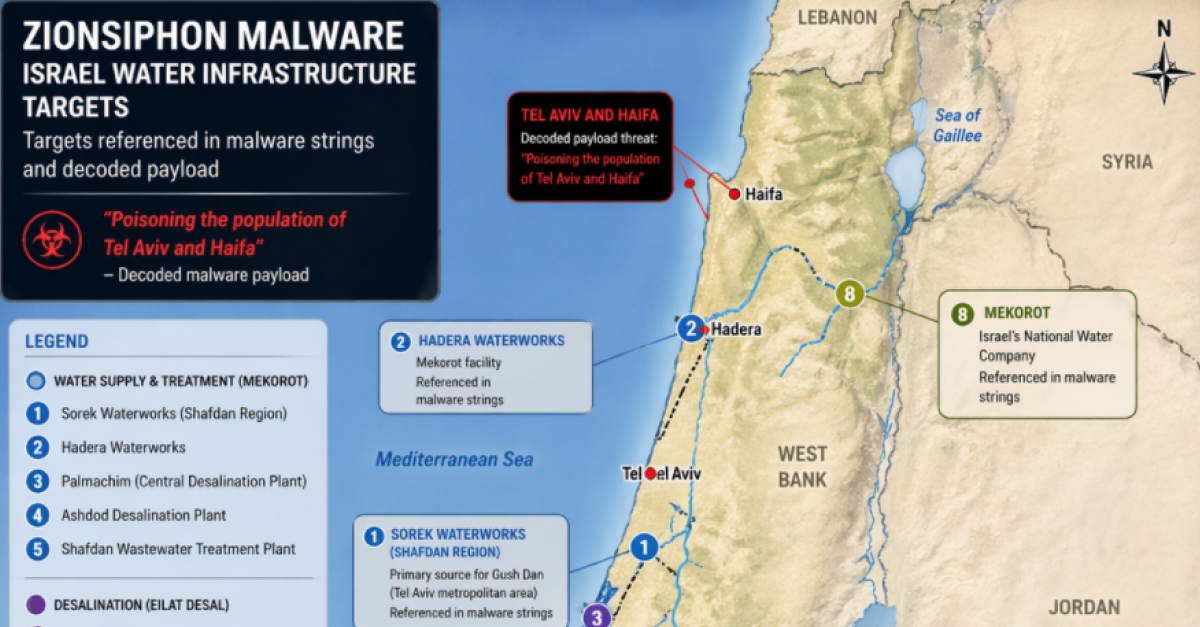
Analysis of ZionSiphon (SCADA_SecurityPatch_v8.4.exe), a .NET OT malware targeting Israeli water utilities. Discover its IOCs, targets, and flawed activation code.
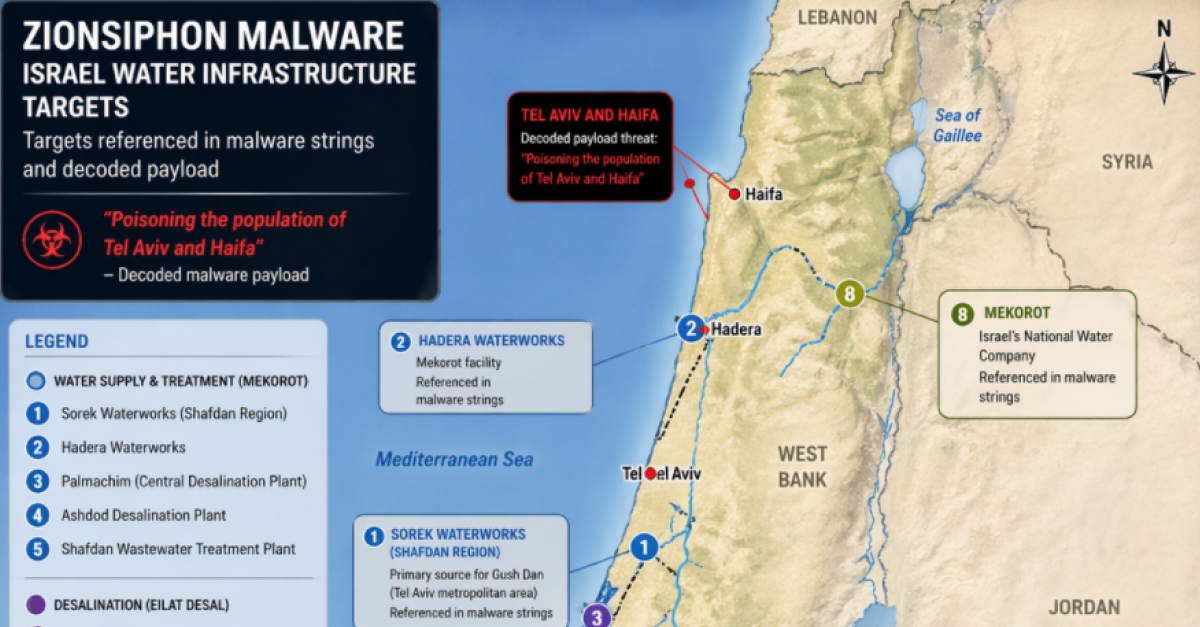
Analysis of ZionSiphon (SCADA_SecurityPatch_v8.4.exe), a .NET OT malware targeting Israeli water utilities. Discover its IOCs, targets, and flawed activation code.
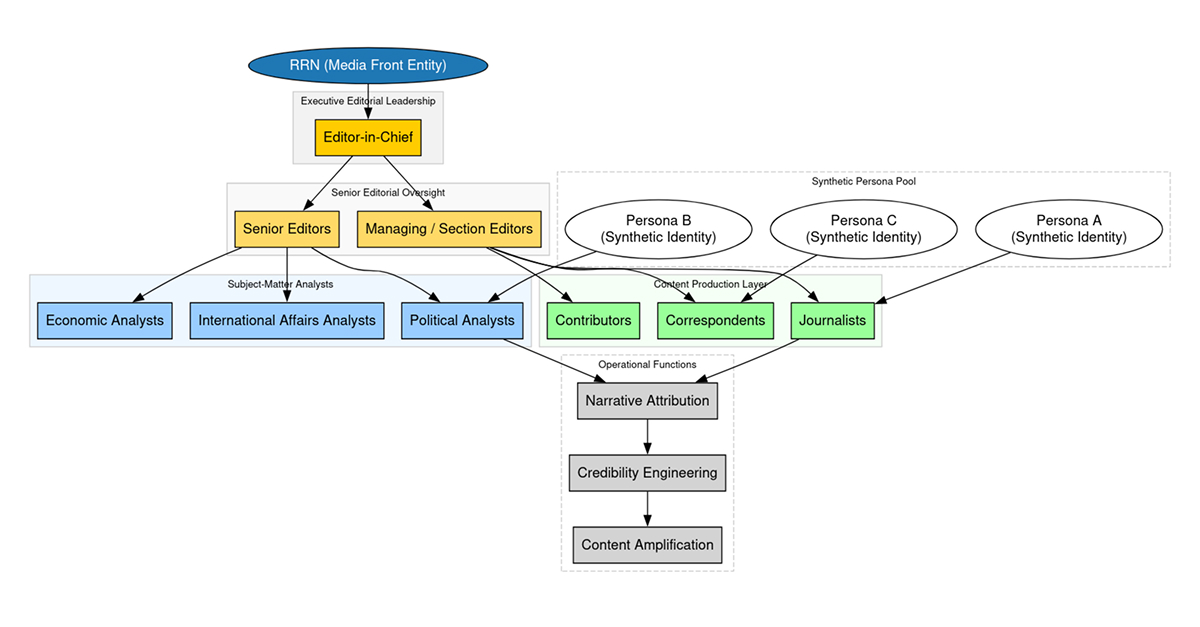
How does the Doppelgänger influence campaign reach 5M+ users? Read DTI’s latest report on the SDA/Structura ecosystem, featuring a deep dive into narrative propagation, domain rotation tactics, and a 72-hour crisis influence timeline.
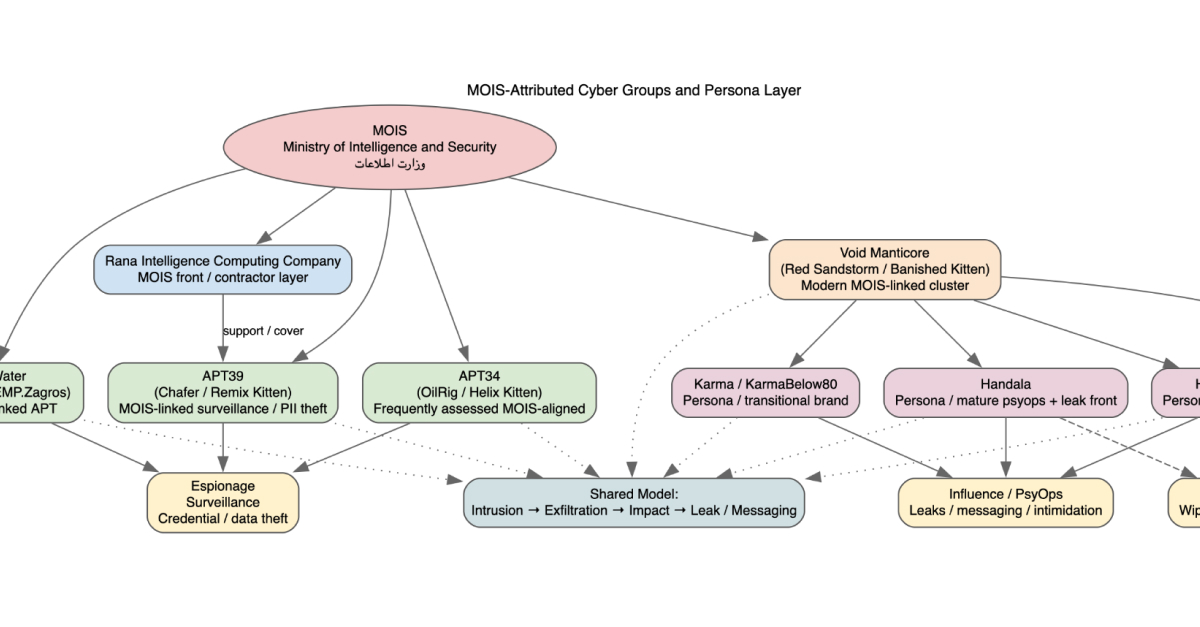
Explore the evolution of MOIS-linked actors Homeland Justice, Karma, and Handala. Analysis of destructive malware, surveillance integration, and the 2026 Stryker incident.

Systems thinking, biolistics, and the danger of mop-up science in infosec — plus this month's reading on ransomware, RPKI exploits, cPanel, and LLM pollution.
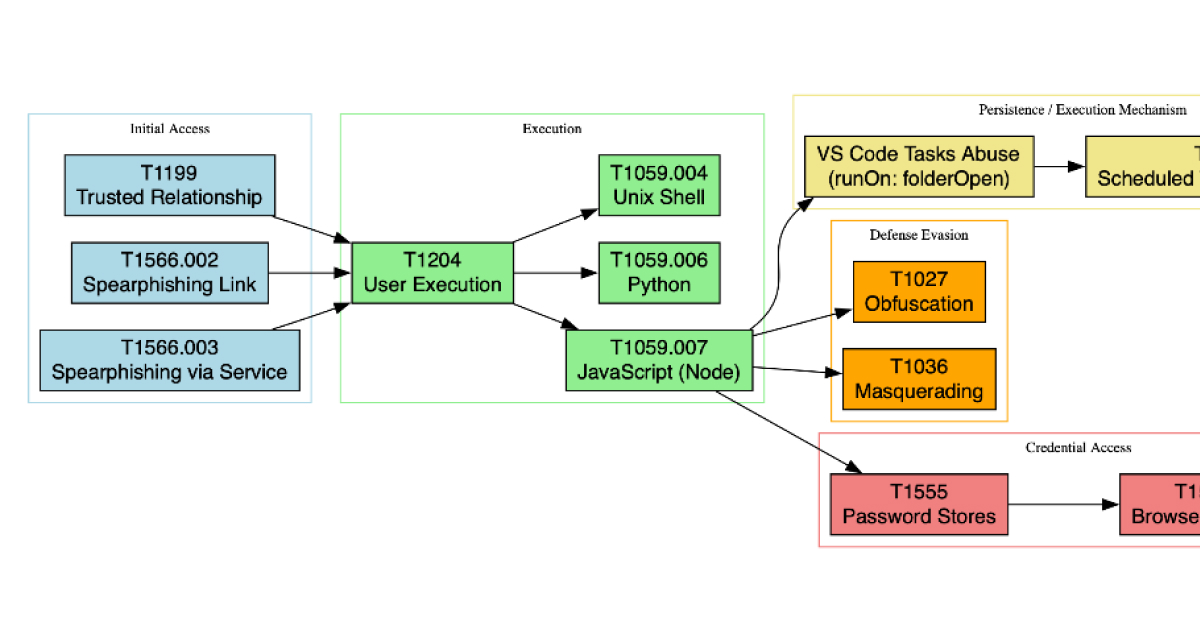
Analyze the DPRK "Contagious Interview" campaign targeting developers. Get technical deep-dives into VS Code task abuse, Node.js malware obfuscation, and a full Sigma/EDR detection pack to defend your CI/CD pipeline and identity perimeter.


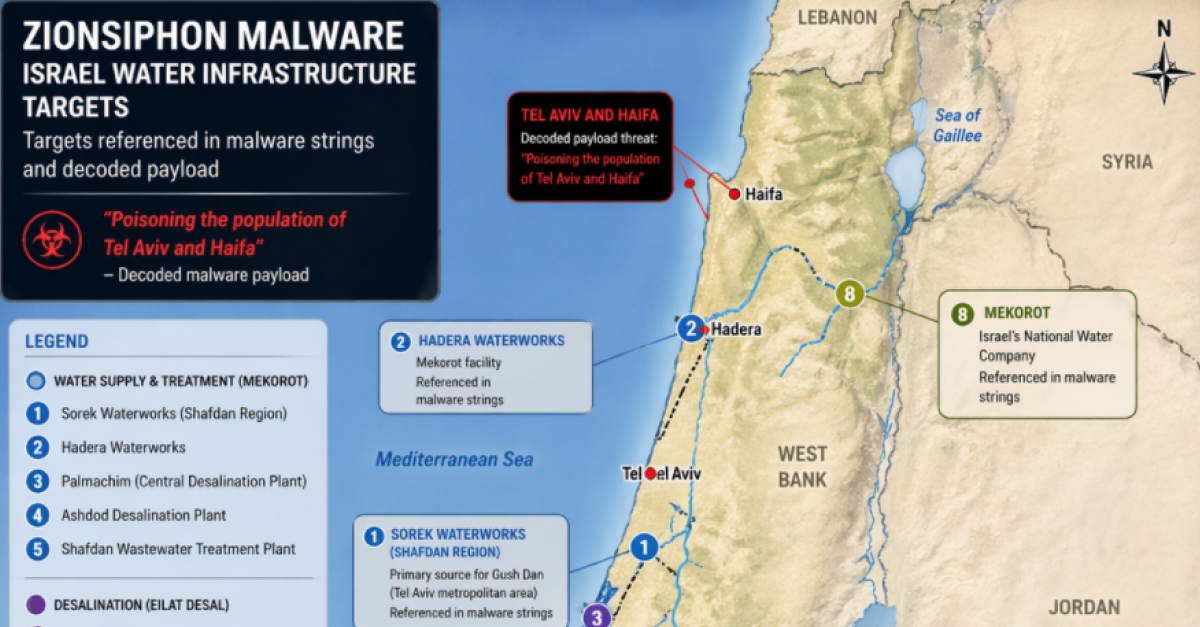
Analysis of ZionSiphon (SCADA_SecurityPatch_v8.4.exe), a .NET OT malware targeting Israeli water utilities. Discover its IOCs, targets, and flawed activation code.
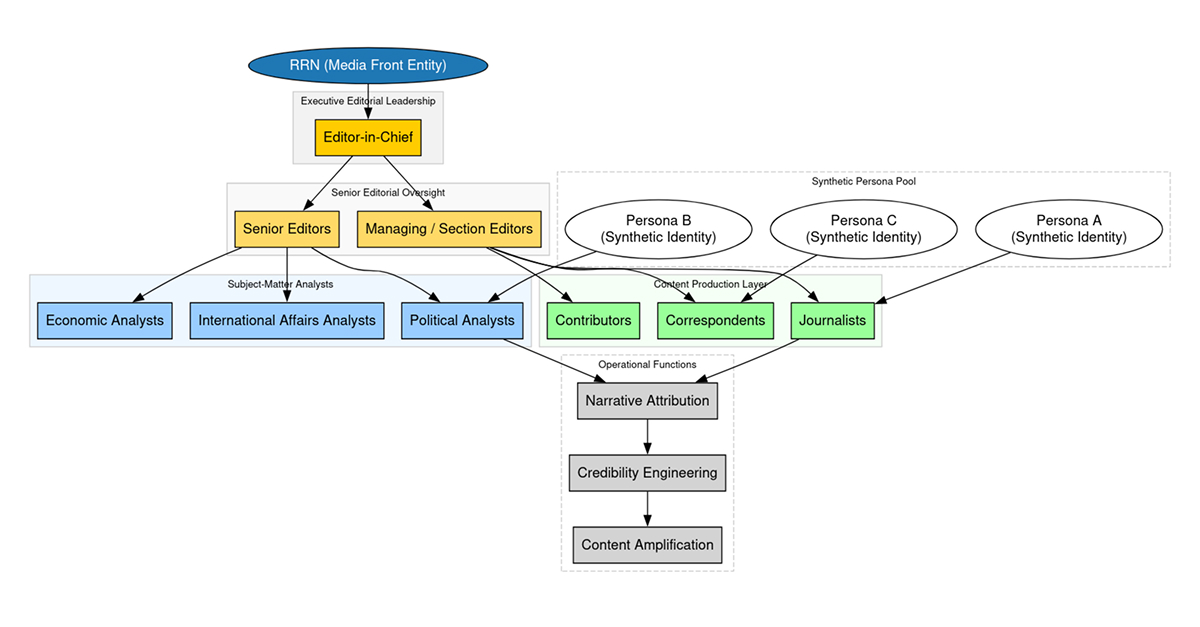
How does the Doppelgänger influence campaign reach 5M+ users? Read DTI’s latest report on the SDA/Structura ecosystem, featuring a deep dive into narrative propagation, domain rotation tactics, and a 72-hour crisis influence timeline.
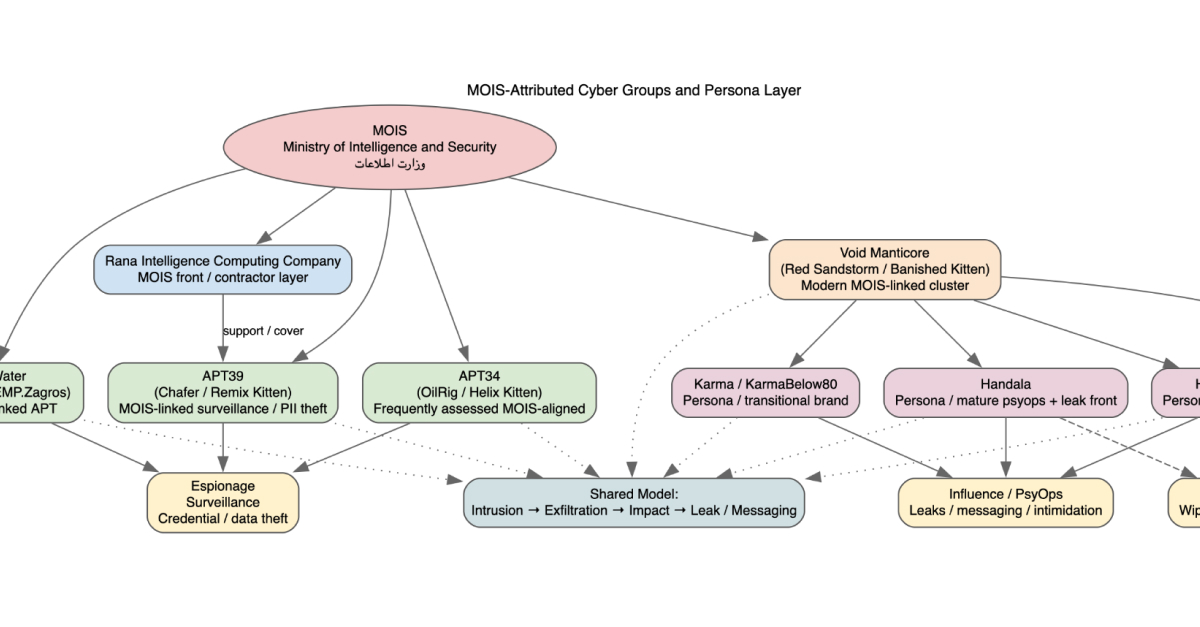
Explore the evolution of MOIS-linked actors Homeland Justice, Karma, and Handala. Analysis of destructive malware, surveillance integration, and the 2026 Stryker incident.

Systems thinking, biolistics, and the danger of mop-up science in infosec — plus this month's reading on ransomware, RPKI exploits, cPanel, and LLM pollution.
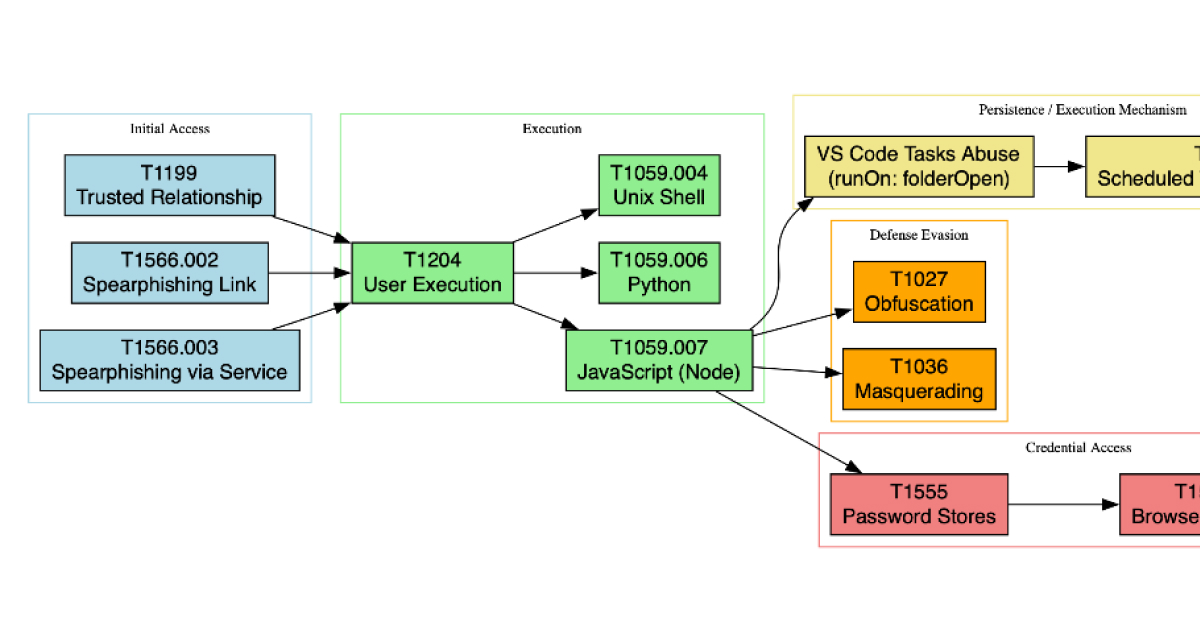
Analyze the DPRK "Contagious Interview" campaign targeting developers. Get technical deep-dives into VS Code task abuse, Node.js malware obfuscation, and a full Sigma/EDR detection pack to defend your CI/CD pipeline and identity perimeter.
Analysis of the persistent AIFrame campaign: A fake Google Authenticator Chrome extension and 6+ related apps use "deploy clean, update dirty" tactics to steal 2FA credentials and inject malicious iframes. Learn how this operation bypasses Google’s security reviews.