As the conflict between Iran and Israel escalated in early 2025, it quickly expanded beyond missiles and airstrikes into a broader battle for digital and psychological dominance. Among the most visible players in this new front is a group known as CyberAv3ngers. Their operations have included hijacking water systems, defacing programmable logic controllers (PLCs), and ridiculing Israeli cybersecurity efforts across social media platforms like Telegram and Twitter. Yet, their rise wasn’t built solely on technical exploits—it began with fabrications and theatrical messaging. CyberAv3ngers evolved from obscure defacers into sophisticated narrative operators, blending cyber sabotage with psychological operations. As their influence grew, so did suspicions of deeper affiliations—particularly with Iran’s Cyber Command, suggesting that the group may be more than a rogue actor and instead part of a broader state-aligned strategy.
Act I: A Hot War Fuels a Digital One
The ongoing conflict between Iran and Israel has intensified across both physical and digital fronts. In the last two weeks alone, Iran has launched multi-warhead missile attacks targeting major Israeli cities such as Tel Aviv and Haifa. In response, Israel conducted retaliatory airstrikes against Iranian military installations, nuclear sites, and key IRGC-Cyber Electronic Command (IRGC-CEC) facilities in cities like Isfahan and Tehran. Alongside these kinetic exchanges, Iranian cyber operators have reportedly hijacked Israeli CCTV and smart home cameras to evaluate the precision and impact of missile strikes in real time. Concurrently, cyberattack activity has spiked dramatically, since early June affecting sectors ranging from energy and defense to agriculture and municipal infrastructure across Israel and extending into Western targets.
Act II: Who Are CyberAv3ngers?


Before CyberAv3ngers emerged as a recognizable threat actor in 2023, they appeared to be reviving an obscure alias from the past. In 2020, a group calling itself “Cyber Avengers” claimed responsibility for a power outage and railway disruption in Israel, events that Israeli officials attributed to technical faults, not cyberattacks. No malware was identified, no indicators of compromise (IOCs) were released, and the group faded from view. Then, in September 2023, a new Telegram channel @CyberAveng3rs was launched, adopting the old name with a stylized twist and retroactively tying itself to the 2020 claims. The group posted ideological threats, listed infrastructure targets, and positioned itself as a cyber-arm of resistance. Its first major public claim came on October 8, 2023, when it announced it had hacked the Dorad power station, one of Israel’s largest private energy producers, a dramatic move intended to cement its arrival in the cyber threat landscape.
Except they didn’t hack it.
CyberAv3ngers' claim that they hacked Israel’s Dorad private power station on October 8, 2023, was quickly debunked by technical analysis. Investigators from Securelist confirmed that the images shared by the group were not the result of a new intrusion but were recycled from a 2022 data leak by the Iranian APT group Moses Staff. The visuals had been cropped, overlaid with new logos, and presented as fresh evidence, but metadata and compression timestamps matched the original files. There was no supporting technical evidence—no new malware, logs, or IOCs to indicate that CyberAv3ngers had gained real access to Dorad’s infrastructure. The only actual activity was a denial-of-service (DDoS) attack on the Dorad website, which served more as a psychological support act than an operational exploit. This episode marked a clear shift in CyberAv3ngers' strategy: from technical sabotage to theatrical propaganda.
Act III: The Illusion of the Dorad Hack

In reality, CyberAv3ngers did not breach the Dorad power station in October 2023. Instead, they repurposed images from a 2022 leak by the Iranian APT group Moses Staff. These files, though legitimate at the time of their original release, were outdated. CyberAv3ngers cropped the images, added their own defacement slogans, and circulated them as if they were proof of a new, live intrusion. No technical compromise occurred at Dorad, but the impact was psychological. The staged attack triggered a wave of reactions across social media and threat monitoring communities. Telegram lit up with reposts, and news outlets picked up the story. To reinforce the illusion, CyberAv3ngers launched DDoS attacks on Israeli websites and released altered versions of Israeli infrastructure security guidance under mocking titles like “Advice for Victims.” It was a performance—but one calibrated to sow fear and disrupt public trust.
Act IV: When the Hacks Became Real

While some of CyberAv3ngers’ early claims were rooted in propaganda, the group did carry out real and damaging cyberattacks. Between November 2023 and April 2024, at least 29 confirmed intrusions targeting industrial control systems (ICS) and operational technology (OT) in the United States were attributed to the group. Among these incidents were compromises of Unitronics PLCs used in municipal water utilities, including one in Aliquippa, Pennsylvania, where human-machine interfaces (HMIs) were defaced with the message: “You have been hacked, down with Israel.” The group also targeted fuel distribution systems, specifically Orpak and Gasboy terminals, disrupting their functionality. Additional intrusions affected routers, IP cameras, firewalls, and HMIs across various sectors of critical infrastructure. At the center of these campaigns was a custom Linux-based malware tool known as IOCONTROL, which enabled persistent access, remote command execution, and stealthy communication via encrypted MQTT channels. These attacks confirmed that beneath the narrative manipulation, CyberAv3ngers had a genuine operational capability with real-world consequences.
Act V: Iran’s Cyber Doctrine Evolves

CyberAv3ngers represents the latest evolution in Iran’s long-standing tradition of blending cyber operations with ideological messaging. While groups like Moses Staff, APT33, and Charming Kitten have previously combined technical intrusions with media theatrics, CyberAv3ngers has refined the model into a fully realized propaganda apparatus. Their approach is not just to breach systems, but to control the narrative surrounding those breaches—turning each operation into a performance aimed at both foreign audiences and domestic sympathizers. What sets them apart is the deliberate construction of a digital persona that fuses propaganda, defacement, and symbolic domain control into a cohesive identity.
Further supporting this narrative-centric shift, we observed three domains registered within hours of CyberAv3ngers’ September 15, 2023 Telegram launch post—a message that introduced the group’s rebranding and outlined threats to Israeli infrastructure. The domains were:
- cyberav3ngers.com
- cyberav3ngers.org
- cyberav3ngers.net
All three were registered through Namecheap using the registrar service registrar-servers.com, with privacy masking enabled via WithheldForPrivacy. As of this writing, none of the domains host active websites, nor do they resolve to public content. Passive DNS history shows that these domains were connected briefly to placeholder IP addresses, but no C2 or content delivery infrastructure has been deployed—strongly suggesting that their primary function is symbolic rather than operational.

This domain registration pattern aligns tightly with CyberAv3ngers’ pivot to psychological operations. Rather than functioning as delivery vehicles for malware or command-and-control beacons, these domains appear to serve as digital flags staking ideological territory on the internet. Just as their defacements aim to instill fear and assert presence, these unused domains enhance the group’s narrative power, presenting them as structured, intentional, and enduring. By echoing the group's name in global domain registries, CyberAv3ngers reinforces its persona as a persistent ideological combatant—building credibility not just through code, but through semiotic control.
CyberAv3ngers’ propaganda and PSYOPS narrative strategy:
- Builds on past Iranian hybrid groups like Moses Staff, APT33, and Charming Kitten, known for blending cyberattacks with ideological content.
- Operates a Telegram channel not just for updates, but as a staged information environment—complete with threats, slogans, and memes.
- Frequently shares repackaged defacements and screenshots to simulate recent operations.
- Registers domain names, to establish symbolic control and brand presence (e.g., cyberav3ngers.com, cyberav3ngers.org, cyberav3ngers.net).
- Continues the Iranian model of patriotic hacker narratives, but with diminished separation between state and grassroots actors.
- Leverages these platforms to mock foreign security services, distribute edited guidance docs, and amplify the psychological effect of their campaigns.
Act VI: Who’s Behind the Mask?
The U.S. government has made no secret of its belief that Iran’s IRGC-Cyber Electronic Command (IRGC-CEC) is behind the escalating cyber campaigns targeting U.S. and Israeli infrastructure. In 2024 and early 2025, the U.S. Treasury and Department of Justice sanctioned six IRGC-CEC operatives, naming them as key players in attacks against critical systems. All six were added to the Rewards for Justice program, with bounties of up to $10 million for information leading to their arrest. Among the most prominent is Mahdi Lashgarian, a senior cyber operations official and likely architect behind multiple OT-focused malware campaigns. While public attribution has yet to confirm a direct link between Homayunfal and the alias Mr. Sul (or Mr. Soul), mounting circumstantial evidence places him squarely in the operational core of the CyberAv3ngers campaign.
Now, he’s also become a target.

In May 2025, an Israeli patriotic hacker group calling itself WeRedEvilsOG claimed on Telegram that they had successfully breached Lashgarian’s personal and professional accounts. The group released what it described as a “partial dox drop”, including purported email addresses, internal communications, and IRGC-linked credentials. While the authenticity of the data is still under review, the leak marked the first instance of direct retaliatory targeting against a named Iranian cyber commander involved in the ICS/OT threat landscape.


Profile: Mahdi Lashgarian
- Full Name: Mahdi (Mehdi) Lashgarian
- Date of Birth: June 2, 1989
- Nationality: Iranian
- Affiliation: Senior official in the Islamic Revolutionary Guard Corps – Cyber‑Electronic Command (IRGC‑CEC)
Why he’s suspected to be “Mr. Sul”
- Matches the technical and leadership profile attributed to the IOCONTROL malware operator
- Named in the same DOJ bounty notice targeting CyberAv3ngers operators
- His sanction timeline aligns with the rollout of the most destructive CyberAv3ngers campaigns
- Newly leaked data by WeRedEvilsOG reportedly ties him to multiple IRGC infrastructure assets
The inclusion of Lashgarian in public sanctions, U.S. bounty programs, and now retaliatory hacker operations by pro-Israel actors suggests that the shadow war between Iran and Israel has entered a new phase—one where attribution isn’t just technical, it’s personal.
Final Act: A War of Machines and Messages
CyberAv3ngers has evolved beyond a conventional threat actor into a strategic asset within Iran’s asymmetric warfare toolkit—combining real-world cyberattacks, recycled leaks, and targeted propaganda to amplify psychological impact. Their operations integrate technical capability, such as IOCONTROL malware and MQTT-based command and control, with ideological messaging distributed via Telegram, Twitter, and symbolic domain registrations. Whether or not “Mr. Sul” is truly Mahdi Lashgarian, the persona functions as a force multiplier shaping narratives, intimidating adversaries, and reinforcing the perception of persistent threat. CyberAv3ngers aren't just breaching systems, they're engineering beliefs.
Sign Up For DomainTools Investigations’ Newsletter for the Latest Research
Want more from DomainTools Investigations? Be sure to sign up for our monthly newsletter to get the latest research from the team – available on LinkedIn or email.










![Domain: gitcodes[.]org resolving website with a Gitcodes service running titled: “Gitcodes - #1 paste tool since 2002!”](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263af101e496079c4d160_Code-Repository.png)
![the script calls out to “http[:]//tradingviewtool[.]com” using the user agent “TradingView.”](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263af101e496079c4d15a_tradingview-developer-mode.png)








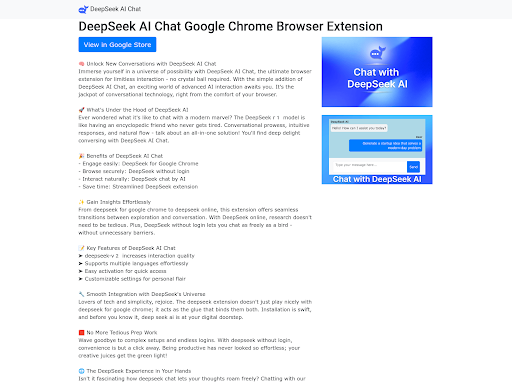
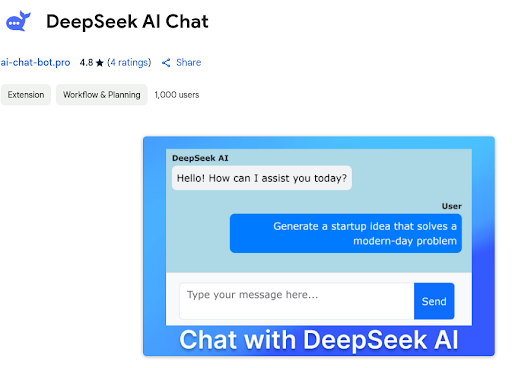
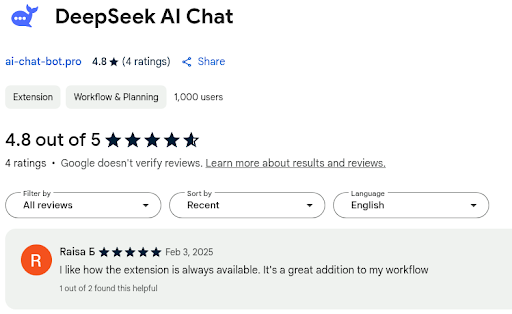
![A DeepSeek Chrome Extension themed lure website ‘deepseek-ai[.]link’](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263b288864d7f5afb84ac_AD_4nXfqv6WgEBSGGa9_Bsv0MYP90Secxk_dKkttE-g2s221Rt6rHn7MXFquTqsGoKFiV6aDrfoY8L5EdDRu5ZQ8Vf2X0TkaMhxiJw8vl8UHc80lHb90m5jURP8jc7IMPuGVoqqNcok2Bg.png)






![lafirebrigade.co[.]uk, lafireonsol[.]xyz attempt to persuade others to purchase a LA Fire themed cryptocurrency coin](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263adcee67731ab0f4b98_AD_4nXcW1mcqkE3HlkIVrjj_H5Ld5Ta0zChrygeWpSwauXAt3reS5WxgVSOHbLQN5HusW4Verqd8Fh-keX9vuoM_5TGWDPgF_FDCtKvu70h36AwocpeU-jOgWwuyyNvgZlKUue8AJ4iJ8A.png)
![lafire[.]io is another website attempting to pawn off scam crypto coin LAFIRE as a donation fund tactic.](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263adcee67731ab0f4b95_AD_4nXeTPwO0WvgKdnPjmL3T0e9TVMWo_uSJ_zTkRIAvt96XjOJlNAdLjpxCSaCaIoXhKQ6yYUrkxz1sshbhPWrN4KK3iJqIz2kK6NaRPD281mRG4HlrHxZZp6P1EB45aTC9BI4Pk3xy2Q.png)
![Myanmar Meme coin myanmarmeme[.]top](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263adcee67731ab0f4b88_AD_4nXdL0VvE3fe3lV1aqfTBVWCX0npkinxZaM93ilorsB2LZgzAo9ToEYLw6P4-sFmQJkevRYtiA_x3v-FGskdxMHw-YseSqB8e2GWJYDtf7xFKv-drkwDSxGSdZsfsGDoX0T8b9NsvnA.png)
![tootonsol[.]xyz](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263adcee67731ab0f4b7c_AD_4nXfaLyaUv6_eQKUtLyaEfbqgZ31ZwiftmI0Y8pNCwbytzn5fWk0CrPIEIyU1_fMvX4htgvM1-Jz6yHWy_bm-rBbFNXdj2D5kPxCCh2p-CRWgJI1yt9XSbXQJArtnnfrVQ3COCJm88A.png)
![gork[.]ink suspected scam meme coin attempted to capitalize on the recent news hype of Elon Musk owned xAI Grok AI model](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263adcee67731ab0f4b8e_AD_4nXd8obIUxOaX5UXJx98HBhqo6FA3Sju-qaL6zle5_MnOTf0J1Tw9q4VhBCvTFbDEZUDdI3dN7GUU2-nl0W-AgqafyIw14_OBYIlNNKL-9avwkX0RU3MwV0IXXVJNyPmeX5xALlYXKg.png)
![lafirevictimsupport[.]com, lafireonsol[.]xyz purported to collect donations on behalf of the American Red Cross](https://cdn.prod.website-files.com/6941445776ba1afe6af83186/695263adcee67731ab0f4b82_AD_4nXdVvQbUD_x8SGl5a5vyY4-73xb1Ul1wuwQKfc33rDMHab3VS0DYP7HyC9aq2hZWHRA7jJPLIVuFVdBaubzIAbHbJVe-tZ78gi_tPJf0ma_5v8ogBQUXrlhRDg1JzC6yb4JZWZnBMg.png)