A new year, a new cover image! We recently went through another rebranding exercise, which brought new collateral templates. Most noticeably, it changed our corporate website. Some of you noticed, and let us know exactly how you felt about it! The DomainTools Investigations site (https://dti.domaintools.com) also got a make-over, and I think the main website compliments our DTI site nicely!
Regular readers will notice that once again the newsletter is a week “late” - but once again, there were good reasons for it. So I’m considering releasing it on the first Tuesday of the Month, instead of the last one. If you feel strongly one way or the other, please let me know in the comments (or email me). The use of song titles with numbers that correspond to the current edition for the newsletter title is sticking around for now. My friend @Kali Fencl started that when she helped me launch this newsletter over a year ago, and while it’s getting more difficult, I’m committed.
Another thing that’s probably staying are mentions of the local weather! Returning readers know I live in Seattle, and the weather here is always a topic of conversation! For example, many of you think the rain never stops in Seattle. Movies depict torrential downpours, but we Seattleites don’t mind: Keep believing that. But in reality, fellow PNW-er Scott Losse explains it best. Check him out and follow him, he’s funny!
Unlike the East Coast (sorry friends!), we just had a brief, miraculous week of mild weather and sunshine. But as it is customary, "The Gray" has returned like clockwork. It’s that part of winter here, where blue sky quickly begins to feel like a distant memory, and dampness is king. Don’t worry, only three to four months of that!
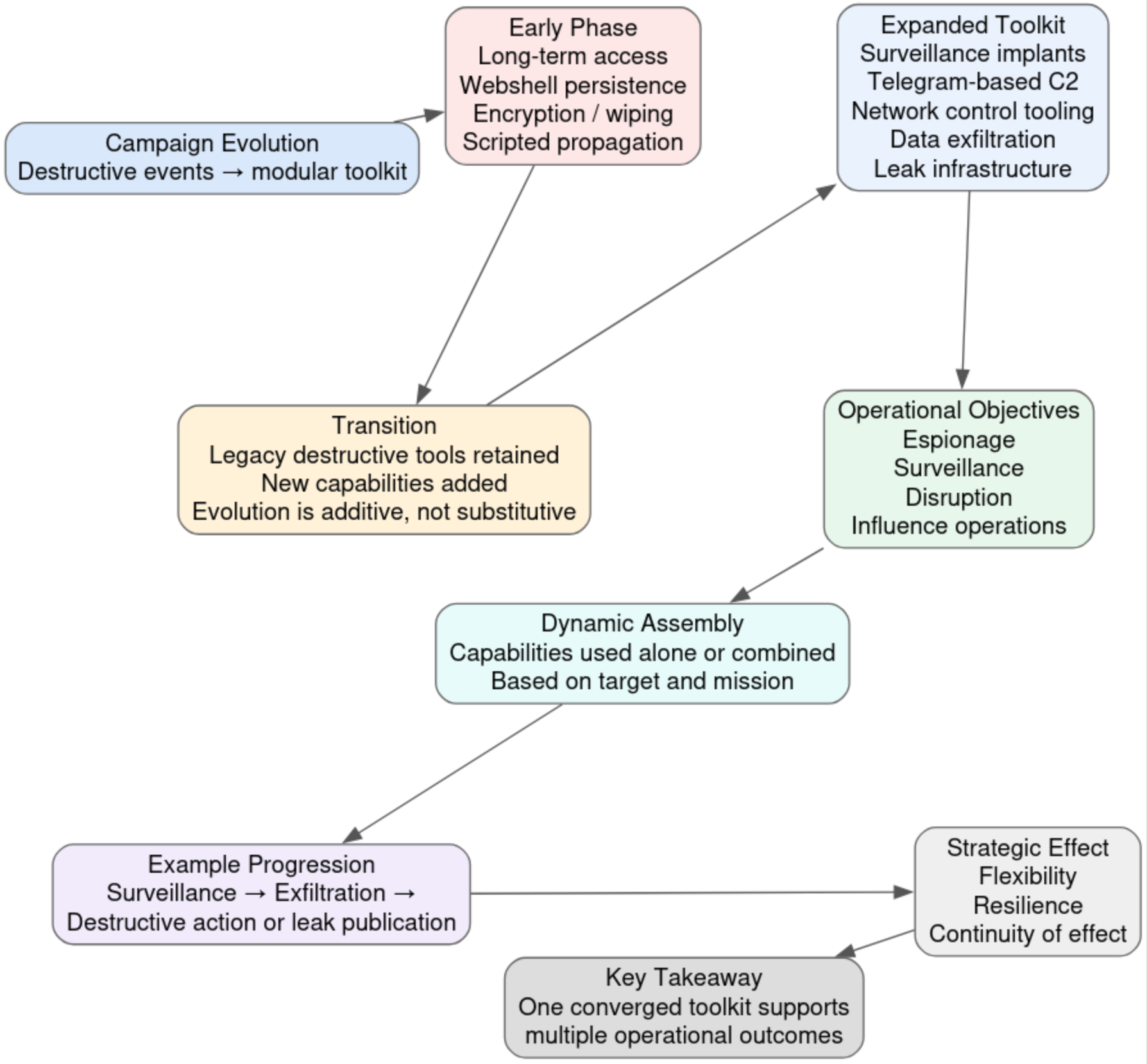
Speaking of winter, while most of the world was recovering from New Year's Eve and shovelling their driveways, my team here at DomainTools Investigations was busy dissecting a fresh mountain of data. If you thought the i-Soon leak from a while back was a one-off, think again. We’ve been heads-down on the KnownSec leak, a fascinating look at one of the supposed "white hat" companies that turned out to be part of the backbone of China’s cyberespionage ecosystem.
Beyond the geopolitical chess match, we’re also tracking some more "down-to-earth" (read: predatory) threats. Our analysts have been playing a high-stakes game of whack-a-mole with a series of dubious online gambling apps that are currently targeting users across the globe with some surprisingly sophisticated evasion tactics.
And for those of you who appreciate a shorter read with your morning coffee, we have a new SecuritySnack focused on "Phishing Interviews." This investigation highlights a particularly cold-hearted campaign that weaponizes the job hunt, exploiting the trust of applicants to harvest government credentials and to drop remote access tools.
We’ve got a lot to cover to kick off the year, so let’s dive right in, and get you all caught up!
Hot off the Presses
THE KNOWNSEC LEAK: Yet Another Leak of China’s Contractor-Driven Cyberespionage Ecosystem
In November of 2025, an allegedly massive leak of data from Chinese company “KnownSec” was posted to a github account. The leak has since been pulled off of Github and downloaded by very few, and of those few who gained access, only one uploaded 65 documents as a primer to the leak elsewhere for others to see. DTI was able to get the 65 document images and this initial investigation is derived from this slice of a much larger leak that is out there but not available.
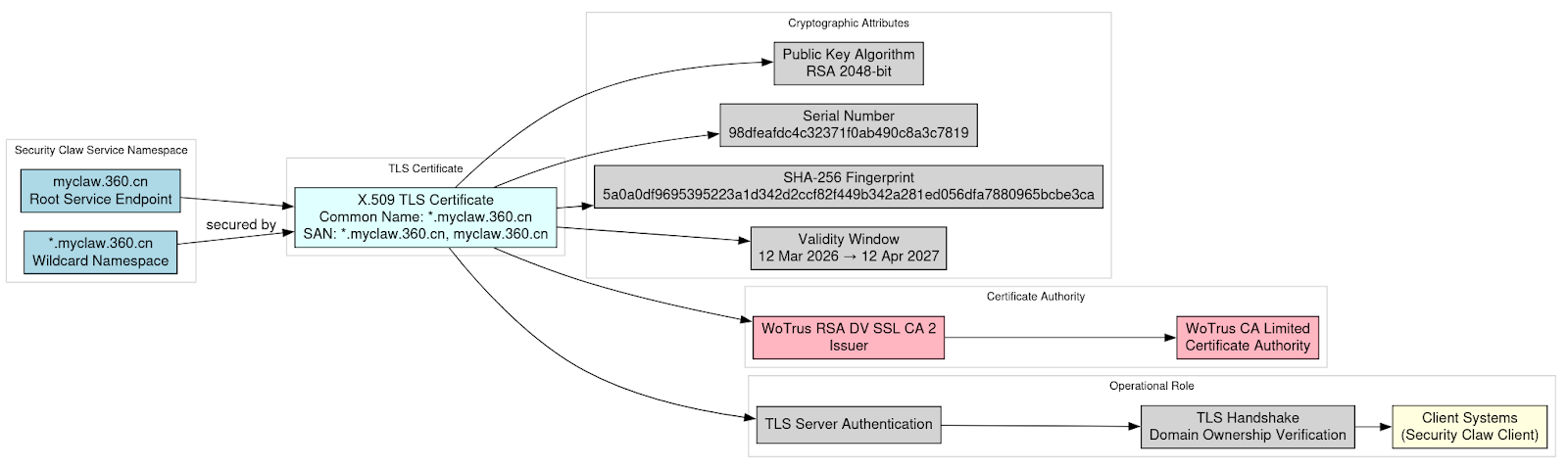
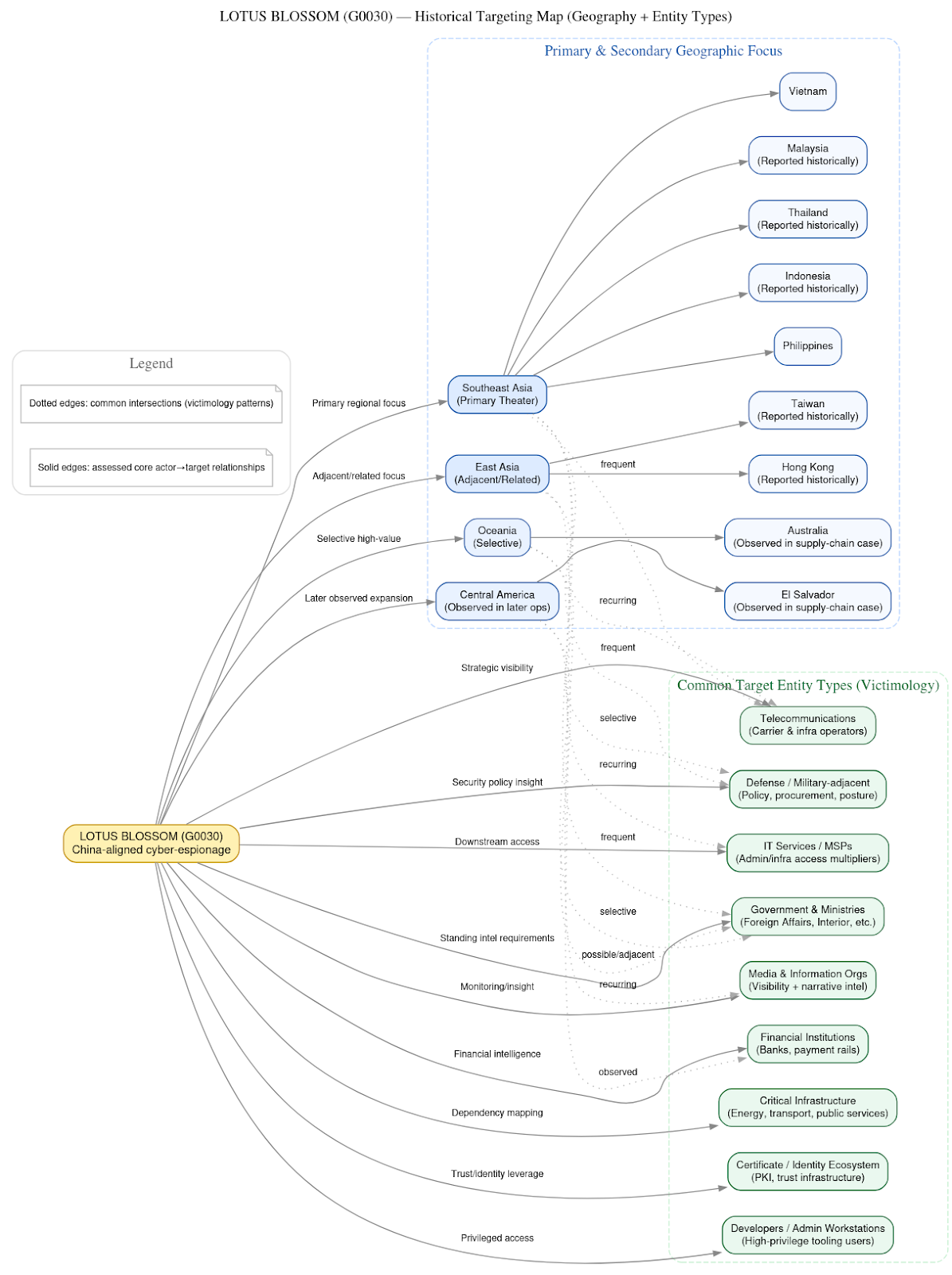
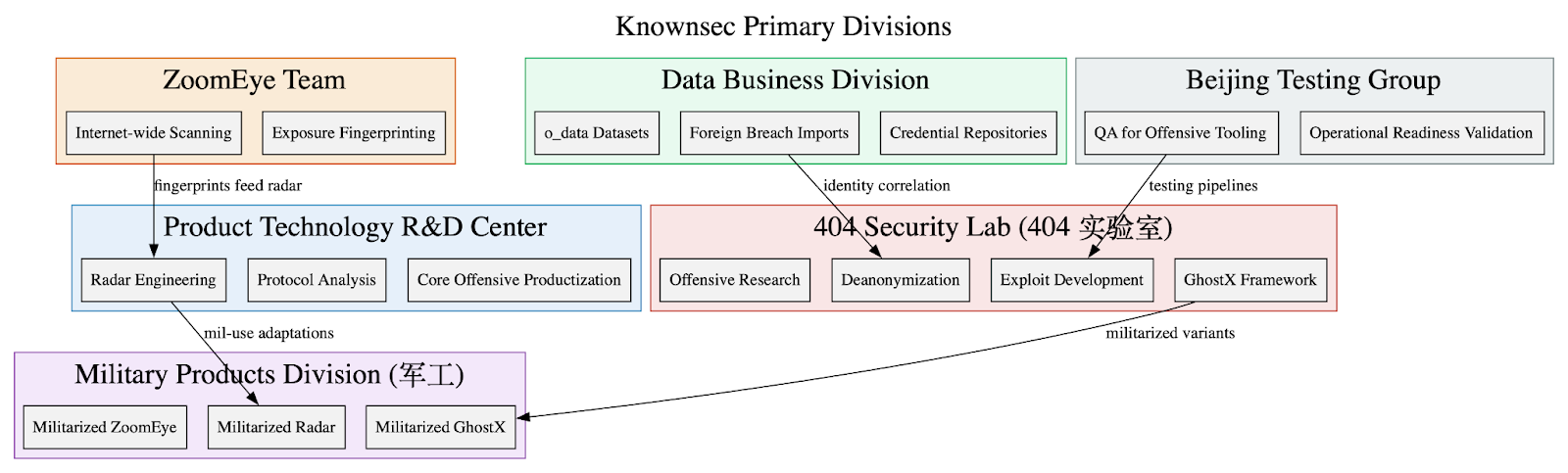
While Knownsec advertises itself as a “white hat” pillar in China’s cybersecurity landscape, the leak revealed the company operates a vertically integrated espionage stack for reconnaissance, exploitation, collection, and persistence, designed for both domestic surveillance and foreign intelligence operations in support of China’s security state.
Its internal documents, product manuals, and data repositories show a company engineered to support Chinese national security, intelligence, and military objectives. Tools like ZoomEye and the Critical Infrastructure Target Library give China a global reconnaissance system that catalogs millions of foreign IPs, domains, and organizations mapped by sector, geography, and strategic value. Massive datasets containing real names, ID numbers, mobile phones, emails, and credentials allow Knownsec and its government clients to correlate infrastructure with people, enabling rapid deanonymization, targeting, and social engineering. On top of this data foundation, Knownsec’s offensive products – GhostX, Un-Mail, and Passive Radar – purport to provide a full intrusion and surveillance pipeline.
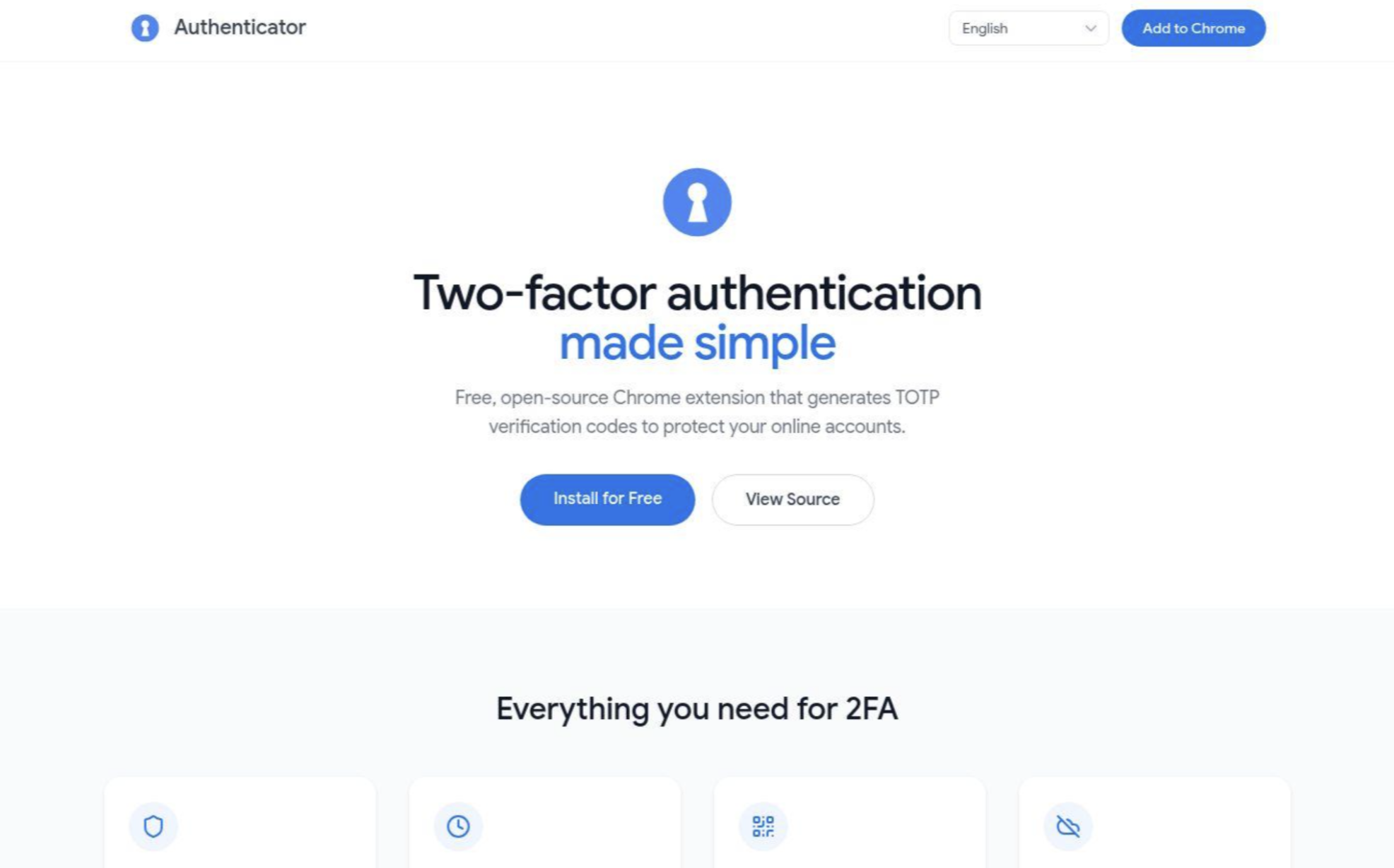
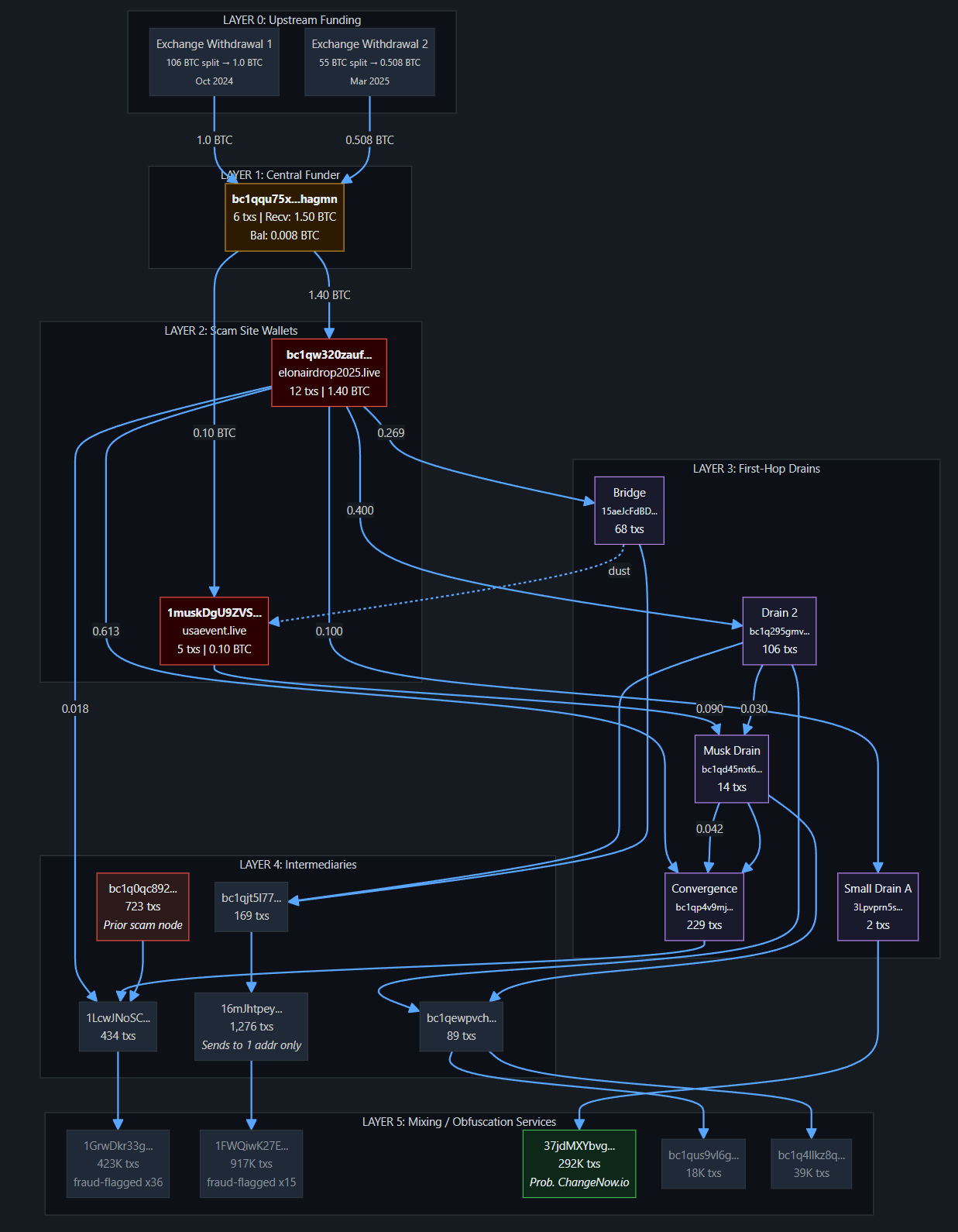
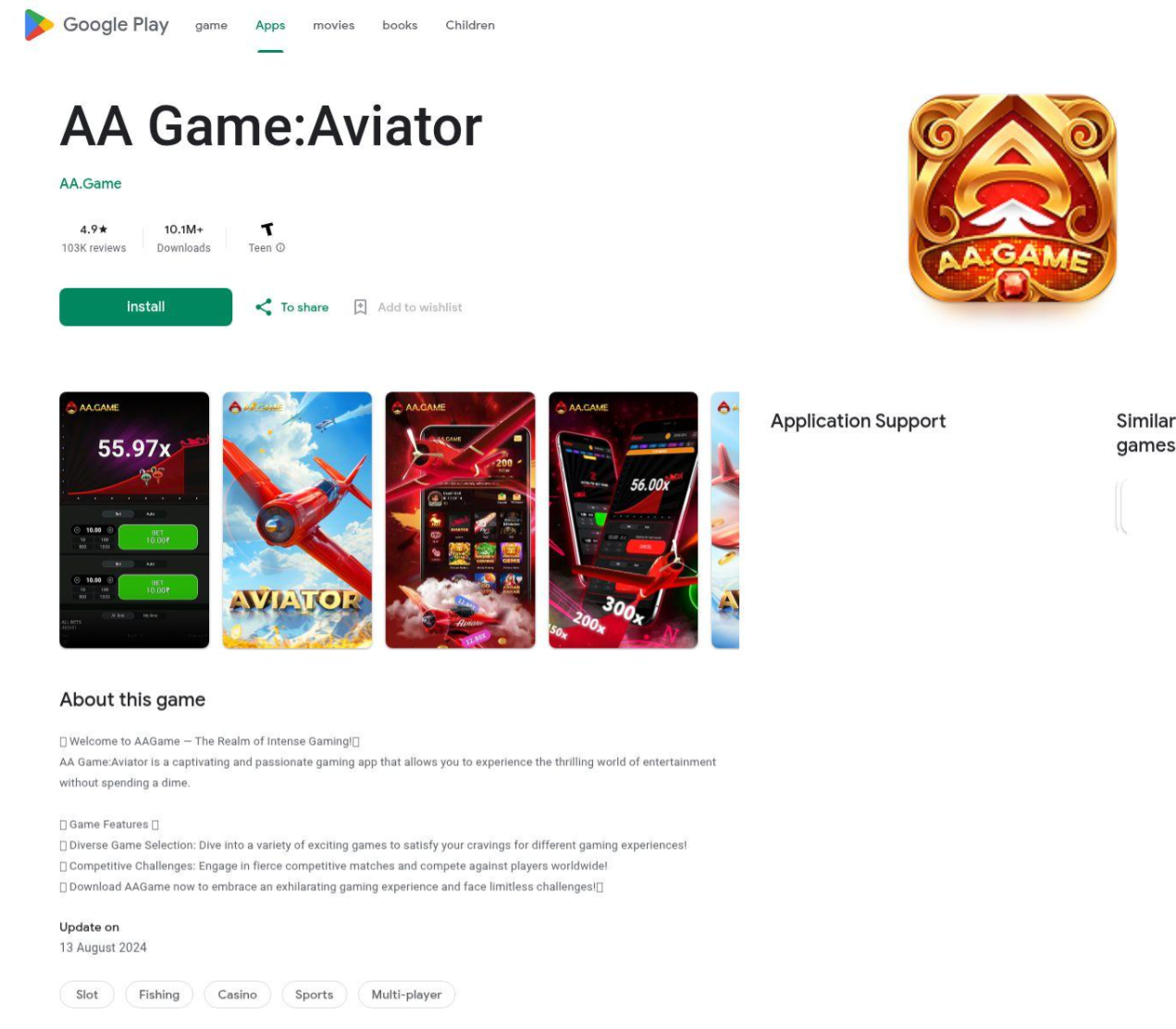
Pay to Lose: Dubious Online Gambling Games
DTI analysts identified multiple clusters of dubious Android applications created in the past few weeks that are engaged in predatory gambling and real money gaming apps. Notably, these are not registered apps. They are intentionally misleading users into thinking they are legitimate and reputable through multiple tactics like spoofing the Google Play Store, creating fake reviews, generating fake public win declarations, and creating entire brands with marketing campaigns and broad distribution tactics. These clusters also attempt to evade detection and analysis by having post install code and configuration retrievals from actor controlled sites, which serve a dual purpose of distributing region specific content to users post installation.
The investigation is segmented into three distinct infrastructure clusters. Each cluster appears to target a general set of countries including Nigeria, India, Pakistan, and the Philippines. They also appear to have non-region specific user base targeting, including English, Portuguese, and Bengali speaking users. Despite the wide range of targets, the clusters share a common theme of mobile-focused gaming or gamified gambling apps to attract users for financial gain
Security Snack: Phishing Interviews
My team uncovered a malicious actor that has created several domain masquerades of small companies posing as job boards, interview themes, and login pages since approximately August 2025.
The investigation revealed two distinct objectives. The first is a credential harvesting scheme targeting ID.me accounts — the official identity provider for US government services like the IRS and SSA — which can then be exploited to facilitate financial fraud, including tax refund theft and fraudulent unemployment benefits.
The second cluster focuses on malware delivery, tricking job seekers via fake Microsoft Teams meeting invites to download a malicious, unsigned variant of the remote access tool Connectwise. This gives the attacker access to the victim’s machine where they may conduct follow-on attacks.
What We’re Reading
In case you’re behind on your cybersecurity reading homework, DTI team member Ian Campbell’s monthly recommended reading list will get you up to speed!
- The top podcast for the month: ChinaTalk - Richard Danzig on AI and Cyber
- The top article for the month: CERT Polska - Energy Sector Incident Report
- The top research for the month: GTIG - No Place Like Home Network: Disrupting the World's Largest Residential Proxy Network
📚Checkout the full reading list here📚
Where We’ll Be
- AFCEA West 2026, San Diego, CA, 10-12 February
- BSides Seattle, Redmond, WA, 27-28 February
- NICAR 2026, Indianapolis, IN, 5-6 March
- BSides SF, San Francisco, CA, 21-22 March
Final Thoughts
As always, thank you to my returning readers! If you’re new, I hope you found this newsletter informational, helpful, and worthy of sharing with your peers. And of course I hope you will be coming back to read future editions!
We share this newsletter via email as well - if you’d prefer to get it to your inbox, sign up here.
If you missed last month's content, here are some quick links:
- Chinese Malware Delivery Domains Part IV
- The APT35 Dump Episode 4: Leaking The Backstage Pass To An Iranian Intelligence Operation
- B2B2C Supply Chain Attack: Hotel’s Booking Accounts Compromised to Target Customers
Thanks for reading - see you next month!
-Daniel