After False Spring and Second Winter, we have reached “The Pollening”, which either precedes actual Spring, or possibly Third Winter - The jury is still out! In any case, I’ve put my "heavy rain coat" in storage, and pulled out my "slightly lighter rain coat." It’s been windy though - the cherry blossoms on the UW Quad are fighting to stay attached, and for a minute today I could have sworn the outside thermometer read 70 degrees. But that can’t be right, it’s April in Seattle after all!
Very much on brand for Spring however, things have started to get real busy again. I just wrapped up a fantastic week in San Francisco at the end of March. I gave a talk at BSidesSF, where I dove deep into the recent activities of Salt Typhoon and the i-Soon leaks.
After that I stuck around for RSAC, and it was great to connect with many of you in person. If I missed you, please drop me a line and let’s figure out the next time we’ll be in the same city. The next opportunity will likely be in Munich toward the end of April, where I will be attending the FIRST CTI Conference. If you’re going to be there, let me know and we’ll research who pours the best Maß !
Speaking of research, in this edition, we’re looking at some heavy-hitting infrastructure research, from the persistent "Doppelgänger" disinformation machine to a significant cryptographic leak within Qihoo 360’s AI platform.
Let’s dive in and get you up to speed!
Hot off the Presses
Doppelgänger / RRN Disinformation Infrastructure Ecosystem 2026
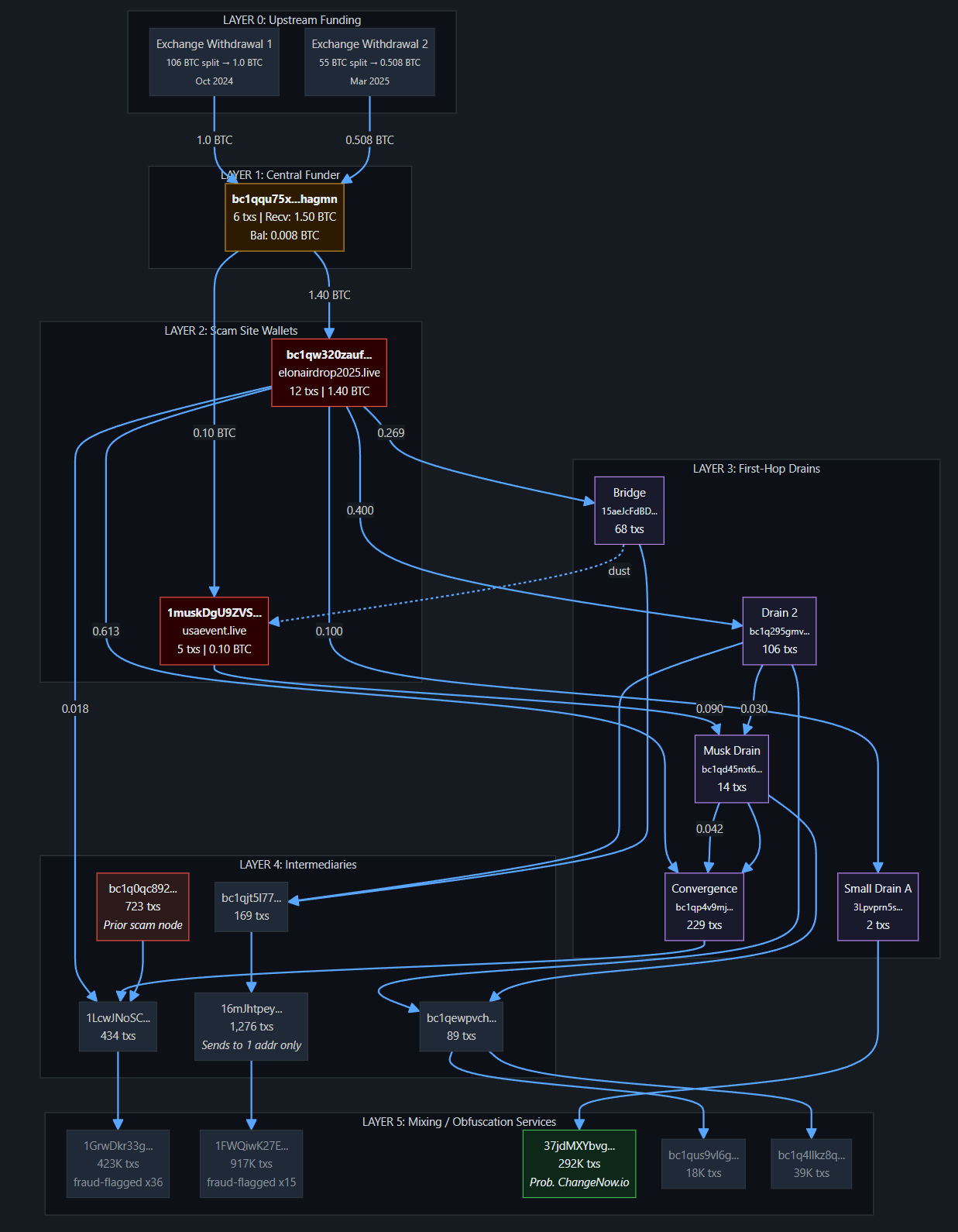
DTI researchers analyzed the Doppelgänger / RRN ecosystem as an infrastructure-based disinformation operation with notable operational waves from 2022 through 2026. Rather than operating as a loose set of fake websites, the network functions as a coordinated system built around large-scale media impersonation. Well-known Western news outlets are copied using domain lookalikes, typo variants, and alternate extensions, all tied to a central group of RRN domains that act as a hub for messaging.
Domain analysis showed registration activity in clear waves, along with consistent use of low-cost top-level domains and repeat patterns in domain naming. The operation also rotates domains after enforcement actions while keeping core naming consistent. The infrastructure is distributed and designed to stay active over time, with multiple connected domains supporting the name narratives. Overall, the findings point to a managed and sustained operation rather than isolated short-term activity.

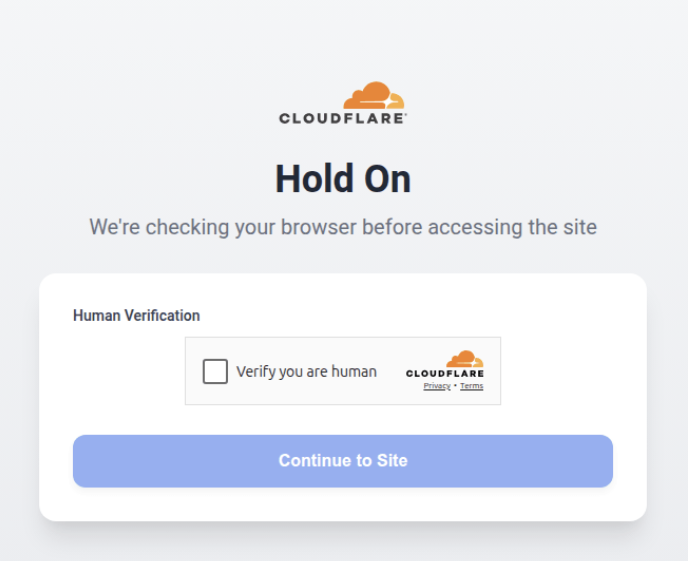
SecuritySnack - CloudFlare Anti-Security For Phishing
A Microsoft 365 credential harvesting campaign leveraged content delivery and security platforms like Cloudflare to delay detection and risk profiling. The campaign implemented multiple anti-detection techniques, including Cloudflare human verification, hardcoded IP block lists, user agent checks, and multiple sites and redirects, filtering out security tools, bots, and known infrastructure, often returning fake “404 Not Found” pages. The credential harvesting logic was executed through a hidden script using a custom VM function, preventing static analysis and dynamically updating destinations to legitimate domains when checks were triggered. Multiple sites in the cluster shared common infrastructure patterns, including Cloudflare nameservers, Namecheap registration, and a consistent Turnstile sitekey that may be used to identify related domains.
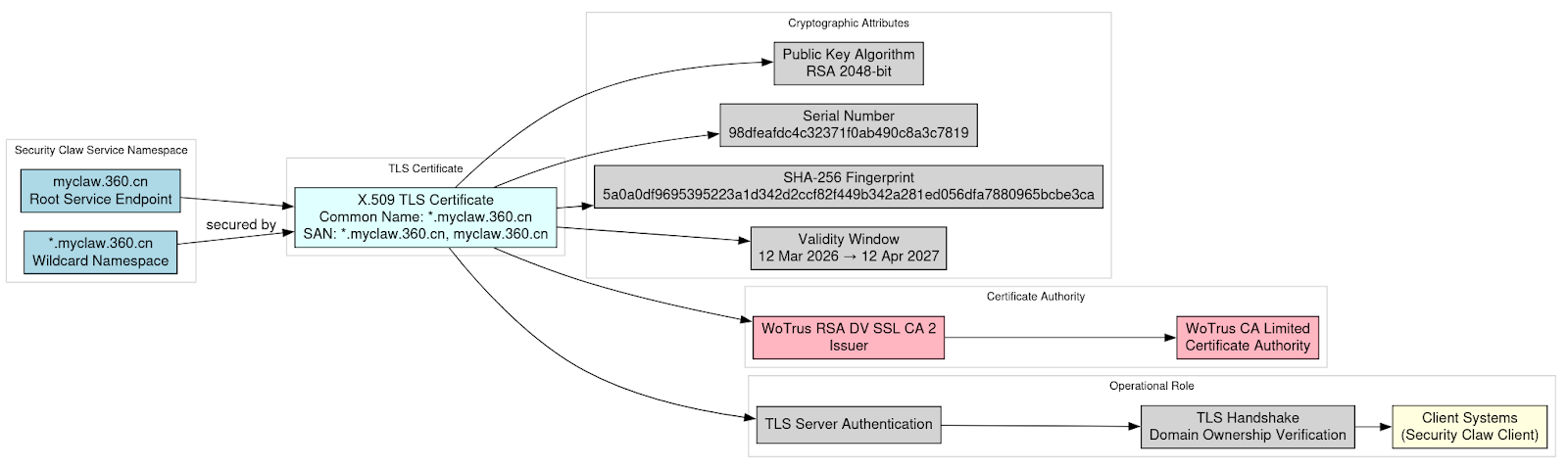
Exposure of TLS Private Key for Myclaw 360 in Qihoo 360 “Security Claw” AI Platform
DTI analyzed the confirmed exposure of a Transport Layer Security (TLS) private key associated with the wildcard certificate *.myclaw[.]360[.]cn, tied to Qihoo 360’s Security Claw platform. Cryptographic validation confirmed that the supplied private key matches the public key contained in the certificate, showing that the exposed credential is authentic and operational. Because the certificate covers the entire domain namespace, possession of the private key would allow impersonation of services across the platform if it remained trusted and unrevoked. Certificate transparency analysis indicates the certificate was subsequently rotated and replaced with a new RSA key pair following the exposure.
The exposure represented a leak of cryptographic trust material associated with the platform’s infrastructure. Evidence indicates the certificate and private key were present within the platform’s installer package, suggesting inclusion during the software build process. Domain registration data, passive DNS, and infrastructure analysis link the affected namespace to Qihoo 360’s operational environment, confirming the exposed key was associated with a service environment under the company’s direct control. Our team worked through a root cause and analytical assessment of the exposure as well as the possible threat scenarios that could result from it.
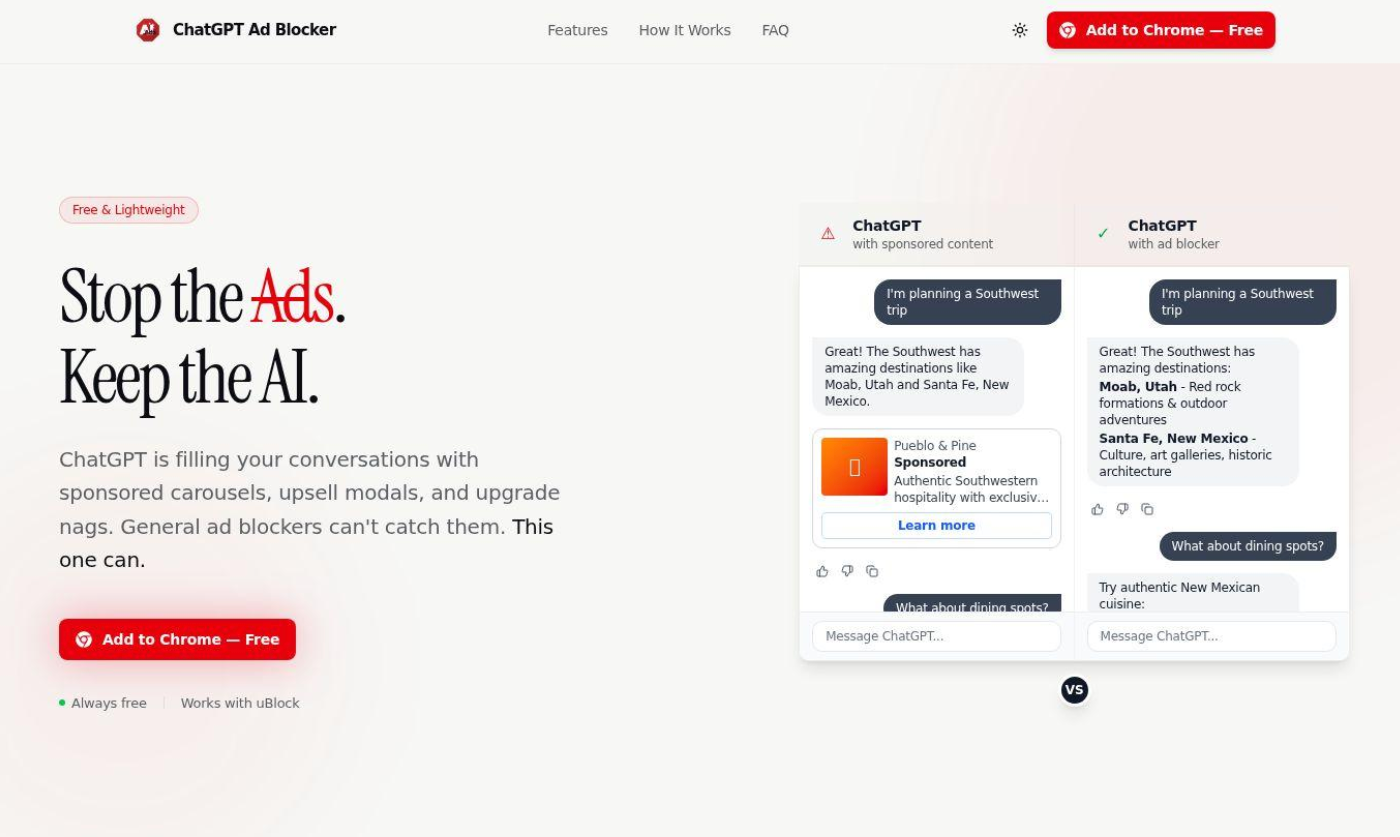
SecuritySnack - OpenAI Anti-Ads Malware
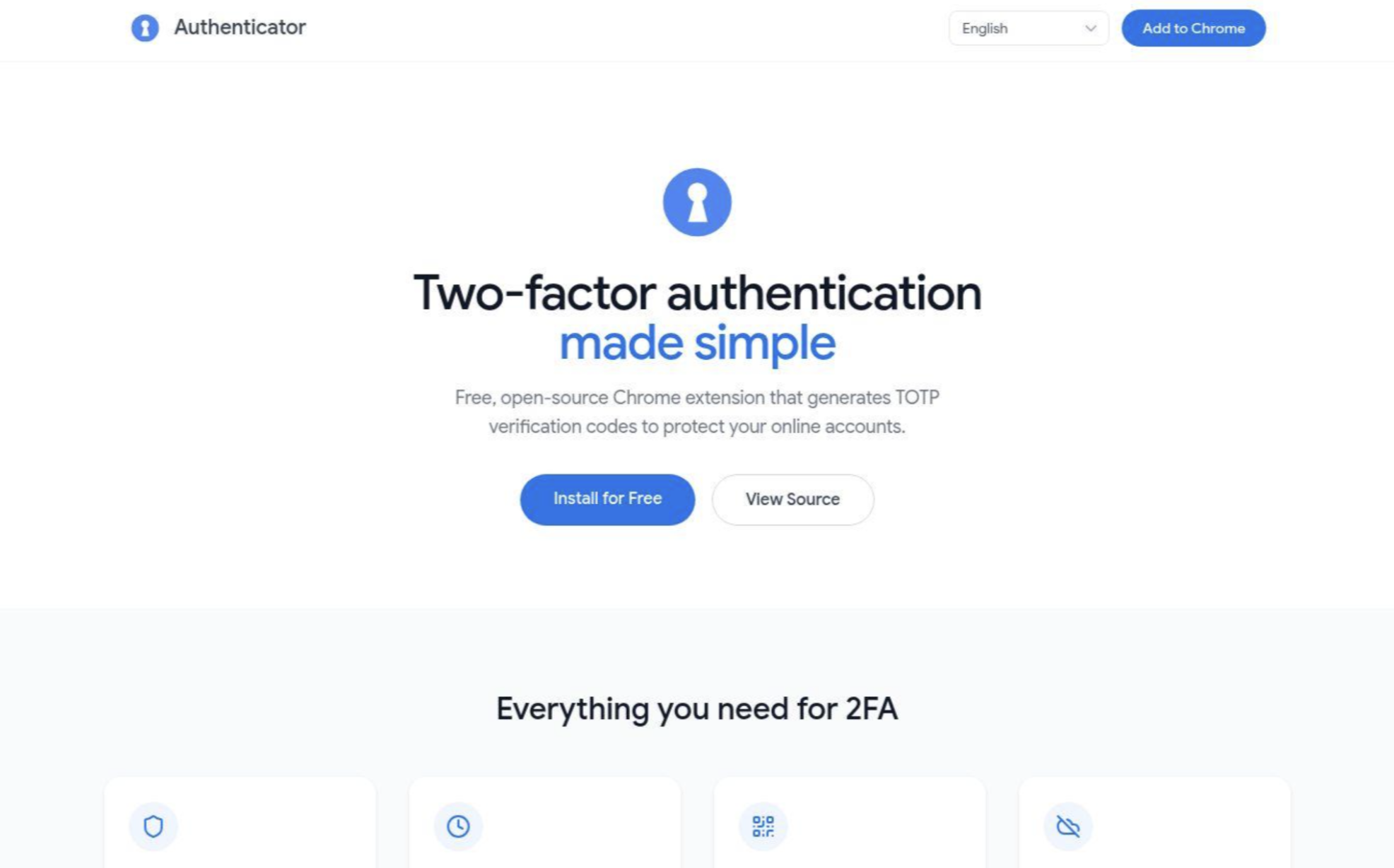
DTI researchers detailed the discovery of a malicious Chrome extension, named "ChatGPT Ad Blocker", found on the Google Chrome Web Store. The extension masquerades as an ad-blocking tool but is primarily designed to steal the user’s ChatGPT conversations data by systematically copying the HTML page and sending it to a webhook on a private Discord channel.
The identified activity appears to be an attempt to capitalize on OpenAI's policy shift to serve advertisements on its free tier by distributing malicious extensions that allege to block these ads.
What We’re Reading
In case you’re behind on your cybersecurity reading homework, DTI team member Ian Campbell’s monthly recommended reading list will get you up to speed!
- The top article for the month: Kentik - Internet and Airstrikes: Tracking Iran's Extended Communication Blackout
- The top research for the month: Mandiant - M-Trends 2026 Report
📚Check out the full reading list here
Where We’ll Be
- FIRST CTI Conference, Munich, Germany - 21-23 April
- SLEUTHCON, Arlington, VA - 05 June
Final Thoughts
As always, thank you to my returning readers! If you’re new, I hope you found this newsletter informational, helpful, and worthy of sharing with your peers. And of course I hope you will be coming back to read future editions!
We share this newsletter via email as well - if you’d prefer to get it to your inbox, sign up here.
If you missed last month's content, here are some quick links:
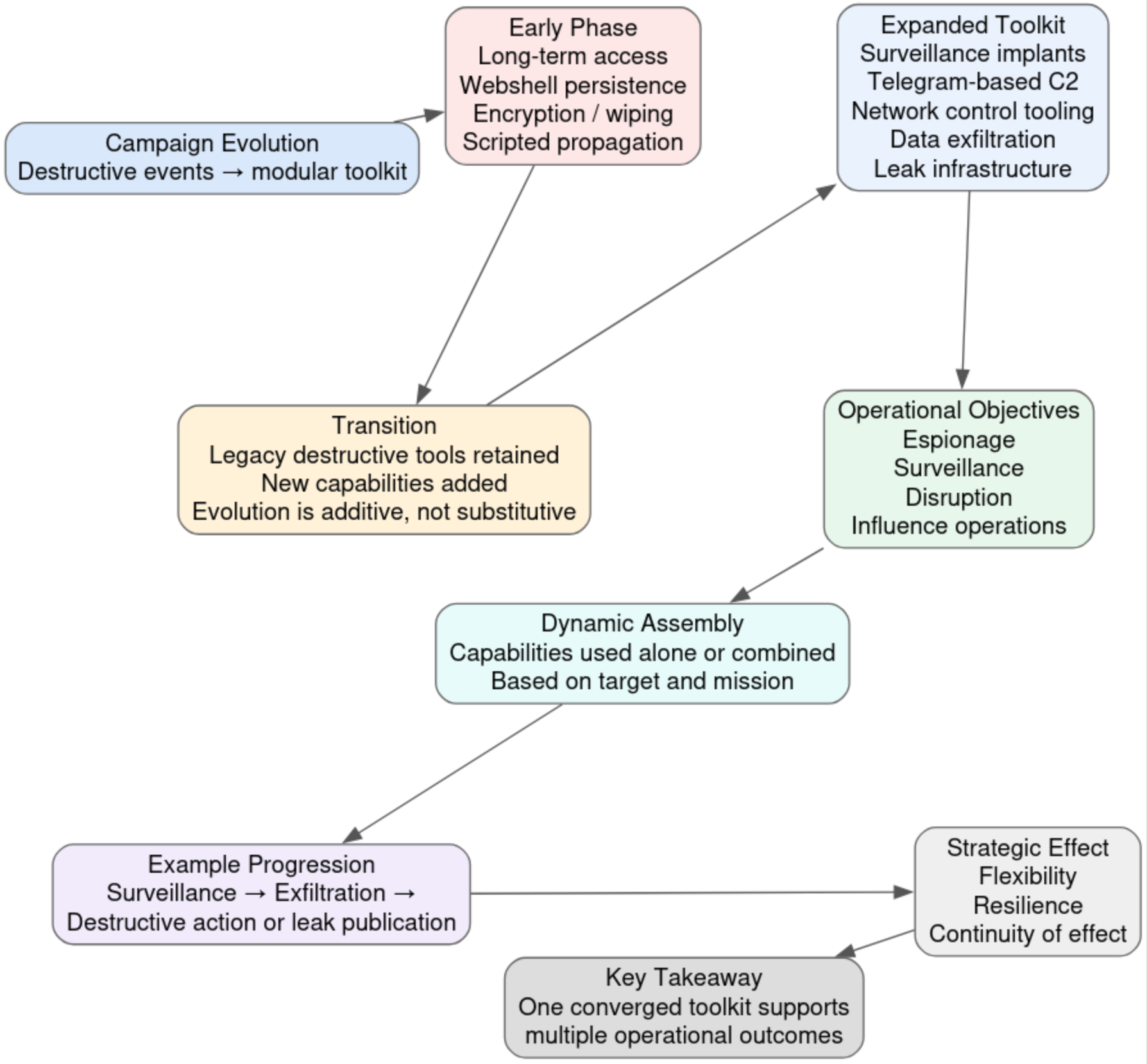
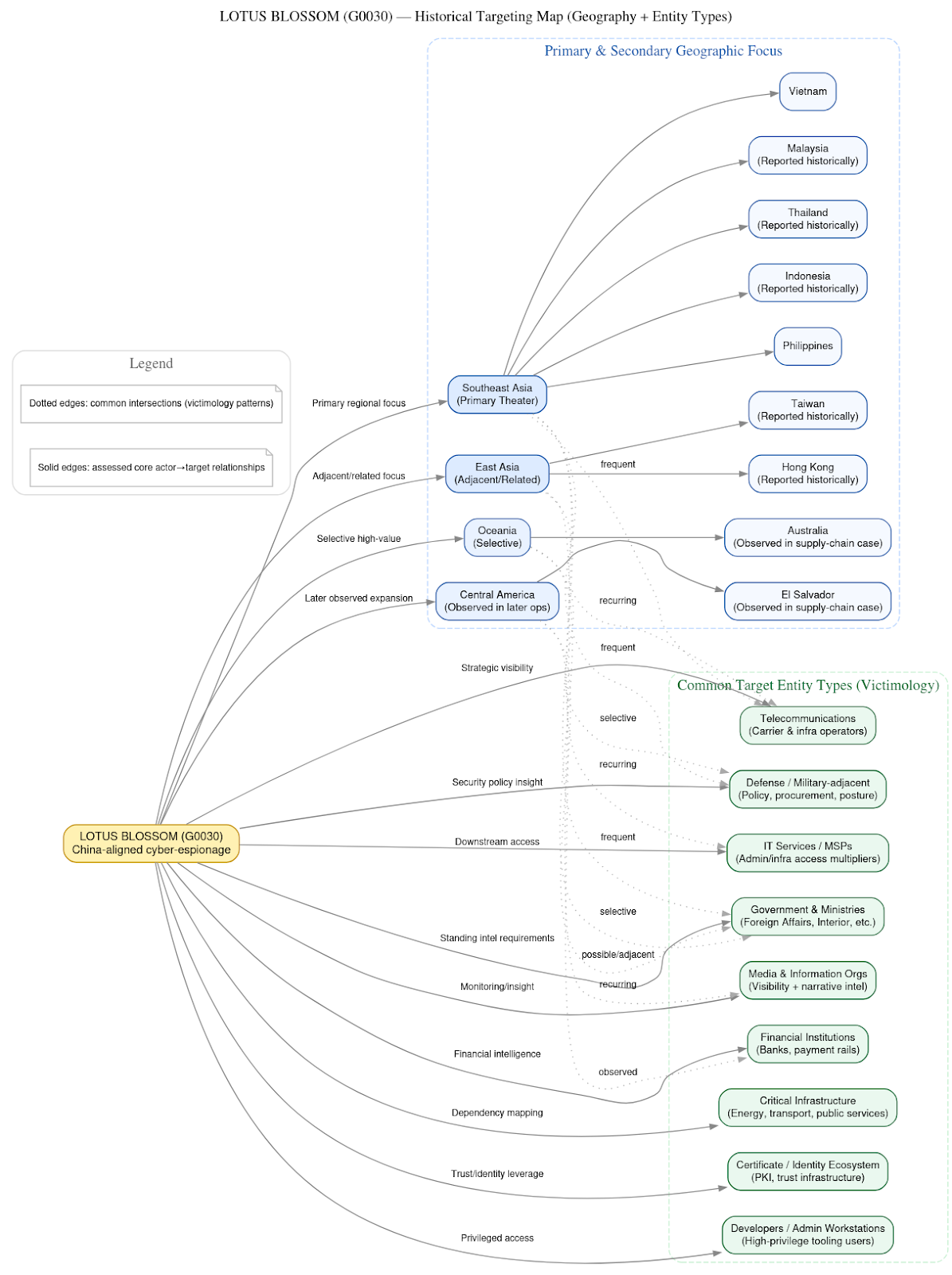
- Lotus Blossom (G0030) and the Notepad++ Supply-Chain Espionage Campaign
- SecuritySnack - Idolized Crypto Scams
Thanks for reading & see you next month!
-Daniel