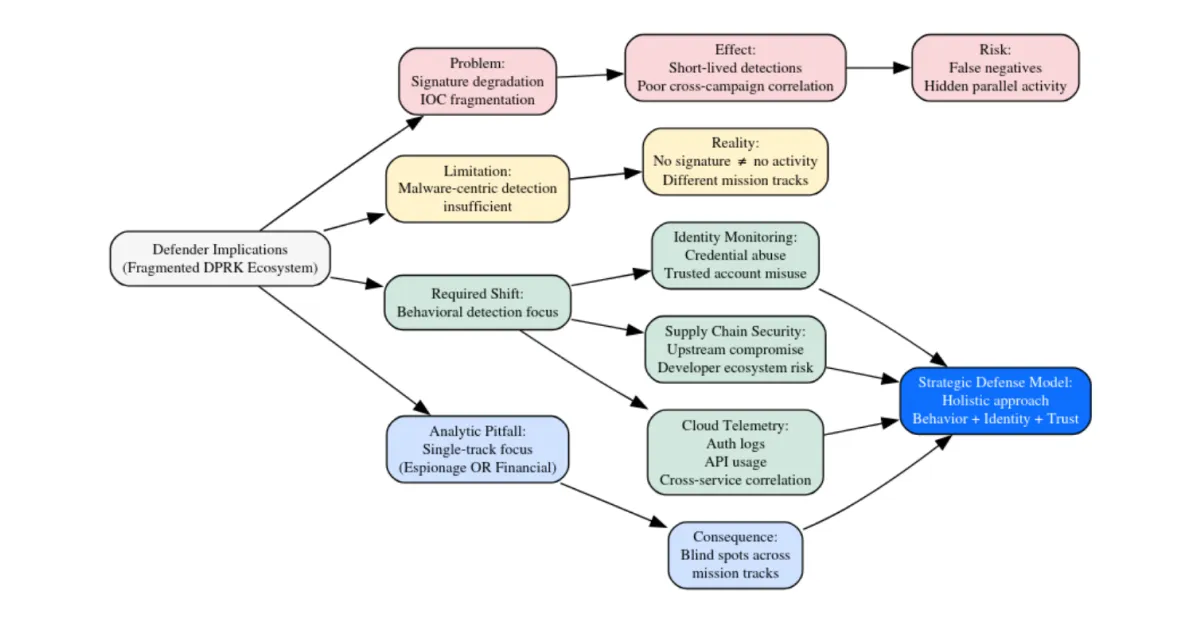
Explore the DPRK’s modular malware architecture. Analyze how North Korea uses compartmentalized toolchains for espionage, crypto theft, and strategic signaling.
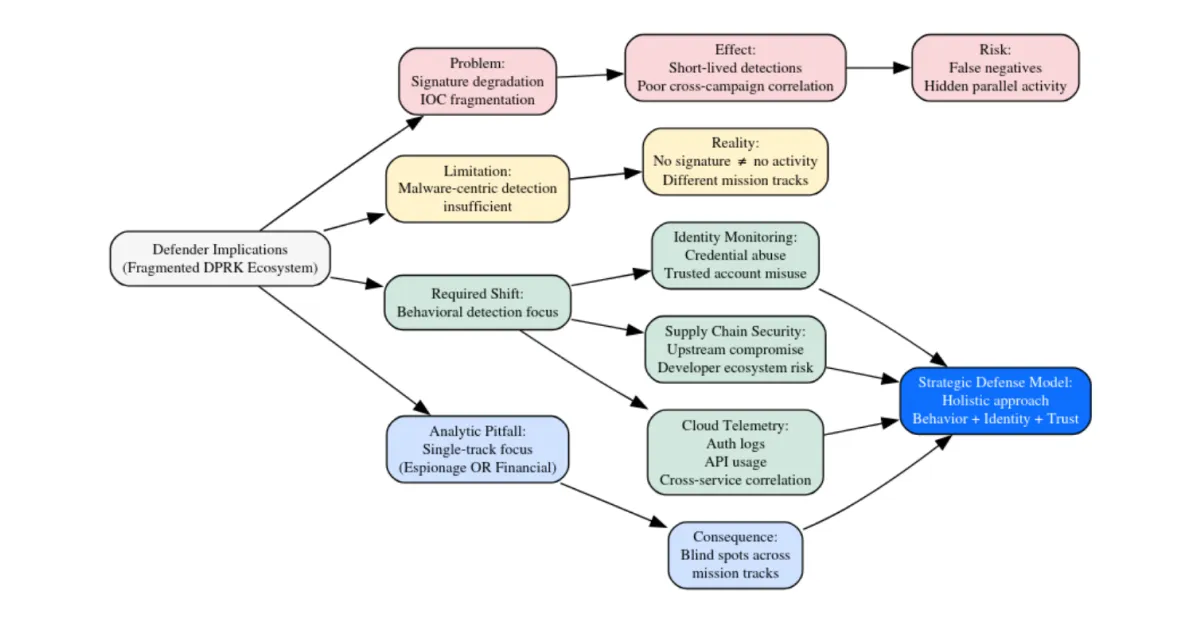
Explore the DPRK’s modular malware architecture. Analyze how North Korea uses compartmentalized toolchains for espionage, crypto theft, and strategic signaling.
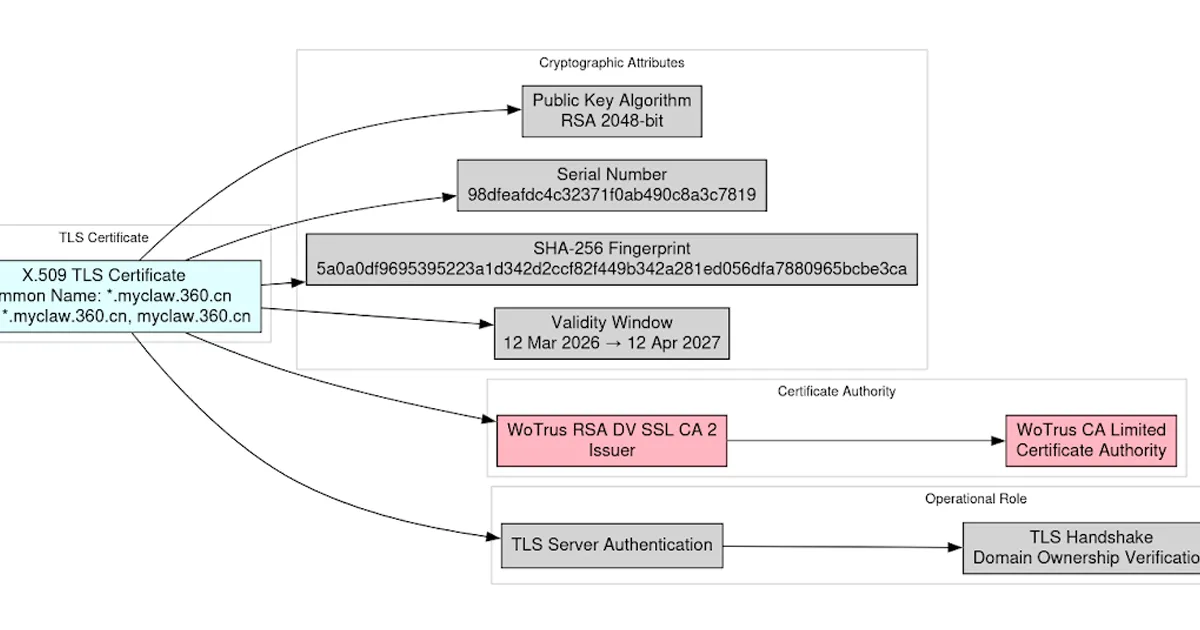
DTI analysis of a leaked TLS private key from Qihoo 360's AI security platform, covering cryptographic validation, threat scenarios, and incident response.
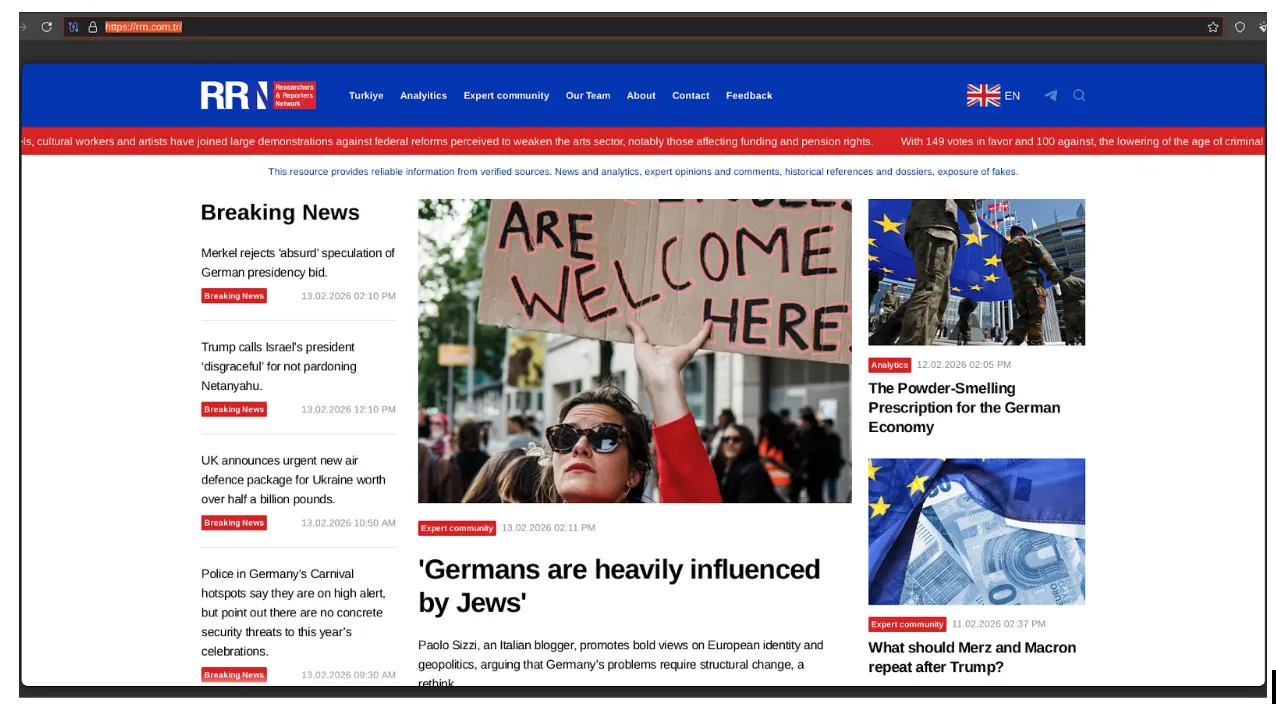
Analysis of the Doppelgänger / RRN disinformation ecosystem. Learn how this DevOps-style infrastructure uses automated media impersonation, TLD rotation, and cloud-native hosting to target global audiences and evade enforcement.

Stay protected against the "ChatGPT Ad Blocker" malware. This investigation reveals how a malicious Chrome extension uses Discord webhooks to steal private ChatGPT conversations, prompts, and metadata.
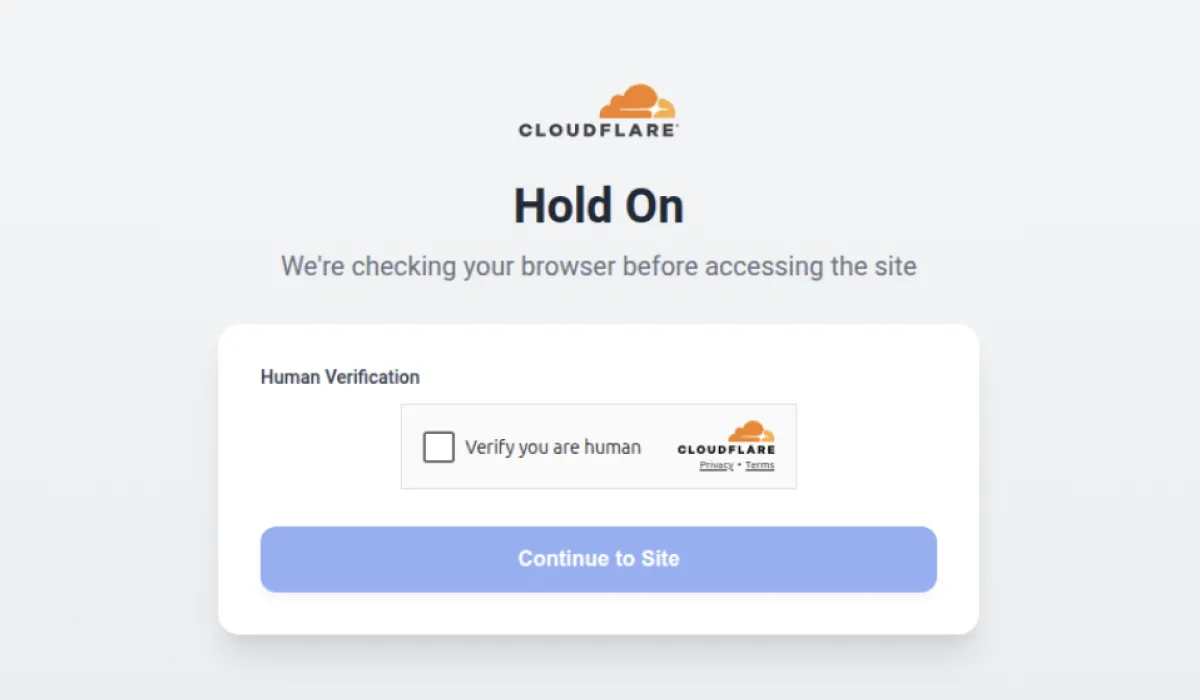
A Microsoft 365 credential harvesting campaign is exploiting CloudFlare's anti-bot and human verification features to evade detection. Learn how attackers use IP blocklists, user-agent filtering, and obfuscated scripts to bypass security scanners—and what it means for the industry.


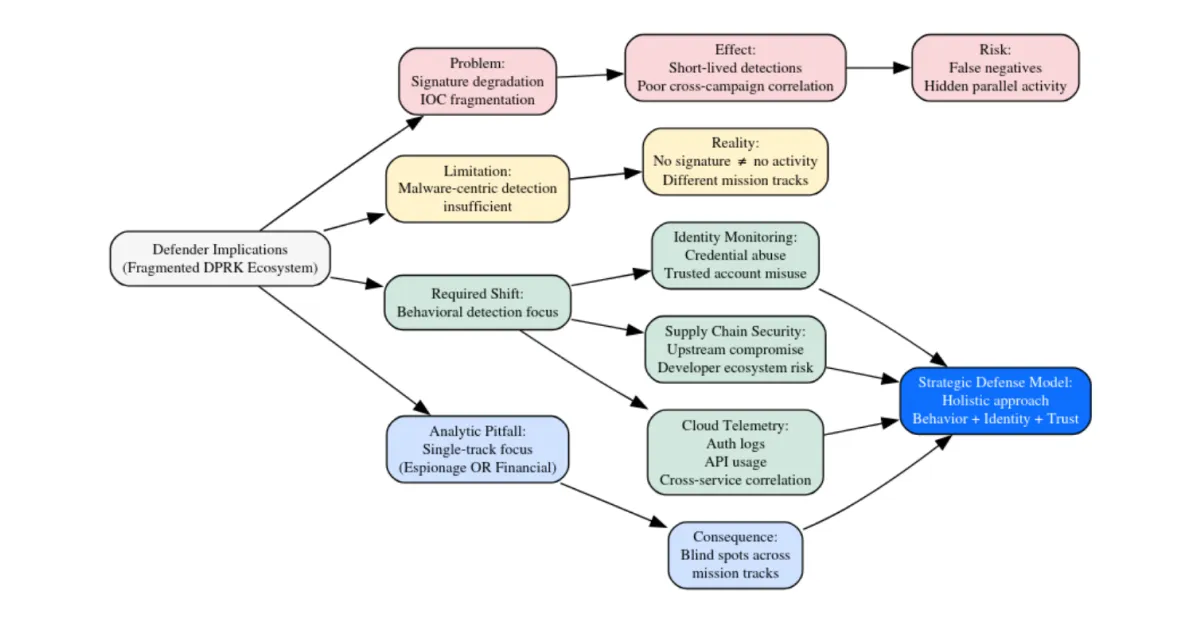
Explore the DPRK’s modular malware architecture. Analyze how North Korea uses compartmentalized toolchains for espionage, crypto theft, and strategic signaling.
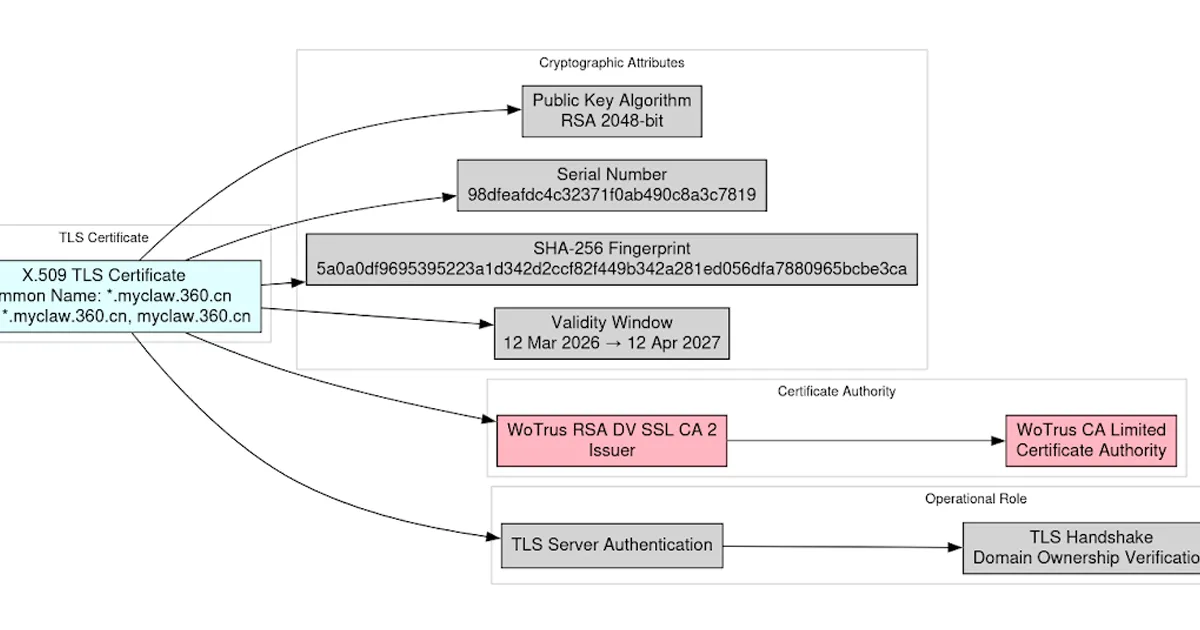
DTI analysis of a leaked TLS private key from Qihoo 360's AI security platform, covering cryptographic validation, threat scenarios, and incident response.
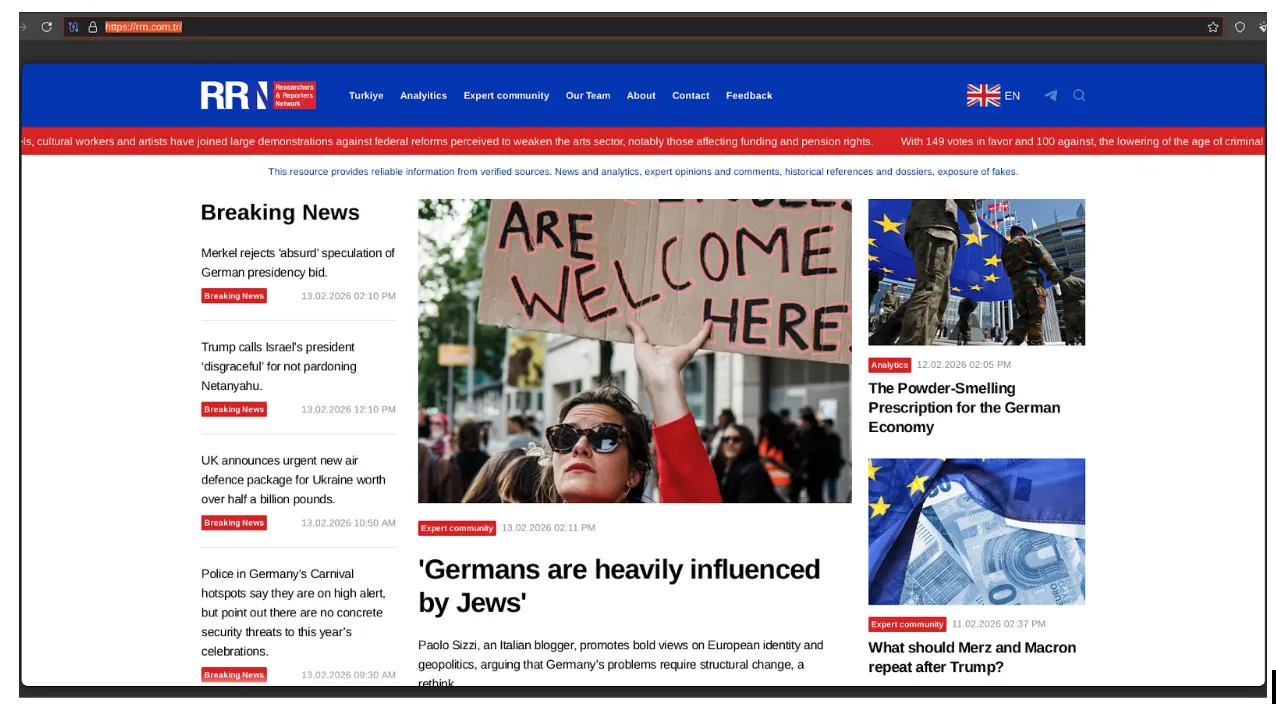
Analysis of the Doppelgänger / RRN disinformation ecosystem. Learn how this DevOps-style infrastructure uses automated media impersonation, TLD rotation, and cloud-native hosting to target global audiences and evade enforcement.

Stay protected against the "ChatGPT Ad Blocker" malware. This investigation reveals how a malicious Chrome extension uses Discord webhooks to steal private ChatGPT conversations, prompts, and metadata.
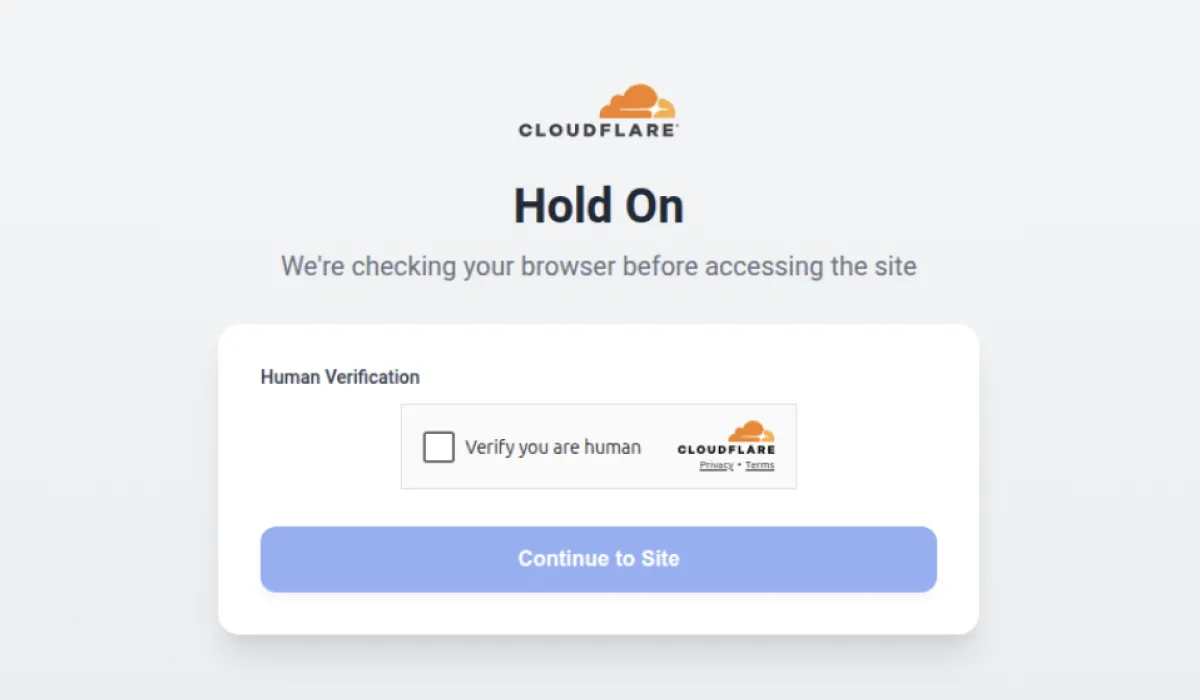
A Microsoft 365 credential harvesting campaign is exploiting CloudFlare's anti-bot and human verification features to evade detection. Learn how attackers use IP blocklists, user-agent filtering, and obfuscated scripts to bypass security scanners—and what it means for the industry.

A broken snowblower belt taught me something cybersecurity professionals often forget — saying "I don't know" isn't failure. It's where the real work begins.