Who doesn’t love a good “The Sound of Music” reference! But did you know that there is a completely different movie based on the same subject matter that was filmed in Germany in 1956, a whole nine years before The Sound of Music? It’s called “Die Trapp-Familie” (or “The Trapp Family”). Unlike the American version, where the von Trapps escape to Switzerland at the end (cue Julie Andrews singing “Climb every Mountain”) - in the German version they emigrate to America, which is also what the “real” von Trapps did. And then there is also a movie sequel that captures their time living in the United States. And before you question my Super Fan status, yes I’ve visited most of the sites in and around Salzburg where “The Sound of Music” was filmed. I highly recommend it!
For those of you who came here for the weather report: April in Seattle was cold and wet. May is off to a bang with an 80 degree day already. This is totally fine.
SPeaking of April, it’s been a high-velocity month for the team. Two weeks ago I was in Munich Germany for the FIRST CTI Conference, while the rest of the team spent most of their time untangling the increasingly complex webs of state-sponsored modularity, from the DPRK’s institutionalized "burn-and-replace" tactics to the shifting veneers of Iranian influence operations.
In this edition, we’re breaking down how these actors are moving away from one-off attacks toward sustainable, parallel pipelines of espionage and disruption. We also take a look at some "clean" Chrome extensions that aren't nearly as helpful as they claim to be.
Let's dive into the research and get you caught up!
Hot off the Presses
DPRK Malware Modularity: Diversity and Functional Specialization
DTI analysts broke down the modular design of the DPRK’s malware ecosystem. Analysis of multiple vendor, government, academic, and secondary reporting confirmed the DPRK operates a mature portfolio model of parallel malware development and rotation pipelines aligned to discrete strategic objectives. This structure enables the DPRK to conduct simultaneous espionage, revenue generation, and disruptive operations without cross-contaminating tooling, infrastructure, or exposure.
What distinguishes the DPRK cyber program is not the existence of malware rotation itself, but how completely burn-and-replace logic is integrated into program design.Across the DPRK’s malware ecosystem, different DPRK threat actors are identified with specific malware tracks: espionage (Kimsuky), financial operations (Lazarus Group), and disruptions and coercion (Andariel). While the burn-and-replace model operated by the DPRK is not unique among nation-state threat actors, the degree of institutionalization and mission coupling seen in DPRK operations is unusually pronounced compared to their counterparts in Russia, Iran, and the PRC.

Handala: MOIS Linked Cyber Influence Ecosystem Threat Intelligence Assessment
DTI spent a lot of April analyzing cyber threats resulting from the conflict in Iran. Our researchers took a deep dive into the threat actor personas aligned with Iran’s Ministry of Intelligence and Security (MOIS; وزارت اطلاعات جمهوری اسلامی ایران). Specifically, the activity attributed to Homeland Justice, Karma/KarmaBelow80, and Handala was assessed as a single, coordinated cyber influence ecosystem aligned with the MOIS. These personas function as interchangeable operational veneers applied to a consistent underlying capability. Their purpose is not to reflect organizational separation, but to enable segmentation of messaging, targeting, and attribution while preserving continuity of infrastructure and tradecraft.
Across all observed phases, the actors exhibit clear temporal continuity, shared infrastructure patterns, and a repeatable operational workflow. The persistence of these elements, despite rebranding, indicates centralized direction and capability management.

MOIS Linked MOIST GRASSHOPPER/ Homeland Justice/ KarmaBelwo80/ Handala Hackers/ Campaigns and Evolution
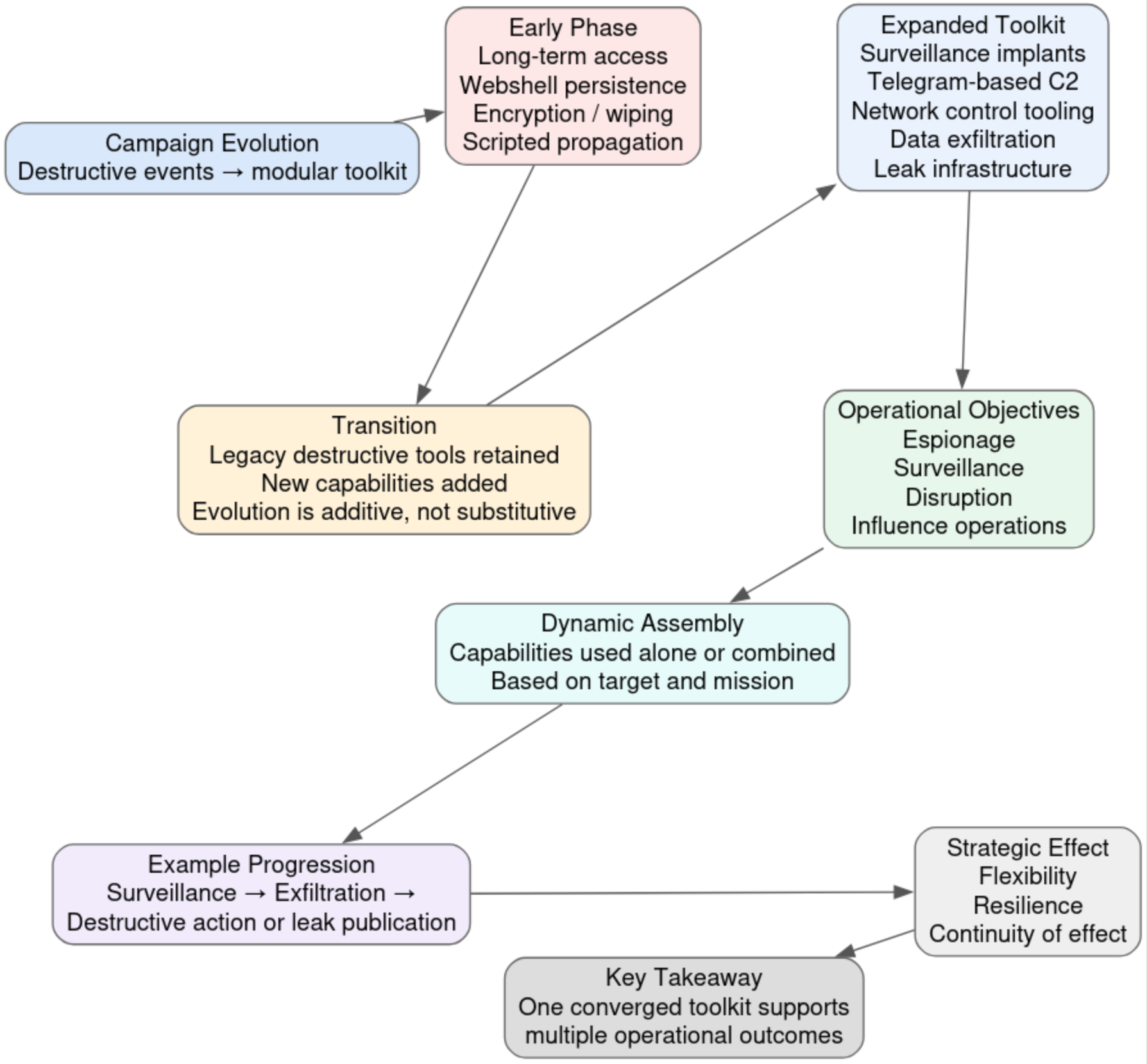
As part of our team’s research into the MOIS cyber influence ecosystem, we examined evidence spanning U.S. government reporting, private-sector threat intelligence research, passive DNS and infrastructure enrichment, and longitudinal review of archived web and Telegram content to build a comprehensive analysis of the campaigns and operational evolution of the Handala/Homeland Justice/ Karma personas. Across these personas, the actors consistently employ a repeatable pattern of intrusion, data exfiltration, disruptive or destructive action, and rapid public disclosure through controlled infrastructure. This is reinforced by shared or cross-referenced domains, persistent use of Telegram for amplification and coordination, and common hosting and obfuscation strategies. The personas also exhibit consistent rhetorical framing, target selection logic, and methods of psychological coercion.
The campaign demonstrates a progression from discrete, high-impact destructive events into a modular and adaptive operational toolkit capable of supporting a wide range of objectives across multiple target sets. Early activity, particularly during the Albania operations, was centered on singular, coordinated events in which long-term access culminated in ransomware-style encryption, wiping, and public attribution. Over time, however, these capabilities were not abandoned; instead, they were retained and integrated into a broader operational framework that supports espionage, surveillance, disruption, influence operations, and destructive capabilities in parallel, culminating in the attack on Stryker in March 2026.
SecuritySnack - The AI Frame Campaign Continues
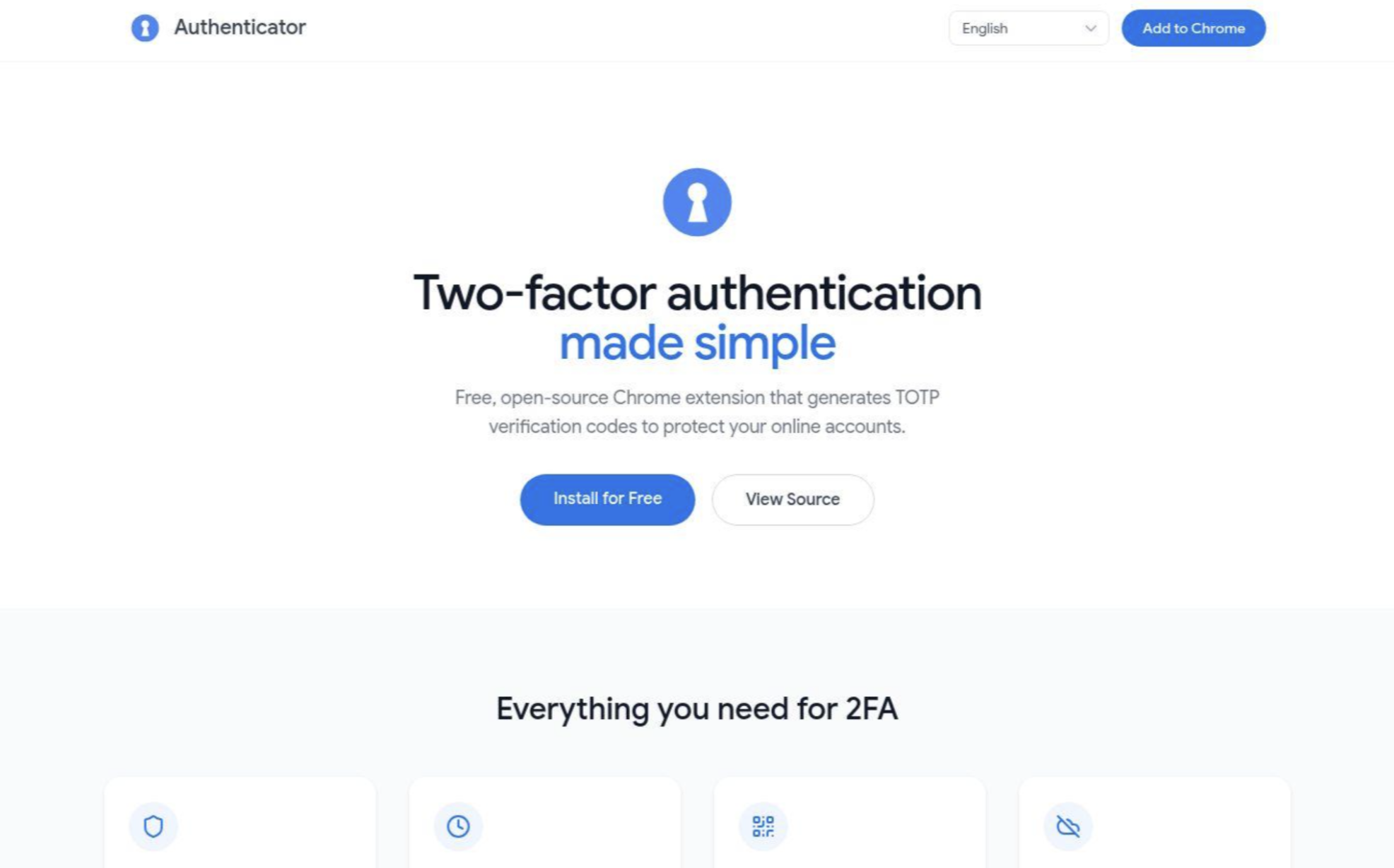
DTI analysts identified a Chrome extension impersonating Google's Authenticator application as part of an ongoing malicious campaign active since at least early 2026. The extension appears to use Chrome's localization system and skeleton code to bypass security reviews. Despite its functional appearance, it requests broad, unnecessary permissions and contains "dormant infrastructure”. This suggests a staged deployment model using a deploy clean, update dirty strategy, where the extension remains trustworthy on the surface while maintaining the architectural groundwork to deliver a malicious update without requiring further permission approvals from the user or the store.
This extension is linked to at least six others through a shared developer front, two of which already carry fully operational malicious payloads. These extensions utilize hidden iframes to inject attacker-controlled content into every webpage, deploy fraudulent paywalls for free services, and maintain bidirectional communication with C2 servers. The infrastructure maps directly to the AiFrame campaign, which reportedly compromised over 260,000 users from 2025 to present.
📚What We’re Reading
In case you’re behind on your cybersecurity reading homework, DTI team member Ian Campbell’s monthly recommended reading list will get you up to speed!
- The top article for the month: watchtowr Labs - The Internet Is Falling Down, Falling Down, Falling Down (cPanel & WHM Authentication Bypass CVE-2026-41940)
- The top research for the month: Europol - Internet Organised Crime Threat Assessment (IOCTA) 2026
- The top podcast for the month: Lawfare - The Shadowy World of Ransomware with Professor Anja Shortland
📚See the full reading list here
Where We’ll Be
- DNS OARC, Edinburgh, UK - 16-17 May
- SLEUTHCON, Arlington, VA - 05 June
Final Thoughts
As always, thank you to my returning readers! If you’re new, I hope you found this newsletter informational, helpful, and worthy of sharing with your peers. And of course I hope you will be coming back to read future editions!
We share this newsletter via email as well - if you’d prefer to get it to your inbox, sign up here.
If you missed last month's content, here are some quick links:
- Doppelgänger / RRN Disinformation Infrastructure Ecosystem 2026
- SecuritySnack - CloudFlare Anti-Security For Phishing
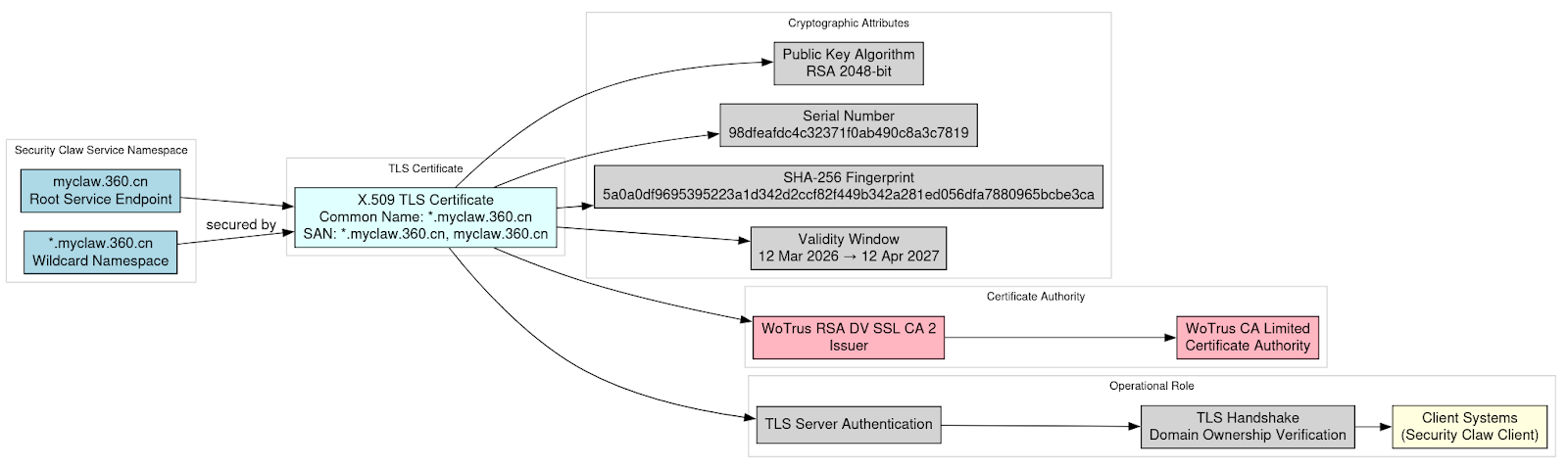
- Exposure of TLS Private Key for Myclaw 360 in Qihoo 360 “Security Claw” AI Platform
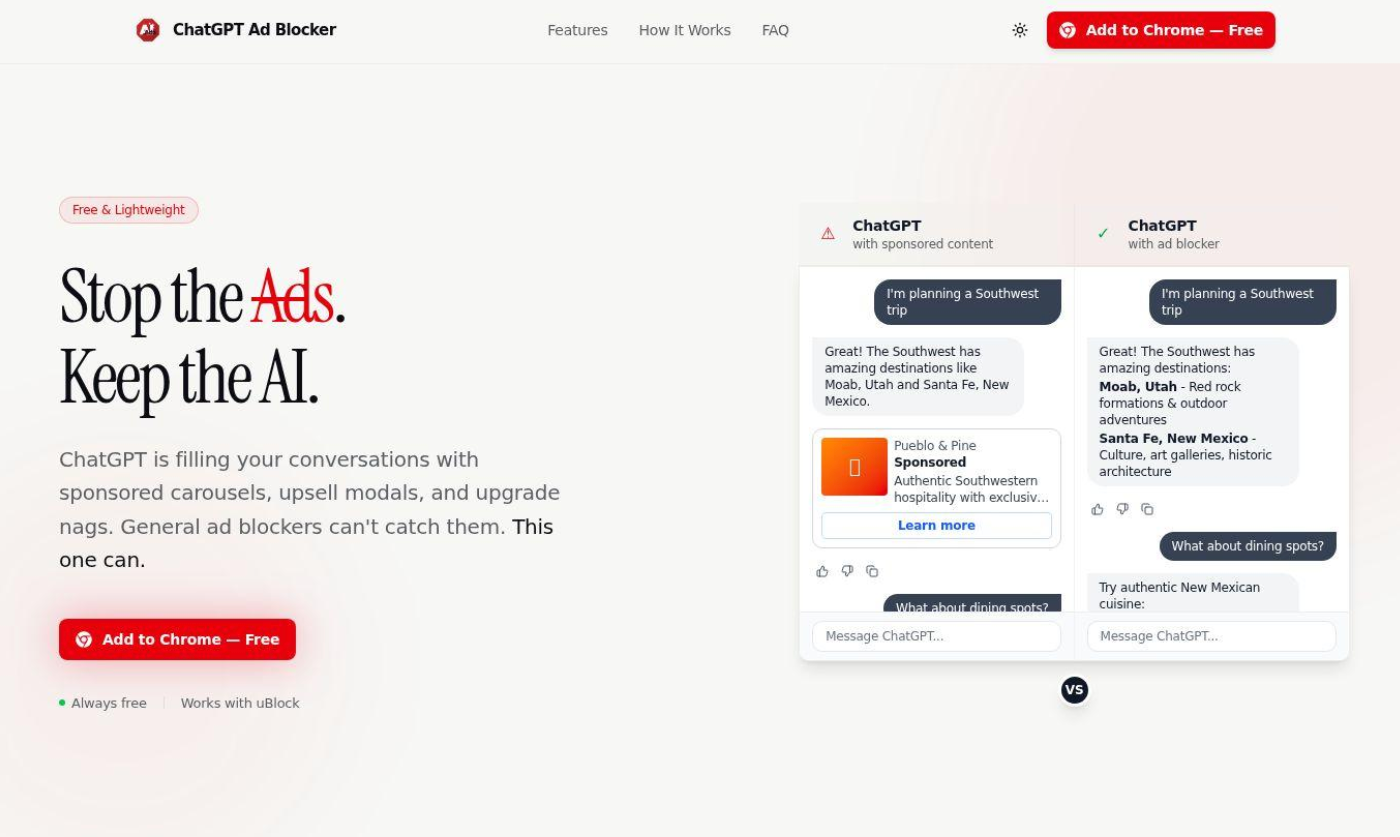
- SecuritySnack - OpenAI Anti-Ads Malware
Thanks for reading & see you next month!
-Daniel
https://www.linkedin.com/in/schwalbe/
https://infosec.exchange/@danonsecurity