Executive Summary
North Korea’s cyber program has evolved into a deliberately fragmented malware ecosystem, optimized for mission specialization, operational resilience, and attribution resistance. Analysis of multiple vendor, government, academic, and secondary reporting confirms that what appears externally as a “fracture” is, in practice, a mature portfolio model: parallel malware development pipelines aligned to discrete strategic objectives.
This structure enables the DPRK to conduct simultaneous espionage, revenue generation, and disruptive operations without cross-contaminating tooling, infrastructure, or exposure. Compartmentalization and diversity is therefore assessed as a feature of program maturity, not decentralization or degradation.
Strategic Drivers
The current compartmentalization and diversity of North Korea’s malware ecosystem is not an accidental byproduct of growth or internal disorder; it is a rational response to sustained and cumulative strategic pressure. Over more than a decade, international sanctions have progressively constricted the regime’s access to hard currency, elevating cyber operations from an auxiliary intelligence function to a core mechanism of economic survival. At the same time, increasingly coordinated law-enforcement actions and intelligence disclosures have reduced the lifespan of individual campaigns, forcing DPRK operators to assume that any exposed tool, infrastructure cluster, or technique will eventually be neutralized.
This pressure has been compounded by the repeated public exposure of specific malware families and campaign narratives. Once-effective tools are now rapidly fingerprinted, attributed, and disseminated across defensive communities, collapsing their operational utility. Parallel to this, target environments particularly in finance, technology, and government have become more defensively mature, with improved telemetry, faster incident response cycles, and greater cross-sector information sharing. In aggregate, these factors have raised the cost of persistence and reduced the viability of monolithic, long-lived malware platforms.
In response, the DPRK has adapted by restructuring its cyber program around principles of resilience rather than longevity. Malware development and operations are increasingly compartmentalized, both technically and organizationally, ensuring that exposure in one mission area does not cascade across the entire program. Toolchains are treated as consumable assets: designed to be burned, replaced, and reconstituted with minimal strategic loss. This loss-tolerant posture enables multiple teams to operate in parallel, pursuing espionage, revenue generation, and disruptive objectives simultaneously without competing for the same infrastructure or codebase.
Crucially, this model also maximizes ambiguity. By separating tooling, infrastructure, and operational patterns along mission lines, the DPRK complicates attribution and slows defender decision-making. What emerges is not compartmentalization and diversity as weakness, but compartmentalization and diversity as control: a cyber apparatus engineered to absorb pressure, survive exposure, and continue functioning even as individual components are repeatedly stripped away.
Compartmentalized Malware Architecture
Espionage Oriented Malware Track
The espionage-oriented malware track represents the most traditional and strategically conservative pillar of the DPRK cyber program. Its purpose is not disruption or immediate financial return, but the quiet, sustained extraction of intelligence from institutions that shape policy, security planning, and strategic decision-making. Targets are selected for their informational value rather than their economic utility, encompassing government ministries, defense contractors, academic research centers, think tanks, and organizations operating at the margins of policy formation.
Operations within this track are characterized by restraint and patience. Activity is deliberately low-noise, with operators prioritizing extended dwell time over rapid exploitation. Initial access is leveraged to establish durable footholds that enable credential harvesting, mailbox surveillance, and systematic document collection. Once embedded, the objective is to observe, monitor, and siphon information continuously, often for months or years, with minimal operational disruption to the victim environment. Destructive actions and monetization are intentionally avoided, as they increase detection risk and prematurely terminate access.
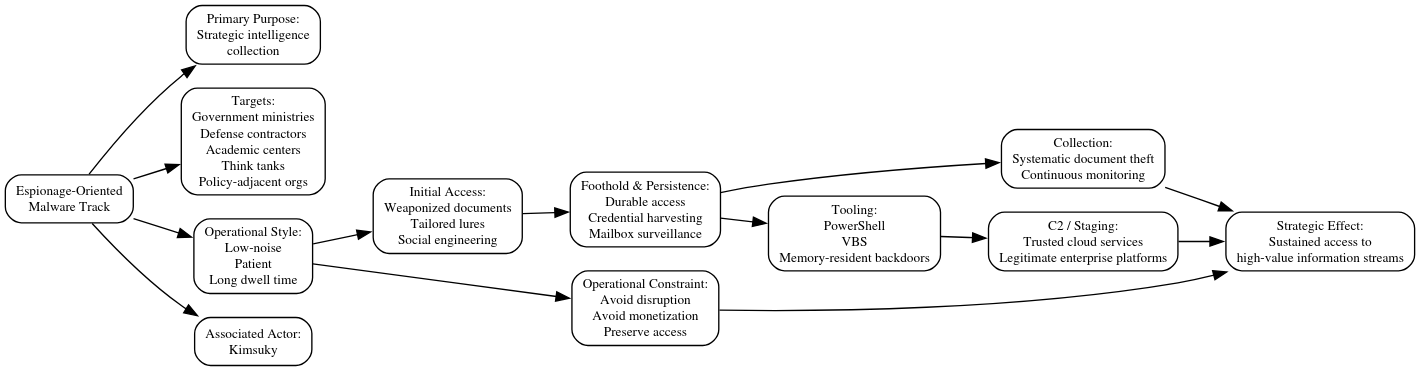
Technically, this restraint is reflected in the tooling. Malware associated with espionage missions favors script-heavy loaders, most commonly PowerShell or VBS that blend into normal administrative activity and reduce the need for large, easily detected binaries. Backdoors are frequently memory-resident, minimizing on-disk artifacts and complicating forensic recovery. Initial access commonly relies on weaponized documents or carefully crafted lures tailored to the professional context of the target, reinforcing the emphasis on social engineering over exploit development.
Once access is established, trusted cloud services are routinely abused for command-and-control and staging. By operating through platforms already embedded in enterprise workflows, operators obscure malicious traffic within legitimate usage patterns and benefit from the implicit trust afforded to major service providers. This approach further reduces operational noise while extending persistence in environments with increasingly mature perimeter defenses.
This espionage track is most commonly associated with Kimsuky, which has long been assessed as a primary intelligence-collection component within the DPRK cyber ecosystem. Its campaigns exemplify the regime’s preference for slow, methodical access to high-value information streams, reinforcing the view that espionage remains a foundational mission even as financial and disruptive cyber operations expand alongside it.
Financial Operations Malware Track
The financially oriented malware track reflects the most adaptive and economically consequential arm of the DPRK cyber program. Its overriding purpose is revenue generation: converting access into currency in order to blunt the effects of international sanctions and directly fund regime priorities, including strategic weapons development. Unlike espionage operations, success in this track is measured not in persistence or insight, but in speed, scale, and yield.
Operations in this category are characterized by a markedly faster tempo. Campaigns are designed to move quickly from initial access to monetization, accepting shorter dwell times and higher exposure risk in exchange for financial return. Targeting is broad and opportunistic, with a pronounced focus on cryptocurrency exchanges, blockchain developers, decentralized finance platforms, and the software supply chains that underpin them. Rather than selecting victims for their strategic influence, operators select ecosystems where a single compromise can yield outsized financial gain or cascade into downstream access.
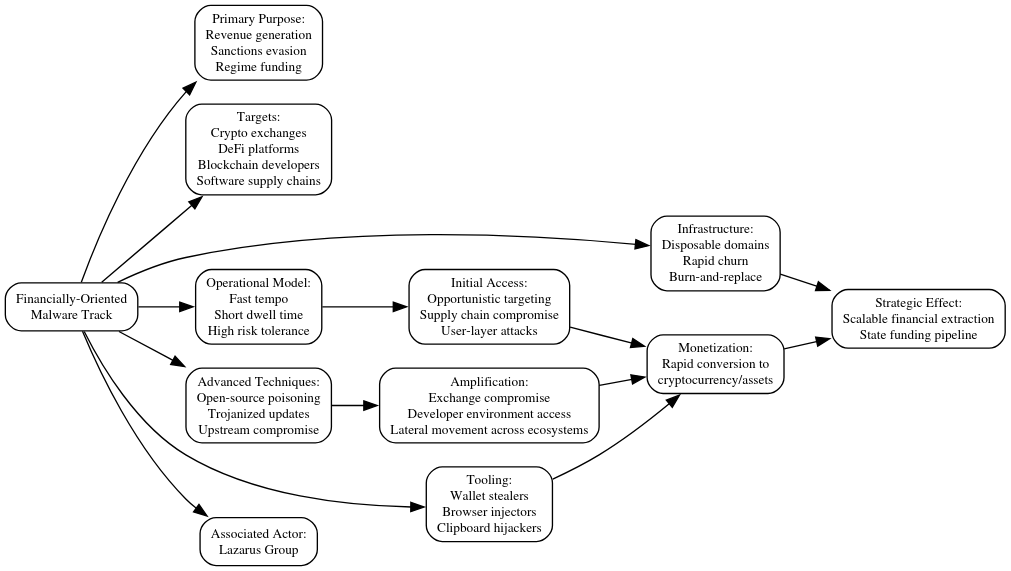
This operational urgency is mirrored in infrastructure management. Hosting, domains, and delivery mechanisms are treated as disposable, with rapid churn used to stay ahead of takedowns and blacklist propagation. Infrastructure longevity is not a priority; instead, it is optimized for brief windows of effectiveness before inevitable exposure. This burn-and-replace mindset distinguishes financial campaigns from the more conservative espionage track and underscores their role as an economic instrument rather than a long-term intelligence platform.
Technically, tooling within this track is purpose-built for theft. Wallet stealers and browser injectors are used to intercept credentials, private keys, and transaction workflows directly at the user layer. Clipboard hijacking exploits habitual behaviors to silently redirect cryptocurrency transfers. Increasingly, operators have demonstrated sophistication in compromising trust boundaries within the developer ecosystem itself, embedding malicious code into open-source packages or trojanizing software updates relied upon by exchanges and development teams. By inserting malware upstream, they convert trusted tooling into a scalable access vector.
Compromise of exchange infrastructure and developer environments further amplifies impact, allowing attackers to move laterally across platforms, users, and assets with minimal additional effort. These techniques reflect a deep understanding of how modern financial and crypto ecosystems are built and where their implicit trust assumptions can be subverted.
This revenue-focused track is most commonly associated with Lazarus Group, which has evolved from a primarily espionage-linked actor into a central pillar of the DPRK’s sanctions-evasion strategy. Its operations illustrate how malware has been weaponized not just as a tool of intrusion, but as a mechanism of state finance, tightly coupled to the regime’s broader strategic objectives.
Disruptive / Coercive Malware Track
The disruptive and coercive malware track represents the most overt and politically expressive component of the DPRK cyber program. Unlike espionage or financially motivated operations, its primary purpose is not persistence or profit, but strategic signaling. These operations are designed to demonstrate capability, impose costs, or deliver retaliation during periods of heightened geopolitical tension, serving as a cyber analogue to more traditional forms of state messaging and coercion.
Operationally, this track prioritizes impact over longevity. Dwell times are intentionally short, as operators expect rapid detection once payloads are deployed. Rather than avoiding attention, these campaigns are constructed to generate it, producing effects that are immediately visible to victims, governments, and, in some cases, the broader public. Tooling and infrastructure are treated as expendable, with a clear willingness to burn assets in exchange for a decisive, time-bound outcome.
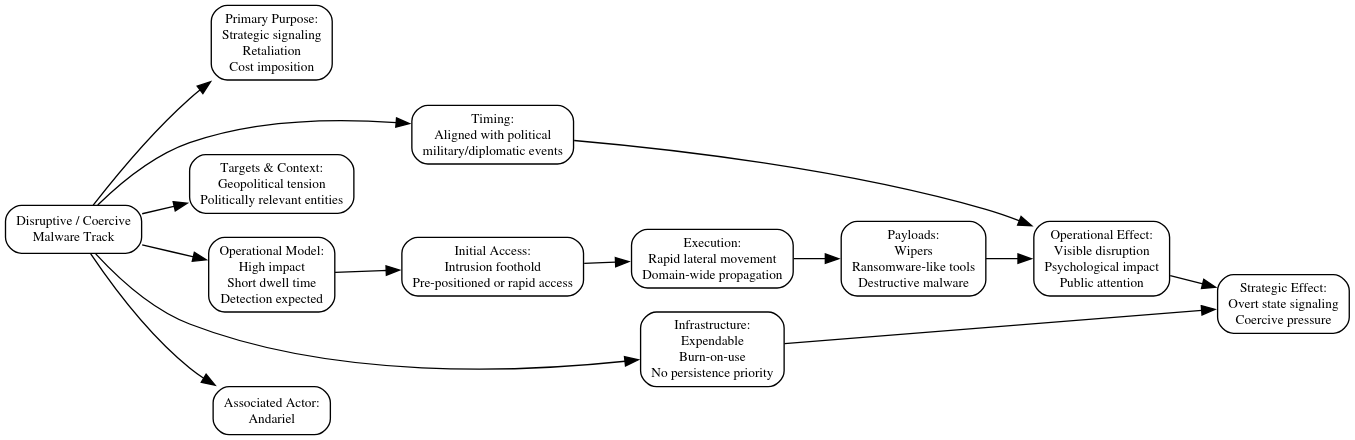
The technical execution of these operations reflects this mindset. Payloads frequently take the form of wipers or ransomware-like tools capable of inflicting widespread disruption across enterprise environments. Once initial access is achieved, operators emphasize rapid lateral movement to maximize reach before containment measures can be enacted. Domain-wide execution is a common objective, enabling simultaneous impact across large portions of a target organization and amplifying both operational and psychological effect.
Timing is a critical element. Deployments are often aligned with external political, military, or diplomatic events, reinforcing the interpretive link between the cyber operation and broader state intent. This temporal coordination strengthens the signaling function of the attack, ensuring that the disruption is read not as isolated cybercrime, but as an intentional act within a wider strategic context.
This disruptive track is most commonly associated with Andariel, which has been linked to campaigns emphasizing sabotage, rapid execution, and overt impact. Within the fragmented DPRK malware ecosystem, this track functions as the regime’s blunt instrument: less subtle than espionage, less financially focused than theft, but uniquely suited to delivering unmistakable signals when strategic conditions demand it.
Cross-Track Technical Invariants
Despite the visible compartmentalization and diversity of tooling and operations, analysis across the full body of known malware reporting reveals a set of persistent unifying elements that cut across mission lines. These commonalities indicate that divergence at the payload and campaign level does not equate to independence at the development or strategic level. Instead, they point to shared standards, reuse patterns, and centralized oversight shaping how disparate malware tracks are built and deployed.
At the technical layer, recurring cryptographic routines and packing styles appear across otherwise distinct malware families. While implementations are often modified to frustrate signature-based detection, the underlying design choices remain recognizable, suggesting common developer playbooks or shared internal libraries. Similarly, loader architectures show strong familial resemblance: lightweight initial components designed to stage or decrypt secondary payloads, reused across campaigns with incremental variation rather than wholesale redesign.
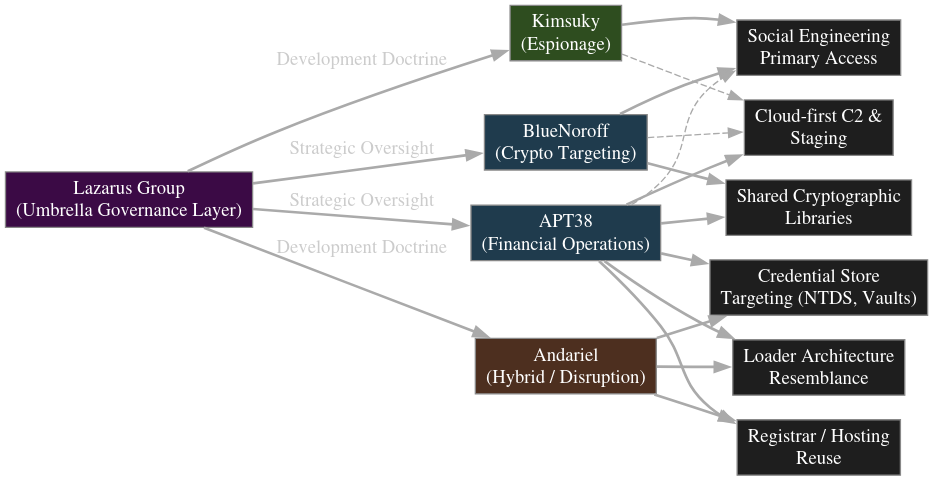
Infrastructure analysis reinforces this picture. Even as domains and servers are rapidly rotated at the campaign level, overlap persists at lower layers of the stack, including registrars, hosting providers, and preferred geographic regions. This reuse reflects both operational convenience and institutional familiarity, revealing constraints and preferences that are difficult to fully obfuscate even in a fragmented model.
Perhaps most importantly, all tracks continue to rely heavily on social engineering as the primary initial access vector. Whether the objective is espionage, financial theft, or disruption, operators consistently exploit human trust rather than novel technical exploits. This dependence underscores a strategic assessment that human-mediated access remains more reliable, scalable, and adaptable than vulnerability-driven intrusion, particularly against increasingly hardened technical defenses.
Once access is achieved, there is a consistent preference for operating within trusted ecosystems. Cloud platforms, developer tooling, and collaboration services are repeatedly abused for command-and-control, staging, or lateral movement. By embedding malicious activity within environments already sanctioned and trusted by enterprises, operators reduce detection risk and leverage the implicit legitimacy of widely used services.
Taken together, these patterns demonstrate that compartmentalization and diversity exists primarily at the operational and payload level, not at the level of governance or development philosophy. The DPRK malware ecosystem is best understood as a collection of specialized instruments built from a common toolkit, governed by shared standards and strategic direction, even as execution diverges to meet distinct mission objectives.
Why Compartmentalization and Diversity Matters
Operationally, compartmentalization and diversity confers a high degree of resilience on the DPRK cyber program. Because malware families, infrastructure, and delivery mechanisms are compartmentalized by mission, the exposure or neutralization of one toolchain has limited impact beyond its immediate operational context. When a specific malware family is detected, attributed, and burned, the loss is contained; parallel mission tracks continue to function largely unaffected. This loss tolerance allows operators to assume compromise as a routine condition rather than an exceptional failure, encouraging aggressive use of tooling without risking systemic degradation of the broader program.
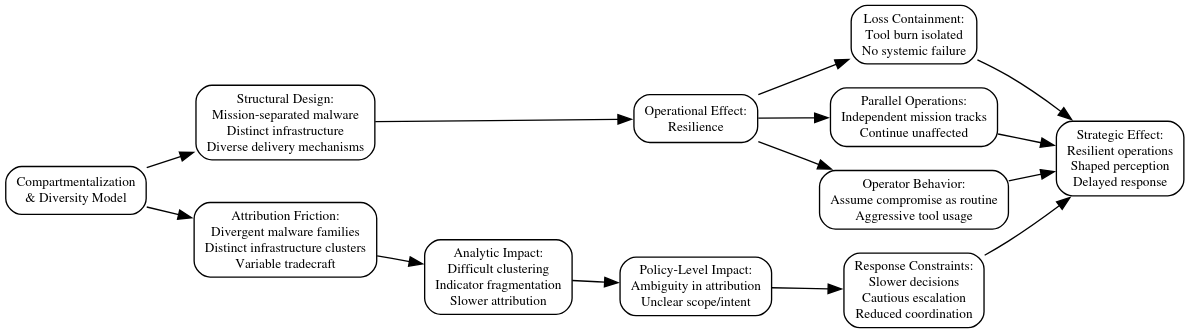
This resilience is reinforced by deliberate attribution friction. Divergent malware families, distinct infrastructure clusters, and varying tradecraft across campaigns complicate efforts to collapse activity into a single coherent actor model. Defenders and analysts are forced to disentangle overlapping indicators, slowing attribution and increasing uncertainty about scope and intent. Campaign clustering becomes more difficult as shared characteristics are diluted by intentional variation, while residual commonalities remain subtle enough to require sustained analytic effort to identify.
At the policy level, this ambiguity has concrete effects. Unclear attribution complicates decision-making around response options, escalation thresholds, and public messaging. When activity cannot be cleanly assigned to a single actor or mission set, responses tend to be slower, more cautious, and less coordinated. In this way, compartmentalization and diversity functions not only as a technical or operational safeguard, but as a strategic instrument shaping how adversary actions are interpreted while also constraining the speed and confidence with which states and organizations can respond.
Parallel Execution
Compartmentalization and diversity enables the DPRK cyber program to operate on multiple fronts simultaneously without the internal friction that would otherwise arise from shared tooling, infrastructure, or operational dependencies. By separating malware families and operational workflows along mission lines, distinct teams can pursue diplomatic, financial, and technological targets in parallel, each optimized for its own objectives and risk profile. This structure avoids the bottlenecks and trade-offs inherent in monolithic campaigns, where a single exposure can force a pause or redesign across all activity.
Against diplomatic and policy-oriented targets, espionage-focused operations can proceed patiently, maintaining long-term access and information flow without being disrupted by the higher-noise activities of financial theft or disruptive attacks. At the same time, financially motivated campaigns can move aggressively against cryptocurrency exchanges, developer communities, and related infrastructure, burning tooling and infrastructure as needed without jeopardizing sensitive intelligence footholds elsewhere. Disruptive operations, when activated, can deliver rapid and visible impact without revealing or contaminating the quieter channels of access maintained in parallel.
This separation of concerns allows the DPRK to treat its cyber operations as a portfolio of independent but strategically coordinated efforts. Each mission track operates according to its own tempo, tolerance for exposure, and technical requirements, yet all contribute to overarching state objectives. The result is a cyber apparatus capable of sustained, multi-domain engagement across diplomatic, economic, and technological domains without mutual interference or cascading operational risk.
Defender Implications
The fragmented structure of the DPRK malware ecosystem fundamentally alters the detection problem for defenders. Static malware signatures degrade rapidly as tooling is routinely modified, re-packed, or replaced altogether. Even when individual samples are successfully identified, their utility is short-lived, offering only fleeting defensive value before variants emerge. Similarly, campaign-level indicators of compromise once effective for clustering activity no longer generalize across operations, as distinct mission tracks deliberately minimize shared surface indicators.
As a result, malware-focused detection in isolation is increasingly insufficient. Focusing on payloads alone risks missing the broader operational context in which access is gained, maintained, and exploited. In a segmented model, the absence of a known malware signature does not imply the absence of DPRK activity; it may simply reflect a different mission track employing different tooling, infrastructure, or delivery mechanisms.
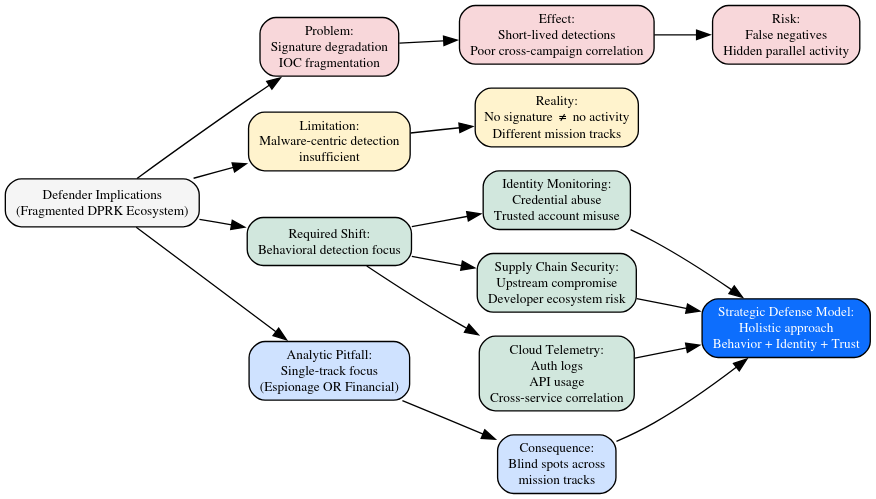
Effective defense therefore requires a shift in priorities. Behavioral analytics become critical for identifying anomalous patterns of access, execution, and data movement that persist regardless of specific malware families. Identity and access monitoring is particularly important, as many DPRK operations across espionage, financial, and disruptive tracks depend on credential abuse and trusted account usage rather than exploit-driven compromise. Strengthening security around supply chains and developer ecosystems is equally essential, given the regime’s demonstrated willingness to compromise upstream tooling to achieve scalable access. Cloud telemetry correlation, spanning authentication events, API usage, and cross-service activity, provides the visibility necessary to detect abuse within trusted platforms.
Organizations that frame DPRK activity too narrowly by treating it exclusively as espionage or, alternatively, as financial cybercrime risk creating analytical blind spots. The segmented nature of the threat means that focusing defenses on a single “type” of activity can leave other mission tracks undetected. Instead, a holistic approach, grounded in behavior, identity, and ecosystem trust relationships, is required to account for the full breadth of DPRK cyber operations.
Malware compartmentalization and diversity in the Broader APT Landscape
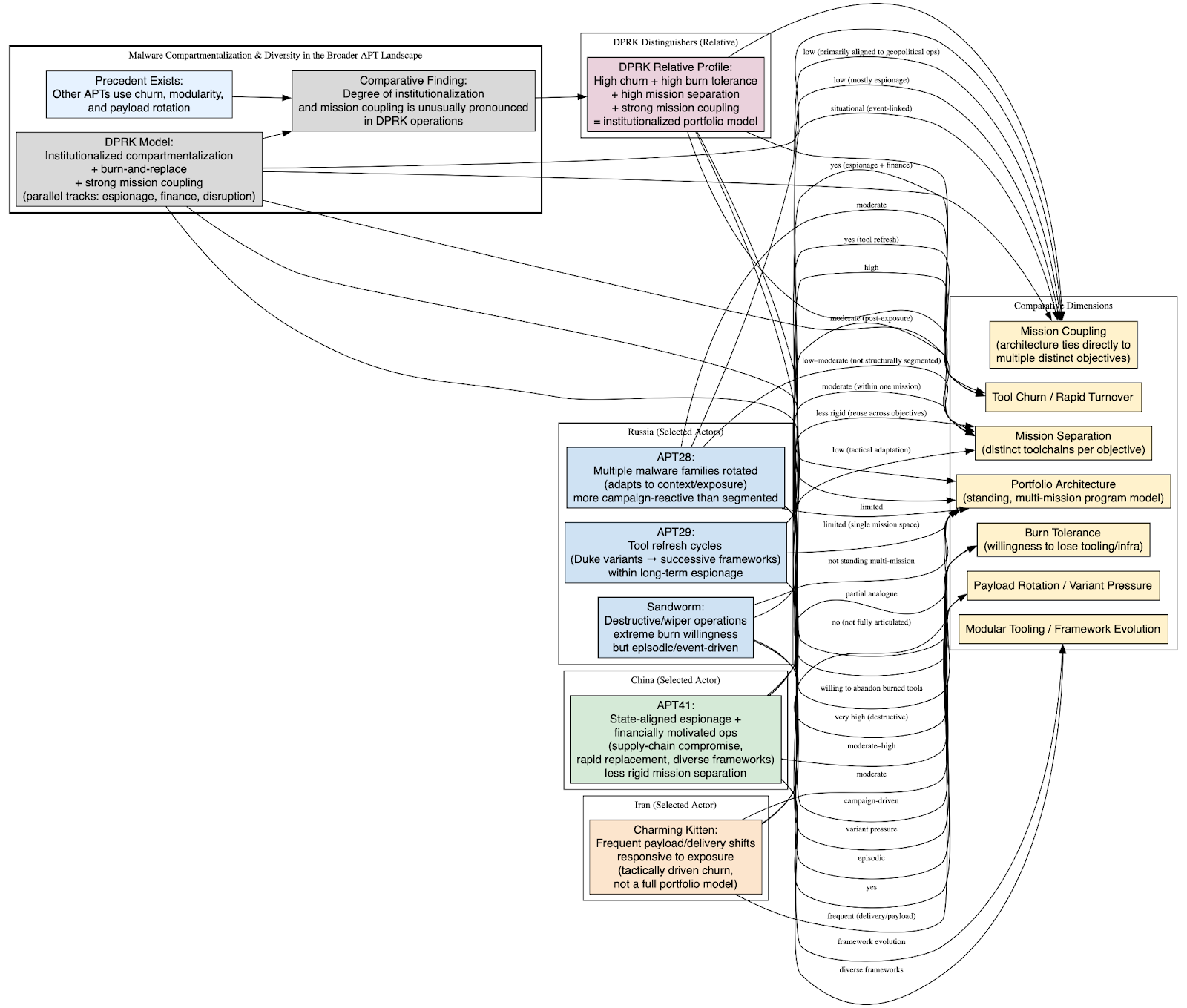
The deliberate burn-and-replace approach observed in DPRK malware campaigns is not without precedent among advanced state-aligned threat actors. However, comparative analysis shows that while similar tactics exist elsewhere, the degree of institutionalization and mission coupling seen in DPRK operations is unusually pronounced.
Several other APT actors have adopted rapid malware turnover, modular tooling, and payload rotation to evade detection and extend campaign viability under defensive pressure.
Russian intelligence–linked actors, such as APT29, have repeatedly evolved malware families over time, transitioning from early Duke variants to successive, distinct frameworks. These shifts demonstrate intentional tool refresh cycles designed to defeat signature-based detection, but they largely occur within a single strategic mission space of long-term espionage rather than across parallel, economically distinct objectives.
Similarly, APT28 has historically rotated between multiple malware families across campaigns, adapting tooling to geopolitical context and operational exposure. While this reflects a willingness to abandon burned tools, the activity remains more campaign-reactive than structurally segmented.
Chinese-linked APT41 presents a closer analogue in that it has demonstrably conducted both state-aligned espionage and financially motivated operations, often with overlapping personnel and infrastructure. APT41’s use of supply-chain compromise, rapid tool replacement, and diverse malware frameworks mirrors aspects of the DPRK model. However, public reporting indicates less rigid separation between mission toolchains, with greater reuse across objectives.
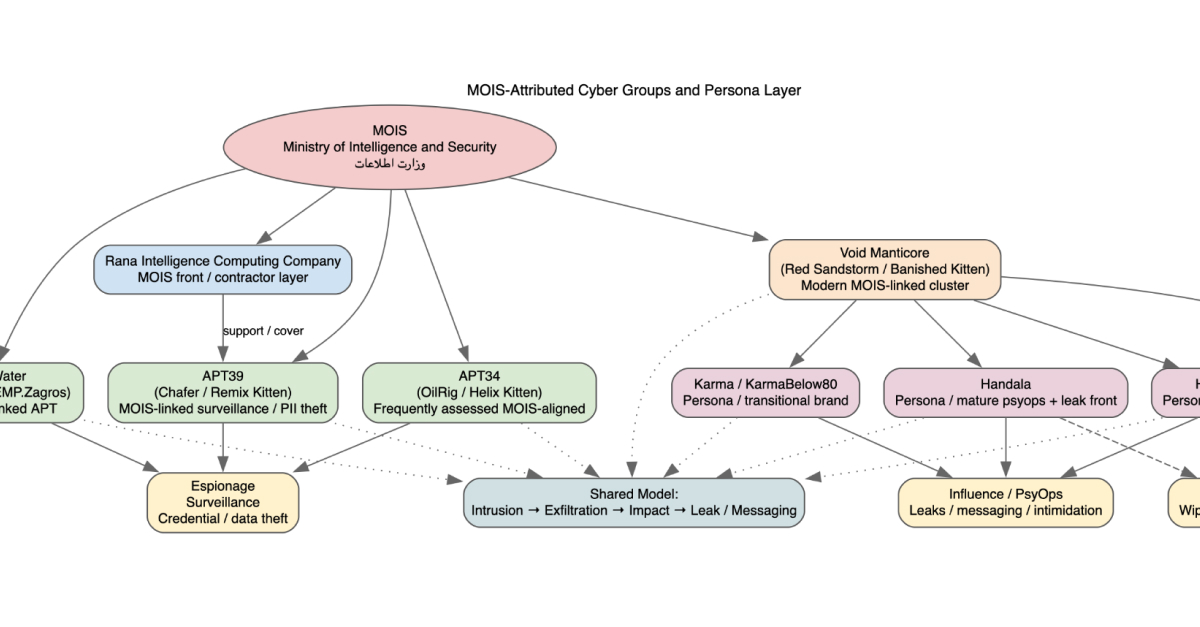
Iranian actors such as Charming Kitten likewise exhibit frequent shifts in malware payloads and delivery mechanisms, particularly in response to exposure. These changes improve survivability but do not rise to the level of a fully articulated portfolio model; tool churn here appears tactically driven, rather than strategically compartmentalized.
Finally, disruptive-focused Russian activity attributed to Sandworm demonstrates an extreme willingness to burn tooling entirely, particularly in wiper and destructive campaigns. However, this behavior is episodic and event-driven, rather than embedded in a standing, multi-mission cyber architecture.
Below is a comparative table showing how DPRK actors stand relative to other major nation-state APT actors (Russia, China, and Iran) in terms of tool churn, mission separation, and burn tolerance. This is based on multiple public sources outlining state-aligned cyber capabilities, campaign evolution, and malware practices.
Comparative Table APT Malware Strategy & Burn Dynamics
Analytic Distinction: Why the DPRK Model Is Different
What distinguishes the DPRK cyber program is not the existence of malware rotation itself, but how completely burn-and-replace logic is integrated into program design.
Across other APT ecosystems, rapid malware turnover is typically:
- A response to detection,
- Confined to a single mission domain, or
- Implemented unevenly across campaigns.
By contrast, DPRK operations demonstrate:
- Standing parallel malware portfolios, not ad-hoc replacements,
- Mission-aligned toolchains (espionage, revenue, disruption),
- Acceptance of tool loss as routine, not exceptional,
- And centralized strategic coordination despite decentralized execution.
This places DPRK activity closer to an industrialized cyber production model, where malware is treated as a consumable input rather than a prized asset.
In contrast, espionage tooling is expected to retain its emphasis on low-noise persistence. Malware supporting intelligence collection will continue to prioritize stealth, credential abuse, and cloud-based living-off-the-land techniques that enable extended dwell times even in increasingly monitored environments.
Taken together, these trends indicate that compartmentalization and diversity is not a transitional phase but a durable feature of the DPRK cyber program. As defensive pressure increases, diversification by mission will deepen, further entrenching a model built to absorb exposure, frustrate attribution, and sustain operations across multiple strategic domains.
Summary Findings
The DPRK malware ecosystem is not simply more prolific or more chaotic than that of its peers; it is more deliberately structured at a fundamental, programmatic level. Where many advanced persistent threat actors treat malware as a semi-durable asset to be preserved and refined over time, the DPRK treats malware as an inherently expendable input. Tool exposure is not regarded as a failure state; it is an assumed outcome. As a result, operational planning begins from the premise that any given toolchain will eventually be detected, attributed, and neutralized.
This assumption fundamentally reshapes how the DPRK designs and deploys cyber capabilities. Malware is engineered for utility within a limited lifespan rather than for long-term survivability. Development pipelines emphasize speed, modularity, and replaceability over elegance or longevity. When a tool is burned, it is not mourned or patched indefinitely; it is discarded and superseded, often by a parallel or already-prepared alternative. In this sense, compartmentalization and diversity is not a defensive reaction to disruption, but the default state of the ecosystem.
By contrast, many other APT actors burn tools reluctantly and reactively. Russian, Chinese, and Iranian groups typically rotate malware families after exposure, but such decisions are often tied to specific campaigns or incidents. The underlying assumption remains that tools should persist as long as possible, evolving incrementally to preserve prior investment. The DPRK departs from this logic entirely. Its cyber operations reflect an acceptance that persistence at the tool level is illusory, and that strategic continuity must instead be achieved through organizational design and operational redundancy.
Seen in comparative context, DPRK cyber operations are therefore best understood not as an anomaly, but as a mature instantiation of a broader trend among advanced threat actors pushed to its logical extreme by unique economic and political constraints. Persistent sanctions, direct linkage between cyber activity and state revenue, and sustained international scrutiny have compressed the DPRK’s tolerance for operational pause or degradation. Under these conditions, a cyber program built around long-lived platforms would be brittle. A program built around compartmentalization and diversity, parallel execution, and consumable tooling is resilient.
Malware diversity, rapid churn, and concurrent mission execution are not symptoms of disorder or indiscipline. They are the visible mechanics of a system engineered to function under constant pressure, where exposure is continuous and inevitability assumed. In this model, coherence does not reside in individual tools, but in strategy: centralized intent, mission-aligned portfolios, and an operational architecture designed to endure even as its individual components are repeatedly destroyed.
APPENDIX A: Representative DPRK Malware IOCs
Government-Published Malware Variants & Names
These malware families have been documented in U.S. government malware reports and advisories associated with North Korean state actors (often referred to collectively as HIDDEN COBRA by U.S. agencies): (CISA)
- BLINDINGCAN – Remote access tool used to maintain persistence and network exploitation. (CISA)
- COPPERHEDGE – Manuscrypt family variant attributed to North Korean APT targeting exchanges/crypto ecosystems. (CISA)
- TAINTEDSCRIBE – Full-featured beaconing implant used by DPRK actors. (CISA)
- PEBBLEDASH – North Korean beaconing implant family. (CISA)
- BISTROMATH – Remote access implant with multiple versions observed. (CISA)
- SLICKSHOES – Dropper with beaconing capabilities. (CISA)
- CROWDEDFLOUNDER – Beaconing payload with packing protections. (CISA)
- HOTCROSSIANT – Full-featured beaconing implant. (CISA)
- ARTFULPIE – Downloader implant that decodes and executes secondary payloads. (CISA)
- BUFFERLINE – Full-featured beaconing implant. (CISA)
- ELECTRICFISH – Proxy malware for tunnelled traffic. (CISA)
- BADCALL – Proxy server malware with Fake TLS methods. (CISA)
- Joanap – RAT enabling botnet management and secondary payload execution. (Wikipedia)
Note: CISA malware analysis reports (MARs) frequently include sample hashes, file Thatnames, network indicators, and signatures for these variants. (CISA)
Appendix B: Malware Linked Activities and Attribution Context
Cryptocurrency-Facilitating Malware
- AppleJeus – Malware family used to facilitate cryptocurrency theft, often distributed under the guise of fake trading platforms or wallets. (CISA)
Operational Artifacts & TTP Context
While specific IOCs vary by incident and campaign, the following patterns are relevant to detection and triage:
- Botnet infrastructure IPs associated with DDoS and proxy relays used by DPRK actors. (CISA)
- Credential harvesting and session token theft in spearphishing campaigns (e.g., mobile-delivered QR code phishing vectors). (Internet Crime Complaint Center)
- Proxy and beaconing communication over Fake TLS or tunneled channels seen in BADCALL/ELECTRICFISH series. (CISA)
Appendix C: Known Malware Families by Associated Actor
Appendix D: Additional IOC Sources and Hunting References
For operational deployment, consult the following sources with downloadable IOC datasets:
- CISA North Korea State-Sponsored Threat Advisories Includes malware reports, sample hashes, and network indicators. (CISA)
- Unit42 Threat Assessment North Korean Groups Malware Arsenal Contains telemetry on recent malware families across OS platforms. (Unit 42)
- Acronis TRU Alliance DPRK Malware Infrastructure Mapping Includes IOCs and hunting guidance for Lazarus and Kimsuky clusters. (Acronis)
Appendix E: Exemplar File Hashes by “Hydra Head” (SHA256)
F.1 Head 1 LABYRINTH CHOLLIMA (Espionage / Industrial, logistics, defense)
Primary exemplars (CrowdStrike community-tracking hashes): (CrowdStrike)
- Dozer 7dee2bd4e317d12c9a2923d0531526822cfd37eabfd7aecc74258bb4f2d3a643 (CrowdStrike)
- Brambul d2359630e84f59984ac7ddebdece9313f0c05f4a1e7db90abadfd86047c12dd6 (CrowdStrike)
- Joanap 4fe3c853ab237005f7d62324535dd641e1e095d1615a416a9b39e042f136cf6b (CrowdStrike)
- KorDLL Bot 73edc54abb3d6b8df6bd1e4a77c373314cbe99a660c8c6eea770673063f55503 (CrowdStrike)
- Koredos a795964bc2be442f142f5aea9886ddfd297ec898815541be37f18ffeae02d32f (CrowdStrike)
- Hawup RAT 453d8bd3e2069bc50703eb4c5d278aad02304d4dc5d804ad2ec00b2343feb7a4 (CrowdStrike)
- Hoplight 05feed9762bc46b47a7dc5c469add9f163c16df4ddaafe81983a628da5714461 (CrowdStrike)
- Manuscrypt dced1acbbe11db2b9e7ae44a617f3c12d6613a8188f6a1ece0451e4cd4205156 (CrowdStrike)
- HTTPHoplight ceccb2339088fa2d6337082704bbf67f84eeb0d0b60ce5ab0ab7e1824002fa4c (CrowdStrike)
- OpenSSL Downloader f749c7e84809ffc3939eaed06ad90e15b0e11375f98d7348c0aa1bf35d3f0b8e (CrowdStrike)
- UnderGroundRAT f9586fdf4e0a65b17ee32bc3c3f493a055409abde373720d594d27fd24adffa0 (CrowdStrike)
- NedDnLoader 512877c98fd83cd51bb287da4462b44f9d276d7ce51890f4ded1b915a6d2d5e1 (CrowdStrike)
- Stackeyflate d2e743216d17e97c8d1913d376d46095b740015f26a3c62a05e286573721d26c (CrowdStrike)
- HiberRAT 58f2972c6a8fc743543f7b8c4df085c5cf2c6e674e5601e85eec60cd269cfb3c (CrowdStrike)
- WinWebDown fc885b323172106ab6f2f0cc77b609987384a38e3af41ad888d5389610d29daf (CrowdStrike)
- FudModule cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b (noted as shared with GOLDEN) (CrowdStrike)
Supplemental “legacy DPRK MAR-derived” hashes (bridging set; keep as non-exclusive DPRK nexus):
Use these as heritage/overlap indicators for “DPRK malware ecosystem” rather than hard-binding them to LABYRINTH specifically.
- BLINDINGCAN (multiple SHA256)
- BISTROMATH (multiple SHA256)
- SLICKSHOES, CROWDEDFLOUNDER, BUFFETLINE, BADCALL (SHA256)
(These remain useful as “DPRK malware portfolio” IOCs, but they are not the cleanest proof of the three-unit split without additional clustering work.)
PRESSURE CHOLLIMA (High-payout crypto theft operations)
Primary exemplars (CrowdStrike community-tracking hashes): (CrowdStrike)
- Scuzzyfuss b9f6a9d4f837f5b8a5dc9987a91ba44bc7ae7f39aa692b5b21dba460f935a0ae (CrowdStrike)
- MataNet 357c9daf6c4343286a9a85a27bc25defdc056877ce1be2943d2e8ede3bce022c (CrowdStrike)
- SwDownloader a61ecbe8a5372c85dcf5d077487f09d01e144128243793d2b97012440dcf106e (CrowdStrike)
- SparkDownloader 9ba02f8a985ec1a99ab7b78fa678f26c0273d91ae7cbe45b814e6775ec477598 (CrowdStrike)
- TwoPence Electric 081804b491c70bfa63ecdbe9fd4618d3570706ad8b71dba13e234069648e5e48 (CrowdStrike)
- MagikCookie 1579347265f948f9646931335d57e7960fe65dd429394be84b4ae15bca73dfde (CrowdStrike)
- StatusSymbol 666c50b8b772101b0e2e35ff1de52a278c2727027b54858e457571d296fec50b (CrowdStrike)
- GhostShip 56e51244e258c39293463c8cf02f5dddb085be90728fab147a60741cf014aa4d (CrowdStrike)
- AlertConf e0aa5ef3af26681a8c8b46d95656580779d0ff3c2fe531b95a59ee918686e443 (CrowdStrike)
GOLDEN CHOLLIMA (Baseline revenue / consistent tempo, fintech & crypto)
Primary exemplars (CrowdStrike community-tracking hashes): (CrowdStrike)
- Jeus fe948451df90df80c8028b969bf89ecbf501401e7879805667c134080976ce2e (CrowdStrike)
- HTTPHelper ff32bc1c756d560d8a9815db458f438d63b1dcb7e9930ef5b8639a55fa7762c9 (CrowdStrike)
- SnakeBaker b6995c31a7ee88392fc25fd6d1a3a7975b3cb4ec3a9a318c3fcfaaf89eb65ce1 (CrowdStrike)
- NodalBaker 0518a163b90e7246a349440164d02d10f31d514a7e5cce842b6cf5b3a0cc1bfa (CrowdStrike)
- PipeDown 2ef212f433b722b734d80b41a2364a41ca0453dbfe3e6ec8b951eca795075a02 (CrowdStrike)
- DevobRAT fde50c3a373ebc2661e08c99c1cb50dc34efc022a3880c317ab5b84108ef83aa (CrowdStrike)
- Anycon 2110a6e89d98a626f846ec8deccbac057300d194933ae0cbf1ef4831a4cc829e (CrowdStrike)
- CitriLoader d0cf9c1f87eac9b8879684a041dd6a2e1a0c15e185d4814a51adda19f9399a9b (CrowdStrike)
- FudModule (shared access noted) cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b (CrowdStrike)
APPENDIX F: ANY RUN and VIRUS TOTAL LINKS
LABYRINTH CHOLLIMA (Espionage Head)
Dozer
VT: https://www.virustotal.com/gui/file/7dee2bd4e317d12c9a2923d0531526822cfd37eabfd7aecc74258bb4f2d3a643
ANY.RUN: https://any.run/search/?query=7dee2bd4e317d12c9a2923d0531526822cfd37eabfd7aecc74258bb4f2d3a643
Brambul
VT: https://www.virustotal.com/gui/file/d2359630e84f59984ac7ddebdece9313f0c05f4a1e7db90abadfd86047c12dd6
ANY.RUN: https://any.run/search/?query=d2359630e84f59984ac7ddebdece9313f0c05f4a1e7db90abadfd86047c12dd6
Joanap
VT: https://www.virustotal.com/gui/file/4fe3c853ab237005f7d62324535dd641e1e095d1615a416a9b39e042f136cf6b
ANY.RUN: https://any.run/search/?query=4fe3c853ab237005f7d62324535dd641e1e095d1615a416a9b39e042f136cf6b
KorDLL Bot
VT: https://www.virustotal.com/gui/file/73edc54abb3d6b8df6bd1e4a77c373314cbe99a660c8c6eea770673063f55503
ANY.RUN: https://any.run/search/?query=73edc54abb3d6b8df6bd1e4a77c373314cbe99a660c8c6eea770673063f55503
Koredos
VT: https://www.virustotal.com/gui/file/a795964bc2be442f142f5aea9886ddfd297ec898815541be37f18ffeae02d32f
ANY.RUN: https://any.run/search/?query=a795964bc2be442f142f5aea9886ddfd297ec898815541be37f18ffeae02d32f
Hawup RAT
VT: https://www.virustotal.com/gui/file/453d8bd3e2069bc50703eb4c5d278aad02304d4dc5d804ad2ec00b2343feb7a4
ANY.RUN: https://any.run/search/?query=453d8bd3e2069bc50703eb4c5d278aad02304d4dc5d804ad2ec00b2343feb7a4
Hoplight
VT: https://www.virustotal.com/gui/file/05feed9762bc46b47a7dc5c469add9f163c16df4ddaafe81983a628da5714461
ANY.RUN: https://any.run/search/?query=05feed9762bc46b47a7dc5c469add9f163c16df4ddaafe81983a628da5714461
Manuscrypt
VT: https://www.virustotal.com/gui/file/dced1acbbe11db2b9e7ae44a617f3c12d6613a8188f6a1ece0451e4cd4205156
ANY.RUN: https://any.run/search/?query=dced1acbbe11db2b9e7ae44a617f3c12d6613a8188f6a1ece0451e4cd4205156
HTTPHoplight
VT: https://www.virustotal.com/gui/file/ceccb2339088fa2d6337082704bbf67f84eeb0d0b60ce5ab0ab7e1824002fa4c
ANY.RUN: https://any.run/search/?query=ceccb2339088fa2d6337082704bbf67f84eeb0d0b60ce5ab0ab7e1824002fa4c
OpenSSL Downloader
VT: https://www.virustotal.com/gui/file/f749c7e84809ffc3939eaed06ad90e15b0e11375f98d7348c0aa1bf35d3f0b8e
ANY.RUN: https://any.run/search/?query=f749c7e84809ffc3939eaed06ad90e15b0e11375f98d7348c0aa1bf35d3f0b8e
UnderGroundRAT
VT: https://www.virustotal.com/gui/file/f9586fdf4e0a65b17ee32bc3c3f493a055409abde373720d594d27fd24adffa0
ANY.RUN: https://any.run/search/?query=f9586fdf4e0a65b17ee32bc3c3f493a055409abde373720d594d27fd24adffa0
NedDnLoader
VT: https://www.virustotal.com/gui/file/512877c98fd83cd51bb287da4462b44f9d276d7ce51890f4ded1b915a6d2d5e1
ANY.RUN: https://any.run/search/?query=512877c98fd83cd51bb287da4462b44f9d276d7ce51890f4ded1b915a6d2d5e1
Stackeyflate
VT: https://www.virustotal.com/gui/file/d2e743216d17e97c8d1913d376d46095b740015f26a3c62a05e286573721d26c
ANY.RUN: https://any.run/search/?query=d2e743216d17e97c8d1913d376d46095b740015f26a3c62a05e286573721d26c
HiberRAT
VT: https://www.virustotal.com/gui/file/58f2972c6a8fc743543f7b8c4df085c5cf2c6e674e5601e85eec60cd269cfb3c
ANY.RUN: https://any.run/search/?query=58f2972c6a8fc743543f7b8c4df085c5cf2c6e674e5601e85eec60cd269cfb3c
WinWebDown
VT: https://www.virustotal.com/gui/file/fc885b323172106ab6f2f0cc77b609987384a38e3af41ad888d5389610d29daf
ANY.RUN: https://any.run/search/?query=fc885b323172106ab6f2f0cc77b609987384a38e3af41ad888d5389610d29daf
FudModule
VT: https://www.virustotal.com/gui/file/cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b
ANY.RUN: https://any.run/search/?query=cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b
PRESSURE CHOLLIMA (High-Payout Crypto)
Scuzzyfuss
VT: https://www.virustotal.com/gui/file/b9f6a9d4f837f5b8a5dc9987a91ba44bc7ae7f39aa692b5b21dba460f935a0ae
ANY.RUN: https://any.run/search/?query=b9f6a9d4f837f5b8a5dc9987a91ba44bc7ae7f39aa692b5b21dba460f935a0ae
MataNet
VT: https://www.virustotal.com/gui/file/357c9daf6c4343286a9a85a27bc25defdc056877ce1be2943d2e8ede3bce022c
ANY.RUN: https://any.run/search/?query=357c9daf6c4343286a9a85a27bc25defdc056877ce1be2943d2e8ede3bce022c
SwDownloader
VT: https://www.virustotal.com/gui/file/a61ecbe8a5372c85dcf5d077487f09d01e144128243793d2b97012440dcf106e
ANY.RUN: https://any.run/search/?query=a61ecbe8a5372c85dcf5d077487f09d01e144128243793d2b97012440dcf106e
SparkDownloader
VT: https://www.virustotal.com/gui/file/9ba02f8a985ec1a99ab7b78fa678f26c0273d91ae7cbe45b814e6775ec477598
ANY.RUN: https://any.run/search/?query=9ba02f8a985ec1a99ab7b78fa678f26c0273d91ae7cbe45b814e6775ec477598
TwoPence Electric
VT: https://www.virustotal.com/gui/file/081804b491c70bfa63ecdbe9fd4618d3570706ad8b71dba13e234069648e5e48
ANY.RUN: https://any.run/search/?query=081804b491c70bfa63ecdbe9fd4618d3570706ad8b71dba13e234069648e5e48
MagikCookie
VT: https://www.virustotal.com/gui/file/1579347265f948f9646931335d57e7960fe65dd429394be84b4ae15bca73dfde
ANY.RUN: https://any.run/search/?query=1579347265f948f9646931335d57e7960fe65dd429394be84b4ae15bca73dfde
StatusSymbol
VT: https://www.virustotal.com/gui/file/666c50b8b772101b0e2e35ff1de52a278c2727027b54858e457571d296fec50b
ANY.RUN: https://any.run/search/?query=666c50b8b772101b0e2e35ff1de52a278c2727027b54858e457571d296fec50b
GhostShip
VT: https://www.virustotal.com/gui/file/56e51244e258c39293463c8cf02f5dddb085be90728fab147a60741cf014aa4d
ANY.RUN: https://any.run/search/?query=56e51244e258c39293463c8cf02f5dddb085be90728fab147a60741cf014aa4d
AlertConf
VT: https://www.virustotal.com/gui/file/e0aa5ef3af26681a8c8b46d95656580779d0ff3c2fe531b95a59ee918686e443
ANY.RUN: https://any.run/search/?query=e0aa5ef3af26681a8c8b46d95656580779d0ff3c2fe531b95a59ee918686e443
GOLDEN CHOLLIMA (Baseline Revenue Track)
Jeus
VT: https://www.virustotal.com/gui/file/fe948451df90df80c8028b969bf89ecbf501401e7879805667c134080976ce2e
ANY.RUN: https://any.run/search/?query=fe948451df90df80c8028b969bf89ecbf501401e7879805667c134080976ce2e
HTTPHelper
VT: https://www.virustotal.com/gui/file/ff32bc1c756d560d8a9815db458f438d63b1dcb7e9930ef5b8639a55fa7762c9
ANY.RUN: https://any.run/search/?query=ff32bc1c756d560d8a9815db458f438d63b1dcb7e9930ef5b8639a55fa7762c9
SnakeBaker
VT: https://www.virustotal.com/gui/file/b6995c31a7ee88392fc25fd6d1a3a7975b3cb4ec3a9a318c3fcfaaf89eb65ce1
ANY.RUN: https://any.run/search/?query=b6995c31a7ee88392fc25fd6d1a3a7975b3cb4ec3a9a318c3fcfaaf89eb65ce1
NodalBaker
VT: https://www.virustotal.com/gui/file/0518a163b90e7246a349440164d02d10f31d514a7e5cce842b6cf5b3a0cc1bfa
ANY.RUN: https://any.run/search/?query=0518a163b90e7246a349440164d02d10f31d514a7e5cce842b6cf5b3a0cc1bfa
PipeDown
VT: https://www.virustotal.com/gui/file/2ef212f433b722b734d80b41a2364a41ca0453dbfe3e6ec8b951eca795075a02
ANY.RUN: https://any.run/search/?query=2ef212f433b722b734d80b41a2364a41ca0453dbfe3e6ec8b951eca795075a02
DevobRAT
VT: https://www.virustotal.com/gui/file/fde50c3a373ebc2661e08c99c1cb50dc34efc022a3880c317ab5b84108ef83aa
ANY.RUN: https://any.run/search/?query=fde50c3a373ebc2661e08c99c1cb50dc34efc022a3880c317ab5b84108ef83aa
Anycon
VT: https://www.virustotal.com/gui/file/2110a6e89d98a626f846ec8deccbac057300d194933ae0cbf1ef4831a4cc829e
ANY.RUN: https://any.run/search/?query=2110a6e89d98a626f846ec8deccbac057300d194933ae0cbf1ef4831a4cc829e
CitriLoader
VT: https://www.virustotal.com/gui/file/d0cf9c1f87eac9b8879684a041dd6a2e1a0c15e185d4814a51adda19f9399a9b
ANY.RUN: https://any.run/search/?query=d0cf9c1f87eac9b8879684a041dd6a2e1a0c15e185d4814a51adda19f9399a9b
FudModule (Shared)
VT: https://www.virustotal.com/gui/file/cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b
ANY.RUN: https://any.run/search/?query=cbd1634cf7c638f2faf5e3ec79137db6704ec9de8df798fc46aeeed38de3da9b