Operational Structure and Attribution
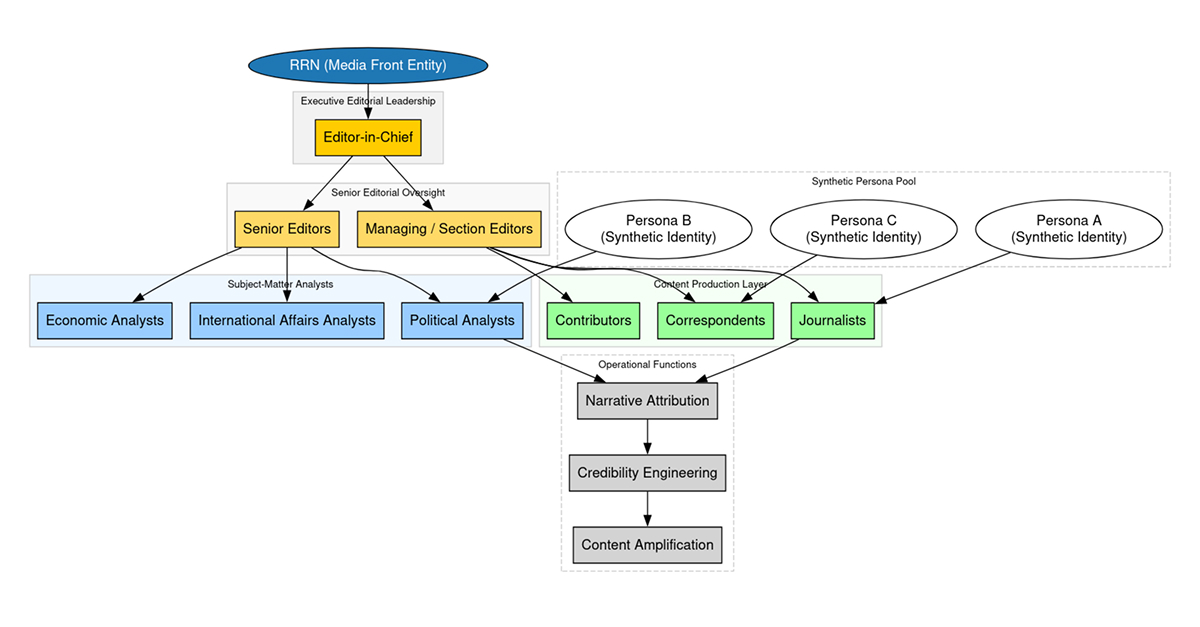
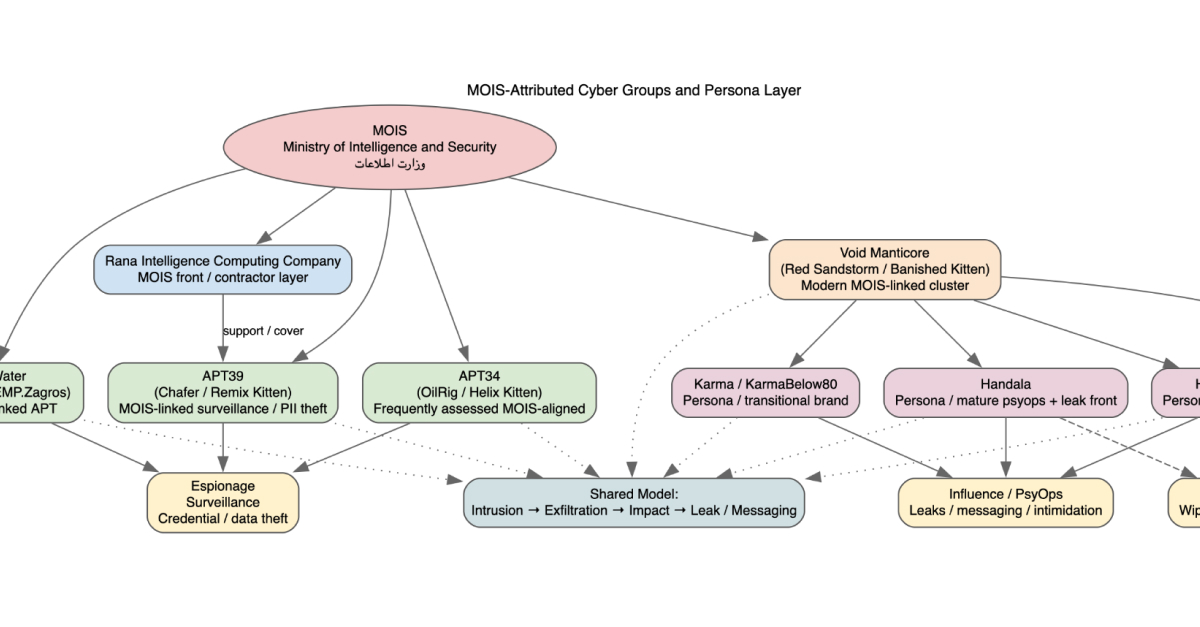
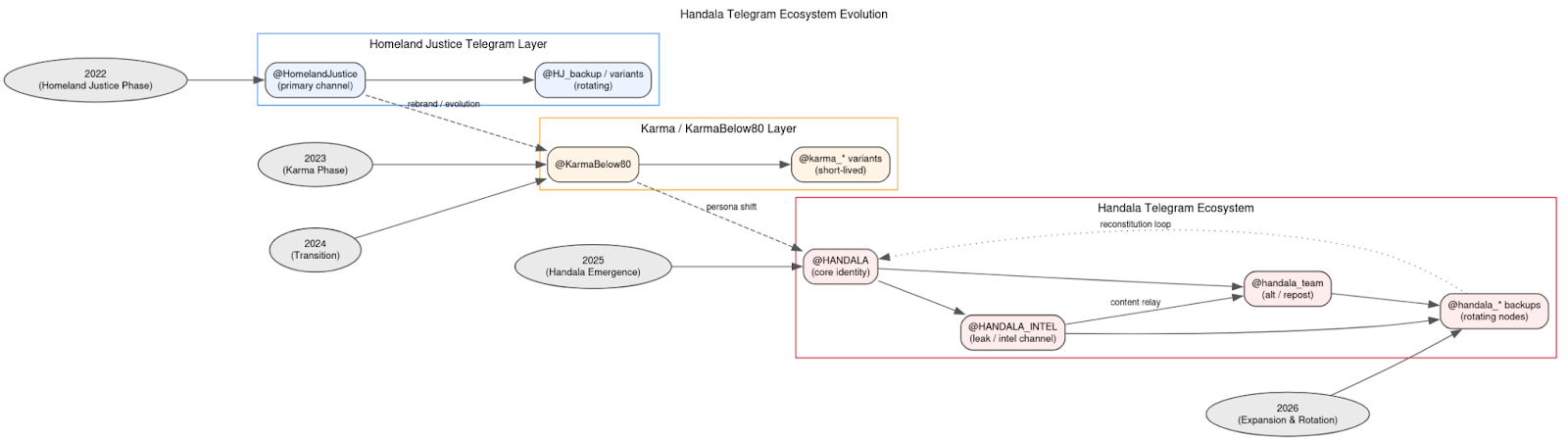
The activity attributed to Homeland Justice, Karma/KarmaBelow80, and Handala is most accurately assessed as a single, coordinated cyber influence ecosystem aligned with Iran’s Ministry of Intelligence and Security (MOIS; وزارت اطلاعات جمهوری اسلامی ایران), rather than a collection of independent hacktivist groups. These personas function as interchangeable operational veneers applied to a consistent underlying capability. Their purpose is not to reflect organizational separation, but to enable segmentation of messaging, targeting, and attribution while preserving continuity of infrastructure and tradecraft.
The use of the name “Handala” itself reinforces the ideological framing of the campaign. Handala (حنظلة) is a well-known Palestinian symbol created by cartoonist Naji al-Ali, depicting a barefoot child who has turned his back on the world in protest of injustice and dispossession. Within the context of this cyber campaign, the adoption of the Handala identity serves to anchor operations within a broader “resistance” narrative, signaling alignment with anti-Israeli and anti-Western themes while providing a culturally resonant and emotionally charged brand for influence operations.
Across all observed phases, the actors exhibit clear temporal continuity, shared infrastructure patterns, and a repeatable operational workflow. The persistence of these elements, despite rebranding, indicates centralized direction and capability management. The use of multiple identities is therefore best understood as a mechanism for narrative flexibility and operational deniability, rather than evidence of distinct actor groups.
Evolution of the Operational Model
The campaign first became visible under the Homeland Justice brand during the 2022 Albania operations, which established its foundational model: long-term access, structured data exfiltration, destructive or disruptive action, and immediate public disclosure. From the outset, technical operations were tightly coupled with messaging, indicating that disruption alone was not the objective. Instead, cyber activity was used to enable narrative exploitation and psychological impact.
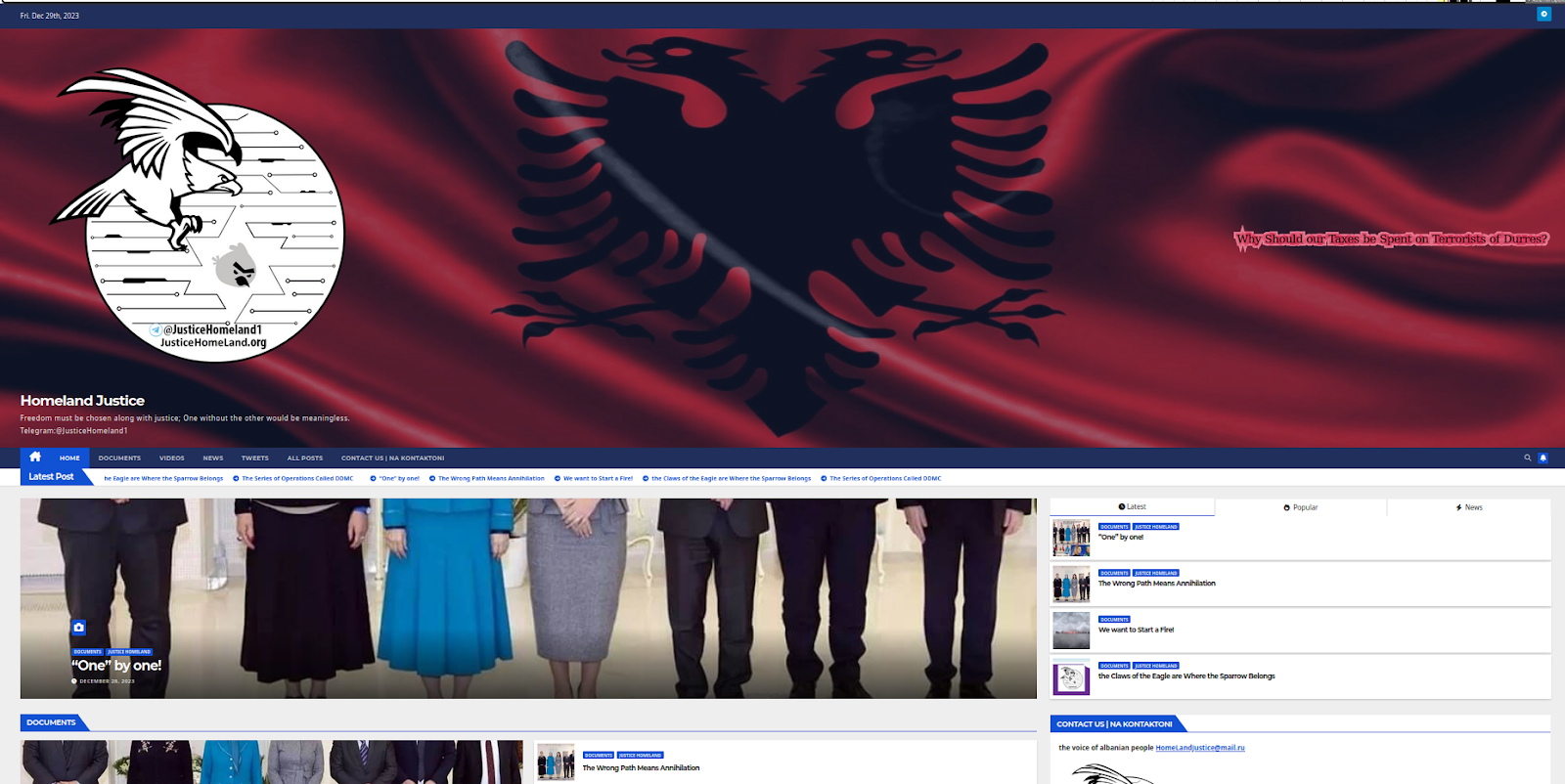
Homeland Justice 2023 aka Handala Albanian Operations
Subsequent phases reflect an additive evolution rather than a replacement of capabilities. The Karma phase introduced a hybrid execution model combining custom tooling, publicly available utilities, and hands-on-keyboard tradecraft. This increased operational flexibility and reduced reliance on bespoke malware. The Handala phase further expanded this model into a multi-vector framework integrating destruction, surveillance, and influence operations. The addition of Telegram-based command-and-control and surveillance tooling marked a shift toward persistent, person-centric targeting, extending the campaign’s reach beyond institutions to individuals.
Convergence of Capabilities
Recent activity demonstrates a convergence of previously distinct operational components into a unified framework. Intrusion, surveillance, disruption, and influence are no longer sequential phases, but simultaneous and interdependent functions. The Stryker incident illustrates this evolution, where large-scale data exfiltration, enterprise-level disruption through administrative control systems, and immediate narrative amplification were executed in a tightly integrated manner.
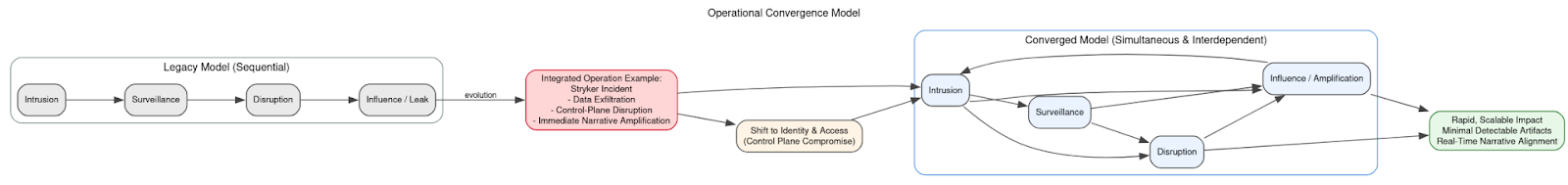
This shift reflects a broader transition away from malware-centric operations toward identity and access compromise at the control-plane level, enabling rapid, scalable impact with minimal reliance on detectable artifacts. It also demonstrates an increased ability to align technical execution with strategic messaging in near real time.
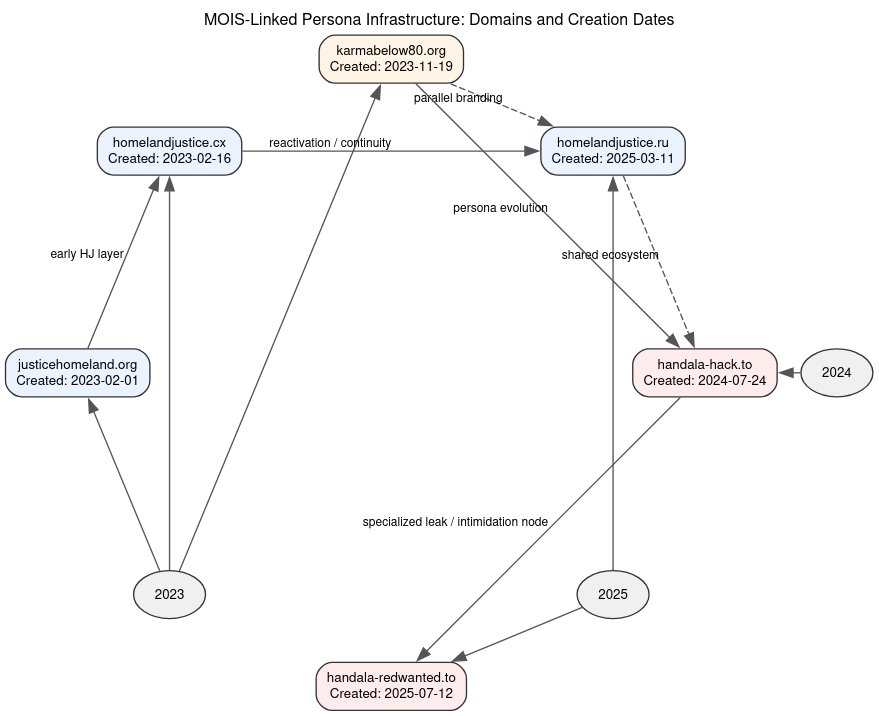
Infrastructure and Amplification Model
The ecosystem is supported by a layered infrastructure designed to separate operational functions while maintaining resilience. Public-facing domains and Telegram channels act as dissemination and amplification nodes, where messaging is curated, claims are published, and stolen data is selectively exposed. These platforms are integral to the operational workflow, bridging the gap between technical compromise and public perception.
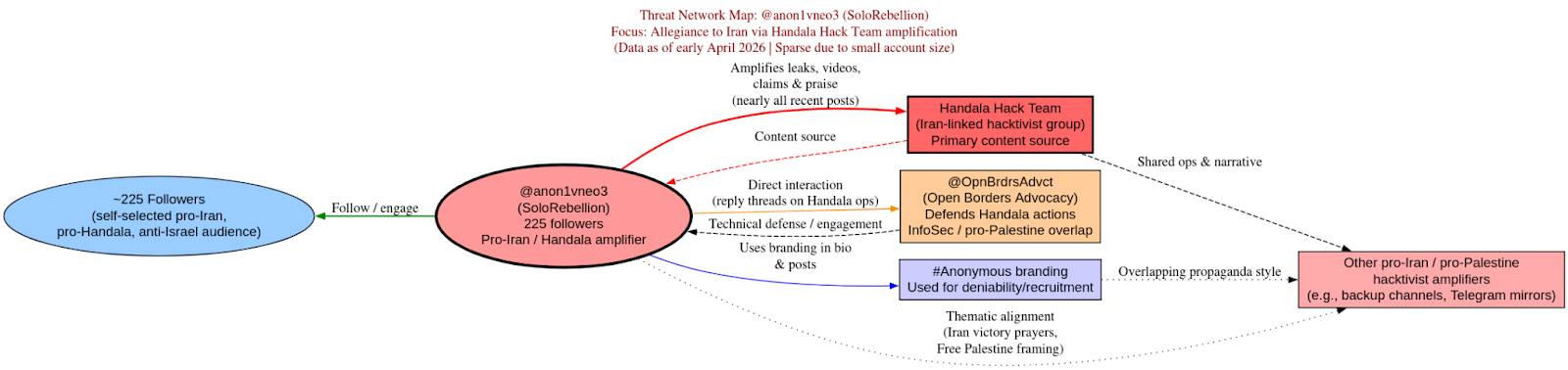
Twitter April 2026 Amplification acct
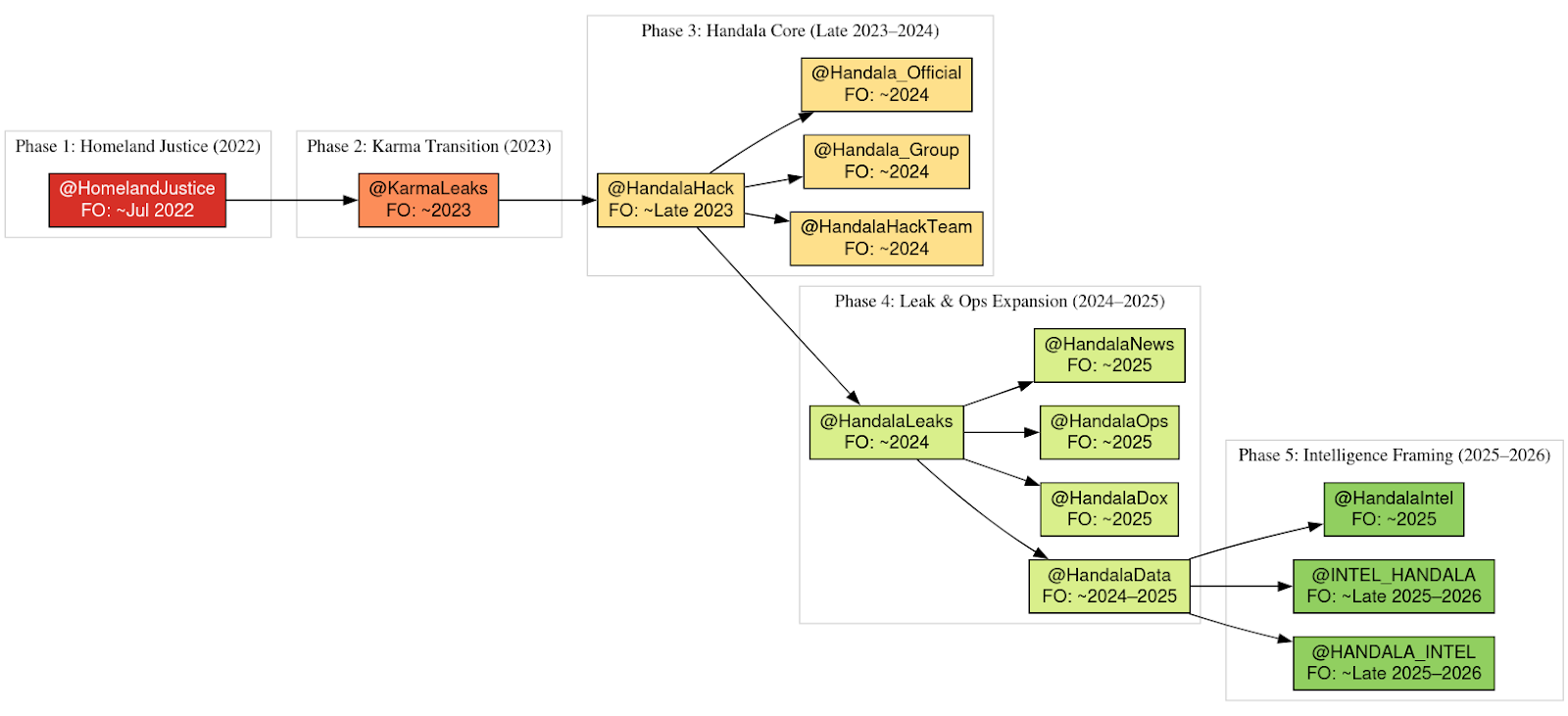
Telegram Amplification Accounts Over Time
Infrastructure is intentionally ephemeral. Domains are frequently rotated, and personas are rebranded or reactivated as needed. However, naming conventions, messaging patterns, and distribution channels remain consistent, allowing the campaign to maintain coherence despite disruption. This results in a system where infrastructure is disposable, but identity and narrative persist.
Operational Effects and Impact
The observable impact of this ecosystem reveals a consistent divergence between claimed and verified outcomes. While the actors present their operations as large-scale destructive intrusions, confirmed system-level disruption is relatively rare. Instead, the majority of activity produces data exposure, reputational damage, and psychological pressure, often targeting both institutions and individuals.

Media hype cycle of low hanging fruit hack of FBI director’s 2009 email account
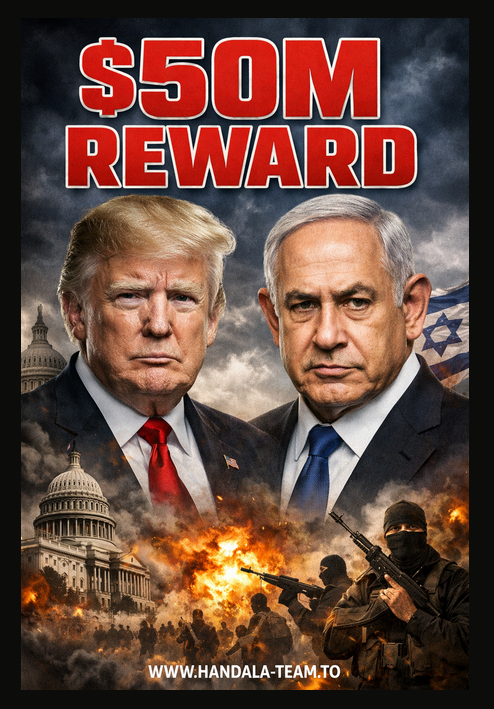
Sensationalized Reward Offer for Trump or Netanyahu 2026
Many claims remain partially verified or unverified, yet still generate significant downstream effects. Organizations are compelled to investigate and respond, media coverage amplifies the narrative, and uncertainty is sustained. In practice, the perception of compromise often produces effects equivalent to confirmed compromise, enabling the actors to achieve disproportionate impact relative to their demonstrated technical capability.
Role of Telegram and Surveillance Integration
Telegram plays a central role within this ecosystem as both a command-and-control channel and a public dissemination platform. By leveraging a widely trusted service, the actors reduce infrastructure overhead and increase operational resilience. Malware can communicate with operator-controlled bots using encrypted channels indistinguishable from legitimate traffic, while Telegram channels simultaneously serve as hubs for messaging and amplification.
The integration of surveillance capabilities further expands the campaign’s scope. Trojanized applications and user-targeted lures enable persistent monitoring of individuals, particularly dissidents and opposition networks. This allows the actors to move seamlessly from covert collection to overt exposure, reinforcing the link between technical activity and psychological pressure.
Strategic Assessment
This ecosystem represents a state-directed instrument of cyber-enabled influence, in which technical operations are tightly integrated with narrative manipulation and media amplification dynamics to achieve coercive and strategic effects. Intrusion enables access, access enables collection, and collection enables controlled disclosure. However, the decisive phase is the conversion of that disclosure into a high-visibility narrative event. Incidents such as the compromise of Kash Patel demonstrate how relatively limited technical access can be operationalized through the modern news cycle, where rapid reporting, social media propagation, and secondary analysis amplify the perceived scale and significance of the breach. In this model, the hype cycle is not incidental; it is a core component of the operation, transforming modest compromises into strategic effects.
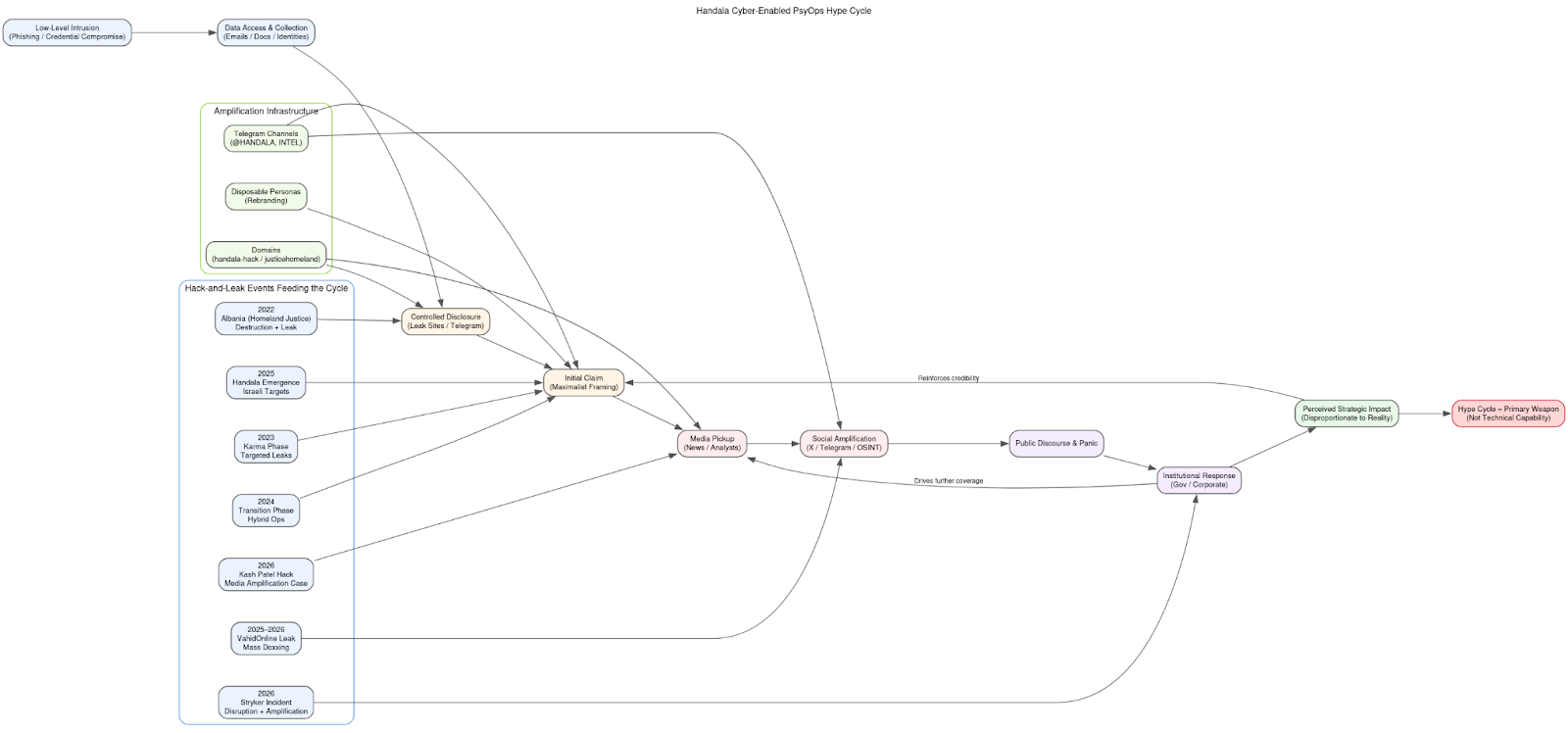
The maintenance of multiple concurrent personas, the rapid regeneration of infrastructure, and the consistent integration of cyber and information operations indicate a mature and adaptive capability optimized for this environment. These personas allow the actors to continuously seed new events into the information ecosystem, while disposable domains and Telegram channels ensure persistence of messaging even as infrastructure is disrupted. Each operation is effectively designed as a trigger for a predictable amplification loop: initial claim, media pickup, public discourse, and institutional response. This loop imposes reputational and operational costs on targets regardless of the underlying technical depth.
As a result, the system can be activated, scaled, or redirected in response to geopolitical conditions with minimal reliance on sustained intrusion capability. Its effectiveness lies in the ability to synchronize cyber activity with the tempo of the information environment, using the hype cycle to magnify impact across multiple theaters and target sets. In practical terms, this means that perception, attention, and narrative momentum are treated as operational objectives on par with access and disruption, allowing the actors to remain effective even when technical outcomes are limited.
Conclusion
Homeland Justice, Karma, and Handala should be treated as components of a unified operational apparatus, not discrete threat actors. Their effectiveness does not derive from sustained technical superiority or advanced intrusion tradecraft, but from their ability to fuse low-to-moderate cyber capability with disciplined psychological and informational operations to create a cohesive and scalable system.
Across observed incidents, the underlying modus operandi is consistent with opportunistic, identity-layer compromise rather than sophisticated exploitation. Initial access is frequently achieved through relatively low-complexity methods such as password guessing, credential stuffing, phishing, exploitation of weak or reused credentials, and poor security hygiene in externally exposed services. Even in higher-impact cases such as Stryker Corporation, the available indicators suggest that compromise likely originated from weak identity and access controls or misconfigured management infrastructure, rather than novel vulnerabilities or advanced malware deployment. This aligns with a broader pattern in which targets are selected not for hardened defenses, but for accessible attack surfaces and exploitable operational gaps.
In this sense, these actors operate closer to low-tier intrusion crews or access brokers in their technical execution. However, what differentiates them is not how they gain access, but what they do with it. Limited footholds – often no more than a compromised account, exposed dataset, or peripheral system – are systematically transformed into hack-and-leak operations designed for maximum psychological and media impact. Small or ambiguous datasets are framed as large-scale breaches; partial access is presented as systemic compromise; and unverified claims are released in ways that ensure rapid amplification.
This is where the integration with influence operations becomes decisive. The ecosystem relies heavily on timing, narrative construction, and media exploitation to convert low-level technical events into high-visibility incidents. The breach and leak involving Kash Patel is illustrative: a compromise of a personal account technically limited in scope was rapidly elevated into a widely covered event, generating disproportionate attention relative to its technical impact. This reflects a deliberate strategy in which the news cycle functions as an extension of the operation, amplifying reach and reinforcing perceived capability.
Targets are therefore often targets of opportunity, selected for their symbolic value, media relevance, or potential to generate secondary effects. The objective is not persistent access or long-term control, but event generation creating moments that can be exploited for narrative gain. Each operation is structured to trigger a predictable response cycle: disclosure, media coverage, public reaction, and institutional response. This cycle imposes real costs on victims and defenders, regardless of the underlying technical depth of the compromise.
The result is a model in which technical simplicity coexists with strategic effectiveness. Low-level intrusions, when paired with coordinated amplification and ambiguity, produce outcomes typically associated with more advanced actors. The distinction between hacking and influence is therefore not incidental but intentional. Cyber activity provides the entry point, but the primary objective is the shaping of perception, the erosion of confidence, and the projection of capability.
This approach reflects a broader evolution in state-aligned cyber operations. Rather than investing exclusively in high-end capabilities, actors can achieve comparable strategic effects by combining accessible intrusion techniques with sophisticated information operations. In this framework, success is measured not by the depth of compromise, but by the ability to control the narrative surrounding that compromise.
Accordingly, Homeland Justice, Karma, and Handala should be understood not as elite intrusion actors, but as hybrid operators leveraging low-cost cyber access to generate high-impact psychological effects. Their significance lies in demonstrating that, in the current information environment, perception can be weaponized as effectively as technical capability. Furthermore, it demonstrates that even modest breaches can be scaled into strategic events when amplified through media and narrative control.