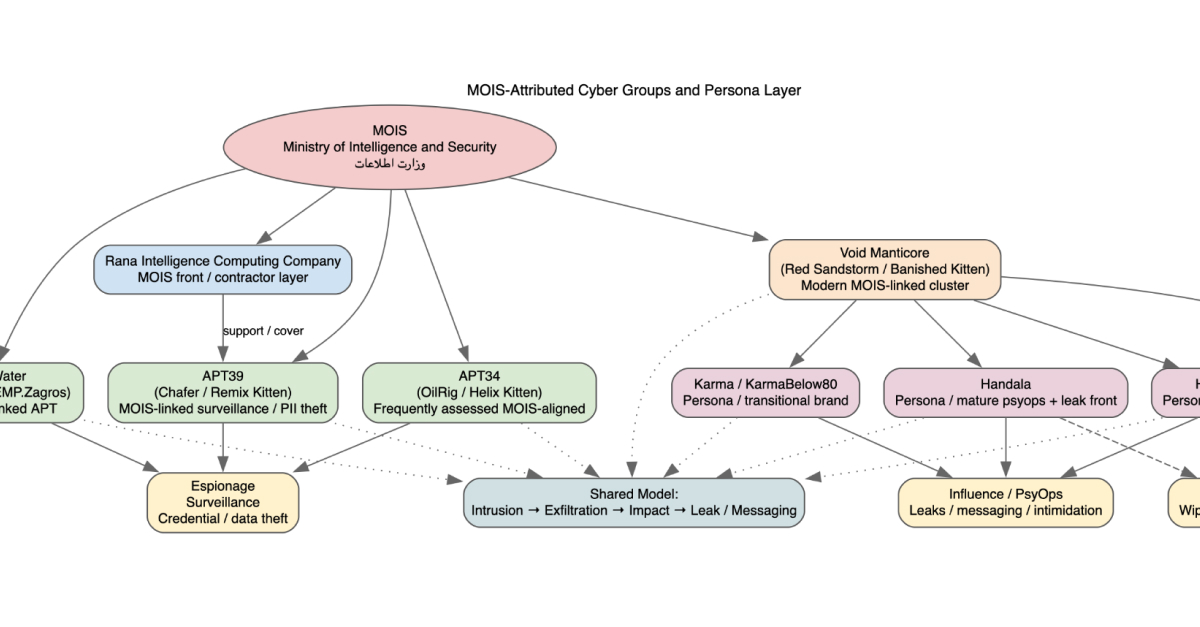
Explore the evolution of MOIS-linked actors Homeland Justice, Karma, and Handala. Analysis of destructive malware, surveillance integration, and the 2026 Stryker incident.

Commentary followed by links to cybersecurity articles and resources that caught our interest internally.
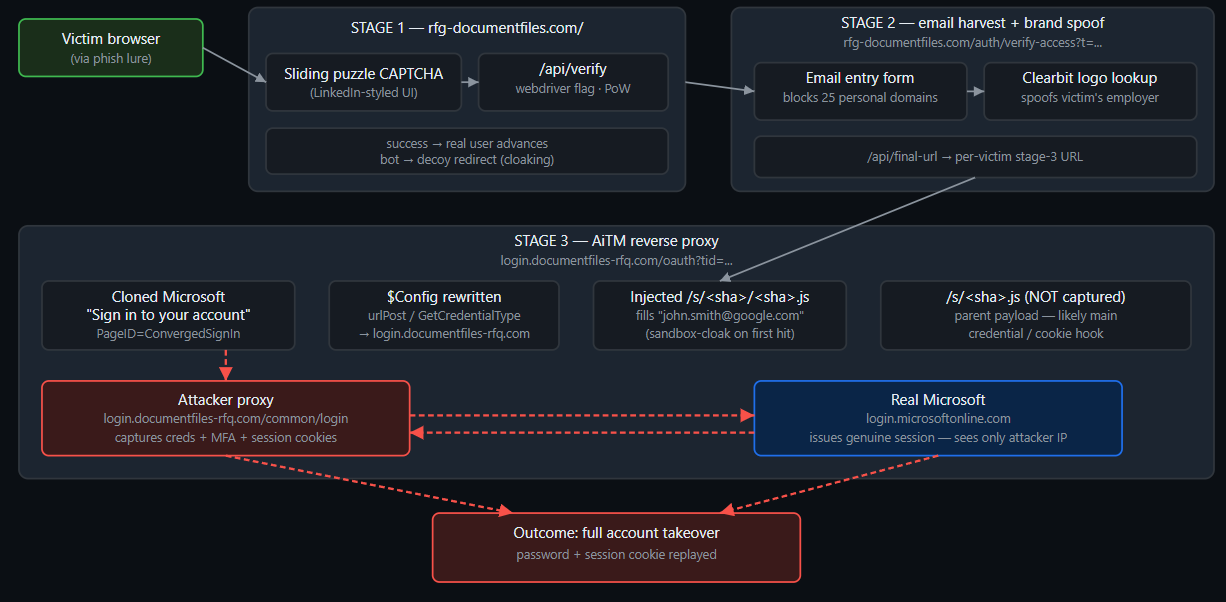
A sophisticated AiTM phishing kit bypassing traditional MFA to steal Microsoft 365 session cookies. Get the full breakdown and IOCs.

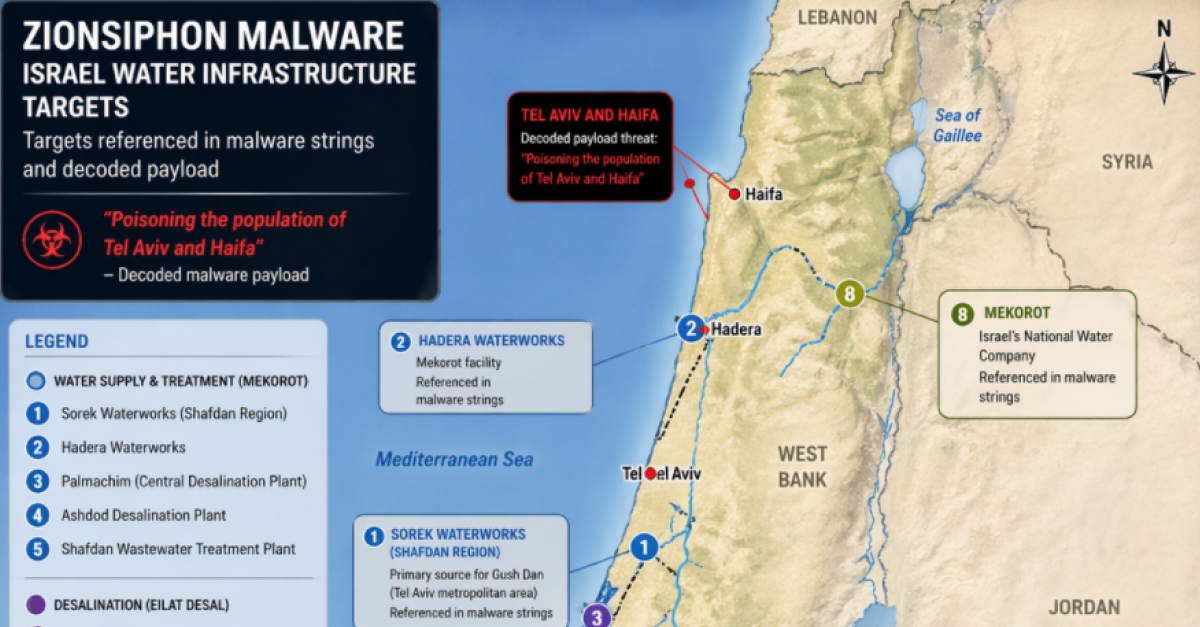
Analysis of ZionSiphon (SCADA_SecurityPatch_v8.4.exe), a .NET OT malware targeting Israeli water utilities. Discover its IOCs, targets, and flawed activation code.
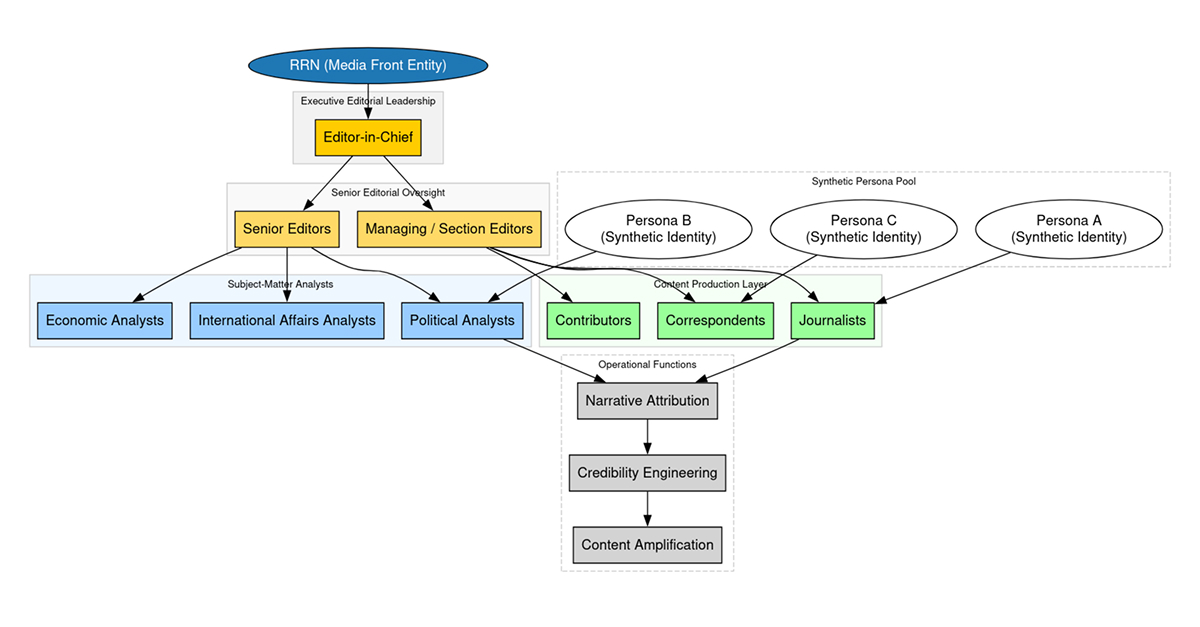
How does the Doppelgänger influence campaign reach 5M+ users? Read DTI’s latest report on the SDA/Structura ecosystem, featuring a deep dive into narrative propagation, domain rotation tactics, and a 72-hour crisis influence timeline.
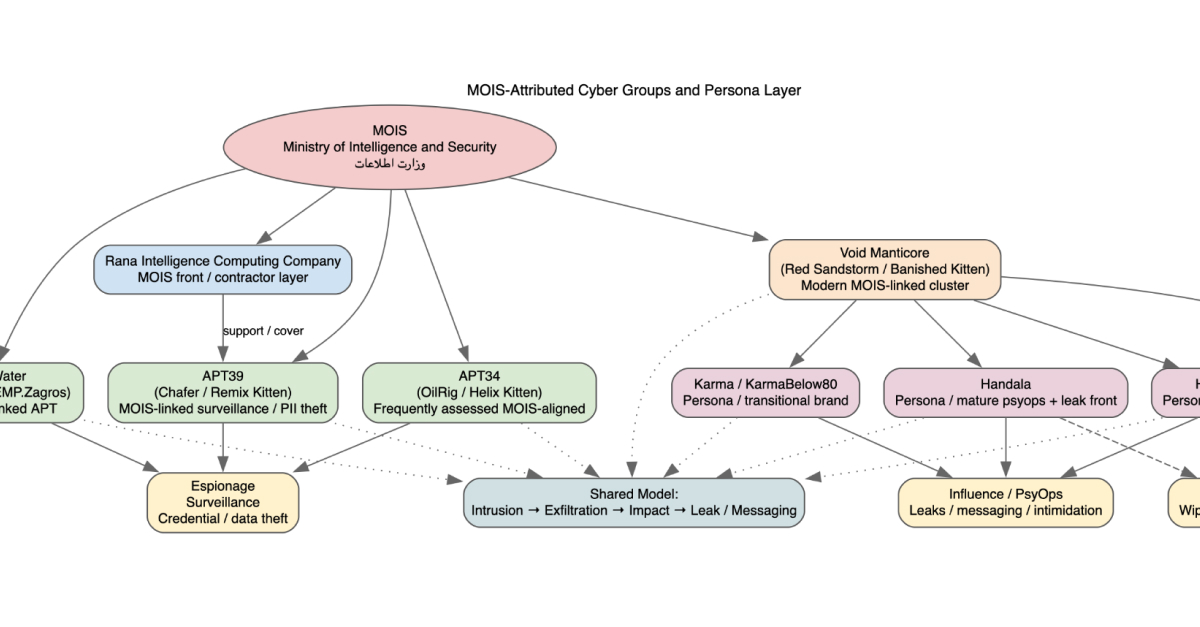
Explore the evolution of MOIS-linked actors Homeland Justice, Karma, and Handala. Analysis of destructive malware, surveillance integration, and the 2026 Stryker incident.

Commentary followed by links to cybersecurity articles and resources that caught our interest internally.
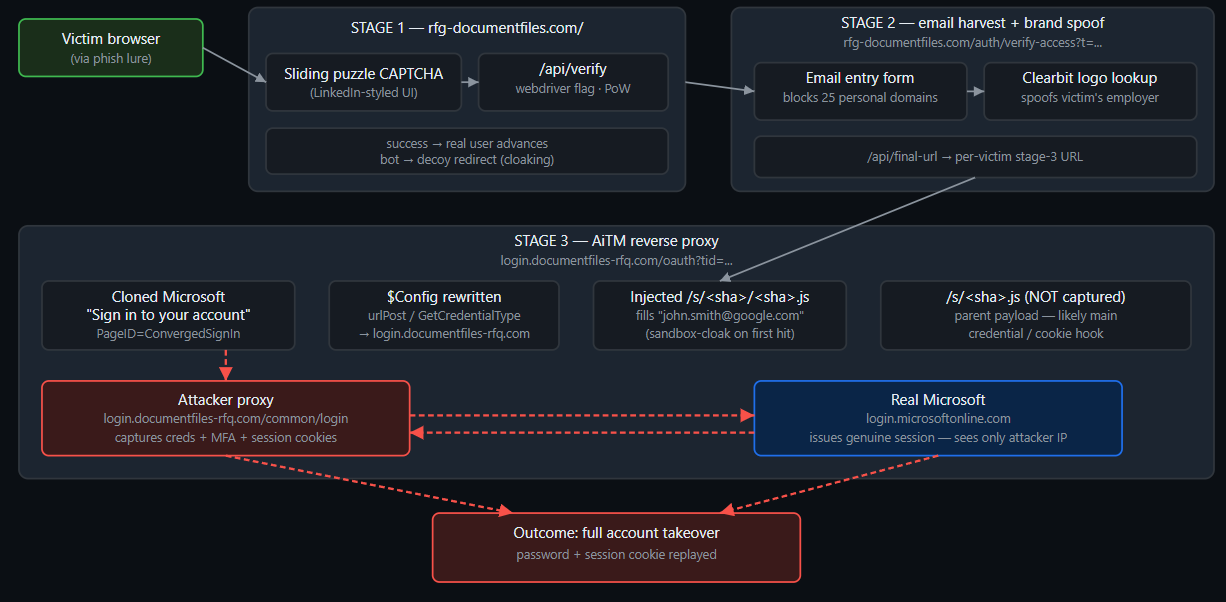
A sophisticated AiTM phishing kit bypassing traditional MFA to steal Microsoft 365 session cookies. Get the full breakdown and IOCs.

Systems thinking, biolistics, and the danger of mop-up science in infosec — plus this month's reading on ransomware, RPKI exploits, cPanel, and LLM pollution.